Vendor: Cisco
Exam Code: 200-301
Exam Name:
CCNA - Cisco Certified
Network Associate
Version: 22.111

Vendor: Cisco
Exam Code: 200-301
Exam Name:
CCNA - Cisco Certified
Network Associate
Version: 22.111
Which statement correctly compares traditional networks and controller-based networks?
|
A. |
Only traditional networks offer a centralized control plane |
|
B. |
Only traditional networks natively support centralized management |
|
C. |
Traditional and controller-based networks abstract policies from
device configurations |
|
D. |
Only controller-based networks decouple the control
plane and the data plane |
Answer: D
Explanation:
Most traditional devices use a distributed architecture, in which each control plane is resided in a networking device. Therefore they need to communicate with each other via messages to work correctly.
In contrast to distributed architecture, centralized (or controller-based) architectures centralizes the control of networking devices into one device, called SDN controller -> Answer D is correct.
How does HSRP provide first hop redundancy?
|
A. |
It load-balances traffic by assigning the
same metric value
to more than
one route to the same destination in the IP routing table. |
|
B. |
It load-balances Layer 2 traffic
along the path
by flooding traffic out all interfaces configured with
the same VLAN. |
|
C. |
It forwards multiple packets to the same destination over
different routed links
in the data
path |
|
D. |
It uses
a shared virtual
MAC and a virtual IP address to a group
of routers that
serve as the default gateway for hosts on a LAN |
Answer: D
Explanation:
This virtual IP address is in the same subnet as the interface IP address, but it is a different IP address. The router then automatically creates the virtual MAC address. All the cooperating HSRP routers know these virtual addresses, but only the HSRP active router uses these addresses at any one point in time.
The virtual router is responsible for host communications such as an ARP request for the host’s default gateway. Technically, this is served by the active router since it is hosting the virtual router. However, it is the virtual router’s IP address and MAC address that are used for outgoing packets.
Which two actions influence the EIGRP route selection process? (Choose two)
|
A. |
The router calculates the reported distance by multiplying the delay on the exiting Interface by 256. |
|
B. |
The router
calculates the best
backup path to the destination route and assigns
it as the feasible
successor. |
|
C. |
The router calculates the feasible distance of all paths
to the destination route |
|
D. |
The advertised distance is calculated by a downstream neighbor to inform
the local router
of the bandwidth on the link |
|
E. |
The router must use the advertised distance as the metric
for any given
route |
Answer:
BC
Explanation:
The reported distance (or advertised distance) is the cost from the neighbor to the destination. It is calculated from the router advertising the route to the network. For example in the topology below, suppose router A & B are exchanging their routing tables for the first time. Router B says "Hey, the best metric (cost) from me to IOWA is 50 and the metric from you to IOWA is 90" and advertises it to router A.
Router A considers the first metric (50) as the Advertised distance. The second metric (90), which is from NEVADA to IOWA (through IDAHO), is called the Feasible distance.
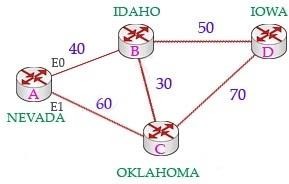
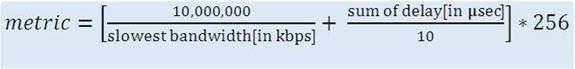
The reported distance is calculated in the same way of calculating the metric. By default (K1 = 1, K2 = 0, K3 = 1, K4 = 0, K5 = 0), the metric is calculated as follows:
-> Answer A is not correct.
Feasible successor is the backup route. To be a feasible successor, the route must have an Advertised distance (AD) less than the Feasible distance (FD) of the current successor route -> Answer B is correct.
Feasible distance (FD): The sum of the AD plus the cost between the local router and the next- hop router.
The router must calculate the FD of all paths to choose the best path to put into the routing table. Note: Although the new CCNA exam does not have EIGRP topic but you should learn the basic knowledge of this routing protocol.
Which two capabilities of Cisco DNA Center make it more extensible as compared to traditional campus device management? (Choose two.)
|
A. |
adapters that support
all families of Cisco IOS
software |
|
B. |
SDKs that
support interaction with third-party network
equipment |
|
C. |
customized versions for small, medium, and large enterprises |
|
D. |
REST APIs
that allow for external applications to interact natively with Cisco DNA
Center |
|
E. |
modular design that is upgradable as needed |
Answer: BD
Explanation:
Cisco DNA Center offers 360-degree extensibility through four distinct types of platform capabilities:
+ Intent-based APIs leverage the controller and enable business and IT applications to deliver intent to the network and to reap network analytics and insights for IT and business innovation.
+ Process adapters, built on integration APIs, allow integration with other IT and network systems to streamline IT operations and processes.
+ Domain adapters, built on integration APIs, allow integration with other infrastructure domains such as data center, WAN, and security to deliver a consistent intent-based infrastructure across the entire IT environment.
+ SDKs allow management to be extended to third-party vendor's network devices to offer support for diverse environments.
Reference: https://www.cisco.com/c/en/us/products/collateral/cloud-systems-management/dna- center/nb- 06-dna-cent-platf-aag-cte-en.html
Refer to the exhibit. What does router R1 use as its OSPF router-ID?
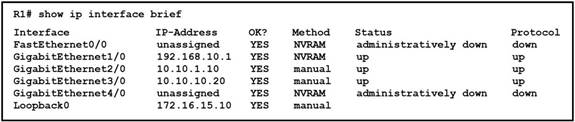
|
A. |
10.10.1.10 |
|
B. |
10.10.10.20 |
|
C. |
172.16.15.10 |
|
D. |
192.168.0.1 |
Answer: C
Explanation:
OSPF uses the following criteria to select the router ID:
1. Manual configuration of the router
ID (via the "router-id x.x.x.x" command under OSPF router
configuration mode).
2. Highest IP address on a loopback
interface.
3.
Highest IP address
on a non-loopback and active
(no shutdown) interface.
Which 802.11 frame type is association response?
|
A. |
management |
|
B. |
protected frame |
|
C. |
control |
|
D. |
action |
Answer:
A
Explanation:
There are three main types of 802.11 frames: the Data Frame, the Management Frame and the Control Frame. Association Response belongs to Management Frame. Association response is sent in response to an association request.
Which API is used in controller-based architectures to interact with edge devices?
|
A. |
overlay |
|
B. |
northbound |
|
C. |
underlay |
|
D. |
southbound |
Answer: D
Explanation:
overlay: the virtual network underlay: the physical network nothbound: interacts with the server
Which statement identifies the functionality of virtual machines?
|
A. |
Virtualized servers run most
efficiently when they
are physically connected to a switch
that is separate from
the hypervisor |
|
B. |
The hypervisor can virtualize physical components including CPU, memory, and storage |
|
C. |
Each hypervisor can support a single virtual
machine and a single software switch |
|
D. |
The hypervisor communicates on Layer 3 without the need for
additional resources |
Answer: B
Which type of address is the public IP address of a NAT device?
|
A. |
outside global |
|
B. |
outside local |
|
C. |
inside global |
|
D. |
inside local |
|
E. |
outside public |
|
F. |
inside public |
Answer: C
Explanation:
NAT use four types of addresses:
*
Inside local address
- The IP address assigned
to a host on the inside network.
The address is usually not an IP address assigned by
the Internet Network Information Center (InterNIC) or service provider. This
address is likely to be an RFC 1918 private address.
*
Inside global address
- A legitimate IP address
assigned by the InterNIC or service provider
that represents one or more inside local IP addresses to the outside
world.
*
Outside local address
- The IP address of an outside
host as it is known to the hosts on the
inside network.
*
Outside global address
- The IP address assigned
to a host on the outside network.
The owner of the host assigns
this address.
Which option about JSON is true?
|
A. |
uses predefined tags
or angle brackets () to delimit
markup text |
|
B. |
used to describe structured data that includes arrays |
|
C. |
used for storing information |
|
D. |
similar to HTML,
it is more verbose than
XML |
Answer: B
Explanation:
JSON data is written as name/value pairs.
A name/value pair consists of a field name (in double quotes), followed by a colon, followed by a value:
"name":"Mark"
JSON can use arrays. Array values must be of type string, number, object, array, boolean or null.. For example:
{
"name":"John", "age":30,
"cars":[ "Ford", "BMW", "Fiat" ]
}
Which attribute does a router use to select the best path when two or more different routes to the same destination exist from two different routing protocols?
|
A. |
dual algorithm |
|
B. |
metric |
|
C. |
administrative distance |
|
D. |
hop count |
Answer: C
Explanation:
Administrative distance is the feature used by routers to select the best path when there are two or more different routes to the same destination from different routing protocols. Administrative distance defines the reliability of a routing protocol.
Which two values or settings must be entered when configuring a new WLAN in the Cisco Wireless LAN Controller GUI? (Choose two)
|
A. |
management interface settings |
|
B. |
QoS settings |
|
C. |
Ip address of one or more
access points |
|
D. |
SSID |
|
E. |
Profile name |
Answer: DE
What are two benefits of network automation? (Choose two)
|
A. |
reduced operational costs |
|
B. |
reduced hardware footprint |
|
C. |
faster changes
with more reliable results |
|
D. |
fewer network
failures |
|
E. |
increased network security |
Answer: AC
Which command prevents passwords from being stored in the configuration as plaintext on a router or switch?
|
A. |
enable secret |
|
B. |
service password-encryption |
|
C. |
username Cisco
password encrypt |
|
D. |
enable password |
Answer:
B
Explanation:
enable password <string> - Sets the enable password, and stores that password in plaintext in the config.
enable secret <string> - Sets the enable password, and stores that password as an md5 hash in the config.
service password-encryption - For any passwords in the config that are stored in plaintext, this command changes them to be stored as hashed values instead.
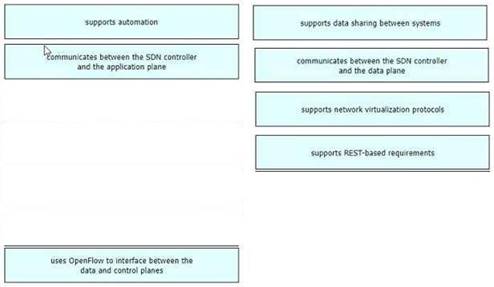
Drag and Drop Question
Drag drop the descriptions from the left on to the correct configuration-management technologies on the right.
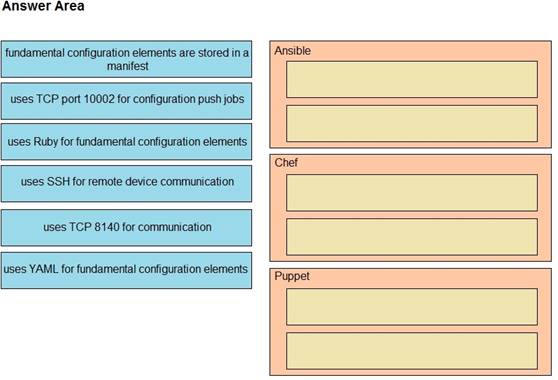
Answer:
Explanation:
The focus of Ansible is to be streamlined and fast, and to require no node agent installation. Thus, Ansible performs all functions over SSH. Ansible is built on Python, in contrast to the Ruby foundation of Puppet and Chef.
TCP port 10002 is the command port. It may be configured in the Chef Push Jobs configuration file . This port allows Chef Push Jobs clients to communicate with the Chef Push Jobs server.
Puppet is an open-source configuration management solution, which is built with Ruby and offers custom Domain Specific Language (DSL) and Embedded Ruby (ERB) templates to create custom Puppet language files, offering a declarative-paradigm programming approach.
A Puppet piece of code is called a manifest, and is a file with .pp extension.
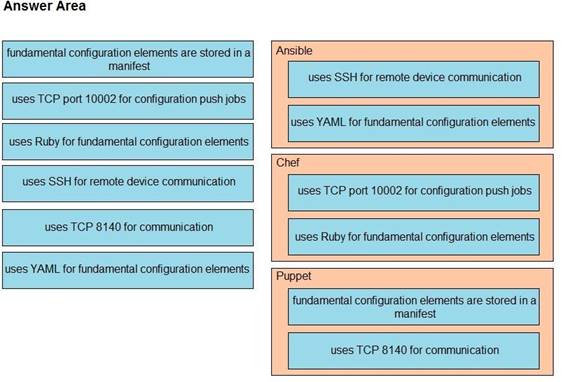
Drag and Drop Question
Drag and drop the descriptions of file-transfer protocols from the left onto the correct protocols on the right.
Answer:
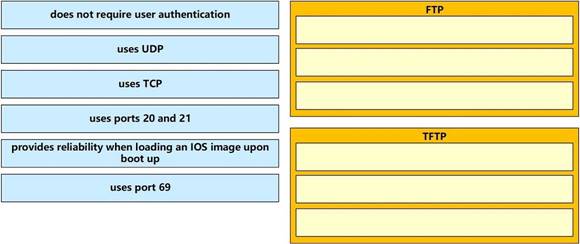
Drag and Drop Question
Drag and drop the WLAN components from the left onto the correct descriptions on the right.
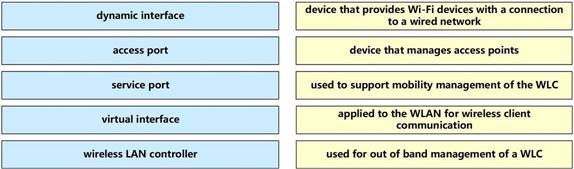
Answer:
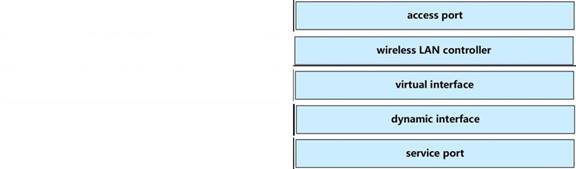
Explanation:
The service port can be used management purposes, primarily for out-of-band management. However, AP management traffic is not possible across the service port. In most cases, the service port is used as a "last resort" means of accessing the controller GUI for management purposes. For example, in the case where the system distribution ports on the controller are down or their communication to the wired network is otherwise degraded.
A dynamic interface with the Dynamic AP Management option enabled is used as the tunnel source for packets from the controller to the access point and as the destination for CAPWAP packets from the access point to the controller.
The virtual interface is used to support mobility management, Dynamic Host Configuration Protocol (DHCP) relay, and embedded Layer 3 security such as guest web authentication. It also maintains the DNS gateway host name used by Layer 3 security and mobility managers to verify the source of certificates when Layer 3 web authorization is enabled.
Reference: https://www.cisco.com/c/en/us/td/docs/wireless/controller/8-5/config- guide/b_cg85/ports_and_interfaces.html
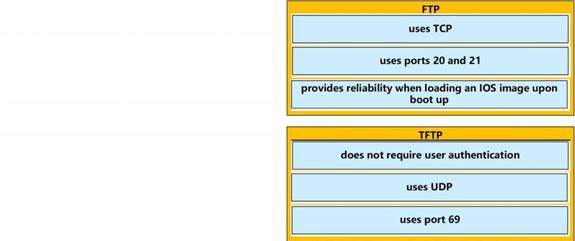
Drag and Drop Question
Drag and drop the threat-mitigation techniques from the left onto the types of threat or attack they
mitigate on the right.
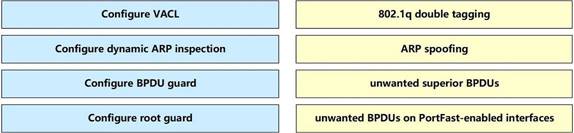
Answer:
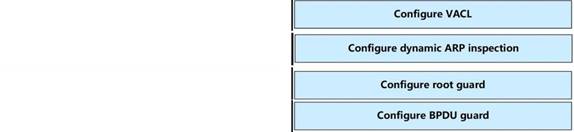
Explanation:
Double-Tagging attack:
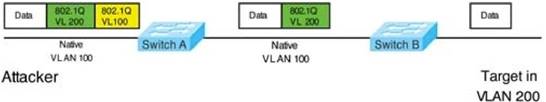
In this attack, the attacking computer generates frames with two 802.1Q tags. The first tag matches the native VLAN of the trunk port (VLAN 10 in this case), and the second matches the VLAN of a host it wants to attack (VLAN 20).
When the packet from the attacker reaches Switch A, Switch A only sees the first VLAN 10 and it matches with its native VLAN 10 so this VLAN tag is removed. Switch A forwards the frame out all links with the same native VLAN 10. Switch B receives the frame with an tag of VLAN 20 so it removes this tag and forwards out to the Victim computer.
Note: This attack only works if the trunk (between two switches) has the same native VLAN as the attacker.
To mitigate this type of attack, you can use VLAN access control lists (VACLs, which applies to all traffic within a VLAN. We can use VACL to drop attacker traffic to specific victims/servers) or implement Private VLANs.
ARP attack (like ARP poisoning/spoofing) is a type of attack in which a malicious actor sends falsified ARP messages over a local area network as ARP allows a gratuitous reply from a host even if an ARP request was not received. This results in the linking of an attacker's MAC address with the IP address of a legitimate computer or server on the network. This is an attack based on ARP which is at Layer 2. Dynamic ARP inspection (DAI) is a security feature that validates ARP
packets in a network which can be used to mitigate this type of attack.
Drag and Drop Question
Drag and drop the functions from the left onto the correct network components on the right.
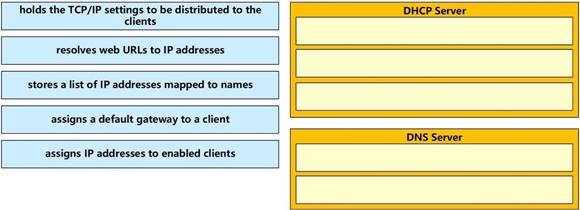
Answer:
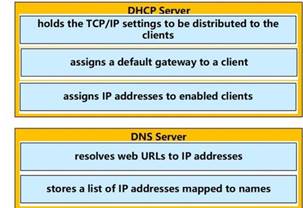
Drag and Drop Question
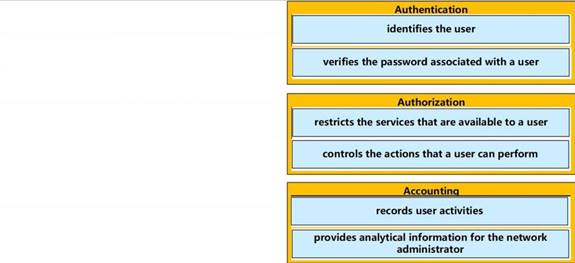
Drag and drop the AAA functions from the left onto the correct AAA services on the right.
Answer:
Drag and Drop Question
Drag and drop the IPv4 network subnets from the left onto the correct usable host ranges on the right
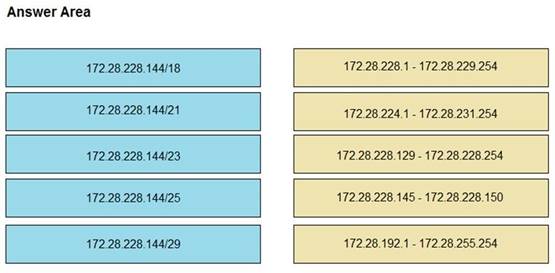
Answer:
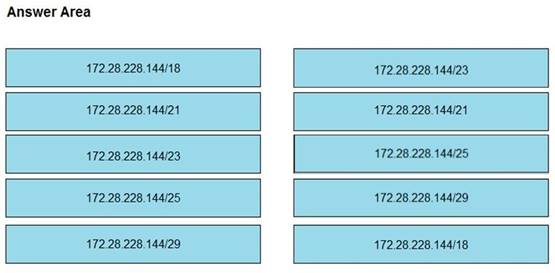
Explanation:
This subnet question requires us to grasp how to subnet very well. To quickly find out the subnet range, we have to find out the increment and the network address of each subnet. Let's take an example with the subnet 172.28.228.144/18:
From the /18 (= 1100 0000 in the 3rd octet), we find out the increment is 64. Therefore the network address of this subnet must be the greatest multiple of the increment but not greater than the value in the 3rd octet (228). We can find out the 3rd octet of the network address is 192 (because 192 = 64 * 3 and 192 < 228) -> The network address is 172.28.192.0. So the first usable host should be 172.28.192.1 and it matches with the 5th answer on the right. In this case we don't need to calculate the broadcast address because we found the correct answer.
Let's take another example with subnet 172.28.228.144/23 -> The increment is 2 (as /23 = 1111 1110 in 3rd octet) -> The 3rd octet of the network address is 228 (because 228 is the multiply of 2 and equal to the 3rd octet) -> The network address is 172.28.228.0 -> The first usable host is 172.28.228.1. It is not necessary but if we want to find out the broadcast address of this subnet,
we can find out the next network address, which is 172.28.(228 + the increment number).0 or 172.28.230.0 then reduce 1 bit -> 172.28.229.255 is the broadcast address of our subnet.
Therefore the last usable host is 172.28.229.254.
Drag and Drop Question
Drag and drop the Cisco Wireless LAN Controller security settings from the left onto the correct security mechanism categories on the right.
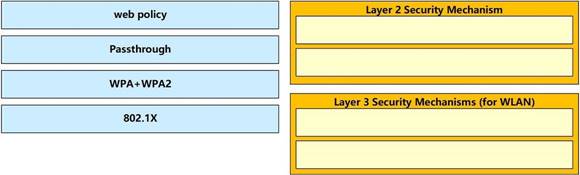
Answer:
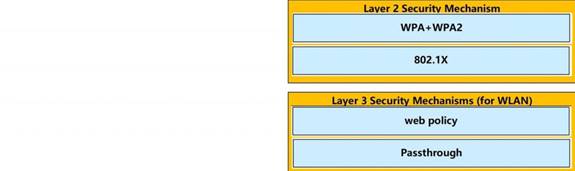
Explanation:
Layer 2 Security Mechanism includes WPA+WPA2, 802.1X, Static WEP, CKIP while Layer 3 Security Mechanisms (for WLAN) includes IPSec, VPN Pass-Through, Web Passthrough ...
Reference: https://www.cisco.com/c/en/us/support/docs/wireless/4400-series-wireless-lan- controllers/106082-wlc-compatibility-matrix.html
What is a benefit of using a Cisco Wireless LAN Controller?
|
A. |
Central AP management requires more complex configurations |
|
B. |
Unique SSIDs
cannot use the
same authentication method |
|
C. |
It supports autonomous and lightweight APs |
|
D. |
It eliminates the need to configure each
access point individually |
Answer: D
Explanation:
A wireless LAN (or WLAN) controller is used in combination with the Lightweight Access Point Protocol (LWAPP) to "manage light-weight access points in large quantities" by the network administrator or network operations center.
Which network allows devices to communicate without the need to access the Internet?
|
A. |
1729.0.0/16 |
|
B. |
172.28.0.0/16 |
|
C. |
192.0.0.0/8 |
|
D. |
209.165.201.0/24 |
Answer:
B
Explanation:
This question asks about the private ranges of IPv4 addresses. The private ranges of each class of IPv4 are listed below:
Class A private IP address ranges from 10.0.0.0 to 10.255.255.255 Class B private IP address ranges from 172.16.0.0 to 172.31.255.255 Class C private IP address ranges from 192.168.0.0 to 192.168.255.255 Only the network 172.28.0.0/16 belongs to the private IP address (of class B).
Which result occurs when PortFast is enabled on an interface that is connected to another switch?
|
A. |
Spanning tree may
fail to detect
a switching loop
in the network
that causes broadcast storms |
|
B. |
VTP is allowed to propagate VLAN
configuration information from
switch to switch
automatically. |
|
C. |
Root port
choice and spanning tree recalculation are accelerated when a switch
link goes down |
|
D. |
After spanning tree
converges PortFast shuts
down any port
that receives BPDUs. |
Answer: A
Explanation:
Enabling the PortFast feature causes a switch or a trunk port to enter the STP forwarding-state immediately or upon a linkup event, thus bypassing the listening and learning states.
Note: To enable portfast on a trunk port you need the trunk keyword "spanning-tree portfast trunk"
When configuring a WLAN with WPA2 PSK in the Cisco Wireless LAN Controller GUI, which two formats are available to select? (Choose two)
|
A. |
ASCII |
|
B. |
base64 |
|
C. |
binary |
|
D. |
decimal |
|
E. |
hexadecimal |
Answer: AE
Explanation:
When configuring a WLAN with WPA2 Preshared Key (PSK), we can choose the encryption key format as either ASCII or HEX.
Reference: https://www.cisco.com/c/en/us/td/docs/wireless/controller/9800/config-
guide/b_wl_16_10_cg/ multi-preshared-key.pdf
Two switches are connected and using Cisco Dynamic Trunking Protocol SW1 is set to Dynamic Desirable What is the result of this configuration?
|
A. |
The link is in a downstate. |
|
B. |
The link is in an error
disables state |
|
C. |
The link is becomes an access port. |
|
D. |
The link becomes a trunkport. |
Answer: D
Explanation:
Dynamic Auto - Makes the Ethernet port willing to convert the link to a trunk link. The port becomes a trunk port if the neighboring port is set to trunk or dynamic desirable mode. This is the default mode for some switchports.
Dynamic Desirable - Makes the port actively attempt to convert the link to a trunk link. The port becomes a trunk port if the neighboring Ethernet port is set to trunk, dynamic desirable or dynamic auto mode.
When configuring IPv6 on an interface, which two IPv6 multicast groups are joined?(Choose two)
|
A. |
2000::/3 |
|
B. |
2002::5 |
|
C. |
FC00::/7 |
|
D. |
FF02::1 |
|
E. |
FF02::2 |
Answer: DE
Explanation:
When an interface is configured with IPv6 address, it automatically joins the all nodes (FF02::1) and solicited-node (FF02::1:FFxx:xxxx) multicast groups. The all-node group is used to communicate with all interfaces on the local link, and the solicited-nodes multicast group is required for link-layer address resolution. Routers also join a third multicast group, the all-routers group (FF02::2).
Which MAC address is recognized as a VRRP virtual address?
|
A. |
0000.5E00.010a |
|
B. |
0005.3711.0975 |
|
C. |
0000.0C07.AC99 |
|
D. |
0007.C070/AB01 |
Answer:
A
Explanation:
With VRRP, the virtual router's MAC address is 0000.5E00.01xx , in which xx is the VRRP group.
in Which way does a spine and-leaf architecture allow for scalability in a network when additional access ports are required?
|
A. |
A spine switch
and a leaf switch can
be added with
redundant connections between them |
|
B. |
A spine switch
can be added
with at least
40 GB uplinks |
|
C. |
A leaf switch can be added
with a single
connection to a core spine
switch. |
|
D. |
A leaf switch
can be added
with connections to every spine
switch |
Answer: D
Explanation:
Spine-leaf architecture is typically deployed as two layers: spines (such as an aggregation layer), and leaves (such as an access layer). Spine-leaf topologies provide high-bandwidth, low-latency, nonblocking server-to-server connectivity.
Leaf (aggregation) switches are what provide devices access to the fabric (the network of spine and leaf switches) and are typically deployed at the top of the rack. Generally, devices connect to the leaf switches.
Devices can include servers, Layer 4-7 services (firewalls and load balancers), and WAN or Internet routers. Leaf switches do not connect to other leaf switches. In spine-and-leaf architecture, every leaf should connect to every spine in a full mesh.
Spine (aggregation) switches are used to connect to all leaf switches and are typically deployed at the end or middle of the row. Spine switches do not connect to other spine switches.
Reference: https://www.cisco.com/c/en/us/products/collateral/switches/nexus-9000-series- switches/guide- c07-733228.html
Which type of wireless encryption is used for WPA2 in pre-shared key mode?
|
A. |
TKIP with RC4 |
|
B. |
RC4 |
|
C. |
AES-128 |
|
D. |
AES-256 |
Answer: D
Explanation:
We can see in this picture we have to type 64 hexadecimal characters (256 bit) for the WPA2 passphrase so we can deduce the encryption is AES-256, not AES-128.
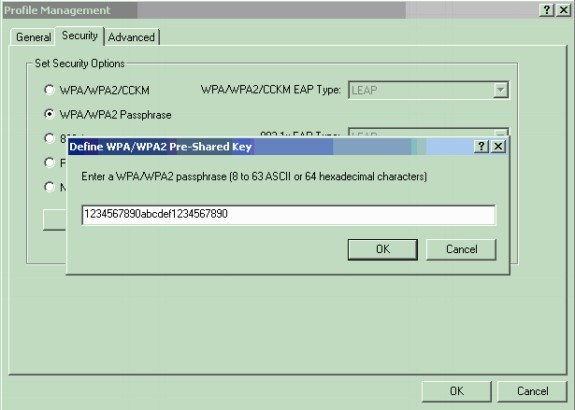
Reference: https://www.cisco.com/c/en/us/support/docs/wireless-mobility/wireless-lan- wlan/67134-wpa2-config.html
What makes Cisco DNA Center different from traditional network management applications and their management of networks?
|
A. |
It only supports auto-discovery of network
elements in a green field
deployment. |
|
B. |
It modular
design allows someone to implement different versions to meet
the specific needs
of an organization |
|
C. |
It abstracts policy from
the actual device
configuration |
|
D. |
It does not support high
availability of management functions when operating in cluster mode |
Answer: C
Explanation:
Automation: Using controllers and open APIs, Cisco DNA simplifies network management through abstraction and centralized policy enforcement that allows IT to focus on business intent and consistently apply configurations to improve service and keep operations consistently secure from the core to the edge.
https://www.cisco.com/c/en/us/solutions/collateral/enterprise-networks/digital-network- architecture/nb-06-digital-nw-architect-faq-cte-en.html
Which two actions are performed by the Weighted Random Early Detection mechanism? (Choose two)
|
A. |
It drops lower-priority packets before it drops higher-priority packets |
|
B. |
It can identify different flows with a high level
of granularity |
|
C. |
It guarantees the delivery of high-priority packets |
|
D. |
It can mitigate congestion by preventing the queue from filling up |
|
E. |
It supports protocol discovery |
Answer:
AD
Explanation:
Weighted Random Early Detection (WRED) is just a congestion avoidance mechanism. WRED drops packets selectively based on IP precedence. Edge routers assign IP precedences to packets as they enter the network. When a packet arrives, the following events occur:
1. The average queue size is calculated.
2. If the average is less than the minimum
queue threshold, the arriving packet
is queued.
3. If the average is between
the minimum queue threshold for that type of traffic and the maximum threshold for the interface, the packet is either dropped
or queued, depending
on the packet drop
probability for that type of traffic.
4. If the average queue size is
greater than the maximum threshold, the packet is dropped. WRED reduces the
chances of tail drop (when the queue is full, the packet is dropped) by
selectively dropping packets
when the output
interface begins to show signs
of congestion (thus
it can mitigate congestion by
preventing the queue from filling
up). By dropping some packets early rather than waiting until the queue
is full, WRED avoids dropping large numbers of packets at once and minimizes
the chances of global synchronization. Thus,
WRED allows the transmission line to be used fully at all times.
WRED generally drops packets selectively based on IP precedence. Packets with a higher IP precedence are less likely to be dropped than packets with a lower precedence. Thus, the higher the priority of a packet, the higher the probability that the packet will be delivered (-> answer A is correct).
Reference: https://www.cisco.com/c/en/us/td/docs/ios-xml/ios/qos_conavd/configuration/15- mt/qos- conavd-15-mt-book/qos-conavd-cfg-wred.html
A network engineer must back up 20 network router configurations globally within a customer environment.
Which protocol allows the engineer to perform this function using the Cisco IOS MIB?
|
A. |
CDP |
|
B. |
SNMP |
|
C. |
SMTP |
|
D. |
ARP |
Answer:
B
Explanation:
SNMP is an application-layer protocol that provides a message format for communication between SNMP managers and agents. SNMP provides a standardized framework and a common language used for the monitoring and management of devices in a network.
The SNMP framework has three parts:
+ An SNMP manager
+ An SNMP agent
+ A Management Information Base (MIB)
The Management Information Base (MIB) is a virtual information storage area for network management information, which consists of collections of managed objects.
With SNMP, the network administrator can send commands to multiple routers to do the backup.
Refer to the exhibit. An engineer is bringing up a new circuit to the MPLS provider on the Gi0/1 interface of Router1.
The new circuit uses eBGP and teams the route to VLAN25 from the BGP path. What is the expected behavior for the traffic flow for route 10.10.13.0/25?
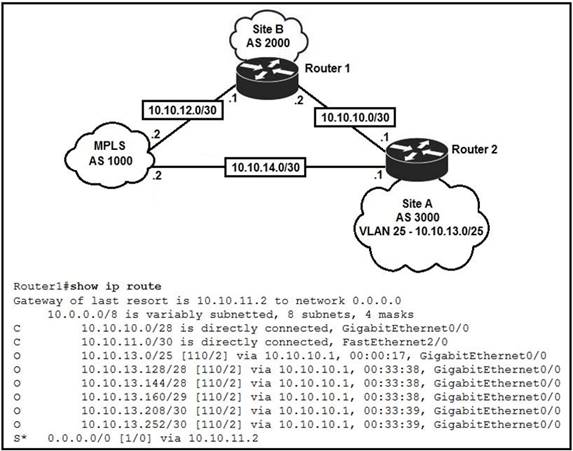
|
A. |
Traffic to 10.10.13.0.25 is load balanced out of multiple interfaces |
|
B. |
Route 10.10.13.0/25 is updated in the routing
table as being
learned from interface Gi0/1. |
|
C. |
Traffic to 10.10.13.0/25 is a symmetrical |
|
D. |
Route 10.10.13.0/25 learned via the GiO/0
interface remains in the routing
table |
Answer: B
Explanation:
You need to assume that the routing table listed is before the change. And that the eBGP route will be the installed route after the change due to lower AD.
The new eBGP route will be added to the routing table. eBGP has an administrative distance of 20 while OSPF has an administrative distance of 110. The new route will be preferred for sending traffic to 10.10.13.0/25. The existing OSPF route will turn into a floating route and not appear in the routing table.
Which action is taken by a switch port enabled for PoE power classification override?
|
A. |
When a powered device begins drawing power from a PoE switch
port a syslog
message is generated |
|
B. |
As power usage
on a PoE switch port is checked
data flow to the connected device is temporarily paused |
|
C. |
If a switch determines that a device
is using less than the minimum configured power it assumes the device has failed and
disconnects |
|
D. |
If a monitored port
exceeds the maximum administrative value for power, the
port is shutdown and err-disabled |
Answer: D
Explanation:
PoE monitoring and policing compares the power consumption on ports with the administrative maximum value (either a configured maximum value or the port's default value). If the power consumption on a monitored port exceeds the administrative maximum value, the following actions occur:
-
A syslog message
is issued.
-
The monitored port is shut down and error-disabled.
- The allocated power is freed.
Reference: https://www.cisco.com/c/en/us/td/docs/switches/lan/catalyst6500/ios/12- 2SX/configuration/ guide/book/power_over_ethernet.pdf
Refer to the exhibit. Which type of route does R1 use to reach host 10.10.13.10/32?
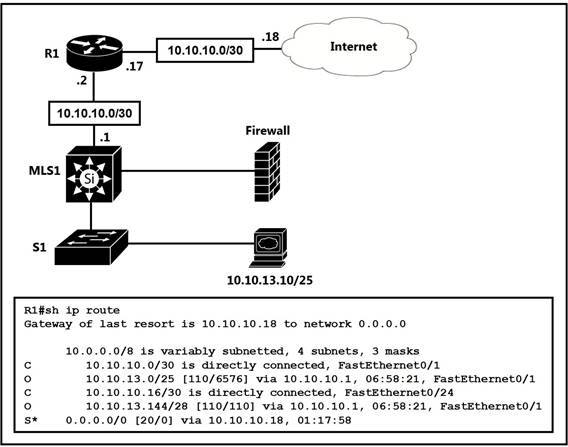
|
A. |
floating static route |
|
B. |
host route |
|
C. |
default route |
|
D. |
network route |
Answer: D
Explanation:
From the output, we see R1 will use the entry "O 10.10.13.0/25 [110/4576] via 10.10.10.1, ..." to reach host 10.10.13.10. This is a network route.
Note: "B* 0.0.0.0/0 ..." is a default route.
Which mode must be used to configure EtherChannel between two switches without using a negotiation protocol?
|
A. |
on |
|
B. |
auto |
|
C. |
active |
|
D. |
desirable |
Answer:
A
Explanation:
The Static Persistence (or "on" mode) bundles the links unconditionally and no negotiation protocol is used. In this mode, neither PAgP nor LACP packets are sent or received.
An engineer configured an OSPF neighbor as a designated router. Which state verifies the designated router is in the proper mode?
|
A. |
Exchange |
|
B. |
2-way |
|
C. |
Full |
|
D. |
Init |
Answer: C
Explanation:
Full is the state for adjacent routers that have fully synchronised databases.
Which configuration is needed to generate an RSA key for SSH on a router?
|
A. |
Configure the version
of SSH |
|
B. |
Configure VTY
access. |
|
C. |
Create a user with a password. |
|
D. |
Assign a DNS domain name |
Answer: D
Explanation:
In order to generate an RSA key for SSH, we need to configure the hostname and a DNS domain
name on the router (a username and password is also required). Therefore in fact both answer C and answer D are correct.
An organization has decided to start using cloud-provided services. Which cloud service allows the organization to install its own operating system on a virtual machine?
|
A. |
platform-as-a-service |
|
B. |
software-as-a-service |
|
C. |
network-as-a-service |
|
D. |
infrastructure-as-a-service |
Answer: D
Explanation:
Below are the 3 cloud supporting services cloud providers provide to customer:
+ SaaS (Software as a Service): SaaS uses the web to deliver applications that are managed by a third- party vendor and whose interface is accessed on the clients' side. Most SaaS applications can be run directly from a web browser without any downloads or installations required, although some require plugins.
+ PaaS (Platform as a Service): are used for applications, and other development, while providing cloud components to software. What developers gain with PaaS is a framework they can build upon to develop or customize applications. PaaS makes the development, testing, and deployment of applications quick, simple, and cost-effective. With this technology, enterprise operations, or a third-party provider, can manage OSes, virtualization, servers, storage, networking, and the PaaS software itself. Developers, however, manage the applications.
+ IaaS (Infrastructure as a Service): self-service models for accessing, monitoring, and managing remote datacenter infrastructures, such as compute (virtualized or bare metal), storage, networking, and networking services (e.g. firewalls). Instead of having to purchase hardware outright, users can purchase IaaS based on consumption, similar to electricity or other utility billing.
In general, IaaS provides hardware so that an organization can install their own operating system.
Refer to Exhibit. Which action do the switches take on the trunk link?
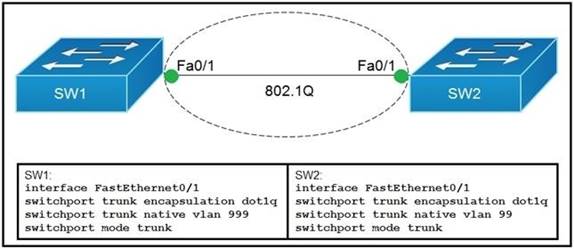
|
A. |
The trunk does not form
and the ports
go into an err-disabled status. |
|
B. |
The trunk forms
but the mismatched native VLANs are
merged into a single broadcast domain. |
|
C. |
The trunk does not form, but VLAN 99 and VLAN 999 are allowed to traverse the link. |
|
D. |
The trunk forms
but VLAN 99 and VLAN 999 are in a shutdown state. |
Answer: B
Explanation:
The trunk still forms with mismatched native VLANs and the traffic can actually flow between mismatched switches. But it is absolutely necessary that the native VLANs on both ends of a trunk link match; otherwise a native VLAN mismatch occurs, causing the two VLANs to effectively merge. For example with the above configuration, SW1 would send untagged frames for VLAN 999. SW2 receives them but would think they are for VLAN 99 so we can say these two VLANs are merged.
Which design element is a best practice when deploying an 802.11b wireless infrastructure?
|
A. |
disabling TPC so that access
points can negotiate signal levels with
their attached wireless devices. |
|
B. |
setting the maximum data rate to 54 Mbps
on the Cisco
Wireless LAN Controller |
|
C. |
allocating non
overlapping channels to access points
that are in close physical proximity to one another |
|
D. |
configuring access points
to provide clients
with a maximum
of 5 Mbps |
Answer: C
Explanation:
Selecting the proper WiFi channel can significantly improve your WiFi coverage and performance. In the 2.4 GHz band, 1, 6, and 11 are the only non-overlapping channels. Selecting one or more of these channels is an important part of setting up your network correctly.
Refer to the exhibit. If OSPF is running on this network, how does Router 2 handle traffic from Site B to 10.10.13.128/25 at Site A?
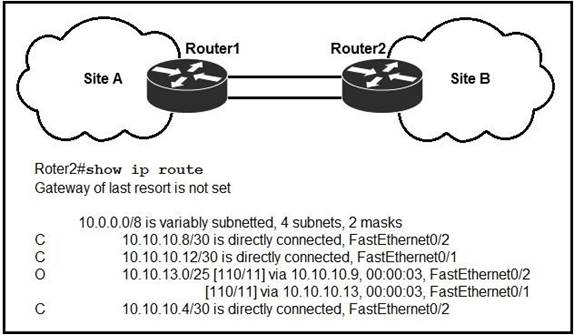
|
A. |
It sends packets
out of interface Fa0/2 only. |
|
B. |
It sends packets out of interface Fa0/1 only. |
|
C. |
It cannot send packets
to 10.10.13.128/25 |
|
D. |
It load-balances traffic
out of Fa0/1
and Fa0/2 |
Answer: C
Explanation:
Router2 does not have an entry for the subnet 10.10.13.128/25. It only has an entry for 10.10.13.0/25, which ranges from 10.10.13.0 to 10.10.13.127.
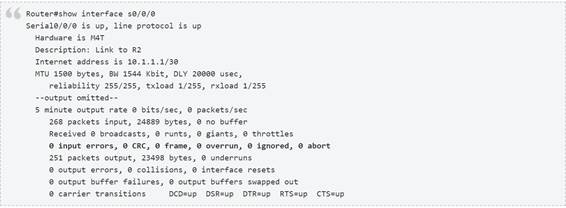
A frame that enters a switch fails the Frame Check Sequence. Which two interface counters are incremented? (Choose two)
|
A. |
runts |
|
B. |
giants |
|
C. |
frame |
|
D. |
CRC |
|
E. |
input errors |
Answer: DE
Explanation:
Whenever the physical transmission has problems, the receiving device might receive a frame whose bits have changed values. These frames do not pass the error detection logic as implemented in the FCS field in the Ethernet trailer. The receiving device discards the frame and counts it as some kind of input error.
Cisco switches list this error as a CRC error. Cyclic redundancy check (CRC) is a term related to how the FCS math detects an error.
The "input errors" includes runts, giants, no buffer, CRC, frame, overrun, and ignored counts. The output below show the interface counters with the "show interface s0/0/0" command:
Which two conditions must be met before SSH operates normally on a Cisco IOS switch? (Choose two.)
|
A. |
The switch must
be running a k9 (crypto) IOS image |
|
B. |
The Ip domain-name command
must be configured on the switch |
|
C. |
IP routing must be enabled on the switch |
|
D. |
A console password must
be configured on the switch |
|
E. |
Telnet must be disabled on the switch |
Answer: AB
Explanation:
The Cisco IOS image used must be a k9(crypto) image in order to support SSH. Step 2: Configure the DNS domain of the router.
ip domain-name rtp.cisco.com
Refer to the exhibit. If configuring a static default route on the router with the ip route 0.0.0.0
0.0.0.0 10.13.0.1 120 command, how does the router respond?
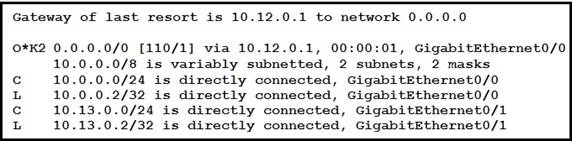
|
A. |
It ignores the new static
route until the
existing OSPF default route is removed |
|
B. |
It immediately replaces the existing OSPF
route in the
routing table with
the newly configured static route |
|
C. |
It starts load-balancing traffic between the two default
routes |
|
D. |
It starts sending traffic without a specific matching entry in the
routing table to Gigabit EthernetO/1 |
Answer: A
Explanation:
Our new static default route has the Administrative Distance (AD) of 120, which is bigger than the AD of OSPF External route (O*E2) so it will not be pushed into the routing table until the current OSPF External route is removed.
For your information, if you don't type the AD of 120 (using the command "ip route 0.0.0.0 0.0.0.0 10.13.0.1") then the new static default route would replace the OSPF default route as the default AD of static route is 1. You will see such line in the routing table:
S* 0.0.0.0/0 [1/0] via 10.13.0.1
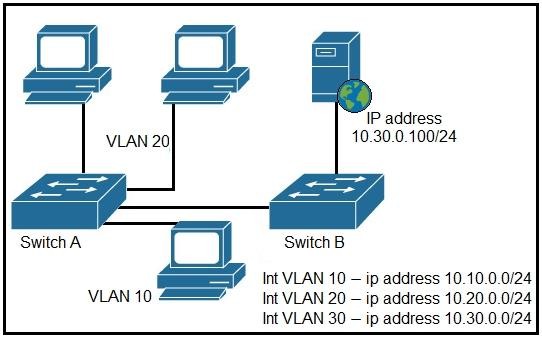
Refer to the exhibit. A network engineer must block access for all computers on VLAN 20 to the web server via HTTP. All other computers must be able to access the web server. Which configuration when applied to switch A accomplishes this task?
|
A. |
|
|
B. |
|
|
C. |
|
|
D. |
|
Answer: D
A router running EIGRP has learned the same route from two different paths. Which parameter does the router use to select the best path?
|
A. |
cost |
|
B. |
administrative distance |
|
C. |
metric |
|
D. |
as-path |
Answer: C
Explanation:
If a router learns two different paths for the same network from the same routing protocol, it has to decide which route is better and will be placed in the routing table. Metric is the measure used to decide which route is better (lower number is better). Each routing protocol uses its own metric. For example, RIP uses hop counts as a metric, while OSPF uses cost.
https://study-ccna.com/administrative-distance-metric/
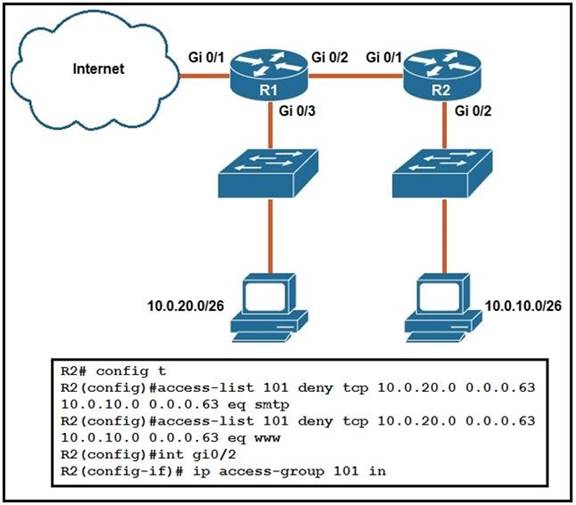
Refer to the exhibit. An extended ACL has been configured and applied to router R2. The configuration failed to work as intended.
Which two changes stop outbound traffic on TCP ports 25 and 80 to 10.0.20.0/26 from the 10.0.10.0/26 subnet while still allowing all other traffic? (Choose two.)
|
A. |
Add a "permit ip any any" statement to the
beginning of ACL 101 for allowed traffic. |
|
B. |
Add a "permit ip any any" statement at the end of ACL 101 for allowed traffic |
|
C. |
The source and destination IPs must be swapped in ACL 101 |
|
D. |
The ACL must be configured the Gi0/2 interface in bound on R1 |
|
E. |
The ACL must
be moved to the Gi0/1interface outbound onR2 |
Answer: BC
What is the primary different between AAA authentication and authorization?
|
A. |
Authentication
verifies a username and password, and
authorization handles the communication between the authentication agent
and the user
database. |
|
B. |
Authentication identifies a user who is attempting to access a system, and authorization validates the users password |
|
C. |
Authentication identifies and
verifies a user
who is attempting to access a system, and authorization controls the tasks the
user can perform. |
|
D. |
Authentication controls the system processes a user can
access and authorization logs the
activities the user initiates |
Answer: C
Explanation:
AAA stands for Authentication, Authorization and Accounting.
+ Authentication: Specify who you are (usually via login username & password) + Authorization: Specify what actions you can do, what resource you can access + Accounting: Monitor what you do, how long you do it (can be used for billing and auditing) An example of AAA is shown below:
+ Authentication: "I am a normal user. My username/password is user_tom/learnforever" + Authorization: "user_tom can access LearnCCNA server via HTTP and FTP" + Accounting: "user_tom accessed LearnCCNA server for 2 hours". This user only uses "show" commands.
When a floating static route is configured, which action ensures that the backup route is used when the primary route fails?
|
A. |
The floating static
route must have
a higher administrative distance than the
primary route so it is used as a
backup |
|
B. |
The administrative distance must be higher on the primary route so that
the backup route becomes secondary. |
|
C. |
The floating static
route must have a lower
administrative distance than the primary route so it is
used as a backup |
|
D. |
The default-information originate command must be configured for the route
to be installed into the
routing table |
Answer: A
Explanation:
By default, IOS considers static routes better than OSPF-learned routes. By default, IOS gives static routes an administrative distance of 1 A floating static route floats or moves into and out of the IP routing table depending on whether the better (lower) administrative distance route learned by the routing protocol happens to exist currently.
Which two outcomes are predictable behaviors for HSRP? (Choose two)
|
A. |
The two routers
share a virtual IP address that
is used as the default
gateway for devices
on the LAN. |
|
B. |
The two routers negotiate one router as the active
router and the other as the standby
router |
|
C. |
Each router
has a different IP address both routers act as the default gateway
on the LAN,
and traffic is load balanced between them. |
|
D. |
The two routers synchronize configurations to provide consistent packet forwarding |
|
E. |
The two
routed share the
same IP address, and default gateway traffic is load-balanced between them |
Answer: AB
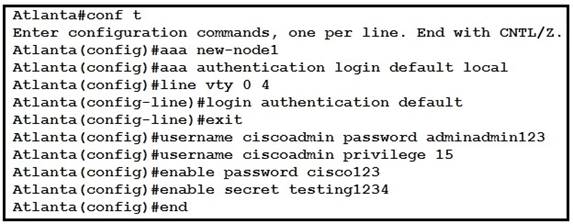
Refer to the exhibit. Which password must an engineer use to enter the enable mode?
|
A. |
adminadmin123 |
|
B. |
default |
|
C. |
testing1234 |
|
D. |
cisco123 |
Answer: C
Explanation:
If neither the enable password command nor the enable secret command is configured, and if there is a line password configured for the console, the console line password serves as the enable password for all VTY sessions -> The "enable secret" will be used first if available, then "enable password" and line password.
Reference: https://www.cisco.com/c/en/us/td/docs/optical/cpt/r9_3/configuration/guide/cpt93_configuration/ cpt93_configuration_chapter_0100
How do TCP and UDP differ in the way that they establish a connection between two endpoints?
|
A. |
TCP uses synchronization packets, and UDP uses acknowledgment packets. |
|
B. |
UDP uses
SYN,SYN ACK and
FIN bits in the frame
header while TCP
uses SYN,SYN ACK
and ACK bits |
|
C. |
UDP provides reliable message
transfer and TCP is a connectionless protocol |
|
D. |
TCP uses the
three-way handshake and
UDP does not guarantee message delivery |
Answer: D
When a site-to-site VPN is used, which protocol is responsible for the transport of user data?
|
A. |
IKEv2 |
|
B. |
IKEv1 |
|
C. |
IPsec |
|
D. |
MD5 |
Answer: C
Explanation:
A site-to-site VPN allows offices in multiple fixed locations to establish secure connections with each other over a public network such as the Internet. A site-to-site VPN means that two sites create a VPN tunnel by encrypting and sending data between two devices. One set of rules for creating a site-to-site VPN is defined by IPsec.
What is the primary effect of the spanning-tree port fast command?
|
A. |
it enables BPDU
messages |
|
B. |
It minimizes spanning-tree convergence time |
|
C. |
It immediately puts the port into
the forwarding state
when the switch
is reloaded |
|
D. |
It immediately enables
the port in the listening state |
Answer: B
Explanation:
The purpose of Port Fast is to minimize the time interfaces must wait for spanning-tree to converge, it is effective only when used on interfaces connected to end stations. https://www.cisco.com/c/en/us/td/docs/switches/lan/catalyst3560/software/release/12- 2_55_se/configuration/guide/3560_scg/swstpopt.html
How will Link Aggregation be implemented on a Cisco Wireless LAN Controller?
|
A. |
To pass client
traffic two or more ports
must be configured. |
|
B. |
The EtherChannel must be configured in "mode active" |
|
C. |
When enabled the
WLC bandwidth drops
to 500 Mbps |
|
D. |
One functional physical port is needed
to pass client
traffic |
Answer: D
Explanation:
Link aggregation (LAG) is a partial implementation of the 802.3ad port aggregation standard. It bundles all of the controller's distribution system ports into a single 802.3ad port channel.
Restriction for Link aggregation:
-
LAG requires the EtherChannel to be configured for `mode on' on both the controller and the Catalyst
switch -> Answer B is not correct.
-
If the recommended load-balancing method cannot be configured on the
Catalyst switch, then configure the LAG connection as a single member link or disable
LAG on the controller -> Answer
A is not correct while answer D is correct.
Reference: https://www.cisco.com/c/en/us/td/docs/wireless/controller/7-5/configuration- guide/b_cg75/ b_cg75_chapter_0100010.html
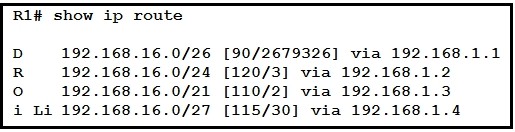
Refer to the exhibit. Which route does R1 select for traffic that is destined to 192 168.16.2?
|
A. |
192.168.16.0/21 |
|
B. |
192.168.16.0/24 |
|
C. |
192.168 26.0/26 |
|
D. |
192.168.16.0/27 |
Answer: D
Explanation:
The destination IP addresses match all four entries in the routing table but the 192.168.16.0/27 has the longest prefix so it will be chosen. This is called the "longest prefix match" rule.
Which two tasks must be performed to configure NTP to a trusted server in client mode on a single network device? (Choose two)
|
A. |
Enable NTP authentication. |
|
B. |
Verify the time zone. |
|
C. |
Disable
NTP broadcasts |
|
D. |
Specify the IP address
of the NTP
server |
|
E. |
Set the NTP
server private key |
Answer:
AD
Explanation:
To configure authentication, perform this task in privileged mode:
Step 1: Configure an authentication key pair for NTP and specify whether the key will be trusted or untrusted.
Step 2: Set the IP address of the NTP server and the public key. Step 3: Enable NTP client mode.
Step 4: Enable NTP authentication. Step 5: Verify the NTP configuration.
Reference: https://www.cisco.com/c/en/us/td/docs/switches/lan/catalyst4000/8- 2glx/configuration/guide/ntp.html
Refer to the exhibit. Which command provides this output?
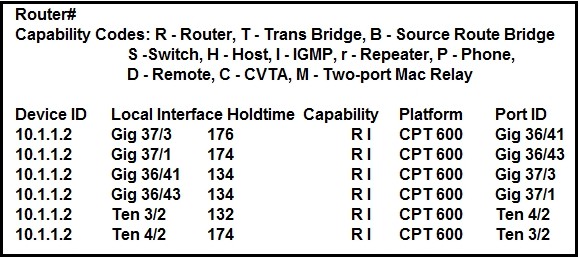
|
A. |
show ip route |
|
B. |
show ip
interface |
|
C. |
show interface |
|
D. |
show cdp neighbor |
Answer: D
Which set of action satisfy the requirement for multi-factor authentication?
|
A. |
The user swipes
a key fob, then clicks
through an email
link |
|
B. |
The user enters
a user name
and password, and then clicks
a notification in an authentication app on a mobile device |
|
C. |
The user enters a PIN into an RSA
token, and then enters the displayed RSA key on a login screen |
|
D. |
The user
enters a user
name and password and then re-enters the credentials on a second screen |
Answer:
B
Explanation:
This is an example of how two-factor authentication (2FA) works:
1. The user logs in to the website or service with their username
and password.
2. The password is validated
by an authentication server and, if correct,
the user becomes
eligible for the second factor.
3. The authentication server sends
a unique code to the user's second-factor method (such as a
smartphone app).
4. The user confirms their
identity by providing the additional authentication for their second-factor method.
Which mode allows access points to be managed by Cisco Wireless LAN Controllers?
|
A. |
autonomous |
|
B. |
lightweight |
|
C. |
bridge |
|
D. |
mobility express |
Answer: B
Explanation:
A Lightweight Access Point (LAP) is an AP that is designed to be connected to a wireless LAN (WLAN) controller (WLC). APs are "lightweight," which means that they cannot act independently of a wireless LAN controller (WLC). The WLC manages the AP configurations and firmware. The APs are "zero touch" deployed, and individual configuration of APs is not necessary.
Reference: https://www.cisco.com/c/en/us/support/docs/wireless/aironet-1200-series/70278-lap- faq.html
Router A learns the same route from two different neighbors, one of the neighbor routers is an OSPF neighbor and the other is an EIGRP neighbor.
What is the administrative distance of the route that will be installed in the routing table?
|
A. |
20 |
|
B. |
90 |
|
C. |
110 |
|
D. |
115 |
Answer:
B
Explanation:
The Administrative distance (AD) of EIGRP is 90 while the AD of OSPF is 110 so EIGRP route will be chosen to install into the routing table.
Refer to the exhibit. What is the effect of this configuration?

|
A. |
The switch port
interface trust state
becomes untrusted |
|
B. |
The switch port remains
administratively down until
the interface is connected to another switch |
|
C. |
Dynamic ARP inspection is disabled because
the ARP ACL is missing |
|
D. |
The switch port
remains down until
it is configured to trust or untrust incoming packets |
Answer: A
Explanation:
Dynamic ARP inspection (DAI) is a security feature that validates ARP packets in a network. It intercepts, logs, and discards ARP packets with invalid IP-to-MAC address bindings. This capability protects the network from certain man-in-the-middle attacks. After enabling DAI, all ports become untrusted ports.
Refer to the exhibit. Which prefix does Router1 use for traffic to Host A?
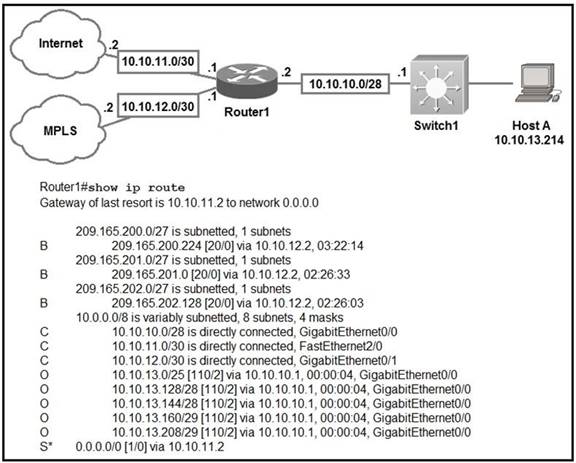
|
A. |
10.10.10.0/28 |
|
B. |
10.10.13.0/25 |
|
C. |
10.10.13.144/28 |
|
D. |
10.10.13.208/29 |
Answer: D
Explanation:
Host A address fall within the address range. However, if more than one route to the same subnet exist (router will use the longest stick match, which match more specific route to the subnet). If there are route 10.10.13.192/26 and 10.10.13.208/29, the router will forward the packet to /29 rather than /28.
What are two characteristics of a controller-based network? (Choose two)
|
A. |
The administrator can
make configuration updates from the CLI |
|
B. |
It uses northbound and southbound APIs
to communicate between architectural layers |
|
C. |
It moves the control
plane to a central point. |
|
D. |
It decentralizes the
control plane, which
allows each device
to make its
own forwarding decisions |
|
E. |
It uses Telnet
to report system
issues. |
Answer: BC
Explanation:
controller-based networking - A style of building computer networks that use a controller that centralizes some features and provides application programming interfaces (APIs) that allow for software interactions between applications and the controller (northbound APIs) and between the controller and the network devices (southbound APIs).
centralized control plane - An approach to architecting network protocols and products that places the control plane functions into a centralized function rather than distributing the function across the networking devices.
Refer to exhibit. Which statement explains the configuration error message that is received?
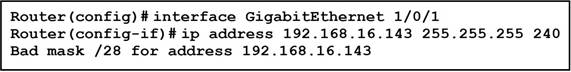
|
A. |
It is a broadcast IP address |
|
B. |
The router does not support /28
mask. |
|
C. |
It belongs to a private IP address range. |
|
D. |
IT is a network IP
address. |
Answer: A
Explanation:
For /28 network, There (2^4)=16 Subnets with each having (2^4-2)=14 host (14 +1 Network ID+ 1Broadcast ID)=16
Subnets are 192.168.16.0
192.168.16.16
..... 192.168.16.128
192.168.16.144 (Above this network ID there will be address 192.168.16.143 which is a broadcast ID of Network 192.168.16.128
Drag and Drop Question
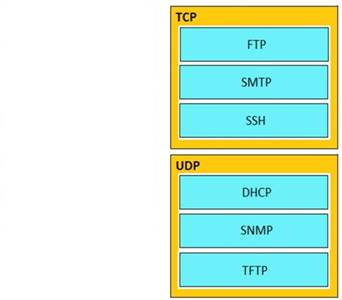
Drag and drop the application protocols from the left onto the transport protocols that is uses on the right.
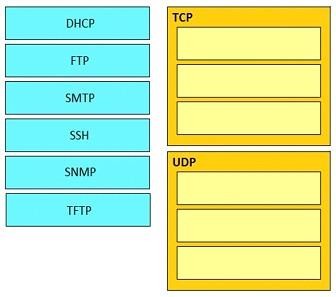
Answer:
Which command must you enter to guarantee that an HSRP router with higher priority becomes the HSRP primary router after it is reloaded?
|
A. |
standby 10 preempt |
|
B. |
standby 10 version 1 |
|
C. |
standby 10 priority 150 |
|
D. |
standby 10 version
2 |
Answer: A
Explanation:
The "preempt" command enables the HSRP router with the highest priority to immediately become the active router.
Which command should you enter to verify the priority of a router in an HSRP group?
|
A. |
show hsrp |
|
B. |
show sessions |
|
C. |
show interfaces |
|
D. |
show standby |
Answer: D
Explanation:
The following is sample output from the show standby command:
![]()
Which command should you enter to configure a device as an NTP sever?
|
A. |
ntp sever |
|
B. |
ntp peer |
|
C. |
ntp authenticate |
|
D. |
ntp master |
Answer: D
Explanation:
To configure a Cisco device as an Authoritative NTP Server, use the ntp master [stratum] command.
To configure a Cisco device as a NTP client, use the command ntp server <IP address>. For example:
Router(config)#ntp server 192.168.1.1. This command will instruct the router to query 192.168.1.1 for the time.
Which two pieces of information can you determine from the output of the show ntp status command? (Choose two)
|
A. |
whether the NTP peer is statically configured |
|
B. |
the IP address of the peer
to which the clock is synchronized |
|
C. |
the configured NTP servers |
|
D. |
whether the clock is
synchronized |
|
E. |
the NTP version number of the peer |
Answer:
BD
Explanation:
Below is the output of the "show ntp status" command. From this output we learn that R1 has a stratum of 10 and it is getting clock from 10.1.2.1.
![]()
Which effete does the aaa new-model configuration command have?
|
A. |
It enables AAA
services on the
device |
|
B. |
It configures the device
to connect to a RADIUS
server for AAA |
|
C. |
It associates a RADIUS
server to an group. |
|
D. |
It configures a local user
on the device. |
Answer:
A
Refer to the exhibit. Which command would you use to configure a static route on Router1 to network 192.168.202.0/24 with a nondefault administrative distance?
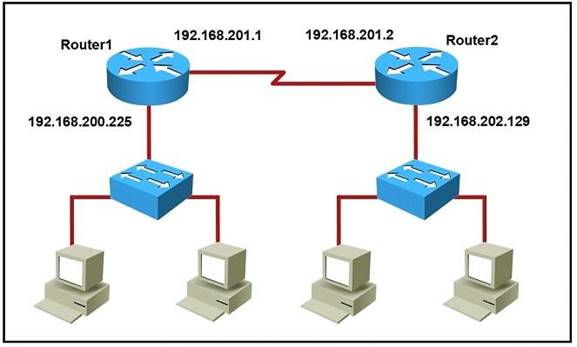
|
A. |
router1(config)#ip route
192.168.202.0 255.255.255.0 192.168.201.2 1 |
|
B. |
router1(config)#ip route 192.168.202.0 255.255.255.0 192.168.201.2 5 |
|
C. |
router1(config)#ip route
1 192.168.201.1 255.255.255.0 192.168.201.2 |
|
D. |
router1(config)#ip route
5 192.168.202.0 255.255.255.0 192.168.201.2 |
Answer: B
Explanation:
The default AD of static route is 1 so we need to configure another number for the static route.
What is the destination MAC address of a broadcast frame?
|
A. |
00:00:0c:07:ac:01 |
|
B. |
ff:ff:ff:ff:ff:ff |
|
C. |
43:2e:08:00:00:0c |
|
D. |
00:00:0c:43:2e:08 |
|
E. |
00:00:0c:ff:ff:ff |
Answer: B
Which command is used to enable LLDP globally on a Cisco IOS ISR?
|
A. |
lldp run |
|
B. |
lldp enable |
|
C. |
lldp transmit |
|
D. |
cdp run |
|
E. |
cdp enable |
Answer:
A
Explanation:
Link Layer Discovery Protocol (LLDP) is a industry standard protocol that allows devices to advertise, and discover connected devices, and there capabilities (same as CDP of Cisco). To enable it on Cisco devices, we have to use this command under global configuration mode: Sw(config)# lldp run
Which of the following dynamic routing protocols are Distance Vector routing protocols?
|
A. |
IS-IS |
|
B. |
EIGRP |
|
C. |
OSPF |
|
D. |
BGP |
|
E. |
RIP |
Answer: BE
Explanation:
EIGRP is sometimes referred to as a hybrid routing protocol because it has characteristics of both distance-vector and link-state protocols. For example, EIGRP doesn’t send link-state packets as OSPF does; instead, it sends traditional distance-vector updates containing information about networks plus the cost of reaching them from the perspective of the advertising router. And EIGRP has link-state characteristics as well—it synchronizes routing tables between neighbors at startup and then sends specific updates only when topology changes occur. This makes EIGRP suitable for very large networks. EIGRP has a maximum hop count of 255 (the default is set to 100).
You have configured a router with an OSPF router ID, but its IP address still reflects the physical interface. Which action can you take to correct the problem in the least disruptive way?
|
A. |
Reload the OSPF
process. |
|
B. |
Specify a loopback address |
|
C. |
Reboot the router. |
|
D. |
Save the router
configuration |
Answer:
A
Explanation:
Once an OSPF Router ID selection is done, it remains there even if you remove it or configure another OSPF Router ID. So the least disruptive way is to correct it using the command “clear ip ospf process”.
Drag and Drop Question
Drag and drop the benefits of a cisco wireless Lan controller from the left onto the correct examples on the right.
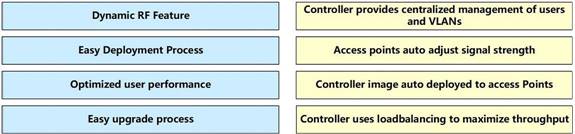
Answer:
![]()
Which command should you enter to configure an LLDP delay time of 5 seconds?
|
A. |
lldp timer 5000 |
|
B. |
lldp holdtime 5 |
|
C. |
lldp reinit
5000 |
|
D. |
lldp reinit 5 |
Answer: D
Explanation:
+ lldp holdtime seconds: Specify the amount of time a receiving device should hold the information from your device before discarding it
+ lldp reinit delay: Specify the delay time in seconds for LLDP to initialize on an interface
+ lldp timer rate: Set the sending frequency of LLDP updates in seconds Reference: https://www.cisco.com/c/en/us/td/docs/switches/lan/catalyst3560/software/release/12-2_55_se/ configuration/guide/3560_scg/swlldp.html
Which keyword in a NAT configuration enables the use of one outside IP address for multiple inside hosts?
|
A. |
source |
|
B. |
static |
|
C. |
pool |
|
D. |
overload |
Answer: D
Explanation:
By adding the keyword "overload" at the end of a NAT statement, NAT becomes PAT (Port Address Translation). This is also a kind of dynamic NAT that maps multiple private IP addresses to a single public IP address (many-to-one) by using different ports. Static NAT and Dynamic NAT
both require a one-to-one mapping from the inside local to the inside global address. By using PAT, you can have thousands of users connect to the Internet using only one real global IP address. PAT is the technology that helps us not run out of public IP address on the Internet. This is the most popular type of NAT.
An example of using "overload" keyword is shown below:
R1(config)# ip nat inside source list 1 interface ethernet1 overload
Which unified access point mode continues to serve wireless clients after losing connectivity to the Cisco Wireless LAN Controller?
|
A. |
sniffer |
|
B. |
mesh |
|
C. |
flex connect |
|
D. |
local |
Answer: C
Explanation:
In previous releases, whenever a FlexConnect access point disassociates from a controller, it moves to the standalone mode. The clients that are centrally switched are disassociated.
However, the FlexConnect access point continues to serve locally switched clients. When the FlexConnect access point rejoins the controller (or a standby controller), all clients are disconnected and are authenticated again. This functionality has been enhanced and the connection between the clients and the FlexConnect access points are maintained intact and the clients experience seamless connectivity. When both the access point and the controller have the same configuration, the connection between the clients and APs is maintained.
Reference: https://www.cisco.com/c/en/us/td/docs/wireless/controller/7-4/configuration/guides/ consolidated/b_cg74_CONSOLIDATED/b_cg74_CONSOLIDATED_chapter_010001101.html
Which QoS Profile is selected in the GUI when configuring a voice over WLAN deployment?
|
A. |
Bronze |
|
B. |
Platinum |
|
C. |
Silver |
|
D. |
Gold |
Answer:
B
Explanation:
Cisco Unified Wireless Network solution WLANs support four levels of QoS: Platinum/Voice, Gold/Video, Silver/Best Effort (default), and Bronze/Background.
Reference: https://www.cisco.com/c/en/us/td/docs/wireless/controller/7-4/configuration/guides/ consolidated/b_cg74_CONSOLIDATED/b_cg74_CONSOLIDATED_chapter_01010111.html
Refer to the exhibit. With which metric was the route to host 172.16.0.202 learned?
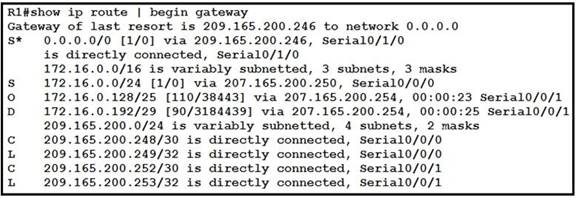
|
A. |
0 |
|
B. |
110 |
|
C. |
38443 |
|
D. |
3184439 |
Answer: C
Explanation:
Both the line "O 172.16.0.128/25" and "S 172.16.0.0/24" cover the host 172.16.0.202 but with the "longest (prefix) match" rule the router will choose the first route.
When OSPF learns multiple paths to a network, how does it select a route?
|
A. |
It multiple the active K value by 256 to calculate the route with
the lowest metric. |
|
B. |
For each existing interface, it adds
the metric from
the source router
to the destination to calculate the
route with the lowest bandwidth. |
|
C. |
It divides a reference bandwidth of 100 Mbps by the actual bandwidth of the existing interface to
calculate the router with the lowest cost. |
|
D. |
It count
the umber of hops between
the source router
and the destination to determine the router
with the lowest metric |
Answer: C
Refer to the Exhibit. After the switch configuration the ping test fails between PC A and PC B Based on the output for switch 1. Which error must be corrected?
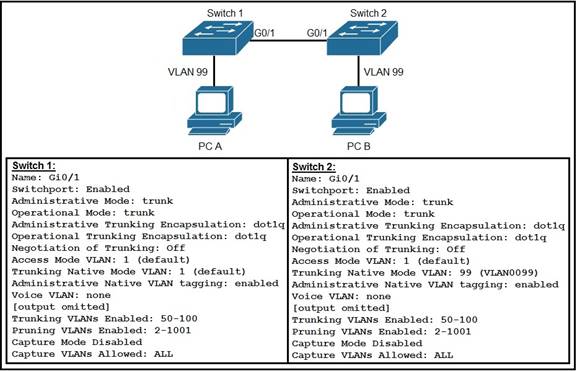
|
A. |
There is a native VLAN
mismatch |
|
B. |
Access mode
is configured on the switch
ports. |
|
C. |
The PCs are m the incorrect VLAN |
|
D. |
All VLANs are not enabled on the trunk |
Answer: A
Explanation:
From the output we see the native VLAN of Switch1 on Gi0/1 interface is VLAN 1 while that of Switch2 is VLAN 99 so there would be a native VLAN mismatch.
Which command enables a router to become a DHCP client?
|
A. |
ip address dhcp |
|
B. |
ip helper-address |
|
C. |
ip dhcp pool |
|
D. |
ip dhcp client |
Answer: A
Explanation:
If we want to get an IP address from the DHCP server on a Cisco device, we can use the command "ip address dhcp".
Note: The command "ip helper-address" enables a router to become a DHCP Relay Agent.
Which two encoding methods are supported by REST APIs? (Choose two)
|
A. |
YAML |
|
B. |
JSON |
|
C. |
EBCDIC |
|
D. |
SGML |
|
E. |
XML |
Answer: BE
Explanation:
The Application Policy Infrastructure Controller (APIC) REST API is a programmatic interface that uses REST architecture. The API accepts and returns HTTP (not enabled by default) or HTTPS messages that contain JavaScript Object Notation (JSON) or Extensible Markup Language (XML) documents.
Reference: https://www.cisco.com/c/en/us/td/docs/switches/datacenter/aci/apic/sw/2- x/rest_cfg/2_1_x/ b_Cisco_APIC_REST_API_Configuration_Guide/ b_Cisco_APIC_REST_API_Configuration_Guide_chapter_01.html
Refer to the exhibit. What is the effect of this configuration?
![]()
|
A. |
All ARP packets
are dropped by the switch |
|
B. |
Egress traffic
is passed only
if the destination is a DHCP
server. |
|
C. |
All ingress and egress
traffic is dropped because the interface is untrusted |
|
D. |
The switch discard all ingress ARP traffic with
invalid MAC-to-IP address
bindings. |
Answer: D
Explanation:
Dynamic ARP inspection is an ingress security feature; it does not perform any egress checking.
In a CDP environment, what happens when the CDP interface on an adjacent device is configured without an IP address?
|
A. |
CDP becomes inoperable on that neighbor |
|
B. |
CDP uses the IP address of another interface for that neighbor |
|
C. |
CDP operates normally,but it cannot provide IP address information for that neighbor |
|
D. |
CDP operates normally,but it cannot provide
any information for that neighbor |
Answer: C
Explanation:
Although CDP is a Layer 2 protocol but we can check the neighbor IP address with the "show cdp neighbor detail" command. If the neighbor does not has an IP address then CDP still operates without any problem.
But the IP address of that neighbor is not provided.
Refer to the exhibit. When PC 1 sends a packet to PC2,the packet has. Which source and destination IP address when it arrives at interface Gi0/0 on router R2?
![]()
|
A. |
source 192.168.10.10 and destination 10.10.2.2 |
|
B. |
source 192.168.20.10 and destination 192.168.20.1 |
|
C. |
source 192.168.10.10 and destination 192.168.20.10 |
|
D. |
source 10.10.1.1 and destination 10.10.2.2 |
Answer: C
Explanation:
The source and destination IP addresses of the packets are unchanged on all the way. Only source and destination MAC addresses are changed.
Which feature or protocol determines whether the QOS on the network is sufficient to support IP services?
|
A. |
LLDP |
|
B. |
CDP |
|
C. |
IP SLA |
|
D. |
EEM |
Answer: C
Explanation:
IP SLA allows an IT professional to collect information about network performance in real time. Therefore it helps determine whether the QoS on the network is sufficient for IP services or not. Cisco IOS Embedded Event Manager (EEM) is a powerful and flexible subsystem that provides real-time network event detection and onboard automation. It gives you the ability to adapt the behavior of your network devices to align with your business needs.
An email user has been lured into clicking a link in an email sent by their company's security organization. The webpage that opens reports that it was safe but the link could have contained
malicious code. Which type of security program is in place?
|
A. |
Physical access control |
|
B. |
Social engineering attack |
|
C. |
brute force
attack |
|
D. |
user awareness |
Answer: D
Explanation:
This is a training program which simulates an attack, not a real attack (as it says "The webpage that opens reports that it was safe") so we believed it should be called a "user awareness" program. Therefore the best answer here should be "user awareness". This is the definition of "User awareness" from CCNA 200- 301 Offical Cert Guide Book:
"User awareness: All users should be made aware of the need for data confidentiality to protect corporate information, as well as their own credentials and personal information. They should also be made aware of potential threats, schemes to mislead, and proper procedures to report security incidents. " Note: Physical access control means infrastructure locations, such as network closets and data centers, should remain securely locked.
What is the default behavior of a Layer 2 switch when a frame with an unknown destination MAC address is received?
|
A. |
The Layer 2 switch drops
the received frame |
|
B. |
The Layer 2 switch
floods packets to all ports
except the receiving port in the given VLAN. |
|
C. |
The Layer 2 switch
sends a copy of a packet to CPU for destination MAC address learning. |
|
D. |
The Layer
2 switch forwards the packet and adds the
destination MAC address to its MAC address table |
Answer:
B
Explanation:
If the destination MAC address is not in the CAM table (unknown destination MAC address), the switch sends the frame out all other ports that are in the same VLAN as the received frame. This is called flooding. It does not flood the frame out the same port on which the frame was received.
Refer to the exhibit. An engineer configured NAT translations and has verified that the configuration is correct.
![]()
Which IP address is the source IP after the NAT has taken place?
|
A. |
10.4.4.4 |
|
B. |
10.4.4.5 |
|
C. |
172.23.103.10 |
|
D. |
172.23.104.4 |
Answer: D
Explanation:
From the output it can be seen that the router is running Dynamic NAT with overloading and after NAT translation the new source address should be the inside global ip address.
Refer to the exhibit. The New York router is configured with static routes pointing to the Atlanta and Washington sites.
Which two tasks must be performed so that the Serial0/0/0 interfaces on the Atlanta and Washington routers can reach one another? (Choose two.)
![]()
|
A. |
Configure the ipv6
route 2012::/126 2023::1 command on the Washington router |
|
B. |
Configure the ipv6 route
2023::/126 2012::1 command on the Atlanta router. |
|
C. |
Configure the Ipv6 route
2012::/126 s0/0/0 command on the Atlanta router |
|
D. |
Configure the ipv6 route
2023::/126 2012::2 command
on the Atlanta router |
|
E. |
Configure the ipv6
route 2012::/126 2023::2 command on the Washington router |
Answer: DE
Explanation:
The short syntax of static IPv6 route is:
ipv6 route <destination-IPv6-address> {next-hop-IPv6-address | exit-interface}
A user configured OSPF and advertised the Gigabit Ethernet interface in OSPF By default, which type of OSPF network does this interface belong to?
|
A. |
point-to-multipoint |
|
B. |
point-to-point |
|
C. |
broadcast |
|
D. |
nonbroadcast |
Answer: C
Explanation:
The Broadcast network type is the default for an OSPF enabled ethernet interface (while Point-to- Point is the default OSPF network type for Serial interface with HDLC and PPP encapsulation).
Reference: https://www.oreilly.com/library/view/cisco-ios-cookbook/0596527225/ch08s15.html
An engineer is asked to protect unused ports that are configured in the default VLAN on a switch. Which two steps will fulfill the request? (Choose two)
|
A. |
Configure the ports
in an EtherChannel. |
|
B. |
Administratively shut
down the ports |
|
C. |
Configure the port type
as access and place in VLAN 99 |
|
D. |
Configure the ports as trunk ports |
|
E. |
Enable the Cisco
Discovery Protocol |
Answer: BC
Which output displays a JSON data representation?
|
A. |
|
|
B. |
|
|
C. |
|
|
D. |
|
Answer: D
Explanation:
JSON data is written as name/value pairs.
A name/value pair consists of a field name (in double quotes), followed by a colon, followed by a value:
"name":"Mark"
JSON can use arrays. Array values must be of type string, number, object, array, boolean or null. For example:
{
"name":"John", "age":30,
"cars":[ "Ford", "BMW", "Fiat" ]
}
JSON can have empty object like "taskId":{}
An engineer must configure a WLAN using the strongest encryption type for WPA2-PSK. Which cipher fulfills the configuration requirement?
|
A. |
WEP |
|
B. |
RC4 |
|
C. |
AES |
|
D. |
TKIP |
Answer: C
Explanation:
Many routers provide WPA2-PSK (TKIP), WPA2-PSK (AES), and WPA2-PSK (TKIP/AES) as options.
TKIP is actually an older encryption protocol introduced with WPA to replace the very-insecure WEP encryption at the time. TKIP is actually quite similar to WEP encryption. TKIP is no longer considered secure, and is now deprecated. In other words, you shouldn't be using it.
AES is a more secure encryption protocol introduced with WPA2 and it is currently the strongest encryption type for WPA2-PSK/
When configuring an EtherChannel bundle, which mode enables LACP only if a LACP device is detected?
|
A. |
Passive |
|
B. |
Desirable |
|
C. |
On |
|
D. |
Auto |
|
E. |
Active |
Answer:
A
Explanation:
The LACP is Link Aggregation Control Protocol. LACP is an open protocol, published under the 802.3ad.
The modes of LACP are active, passive or on. The side configured as “pasive” will waiting the other side that should an Active for the Etherchannel to be established.
PAgP is Port-Aggregation Protocol. It is Cisco proprietary protocol. The mode are On, Desirable or Auto. Desirable – Auto will establish a EtherChannel.
An example of how to configure an Etherchannel: SwitchFormula1>enable SwitchFormula1#configure terminal SwitchFormula1(config)# interface range f0/5 -14
SwitchFormula1(config-if-range)# channel-group 13 mode ? active Enable LACP unconditionally
auto Enable PAgP only if a PAgP device is detected desirable Enable PAgP unconditionally
on Enable Etherchannel only
passive Enable LACP only if a LACP device is detected
Refer to the exhibit. Which VLAN ID is associated with the default VLAN in the given environment?
![]()
|
A. |
VLAN 1 |
|
B. |
VLAN 5 |
|
C. |
VLAN 10 |
|
D. |
VLAN 20 |
Answer:
A
Explanation:
Cisco switches always have VLAN 1 as the default VLAN, which is needed for many protocol communication between switches like spanning-tree protocol for instance.
You can't change or even delete the default VLAN, it is mandatory.
The native VLAN is the only VLAN which is not tagged in a trunk, in other words, native VLAN frames are transmitted unchanged.
Which two VLAN IDs indicate a default VLAN? (Choose two.)
|
A. |
0 |
|
B. |
1 |
|
C. |
1005 |
|
D. |
1006 |
|
E. |
4096 |
Answer: BC
Explanation:
VLAN 1 is a system default VLAN, you can use this VLAN but you cannot delete it. By default VLAN 1 is use for every port on the switch.
Standard VLAN range from 1002-1005 it's Cisco default for FDDI and Token Ring. You cannot delete VLANs 1002-1005. mostly we don't use VLAN in this range.
Refer to the exhibit. Which statement about the interface that generated the output is true?
![]()
|
A. |
A syslog message is generated when
a violation occurs. |
|
B. |
One secure MAC address is manually configured on the interface. |
|
C. |
One secure MAC address is dynamically learned on the interface. |
|
D. |
Five secure MAC addresses are dynamically learned on the interface. |
Answer: B
Which command should you enter to view the error log in an EIGRP for IPv6 environment?
|
A. |
show ipv6 eigrp
neighbors |
|
B. |
show ipv6 eigrp topology |
|
C. |
show ipv6 eigrp traffic |
|
D. |
show ipv6 eigrp
events |
Answer: D
Explanation:
show ip eigrp events
To display the Enhanced Interior Gateway Routing Protocol (EIGRP) event log, use the show ip eigrp events command in user EXEC or privileged EXEC mode. https://www.cisco.com/c/en/us/td/docs/ios-xml/ios/iproute_eigrp/command/ire-cr-book/ire- s1.html#wp3095206170
If a notice-level messaging is sent to a syslog server, which event has occurred?
|
A. |
A network device
has restarted |
|
B. |
An ARP inspection has
failed |
|
C. |
A routing instance has flapped |
|
D. |
A debug operation is running |
Answer: A
Explanation:
Router flapping would be level 3 (as it means that interface(s) are going up down multiple times in very short period).
What are two southbound APIs? (Choose two )
|
A. |
OpenFlow |
|
B. |
NETCONF |
|
C. |
Thrift |
|
D. |
CORBA |
|
E. |
DSC |
Answer: AB
Explanation:
OpenFlow is a well-known southbound API. OpenFlow defines the way the SDN Controller should interact with the forwarding plane to make adjustments to the network, so it can better adapt to changing business requirements.
The Network Configuration Protocol (NetConf) uses Extensible Markup Language (XML) to install, manipulate and delete configuration to network devices.
Other southbound APIs are:
+ onePK: a Cisco proprietary SBI to inspect or modify the network element configuration without hardware upgrades.
+ OpFlex: an open-standard, distributed control system. It send "summary policy" to network elements.
Which feature on the Cisco Wireless LAN Controller when enabled restricts management access from specific networks?
|
A. |
CPU ACL |
|
B. |
TACACS |
|
C. |
Flex ACL |
|
D. |
RADIUS |
Answer:
A
Explanation:
Whenever you want to control which devices can talk to the main CPU, a CPU ACL is used. Note: CPU ACLs only filter traffic towards the CPU, and not any traffic exiting or generated by the CPU.
Reference: https://www.cisco.com/c/en/us/support/docs/wireless/4400-series-wireless-lan- controllers/109669-secure-wlc.html
Which command automatically generates an IPv6 address from a specified IPv6 prefix and MAC address of an interface?
|
A. |
ipv6 address dhcp |
|
B. |
ipv6 address
2001:DB8:5:112::/64 eui-64 |
|
C. |
ipv6 address
autoconfig |
|
D. |
ipv6 address 2001:DB8:5:112::2/64 link-local |
Answer: C
Explanation:
The "ipv6 address autoconfig" command causes the device to perform IPv6 stateless address auto-configuration to discover prefixes on the link and then to add the EUI-64 based addresses to the interface.
Addresses are configured depending on the prefixes received in Router Advertisement (RA) messages.
The device will listen for RA messages which are transmitted periodically from the router (DHCP Server).
This RA message allows a host to create a global IPv6 address from:
+ Its interface identifier (EUI-64 address)
+ Link Prefix (obtained via RA)
Note: Global address is the combination of Link Prefix and EUI-64 address
A network administrator enters the following command on a router: logging trap 3. What are three message types that will be sent to the Syslog server? (Choose three.)
|
A. |
informational |
|
B. |
emergency |
|
C. |
warning |
|
D. |
critical |
|
E. |
debug |
|
F. |
error |
Answer: BDF
Refer to the exhibit. Which two statements about the network environment of router R1 must be true? (Choose two.)
![]()
|
A. |
The EIGRP administrative distance was manually changed from 90 to 170. |
|
B. |
There are 20 different network masks within
the 10.0.0.0/8 network. |
|
C. |
Ten routes are equally load-balanced between Te0/1/0.100 and Te0/2/0.100 |
|
D. |
The 10.0.0.0/8 network was learned via external EIGRP. |
|
E. |
A static default route to 10.85.33.14 was defined. |
Answer:
BC
Which two statements about exterior routing protocols are true? (Choose two.)
|
A. |
They determine the optimal within
an autonomous system. |
|
B. |
They determine the optimal path
between autonomous systems. |
|
C. |
BGP is the current standard exterior routing protocol. |
|
D. |
Most modern
networking supports both
EGP and BGP for external routing. |
|
E. |
Most modern network routers support both EGP and EIGRP for
external routing. |
Answer: BC
Explanation:
Exterior Gateway Protocols (EGP): Used for routing between autonomous systems. It is also referred to as inter-AS routing. Service providers and large companies may interconnect using an EGP. The Border Gateway Protocol (BGP) is the only currently viable EGP and is the official routing protocol used by the Internet.
Because BGP is the only EGP available, the term EGP is rarely used; instead, most engineers simply refer to BGP.
https://www.ciscopress.com/articles/article.asp?p=2180210&seqNum=7
Which two pieces of information about a Cisco device can Cisco Discovery Protocol communicate? (Choose two.)
|
A. |
the native VLAN |
|
B. |
the trunking protocol |
|
C. |
the VTP domain |
|
D. |
the spanning-tree priority |
|
E. |
the spanning tree
protocol |
Answer:
AC
Explanation:
The information contained in Cisco Discovery Protocol advertisements varies based on the type of device and the installed version of the operating system. Some of the information that Cisco Discovery Protocol can learn includes:
Cisco IOS version running on Cisco devices Hardware platform of devices
IP addresses of interfaces on devices
Locally connected devices advertising Cisco Discovery Protocol Interfaces active on Cisco devices, including encapsulation type Hostname
Duplex setting
***VLAN Trunking Protocol (VTP) domain
***Native VLAN
https://www.cisco.com/c/en/us/td/docs/ios-xml/ios/cdp/configuration/15-mt/cdp-15-mt-book/nm- cdp-discover.html
Which two statements about NTP operations are true? (Choose two.)
|
A. |
NTP uses UDP over
IP. |
|
B. |
Cisco routers can act as both NTP
authoritative servers and NTP clients. |
|
C. |
Cisco routers can act only as NTP servers. |
|
D. |
Cisco routers can act only as NTP clients. |
|
E. |
NTP uses TCP over IP. |
Answer:
AB
Which command is used to specify the delay time in seconds for LLDP to initialize on any interface?
|
A. |
lldp timer |
|
B. |
lldp holdtime |
|
C. |
lldp reinit |
|
D. |
lldp tlv-select |
Answer: C
Explanation:
+ lldp holdtime seconds: Specify the amount of time a receiving device should hold the information from your device before discarding it
+ lldp reinit delay: Specify the delay time in seconds for LLDP to initialize on an interface
+ lldp timer rate: Set the sending frequency of LLDP updates in seconds
Reference: https://www.cisco.com/c/en/us/td/docs/switches/lan/catalyst3560/software/release/12- 2_55_se/ configuration/guide/3560_scg/swlldp.html
A Cisco IP phone receive untagged data traffic from an attached PC. Which action is taken by the phone?
|
A. |
It allows the traffic to pass through unchanged |
|
B. |
It drops the traffic |
|
C. |
It tags the traffic
with the default
VLAN |
|
D. |
It tags the traffic with
the native VLAN |
Answer: A
Explanation:
Untagged traffic from the device attached to the Cisco IP Phone passes through the phone unchanged, regardless of the trust state of the access port on the phone.
Reference: https://www.cisco.com/c/en/us/td/docs/switches/lan/catalyst2960/software/release/12- 2_40_se/ configuration/guide/scg/swvoip.pdf
Refer to the exhibit. Based on the LACP neighbor status, in which mode is the SW1 port channel configured?
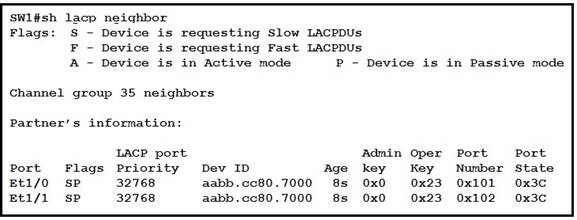
|
A. |
passive |
|
B. |
mode on |
|
C. |
auto |
|
D. |
active |
Answer: D
Explanation:
From the neighbor status, we notice the "Flags" are SP. "P" here means the neighbor is in Passive mode.
In order to create an Etherchannel interface, the (local) SW1 ports should be in Active mode. Moreover, the "Port State" in the exhibit is "0x3c" (which equals to "00111100 in binary format). Bit 3 is "1" which means the ports are synchronizing -> the ports are working so the local ports should be in Active mode.
Reference: https://www.cisco.com/c/en/us/td/docs/switches/lan/catalyst3650/software/release/3se/consolidat ed_guide/command_reference/b_c
Refer to the exhibit. The show ip ospf interface command has been executed on R1 How is OSPF configured?
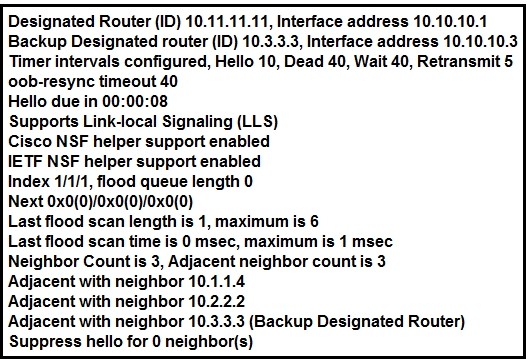
|
A. |
The interface is not participating in OSPF |
|
B. |
A point-to-point network type
is configured |
|
C. |
The default Hello and Dead timers
are in use |
|
D. |
There are six OSPF neighbors on this interface |
Answer: C
Explanation:
From the output we can see there are Designated Router & Backup Designated Router for this OSPF domain so this is a broadcast network (point-to-point and point-to-multipoint networks do not elect DR & BDR) -> Answer B is not correct.
By default, the timers on a broadcast network (Ethernet, point-to-point and point-to-multipoint) are 10 seconds hello and 40 seconds dead (therefore answer C is correct). The timers on a non- broadcast network are 30 seconds hello 120 seconds dead.
From the line "Neighbor Count is 3", we learn there are four OSPF routers in this OSPF domain
-> Answer D is not correct.
R1 has learned route 192.168.12.0/24 via IS-IS, OSPF, RIP and Internal EIGRP Under normal operating conditions, which routing protocol is installed in the routing table?
|
A. |
IS-IS |
|
B. |
RIP |
|
C. |
Internal EIGRP |
|
D. |
OSPF |
Answer: C
Explanation:
With the same route (prefix), the router will choose the routing protocol with lowest Administrative Distance (AD) to install into the routing table. The AD of Internal EIGRP (90) is lowest so it would
be chosen. The table below lists the ADs of popular routing protocols.
![]()
Note: The AD of IS-IS is 115. The "EIGRP" in the table above is "Internal EIGRP". The AD of "External EIGRP" is 170. An EIGRP external route is a route that was redistributed into EIGRP.
Which IPv6 address block sends packets to a group address rather than a single address?
|
A. |
2000::/3 |
|
B. |
FC00::/7 |
|
C. |
FE80::/10 |
|
D. |
FF00::/8 |
Answer: D
Explanation:
FF00::/8 is used for IPv6 multicast and this is the IPv6 type of address the question wants to ask. FE80::/10 range is used for link-local addresses. Link-local addresses only used for communications within the local subnetwork (automatic address configuration, neighbor discovery, router discovery, and by many routing protocols). It is only valid on the current subnet. It is usually created dynamically using a link-local prefix of FE80::/10 and a 64-bit interface identifier (based on 48-bit MAC address).
Which feature or protocol is required for an IP SLA to measure UDP jitter?
|
A. |
LLDP |
|
B. |
EEM |
|
C. |
CDP |
|
D. |
NTP |
Answer: D
Explanation:
Time synchronization, such as that provided by the Network Time Protocol (NTP), is required between the source and the target device to provide accurate one-way delay (latency) measurements.
Which two pieces of information can you learn by viewing the routing table? (Choose two)
|
A. |
whether an ACL was applied inbound or outbound to an interface |
|
B. |
the EIGRP or BGP
autonomous system |
|
C. |
whether the administrative distance was manually or dynamically configured |
|
D. |
Which neighbor adjacencies are established |
|
E. |
the length of time that
a route has been known |
Answer: CE
Refer to the exhibit. Which two events occur on the interface,if packets from an unknown Source address arrive after the interface learns the maximum number of secure MAC address? (Choose two)
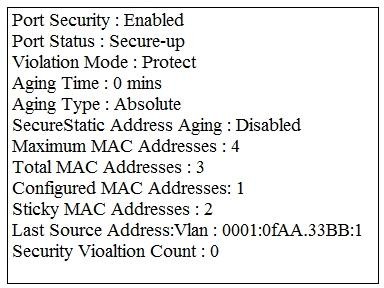
|
A. |
The security violation counter dose not
increment |
|
B. |
The port LED turns
off |
|
C. |
The interface is error-disabled |
|
D. |
A syslog message is
generated |
|
E. |
The interface drops
traffic from unknown
MAC address |
Answer: AE
Explanation:
protect - Drops packets with unknown source addresses until you remove a sufficient number of secure MAC addresses to drop below the maximum value.
restrict- Drops packets with unknown source addresses until you remove a sufficient number of secure MAC addresses to drop below the maximum value and causes the SecurityViolation counter to increment.
shutdown - Puts the interface into the error-disabled state immediately and sends an SNMP trap notification.
Refer to the exhibit. Which feature is enabled by this configuration?
![]()
|
A. |
static NAT translation |
|
B. |
a DHCP pool |
|
C. |
a dynamic NAT address pool |
|
D. |
PAT |
Answer: C
For what two purposes does the Ethernet protocol use physical addresses?
|
A. |
to uniquely identify devices at Layer
2 |
|
B. |
to allow communication with devices on a different network |
|
C. |
to differentiate a Layer
2 frame from
a Layer 3 packet |
|
D. |
to establish a priority system to determine which device gets
to transmit first |
|
E. |
to allow communication between different devices on the same
network |
|
F. |
to allow detection of a remote
device when its
physical address is
unknown |
Answer:
AE
Refer to Exhibit. An engineer is configuring the NEW York router to reach the Lo1 interface of the Atlanta router using interface Se0/0/0 as the primary path.
Which two commands must be configured on the New York router so that it can reach the Lo1 interface of the Atlanta router via Washington when the link between New York and Atlanta goes down? (Choose two)
![]()
|
A. |
ipv6 router 2000::1/128 2012::1 |
|
B. |
ipv6 router 2000::1/128 2012::1 5 |
|
C. |
ipv6 router
2000::1/128 2012::2 |
|
D. |
ipv6 router 2000::1/1282023::2 5 |
|
E. |
ipv6 router
2000::1/1282023::3 5 |
Answer: AE
Explanation:
Floating static routes are static routes that have an administrative distance greater than the administrative distance (AD) of another static route or dynamic routes. By default a static route has an AD of 1 then floating static route must have the AD greater than 1. Floating static route has a manually configured administrative distance greater than that of the primary route and therefore would not be in the routing table until the primary route fails.
Refer to Exhibit. How does SW2 interact with other switches in this VTP domain?
![]()
|
A. |
It processes VTP updates from
any VTP clients on the network
on its access ports. |
|
B. |
It receives updates from all
VTP servers and
forwards all locally configured VLANs out
all trunk ports |
|
C. |
It forwards only the VTP advertisements that it receives on its trunk
ports. |
|
D. |
It transmits and processes VTP updates from
any VTP Clients
on the network on its trunk
ports |
Answer: C
Explanation:
The VTP mode of SW2 is transparent so it only forwards the VTP updates it receives to its trunk links without processing them.
Drag and Drop Question
Drag and drop the networking parameters from the left on to the correct values on the right.
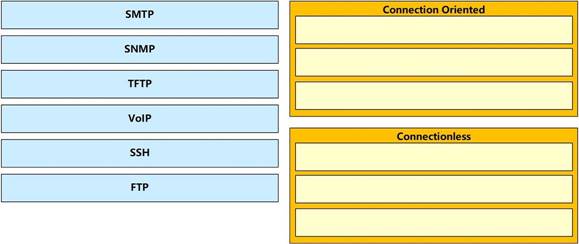
Answer:
![]()
Explanation:
SSH uses TCP port 22 while SNMP uses UDP port 161 and 162.
Drag and Drop Question
A network engineer is configuring an OSPFv2 neighbor adjacency. Drag and drop the parameters from the left onto their required categories on the right. No all parameters are used.

Answer:
![]()
Drag and Drop Question
Refer to the exhibit. Drag and drop the networking parameters from the left on to the correct values on the right.
![]()
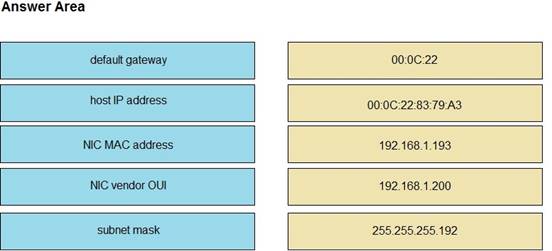
Answer:
![]()
Explanation:
The "ip route" and "ip addr show eth1" are Linux commands.
+ "ip route": display the routing table
+ "ip addr show eth1": get depth information (only on eth1 interface) about your network interfaces like IP Address, MAC Address information
Which NAT term is defined as a group of addresses available for NAT use?
|
A. |
NAT pool |
|
B. |
dynamic NAT |
|
C. |
static NAT |
|
D. |
one-way NAT |
Answer: A
After you deploy a new WLAN controller on your network, which two additional tasks should you consider? (Choose two)
|
A. |
deploy load balancers |
|
B. |
configure additional vlans |
|
C. |
configure multiple VRRP groups |
|
D. |
deploy POE
switches |
|
E. |
configure additional security policies |
Answer: AE
Explanation:
In order of importance security policies and load balancing should be at the top of the list. POE would likely be third in line mainly because this would be a budgeted consideration and not necessarily an immediate post-deployment task requirement.
Which component of an Ethernet frame is used to notify a host that traffic is coming?
|
A. |
start of frame
delimiter |
|
B. |
Type field |
|
C. |
preamble |
|
D. |
Data field |
Answer: C
Explanation:
Preamble is a 7 Byte field in the Ethernet frame which helps to receiver to know that it is an actual data ( Ethernet Frame) and not some random noise in the transmission medium. It acts like a doorbell telling about the incoming data.
Refer to the exhibit. How will switch SW2 handle traffic from VLAN 10 on SW1?
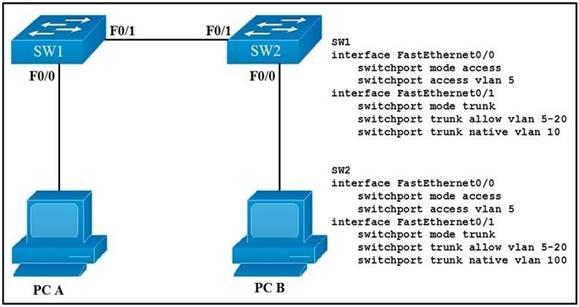
|
A. |
It sends the traffic to VLAN 10. |
|
B. |
It sends the traffic to VLAN 100. |
|
C. |
It drops the traffic. |
|
D. |
It sends the traffic to VLAN 1. |
Answer: B
Explanation:
Since SW-1 is configured native VLAN is VLAN10, so traffic coming out of VLAN-10 is untagged, & goes directly to SW-2 Native VLAN: VLAN100, due to VLAN mismatch.
You are configuring your edge routers interface with a public IP address for Internet connectivity. The router needs to obtain the IP address from the service provider dynamically. Which command is needed on interface FastEthernet 0/0 to accomplish this?
|
A. |
ip default-gateway |
|
B. |
ip route |
|
C. |
ip default-network |
|
D. |
ip address dhcp |
|
E. |
ip address dynamic |
Answer: D
What are two reasons that cause late collisions to increment on an Ethernet interface? (Choose two)
|
A. |
when the sending
device waits 15 seconds before
sending the frame
again |
|
B. |
when the
cable length limits
are exceeded |
|
C. |
when one side of the connection is configured for
half-duplex |
|
D. |
when Carner Sense
Multiple Access/Collision Detection is used |
|
E. |
when a collision occurs after the
32nd byte of a frame
has been transmitted |
Answer:
BC
Explanation:
A late collision is defined as any collision that occurs after the first 512 bits (or 64th byte) of the frame have been transmitted. The usual possible causes are full-duplex/half-duplex mismatch, exceeded Ethernet cable length limits, or defective hardware such as incorrect cabling, non- compliant number of hubs in the network, or a bad NIC.
Late collisions should never occur in a properly designed Ethernet network. They usually occur when Ethernet cables are too long or when there are too many repeaters in the network.
Reference: https://www.cisco.com/en/US/docs/internetworking/troubleshooting/guide/tr1904.html
Which IPv6 address type provides communication between subnets and cannot route on the Internet?
|
A. |
global unicast |
|
B. |
unique local |
|
C. |
link-local |
|
D. |
multicast |
Answer:
B
Explanation:
A IPv6 Unique Local Address is an IPv6 address in the block FC00::/7. It is the approximate IPv6 counterpart of the IPv4 private address. It is not routable on the global Internet.
Note: In the past, Site-local addresses (FEC0::/10) are equivalent to private IP addresses in IPv4 but now they are deprecated.
Link-local addresses only used for communications within the local subnet. It is usually created dynamically using a link-local prefix of FE80::/10 and a 64-bit interface identifier (based on 48-bit MAC address).
A user configured OSPF in a single area between two routers A serial interface connecting R1 and R2 is running encapsulation PPP.
By default which OSPF network type is seen on this interface when the user types show ip ospf interface on R1 or R2?
|
A. |
port-to-multipoint |
|
B. |
broadcast |
|
C. |
point-to-point |
|
D. |
non-broadcast |
Answer: C
Explanation:
The default OSPF network type for HDLC and PPP on Serial link is point-to-point (while the default OSPF network type for Ethernet link is Broadcast).
You have two paths for the 10.10.10.0 network - one that has a feasible distance of 3072 and the other of 6144.
What do you need to do to load balance your EIGRP routes?
|
A. |
Change the maximum
paths to 2 |
|
B. |
Change the configuration so they both
have the same
feasible distance |
|
C. |
Change the
variance for the path that
has a feasible distance of 3072
to 2 |
|
D. |
Change the IP addresses so both paths
have the same
source IP address |
Answer: BC
Explanation:
Every routing protocol supports equal cost path load balancing. In addition, Interior Gateway Routing Protocol (IGRP) and EIGRP also support unequal cost path load balancing. Use the variance n command in order to instruct the router to include routes with a metric of less than n times the minimum metric route for that destination. The variable n can take a value between 1 and 128. The default is 1, which means equal cost load balancing. Traffic is also distributed among the links with unequal costs, proportionately, with respect to the metric.
Reference:
https://www.cisco.com/c/en/us/support/docs/ip/enhanced-interior-gateway-routing-protocol- eigrp/13677-19.html#topic1
Drag and Drop Question
Drag each route source from the left to the numbers on the right. Beginning with the lowest and ending with the highest administrative distance.
![]()
Answer:
![]()
Which two commands can you use to configure an actively negotiate EtherChannel? (Choose two)
|
A. |
channel-group 10 mode
on |
|
B. |
channel-group 10 mode auto |
|
C. |
channel-group 10 mode passive |
|
D. |
channel-group 10 mode desirable |
|
E. |
channel-group 10 mode
active |
Answer: DE
Explanation:
Desirable mode: Desirable mode in Port Aggregation Protocol (PAgP) initiates the negotiation and tries to form EtherChannel with other end.
Active Mode: Active Mode in Link Aggregation Control Protocol (LACP) initiates the negotiation and tries to form EtherChannel with other end.
Refer to the exhibit. Which two statements about the interface that generated the output are true? (Choose two)
![]()
|
A. |
learned MAC addresses are deleted after
five minutes of inactivity |
|
B. |
the interface is error-diabled if packets arrive
from a new unknown source
address |
|
C. |
it has dynamically learned two secure MAC addresses |
|
D. |
it has dynamically learned three secure MAC
addresses |
|
E. |
the security violation counter increments if packets arrive
from a new unknown source
address |
Answer: AC
Which two circumstances can prevent two routers from establishing an OSPF neighbor adjacency? (Choose two.)
|
A. |
mismatched autonomous system
numbers |
|
B. |
an ACL blocking traffic
from multicast address
224.0.0.10 |
|
C. |
mismatched process
IDs |
|
D. |
mismatched hello
timers and dead
timers |
|
E. |
use of the same router
ID on both
devices |
Answer: DE
Explanation:
Must be unique:
– OSPF process ID
– router ID
–
IP address Must match:
–
netmask
– area ID
–
timers
Which two statements about the purpose of the OSI model are accurate? (Choose two)
|
A. |
Defines the network functions that occur
at each layer |
|
B. |
Facilitates an understanding of how information travels throughout a network |
|
C. |
Changes in one layer
do not impact
other layer |
|
D. |
Ensures reliable data
delivery through its
layered approach |
Answer:
AB
Which option best describes an API?
|
A. |
a contract that describes how
various components communicate and exchange data
with each other. |
|
B. |
an architectural style (versus a protocol) for designing applications |
|
C. |
a stateless client-server model |
|
D. |
request a certain
type of data
by specifying the URL path
that models the
data |
Answer: A
Which of the following is the JSON encoding of a dictionary or hash?
|
A. |
{"key": "value"} |
|
B. |
["key",
"value"] |
|
C. |
{"key",
"value"} |
|
D. |
("key": "value") |
Answer:
A
What will happen if you configure the logging trap debug command on a router?
|
A. |
It causes the
router to send
messages with lower
severity levels to the syslog
server |
|
B. |
It causes
the router to send all messages with
the severity levels
Warning, Error, Critical, and Emergency to the syslog server |
|
C. |
It causes the router
to send all messages to the syslog
server |
|
D. |
It causes the
router to stop sending all
messages to the syslog server |
Answer: C
An engineer must configure a /30 subnet between two routers. Which usable IP address and subnet mask combination meets this criteria?
|
A. |
interface e0/0 description to HQ-A371:10975 ip address 172.16.1.4 255.255.255.248 |
|
B. |
interface e0/0 description to HQ-A371:10975 ip address 10.2.1.3 255.255.255.252 |
|
C. |
interface e0/0 description to HQ-A371:10975 ip address 192.168.1.1 255.255.255.248 |
|
D. |
interface e0/0 description to HQ-A371:10975 ip address 209.165.201.2 255.255.255.252 |
Answer: D
Explanation:
A /30 subnet means subnet mask of 255.255.255.252. But 10.2.1.3 255.255.255.252 is a broadcast IP address; only 209.165.201.2/30 is the usable IP address.
How does STP prevent forwarding loops at OSI Layer 2?
|
A. |
TTL |
|
B. |
MAC address forwarding |
|
C. |
Collision avoidance. |
|
D. |
Port blocking |
Answer: D
Explanation:
TTL is a Layer 3 mechanism that routers decrement after a successful hop.
Which three statements about MAC addresses are correct? (Choose three)
|
A. |
To communicate with other devices on a network, a network device
must have a unique MAC address |
|
B. |
The MAC address
is also referred to as the IP address |
|
C. |
The MAC address
of a device must be configured in the Cisco
IOS CLI by a user
with administrative privileges |
|
D. |
A MAC address contains two main components, the first of which identifies the manufacturer of the hardware and the second of which
uniquely identifies the hardware |
|
E. |
An example of a MAC address is 0A:26:B8:D6:65:90 |
|
F. |
A MAC address contains two main components, the first of which identifies the network on which
the host resides and the second of which uniquely identifies the host on the
network |
Answer: ADE
Which Cisco IOS command will indicate that interface GigabitEthernet 0/0 is configured via DHCP?
|
A. |
show ip interface GigabitEthernet 0/0 dhcp |
|
B. |
show interface GigabitEthernet 0/0 |
|
C. |
show ip interface dhcp |
|
D. |
show ip interface GigabitEthernet 0/0 |
|
E. |
show ip interface GigabitEthernet 0/0 brief |
Answer: D
Which command can you enter to allow Telnet to be supported in addition to SSH?
|
A. |
transport input telnet
ssh |
|
B. |
transport input
telnet |
|
C. |
no transport input telnet |
|
D. |
privilege level 15 |
Answer: A
Refer to the exhibit. The default-information originate command is configured under the R1 OSPF configuration. After testing, workstations on VLAN 20 at Site B cannot reach a DNS server on the Internet.
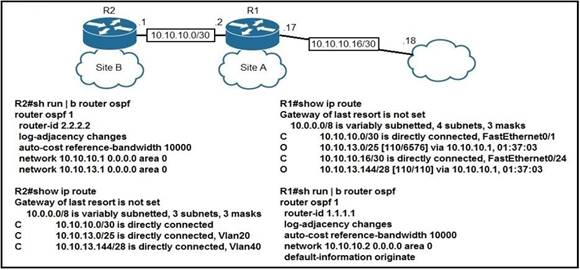
Which action corrects the configuration issue?
|
A. |
Add the default-information originate command on R2. |
|
B. |
Add the always keyword to the default-information originate command on R1. |
|
C. |
Configure the ip route 0.0.0.0 0.0.0.0 10.10.10.18 command on R1. |
|
D. |
Configure the ip route 0.0.0.0 0.0.0.0 10.10.10.2 command on R2. |
Answer: C
Which three describe the reasons large OSPF networks use a hierarchical design? (Choose Three)
|
A. |
to speed up convergence |
|
B. |
to reduce routing overhead |
|
C. |
to lower costs by replacing routers with distribution layer
switches. |
|
D. |
to decrease latency by increasing bandwidth. |
|
E. |
to confine network instability to single areas
of the network. |
|
F. |
to reduce the
complexity of router
configuration. |
Answer:
ABE
Explanation:
Hierarchical design of OSPF (basically means that you can separate the larger internetwork into smaller internetworks called areas) helps us create a network with all features listed above (decrease routing overhead, speed up convergence, confine network instability to single areas of the network).
What is the binary pattern of unique ipv6 unique local address?
|
A. |
00000000 |
|
B. |
11111100 |
|
C. |
11111111 |
|
D. |
11111101 |
Answer:
B
Explanation:
A IPv6 Unique Local Address is an IPv6 address in the block FC00::/7, which means that IPv6 Unique Local addresses begin with 7 bits with exact binary pattern as 1111 110 -> Answer B is correct.
Note: IPv6 Unique Local Address is the approximate IPv6 counterpart of the IPv4 private address. It is not routable on the global Internet.
Refer to the exhibit. If R1 receives a packet destined to 172.16.1.1, to which IP address does it send the packet?
![]()
|
A. |
192.168.14.4 |
|
B. |
192.168.12.2 |
|
C. |
192.168.13.3 |
|
D. |
192.168.15.5 |
Answer:
A
Explanation:
172.16.1.1 is not in the routing table this means it is a random address.
But since a default static route of 0.0.0.0 has been configured and injected to OSPF with the next hope address of 192.168.14.4 through FastEthernet1/0, thus R1 will send the packet to 192.168.14.4.
Which two statements about VTP are true? (Choose two.)
|
A. |
All switches must be configured with the same
VTP domain name |
|
B. |
All switches must
be configured to perform trunk
negotiation. |
|
C. |
All switches must
be configured with
a unique VTP
domain name |
|
D. |
The VTP server must
have the highest revision number in the domain |
|
E. |
All switches must
use the same
VTP version. |
Answer: AE
Explanation: https://www.cisco.com/c/en/us/td/docs/switches/lan/catalyst3750/software/release/12- 2_25_sea/configuration/guide/3750scg/swvtp.pdf
Refer to the exhibit. On R1 which routing protocol is in use on the route to 192.168.10.1?
![]()
|
A. |
RIP |
|
B. |
OSPF |
|
C. |
IGRP |
|
D. |
EIGRP |
Answer: D
Which two options are the best reasons to use an IPV4 private IP space? (Choose two)
|
A. |
to enable intra-enterprise communication |
|
B. |
to implement NAT |
|
C. |
to connect applications |
|
D. |
to conserve global address
space |
|
E. |
to manage routing overhead |
Answer:
AD
Which type does a port become when it receives the best BPDU on a bridge?
|
A. |
The designated port |
|
B. |
The backup port |
|
C. |
The alternate port |
|
D. |
The root port |
Answer: D
Explanation:
The port that receives the best BPDU on a bridge is the root port.
Which value can you modify to configure a specific interface as the preferred forwarding interface?
|
A. |
The interface number |
|
B. |
The port priority |
|
C. |
The VLAN priority |
|
D. |
The hello time |
Answer:
B
Explanation:
This example shows how to increase the probability that the spanning tree instance on access port interface 2/0 is chosen as the root bridge by changing the port priority to 32:
switch(config-if)# spanning-tree port-priority 32
Which statement about VLAN configuration is true?
|
A. |
The switch must
be in VTP server or transparent mode
before you can
configure a VLAN |
|
B. |
The switch must be in config-vlan mode before you
configure an extended VLAN |
|
C. |
Dynamic inter-VLAN routing is supported on VLAN2 through VLAN 4064 |
|
D. |
A switch in VTP transparent mode save the VLAN databases to the running configuration only |
Answer:
A
Explanation:
You can only create, add, delete edit vlan in server and transparent mode, you won’t be able to create, delete vlan in client mode.
Refer to the exhibit. Which Command do you enter so that R1 advertises the loopback0 interface to the BGP Peers?
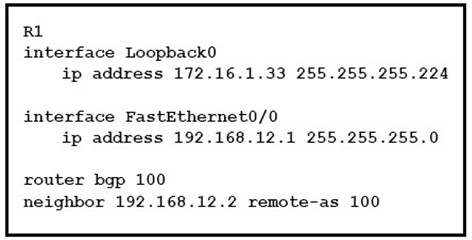
|
A. |
Network 172.16.1.32 mask
255.255.255.224 |
|
B. |
Network 172.16.1.0 0.0.0.255 |
|
C. |
Network 172.16.1.32 255.255.255.224 |
|
D. |
Network 172.16.1.33 mask 255.255.255.224 |
|
E. |
Network 172.16.1.32 mask 0.0.0.31 |
|
F. |
Network 172.16.1.32 0.0.0.31 |
Answer:
A
Explanation:
First please notice that unlike other routing protocols like OSPF or EIGRP, we have to use subnet mask, not wildcard mask, to advertise the routes in the “network” command -> C is not correct.
Secondly, with BGP, you must advertise the correct network and subnet mask in the “network” command ( in this case network 172.16.1.32/27). BGP is very strict in the routing advertisements. In other words, BGP only advertises the network which exists exactly in the routing table (in this case network x.x.x.32/27 exists in the routing table as the Fa0/0 interface). If you put the command “network x.x.0.0 mask 255.255.0.0” or “network x.0.0.0 mask 255.0.0.0” or “network
x.x.x.33 mask 255.255.255.255” then BGP will not advertise anything. Therefore the full command in this question is “network 172.16.1.32 mask 255.255.255.224”.
Refer to exhibit. What Administrative distance has route to 192.168.10.1 ?
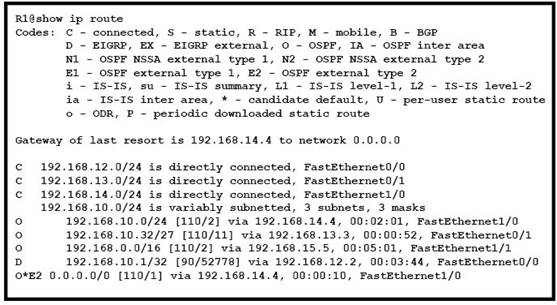
|
A. |
1 |
|
B. |
90 |
|
C. |
110 |
|
D. |
120 |
Answer:
B
Which value is used to determine the active router in an HSRP default configuration?
|
A. |
Router loopback address |
|
B. |
Router IP address |
|
C. |
Router priority |
|
D. |
Router tracking number |
Answer:
B
Explanation:
Q. If there is no priority
configured for a standby group,
what determines which
router is active?
A. The priority field is used to elect the active router and the standby router for the specific group. In the case of an equal priority, the router with the highest IP address for the respective group is elected as active. Furthermore, if there are more than two routers in the group, the second highest IP address determines the standby router and the other router/routers are in the listen state.
Refer to the exhibit. If RTR01 is configured as shown, which three addresses will be received by other routers that are running EIGRP on the network? (Choose three)
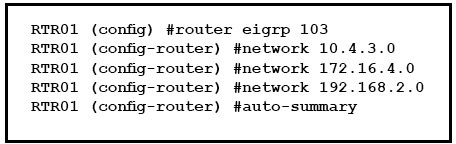
|
A. |
192.168.2.0 |
|
B. |
10.4.3.0 |
|
C. |
10.0.0.0 |
|
D. |
172.16.0.0 |
|
E. |
172.16.4.0 |
|
F. |
192.168.0.0 |
Answer: ACD
Explanation:
Auto summary uses "classful boundary"
- 10.4.3.0 with mask 255.0.0.0 gives 10.0.0.0
- 172.16.4.0 with mask 255.255.0.0 gives 172.16.0.0
- 192.168.2.0 with mask 255.255.255.0 gives 192.168.2.0
Which configuration command can you apply to a HSRP router so that its local interface becomes active if all other routers in the group fail?
|
A. |
no additional config
is required |
|
B. |
standby 1 track
ethernet |
|
C. |
standby 1 preempt |
|
D. |
standby 1 priority 250 |
Answer: A
Explanation:
Simply because that will be the default behavior routers would follow in the event all other routers in the HSRP group fail, then it would not keep attributes such as priority or preemption.
What preemption does in summary is to make sure that the configured Priority on all routers within the same HSRP group is always respected. That is, if R1 is configured on the HSRP group with a priority of 150 but he stands as active since all other routers currently subscribed to that group have a priority 150, then will router will preempt the current active router and will take over hence becoming the new active router.
With preemption disabled, the new router does not preempt the current active router, unless routers in the group have to renegotiate their roles based on each router’s priority at the time of negotiation.
Refer to the exhibit. After you apply the given configuration to a router, the DHCP clients behind the device cannot communicate with hosts outside of their subnet. Which action is most likely to correct the problem?
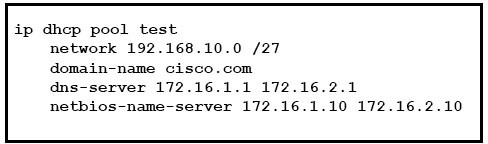
|
A. |
Configure the dns
server on the same subnet
as the clients |
|
B. |
Activate the dhcp pool |
|
C. |
Correct the subnet mask |
|
D. |
Configure the default
gateway |
Answer: D
Explanation:
Configuring a DHCP server on a router:
conf t service dhcp
ip dhcp pool <pool name>
network <network address of the pool>
default-router <ip address of the interface facing the hosts, or ip adress of the interface facing downstream clients>
dns-server <ip address of dns-server> exit
Which two statements about eBGP neighbor relationships are true? (Choose two)
|
A. |
The two devices must reside in different autonomous systems |
|
B. |
Neighbors must
be specifically declared in the configuration of each device |
|
C. |
They can be created dynamically after the
network statement is configured. |
|
D. |
The two devices must
reside in the same autonomous system |
|
E. |
The two devices must have matching timer settings |
Answer: AB
Explanation:
Just like OSPF or EIGRP, BGP establishes a neighbor adjacency with other BGP routers before they exchange any routing information. Unlike other routing protocols however, BGP does not use broadcast or multicast to “discover” other BGP neighbors.
Neighbors have to be configured manually and BGP uses TCP port 179 for the connection.
Which statement about Cisco Discovery Protocol is true?
|
A. |
It is a Cisco-proprietary protocol. |
|
B. |
It runs on the network
layer. |
|
C. |
It can discover information from routers, firewalls, and switches. |
|
D. |
It runs on the physical layer and the data link
layer. |
Answer:
A
Refer to the exhibit. How will the router handle a packet destined for 192.0.2.156?
![]()
|
A. |
The router will
forward the packet
via either Serial0 or Serial1. |
|
B. |
The router will return
the packet to its source. |
|
C. |
The router will forward
the packet via
Serial2. |
|
D. |
The router will
drop the packet. |
Answer: C
Explanation:
Router has pointed default router to 192.168.4.1 and this subnet is connected via serial 2 interface. Router does not have router for the 192.0.2.156. so it will use the default gateway 192.168.4.1. A default route identifies the gateway IP address to which the router sends all IP packets for which it does not have a learned or static route.
Which technique can you use to route IPv6 traffic over an IPv4 infrastructure?
|
A. |
NAT |
|
B. |
6 to 4 tunneling |
|
C. |
L2TPv3 |
|
D. |
dual-stack |
Answer:
B
Explanation:
Overlay tunneling encapsulates IPv6 packets in IPv4 packets for delivery across an IPv4 infrastructure (a core network or the figure below). By using overlay tunnels, you can communicate with isolated IPv6 networks without upgrading the IPv4 infrastructure between
them. Overlay tunnels can be configured between border devices or between a border device and a host; however, both tunnel endpoints must support both the IPv4 and IPv6 protocol stacks. IPv6 supports the following types of overlay tunneling mechanisms:
1
Manual
2 Generic routing
encapsulation (GRE)
3 IPv4-compatible
4 6to4
5
Intrasite Automatic Tunnel
Addressing Protocol (ISATAP)
Which statements describe the routing protocol OSPF? (Choose three.)
|
A. |
It supports VLSM. |
|
B. |
It is used to route between
autonomous systems. |
|
C. |
It confines network instability to one area
of the network. |
|
D. |
It increases routing overhead on the network. |
|
E. |
It allows extensive control of routing updates. |
|
F. |
It is simpler
to configure than RIP v2. |
Answer:
ACE
Explanation:
The OSPF protocol is based on link-state technology, which is a departure from the Bellman-Ford vector based algorithms used in traditional Internet routing protocols such as RIP. OSPF has introduced new concepts such as authentication of routing updates, Variable Length Subnet Masks (VLSM), route summarization, and so forth.
OSPF uses flooding to exchange link-state updates between routers. Any change in routing information is flooded to all routers in the network. Areas are introduced to put a boundary on the explosion of link-state updates. Flooding and calculation of the Dijkstra algorithm on a router is limited to changes within an area.
Refer to the exhibit. After you apply the given configurations to R1 and R2 you notice that OSPFv3 fails to start.
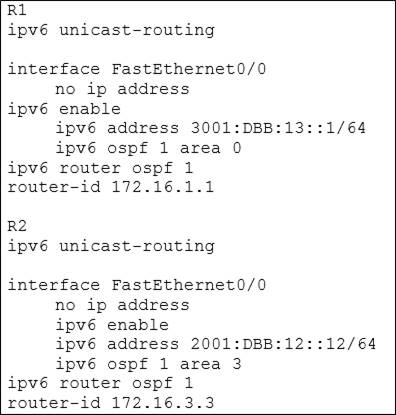
Which reason for the problem is most likely true ?
|
A. |
The area numbers
on R1 and R2 are mismatched |
|
B. |
The IPv6 network addresses on R1 and R2 are mismatched |
|
C. |
The autonomous system numbers
on R1 and R2 are mismatched |
|
D. |
The router ids on R1 and R2 are mismatched |
Answer:
A
Which command is used to display the collection of OSPF link states?
|
A. |
show ip ospf
link-state |
|
B. |
show ip ospf lsa
database |
|
C. |
show ip ospf neighbors |
|
D. |
show ip ospf
database |
Answer: D
Explanation:
The "show ip ospf database" command displays the link states. Here is an example: Here is the lsa database on R2.
R2#show ip ospf database
OSPF Router with ID (2.2.2.2) (Process ID 1) Router Link States (Area 0)
Link ID ADV Router Age Seq# Checksum Link count2.2.2.2 2.2.2.2 793 0x80000003 0x004F85
210.4.4.4 10.4.4.4 776 0x80000004 0x005643 1111.111.111.111 111.111.111.111 755
0x80000005 0x0059CA 2133.133.133.133 133.133.133.133 775 0x80000005 0x00B5B1 2 Net
Link States (Area 0)
Link ID ADV Router Age Seq# Checksum10.1.1.1 111.111.111.111 794 0x80000001 0x001E8B10.2.2.3 133.133.133.133 812 0x80000001 0x004BA910.4.4.1 111.111.111.111 755
0x80000001 0x007F1610.4.4.3 133.133.133.133 775 0x80000001 0x00C31F
Refer to the exhibit. A network associate has configured OSPF with the command:
City(config-router)# network
192.168.12.64 0.0.0.63 area 0
After completing the configuration, the associate discovers that not all the interfaces are participating in OSPF. Which three of the interfaces shown in the exhibit will participate in OSPF according to this configuration statement? (Choose three.)
![]()
|
A. |
FastEthernet0 /0 |
|
B. |
FastEthernet0 /1 |
|
C. |
Serial0/0 |
|
D. |
Serial0/1.102 |
|
E. |
Serial0/1.103 |
|
F. |
Serial0/1.104 |
Answer:
BCD
Explanation:
The "network 192.168.12.64 0.0.0.63 equals to network 192.168.12.64/26. This network has:
+ Increment: 64 (/26= 1111 1111.1111 1111.1111 1111.1100 0000) + Network address:
192.168.12.64
+ Broadcast address: 192.168.12.127
Therefore all interface in the range of this network will join OSPF.
Refer to the exhibit. C-router is to be used as a "router-on-a-stick" to route between the VLANs. All the interfaces have been properly configured and IP routing is operational. The hosts in the VLANs have been configured with the appropriate default gateway.
What is true about this configuration?
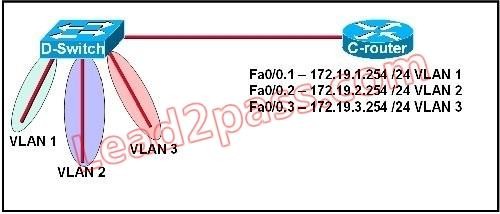
|
A. |
These commands need
to be added to the
configuration: C-router(config)# router eigrp
123 C-router(config-router)# network
172.19.0.0 |
|
B. |
These commands need
to be added to the
configuration: C-router(config)# router
ospf 1 C-router(config-router)# network 172.19.0.0 0.0.3.255 area
0 |
|
C. |
These commands need to be added to the configuration: C-router(config)# router
rip C-router(config-router)# network
172.19.0.0 |
|
D. |
No further routing configuration is required. |
Answer: D
Explanation:
Since all the same router (C-router) is the default gateway for all three VLANs, all traffic destined to a different VLAN will be sent to the C-router. The C-router will have knowledge of all three networks since they will appear as directly connected in the routing table. Since the C-router already knows how to get to all three networks, no routing protocols need to be configured.
Refer to the exhibit. Which address and mask combination represents a summary of the routes learned by EIGRP?
![]()
|
A. |
192.168.25.0 255.255.255.240 |
|
B. |
192.168.25.0 255.255.255.252 |
|
C. |
192.168.25.16 255.255.255.240 |
|
D. |
192.168.25.16 255.255.255.252 |
|
E. |
192.168.25.28 255.255.255.240 |
|
F. |
192.168.25.28 255.255.255.252 |
Answer: C
Explanation:
The binary version of 20 is 10100. The binary version of 16 is 10000. The binary version of 24 is 11000. The binary version of 28 is 11100.
The subnet mask is /28. The mask is 255.255.255.240.
Note:
From the output above, EIGRP learned 4 routes and we need to find out the summary of them:
+ 192.168.25.16
+ 192.168.25.20
+ 192.168.25.24
+ 192.168.25.28
-> The increment should be: 28 - 16 = 12 but 12 is not an exponentiation of 2 so we must choose 16 (24). Therefore the subnet mask is /28 (=1111 1111.1111 1111.1111 1111.11110000) =
255.255.255.240
So the best answer should be 192.168.25.16 255.255.255.240
Refer to the exhibit. Given the output for this command, if the router ID has not been manually set, what router ID will OSPF use for this router?
![]()
|
A. |
10.1.1.2 |
|
B. |
10.154.154.1 |
|
C. |
172.16.5.1 |
|
D. |
192.168.5.3 |
Answer: C
Explanation:
The highest IP address of all loopback interfaces will be chosen -> Loopback 0 will be chosen as the router ID.
Refer to the exhibit. Which rule does the DHCP server use when there is an IP address conflict?
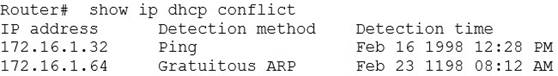
|
A. |
The address is removed from the pool
until the conflict is resolved. |
|
B. |
The address remains in the pool
until the conflict is resolved. |
|
C. |
Only the IP detected by Gratuitous ARP is removed
from the pool. |
|
D. |
Only the IP detected by Ping is removed from
the pool. |
|
E. |
The IP will
be shown, even
after the conflict is resolved. |
Answer: A
Explanation:
An address conflict occurs when two hosts use the same IP address. During address assignment, DHCP checks for conflicts using ping and gratuitous ARP. If a conflict is detected, the address is removed from the pool. The address will not be assigned until the administrator resolves the conflict.
Refer to the exhibit. When running EIGRP, what is required for RouterA to exchange routing updates with RouterC?
![]()
|
A. |
AS numbers must
be changed to match on all the
routers |
|
B. |
Loopback interfaces must be configured so a DR is elected |
|
C. |
The no auto-summary command is needed on Router A and Router
C |
|
D. |
Router B needs
to have two
network statements, one
for each connected network |
Answer: A
Explanation:
This question is to examine the understanding of the interaction between EIGRP routers. The following information must be matched so as to create neighborhood. EIGRP routers to establish, must match the following information:
1. AS Number;
2. K value.
Refer to the exhibit. A network technician is asked to design a small network with redundancy. The exhibit represents this design, with all hosts configured in the same VLAN.
What conclusions can be made about this design?
![]()
|
A. |
This design will
function as intended. |
|
B. |
Spanning-tree will need to be used. |
|
C. |
The router will not
accept the addressing scheme. |
|
D. |
The connection between
switches should be a trunk. |
|
E. |
The router interfaces must be encapsulated with the 802.1Q
protocol. |
Answer: C
Explanation:
Each interface on a router must be in a different network. If two interfaces are in the same network, the router will not accept it and show error when the administrator assigns it.
A network administrator is troubleshooting the OSPF configuration of routers R1 and R2. The routers cannot establish an adjacency relationship on their common Ethernet link.
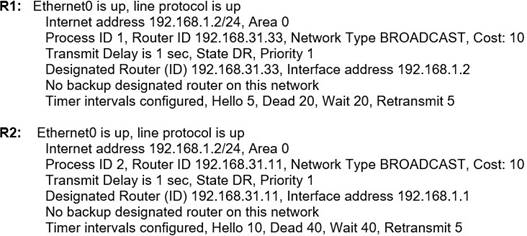
The graphic shows the output of the show ip ospf interface e0 command for routers R1 and R2. Based on the information in the graphic, what is the cause of this problem?
|
A. |
The OSPF area is not
configured properly. |
|
B. |
The priority on R1 should be set higher. |
|
C. |
The cost on R1 should be set higher. |
|
D. |
The hello and dead
timers are not configured properly. |
|
E. |
A backup designated router
needs to be added to the network. |
|
F. |
The OSPF process
ID numbers must
match. |
Answer: D
Explanation:
In OSPF, the hello and dead intervals must match and here we can see the hello interval is set to 5 on R1 and 10 on R2. The dead interval is also set to 20 on R1 but it is 40 on R2.
Refer to the graphic. R1 is unable to establish an OSPF neighbor relationship with R3. What are possible reasons for this problem? (Choose two.)
![]()
|
A. |
All of the routers need
to be configured for backbone Area 1. |
|
B. |
R1 and R2 are the DR and BDR, so OSPF will not establish neighbor adjacency with
R3. |
|
C. |
A static route
has been configured from R1 to R3 and prevents the neighbor adjacency from being established. |
|
D. |
The hello and dead interval timers
are not set to the same values
on R1 and R3. |
|
E. |
EIGRP is also
configured on these
routers with a lower administrative distance. |
|
F. |
R1 and R3 are configured in different areas. |
Answer: DF
Explanation:
This question is to examine the conditions for OSPF to create neighborhood. So as to make the two routers become neighbors, each router must be matched with the following items:
1. The area ID and its types;
2. Hello and failure time interval timer;
3. OSPF Password (Optional);
Refer to the exhibit. Which two statements are true about the loopback address that is configured on RouterB? (Choose two.)
![]()
|
A. |
It ensures that
data will be forwarded by RouterB. |
|
B. |
It provides stability for the OSPF process on RouterB. |
|
C. |
It specifies that the router ID for RouterB should be 10.0.0.1. |
|
D. |
It decreases the metric
for routes that
are advertised from
RouterB. |
|
E. |
It indicates that
RouterB should be elected the DR for the LAN. |
Answer: BC
Explanation:
A loopback interface never comes down even if the link is broken so it provides stability for the OSPF process (for example we use that loopback interface as the router-id).
The router-ID is chosen in the order below:
The highest IP address assigned to a loopback (logical) interface. If a loopback interface is not defined, the highest IP address of all active router's physical interfaces will be chosen. -The loopback interface will be chosen as the router ID of RouterB.
What are two reasons a network administrator would use CDP? (Choose two.)
|
A. |
to verify the type of cable interconnecting two devices |
|
B. |
to determine the status
of network services on a remote
device |
|
C. |
to obtain VLAN information from directly connected switches |
|
D. |
to verify Layer 2 connectivity between two devices when
Layer 3 fails |
|
E. |
to obtain the IP address of a connected device in order
to telnet to the device |
|
F. |
to determine the status of the routing
protocols between directly connected routers |
Answer: DE
What are two benefits of using VTP in a switching environment? (Choose two.)
|
A. |
It allows switches to read frame
tags. |
|
B. |
It allows ports to be assigned to VLANs automatically. |
|
C. |
It maintains VLAN consistency across a switched network. |
|
D. |
It allows frames from
multiple VLANs to use a single interface. |
|
E. |
It allows VLAN information to be automatically propagated throughout the
switching environment. |
Answer: CE
Explanation:
VLAN Trunk Protocol (VTP) reduces administration in a switched network. When you configure a new VLAN on one VTP server, the VLAN is distributed through all switches in the domain. This reduces the need to configure the same VLAN everywhere.
Which two statements are true about the command ip route 172.16.3.0 255.255.255.0 192.168.2.4? (Choose two.)
|
A. |
It establishes a static route
to the 172.16.3.0 network. |
|
B. |
It establishes a static
route to the
192.168.2.0 network. |
|
C. |
It configures the router
to send any
traffic for an unknown destination to the 172.16.3.0 network. |
|
D. |
It configures the
router to send
any traffic for
an unknown destination out the interface with the address
192.168.2.4. |
|
E. |
It uses the default
administrative distance. |
|
F. |
It is a route that
would be used last if other routes
to the same
destination exist. |
Answer:
AE
Which three statements are typical characteristics of VLAN arrangements? (Choose three.)
|
A. |
A new switch
has no VLANs
configured. |
|
B. |
Connectivity between VLANs requires a Layer 3
device. |
|
C. |
VLANs typically decrease the number
of collision domains. |
|
D. |
Each VLAN uses a separate address space. |
|
E. |
A switch maintains a separate bridging table for each
VLAN. |
|
F. |
VLANs cannot span
multiple switches. |
Answer:
BDE
Explanation:
To communicate between two different VLANs we need to use a Layer 3 device like router or Layer 3 switch -> B is correct.
VLANs don’t affect the number of collision domains, they are the same -> C is not correct. Typically, VLANs increase the number of broadcast domains.
We must use a different network (or sub-network) for each VLAN. For example we can use 192.168.1.0/24 for VLAN 1, 192.168.2.0/24 for VLAN 2 -> D is correct.
A switch maintains a separate bridging table for each VLAN so that it can send frame to ports on the same VLAN only. For example, if a PC in VLAN 2 sends a frame then the switch look-ups its bridging table and only sends frame out of its ports which belong to VLAN 2 (it also sends this frame on trunk ports) -> E is correct.
If all OSPF routers in a single area are configured with the same priority value, what value does a router use for the OSPF router ID in the absence of a loopback interface?
|
A. |
the IP address
of the first
Fast Ethernet interface |
|
B. |
the IP address of the console
management interface |
|
C. |
the highest IP address among its active
interfaces |
|
D. |
the lowest IP address among its active
interfaces |
|
E. |
the priority value
until a loopback interface is configured |
Answer: C
Explanation:
A router ID is determined in the following order:
1. using the router-id command
under the OSPF process to statically configure the router ID.
2. using the highest IP address of the router’s
loopback interfaces.
3. using the highest IP address of the router’s
active physical interfaces.
The OSPF Hello protocol performs which of the following tasks? (Choose two.)
|
A. |
It provides dynamic neighbor discovery. |
|
B. |
It detects unreachable neighbors in 90 second
intervals. |
|
C. |
It maintains neighbor relationships. |
|
D. |
It negotiates correctness parameters between neighboring interfaces. |
|
E. |
It uses timers to elect the router with the fastest links as the designated router. |
|
F. |
It broadcasts hello
packets throughout the internetwork to discover all
routers that are running OSPF. |
Answer:
AC
What are two requirements for an HSRP group? (Choose two.)
|
A. |
exactly one active
router |
|
B. |
one or more standby
routers |
|
C. |
one or more
backup virtual routers |
|
D. |
exactly one standby active
router |
|
E. |
exactly one backup virtual router |
Answer: AB
Explanation:
Exactly one active router: Only one Active Router per HSRP group will be elected based on highest priority. In case of equal priority, Highest IP address will be elected as Active Router. One or more standby routers: There can be one or more Standby Routers.
Which command can you enter to determine the addresses that have been assigned on a DHCP Server?
|
A. |
Show ip DHCP
database. |
|
B. |
Show ip DHCP pool. |
|
C. |
Show ip DHCP binding. |
|
D. |
Show ip DHCP
server statistic. |
Answer: C
Explanation:
Router#show ip dhcp binding - Displays a list of all bindings created.
On a corporate network, hosts on the same VLAN can communicate with each other, but they are unable to communicate with hosts on different VLANs. What is needed to allow communication between the VLANs?
|
A. |
a router with subinterfaces configured on the physical interface that is connected to the switch |
|
B. |
a router with an IP address on the physical interface connected to the switch |
|
C. |
a switch with an access link
that is configured between the switches |
|
D. |
a switch with
a trunk link
that is configured between the switches |
Answer:
A
Explanation:
Different VLANs can't communicate with each other , they can communicate with the help of Layer3 router. Hence , it is needed to connect a router to a switch , then make the sub-interface on the router to connect to the switch, establishing Trunking links to achieve communications of devices which belong to different VLANs.
Which IPv6 address block forwards packets to a multicast address rather than a unicast address?
|
A. |
2000::/3 |
|
B. |
FC00::/7 |
|
C. |
FE80::/10 |
|
D. |
FF00::/12 |
Answer: D
Explanation:
Multicast: FF00/8 -- FF00:: - FFFF::
Global Unicast: 2000::/3, 2001::/3, 2002::/4, 2001:db8::/32
Link Local Unicast: FE80::/10 -- FE80:: - FEBF::
Unique Local Unicast: FC00::/7 -- FC00:: - FDFF::
Loopback: ::1/128
What is the expected outcome when an EUI-64 address is generated?
|
A. |
The seventh bit of original MAC address of the interface is inverted |
|
B. |
The interface ID is configured as a random
64-bit value |
|
C. |
The characters FE80 are
inserted at the beginning of the MAC address of the interface |
|
D. |
The MAC address
of the interface is used as the interface ID without modification |
Answer:
A
Explanation:
The EUI-64 format interface ID is derived from the 48-bit MAC address by inserting the hexadecimal number fffe between the upper 3 bytes (OUI field) and the lower 3 vendor assigned bytes of the MAC address. Then, the seventh bit of the first octet is inverted. (In a MAC address, this bit indicates the scope and has a value of 1 for global scope and 0 for local scope; it will be 1 for globally unique MAC addresses. In the EUI-64 format, the meaning of this bit is opposite, so the bit is inverted.)
What is the difference regrading reliability and communication type between TCP and UDP?
|
A. |
TCP is reliable and is a connectionless protocol; UDP is not
reliable and is a connection-oriented protocol. |
|
B. |
TCP is not reliable and is a connectionless protocol; UDP is reliable and is a connection-oriented
protocol. |
|
C. |
TCP is reliable and
is a connection-oriented protocol; UDP is not
reliable and is a connectionless protocol. |
|
D. |
TCP is not reliable and is a connection-oriented protocol; UDP is reliable and is a connectionless
protocol. |
Answer: C
Router R1 must send all traffic without a matching routing-table entry to 192.168.1.1. Which configuration accomplishes this task?
|
A. |
R1#
config t R1(config)# ip routing R1(config)# ip route default-route 192.168.1.1 |
|
B. |
R1# config t R1(config)# ip routing R1(config)# ip route 0.0.0.0
0.0.0.0 192.168.1.1 |
|
C. |
R1# config t R1(config)# ip routing R1(config)# ip route 192.168.1.1 0.0.0.0 0.0.0.0 |
|
D. |
R1# config t R1(config)# ip routing R1(config)# ip default-gateway 192.168.1.1 |
Answer:
B
Explanation:
This text appears to be from a L3 switch. On a router there is no need to turn on (config)# "ip routing" first and then the default route command.
Which function dose the range of private IPv4 addresses perform?
|
A. |
allow multiple companies to each use the same
address without conflicts |
|
B. |
provides a direct connection for hosts from outside of the enterprise network |
|
C. |
ensues that
NAT is not required to reach the internet with
private range addressing |
|
D. |
enable secure communications to the internet for all external hosts |
Answer:
A
Which purpose does a northbound API serve in a controller-based networking architecture?
|
A. |
communicates between the controller and the physical network hardware |
|
B. |
reports device
errors to a
controller |
|
C. |
generates statistics for network hardware and traffic |
|
D. |
facilitates communication between
the controller and the applications |
Answer: D
How do traditional campus device management and Cisco DNA Center device management differ in regards to deployment?
|
A. |
Cisco DNA Center
device management can be implemented at a lower
cost than most
traditional campus device
management options. |
|
B. |
Traditional campus
device management schemes can typically deploy
patches and updates
more quickly than Cisco DNA Center device management. |
|
C. |
Cisco DNA Center
device management can deploy a network more
quickly than traditional campus device management. |
|
D. |
Traditional campus
device management allows
a network to scale more
quickly than with
Cisco DNA Center device management. |
Answer: C
What are two fundamentals of virtualization? (Choose two.)
|
A. |
It allows multiple operating systems and applications to run independently on one physical server. |
|
B. |
It allows a physical router to directly connect NICs from
each virtual machine into the network. |
|
C. |
The environment must be configured with one hypervisor that serves solely
as a network manager to monitor SNMP traffic. |
|
D. |
It allows logical network devices to move traffic
between virtual machines and the rest
of the |
|
|
physical network. |
|
E. |
It requires that
some servers, virtual
machines, and network gear reside on the Internet. |
Answer: AD
What is an advantage of Cisco DNA Center versus traditional campus device management?
|
A. |
It supports numerous extensibility options, including cross-domain adapters and
third-party SDKs. |
|
B. |
It enables easy autodiscovery of network elements in a brownfield deployment. |
|
C. |
It is designed primarily to provide network
assurance. |
|
D. |
It supports high availability for management functions when operating in cluster mode. |
Answer:
A
What occurs to frames during the process of frame flooding?
|
A. |
Frames are sent
to all ports,
including those that are assigned to other VLANs. |
|
B. |
Frames are sent to every port
on the switch
that has a matching entry
in MAC address
table. |
|
C. |
Frames are sent to every port on the switch in the same
VLAN except from
the originating port. |
|
D. |
Frames are sent
to every port
on the switch
in the same
VLAN. |
Answer: C
Explanation:
Frame flooding would be restricted to the devices that are in that VLAN. With a potential loop issue the flooding could occur from the switch NOT having a device match nor location in the MAC table. B would describe a broadcast.
Which action must be taken to assign a global unicast IPv6 address on an interface that is derived from the MAC address of that interface?
|
A. |
explicitly assign a link-local address |
|
B. |
disable the EUI-64 bit
process |
|
C. |
enable SLAAC
on an interface |
|
D. |
configure a stateful DHCPv6 server on the network |
Answer: C
Explanation:
SLAAC stands for Stateless Address Autoconfiguration and the name pretty much explains what it does. It is a mechanism that enables each host on the network to auto-configure a unique IPv6 address without any device keeping track of which address is assigned to which node.
Several new coverage cells are required to improve the Wi-Fi network of an organization. Which two standard designs are recommended? (Choose two.)
|
A. |
5GHz provides increased network capacity with
up to 23 nonoverlapping channels. |
|
B. |
5GHz channel selection requires an autonomous access point. |
|
C. |
Cells that
overlap one another
are configured to use nonoverlapping channels. |
|
D. |
Adjacent cells
with overlapping channels use a repeater access point. |
|
E. |
For maximum
throughput, the WLC is configured to dynamically set adjacent access
points to the channel. |
Answer:
AC
Explanation:
The channels for 5 GHz are 36, 40, 44, 48. For 5 GHz, you can set channels to Automatic, 36,
40, 44, 48, 52, 56, 60, 64, 100, 104, 108, 112, 116, 132, 136, 140, 149, 153, 157, 161, or 165.
For the 5 GHz radio, up to 23 non-overlapping channels are offered. https://www.cisco.com/c/en/us/support/docs/smb/wireless/CB-Wireless-Mesh/2069-tz-Changing- RF-Channels.html
How do TCP and UDP differ in the way they provide reliability for delivery of packets?
|
A. |
TCP does not guarantee delivery or error checking to ensure that
there is no corruption of data, UDP provides message acknowledgement and retransmits data if lost. |
|
B. |
TCP provides flow control to avoid overwhelming a receiver by sending too
many packets at once, UDP sends packets to the
receiver in a continuous stream without checking. |
|
C. |
TCP is a connectionless protocol that does not provide
reliable delivery of data; UDP
is a connection- oriented
protocol that uses sequencing to provide reliable delivery. |
|
D. |
TCP uses windowing to deliver packets reliably; UDP provides reliable message transfer between hosts by establishing a three-way handshake. |
Answer: B
What are two differences between optical-fiber cabling and copper cabling? (Choose two.)
|
A. |
A BNC connector is used for fiber connections |
|
B. |
The glass core component is encased in a cladding |
|
C. |
The data can pass through the cladding |
|
D. |
Light is transmitted through
the core of the fiber |
|
E. |
Fiber connects to physical interfaces using RJ-45 connections |
Answer: BD
How does CAPWAP communicate between an access point in local mode and a WLC?
|
A. |
The access point
must not be connected to the wired
network, as it would create
a loop |
|
B. |
The access point must
be connected to the same
switch as the WLC |
|
C. |
The access point must
directly connect to the WLC using a copper cable |
|
D. |
The access
point has the ability to link to any switch
in the network, assuming connectivity to the
WLC |
Answer: D
Explanation:
The Control And Provisioning of Wireless Access Points is a point to point tunnel between the AP's you deploy out in the office space and the central WLC device sitting in your datacentre.
What are two descriptions of three-tier network topologies? (Choose two.)
|
A. |
The distribution layer
runs Layer 2 and Layer
3 technologies |
|
B. |
The network core is designed to maintain continuous connectivity when devices fail |
|
C. |
The access layer manages routing between devices in different domains |
|
D. |
The core layer maintains wired connections for each host |
|
E. |
The core and distribution layers
perform the same
functions |
Answer: AB
Explanation:
Access: Provides a connection point (access) for end-user devices. Does not forward frames between two other access switches under normal circumstances.
Distribution: Provides an aggregation point for access switches, providing connectivity to the rest of the devices in the LAN, forwarding frames between switches, but not connecting directly to end-user devices.
The distribution layer is where redistribution of routing protocols should be performed. It should never be performed at the core or access layer.
Core: Aggregates distribution switches in very large campus LANs, providing very high forwarding rates for the larger volume of traffic due to the size of the network.
Only switching between campus (distribution) switches should be performed at the core layer. Nothing should be done to slow down forwarding of traffic, such as using ACLs, supporting clients, or routing between VLANs.
Core layer switches are commonly set up in a star topology. This is because core layer switches connect multiple campuses via distribution layer switches.
Which type of ipv6 address is publicly routable in the same way as ipv4 public addresses?
|
A. |
multicast |
|
B. |
unique local |
|
C. |
link-local |
|
D. |
global unicast |
Answer: D
Explanation:
Global unicast addresses (GUAs), also known as aggregatable global unicast addresses, are globally routable and reachable in the IPv6 Internet. They are equivalent to public IPv4 addresses. They play a significant role in the IPv6 addressing architecture.
A corporate office uses four floors in a building.
- Floor 1 has 24 users.
- Floor 2 has 29 users.
- Floor 3 has 28 users.
- Floor 4 has 22 users.
Which subnet summarizes and gives the most efficient distribution of IP addresses for the router configuration?
|
A. |
192.168.0.0/24 as summary and
192.168.0.0/28 for each
floor |
|
B. |
192.168.0.0/23 as summary and 192.168.0.0/25 for
each floor |
|
C. |
192.168.0.0/25
as summary and
192.168.0.0/27 for each
floor |
|
D. |
192.168.0.0/26 as summary and
192.168.0.0/29 for each
floor |
Answer: C
Refer to the exhibit. An engineer must add a subnet for a new office that will add 20 users to the network. Which IPv4 network and subnet mask combination does the engineer assign to minimize wasting addresses?
![]()
|
A. |
10.10.225.48 255.255.255.240 |
|
B. |
10.10.225.32 255.255.255.240 |
|
C. |
10.10.225.48 255.255.255.224 |
|
D. |
10.10.225.32 255.255.255.224 |
Answer: D
Explanation:
Find the subnet mask
* To have 20 User in a subnet We have to use /27 prefix
*
So Host count for /27 prefix is (2^5-2)=30
*
Subnet Mask for /27 prefix
is (sum of Network bits (128+64+32)=224, so 255.255.255.224
Find the network ID
* As per the /27 prefix each subnet has 30 host and 32 including network
ID & Broadcast ID
* so first network ID is 10.10.255.0 and the second will be 10.10.255.32
What is a characteristic of spine-and-leaf architecture?
|
A. |
Each link between
leaf switches allows
for higher bandwidth. |
|
B. |
It provides greater predictability on STP blocked
ports. |
|
C. |
It provides variable latency. |
|
D. |
Each device is separated by the same
number of hops. |
Answer: D
Refer to the exhibit. The network administrator wants VLAN 67 traffic to be untagged between Switch 1 and Switch 2, while all other VLANs are to remain tagged. Which command accomplishes this task?
![]()
|
A. |
switchport access vlan
67 |
|
B. |
switchport trunk
allowed vlan 67 |
|
C. |
switchport private-vlan association host 67 |
|
D. |
switchport trunk native
vlan 67 |
Answer: D
Explanation:
Native VLAN: The native VLAN is the one into which untagged traffic will be put when it’s received on a trunk port. This makes it possible for your VLAN to support legacy devices or devices that don’t tag their traffic like some wireless access points and simply network attached devices.
Which two command sequences must be configured on a switch to establish a Layer 3 EtherChannel with an open-standard protocol? (Choose two.)
|
A. |
interface GigabitEthernet0/0/1
channel-group 10 mode auto |
|
B. |
interface GigabitEthernet0/0/1 channel-group 10 mode on |
|
C. |
interface port-channel 10 no switchport |
|
|
ip address 172.16.0.1 255.255.255.0 |
|
D. |
interface GigabitEthernet0/0/1
channel-group 10 mode active |
|
E. |
interface port-channel 10 switchport switchport mode trunk |
Answer: CD
Refer to the exhibit. Which two commands were used to create port channel 10? (Choose two.)
![]()
|
A. |
int range g0/0-1 channel-group 10 mode active |
|
B. |
int range
g0/0-1 channel-group 10 mode desirable |
|
C. |
int range g0/0-1 channel-group 10 mode passive |
|
D. |
int range g0/0-1 channel-group 10 mode auto |
|
E. |
int range
g0/0-1 channel-group 10 mode
on |
Answer: AC
Explanation:
PAgP- Disirable/Auto (Link formation)
LACP- Active/Active or Active/Passive (Link formation)
Refer to the exhibit. An administrator is tasked with configuring a voice VLAN. What is the expected outcome when a Cisco phone is connected to the GigabitEthernet 3/1/4 port on a switch?
![]()
|
A. |
The phone and a workstation that is connected to the phone
do not have
VLAN connectivity. |
|
B. |
The phone sends
and receives data in VLAN
50, but a workstation connected to the phone
sends and receives data in VLAN 1. |
|
C. |
The phone
sends and receives data in VLAN
50, but a workstation connected to the phone
has no VLAN connected. |
|
D. |
The phone and
a workstation that
is connected to the phone
send and receive data in VLAN
50. |
Answer:
B
Refer to the exhibit. Which action is expected from SW1 when the untagged frame is received on the GigabitEthernet0/1 interface?
![]()
|
A. |
The frame is processed in VLAN 1 |
|
B. |
The frame is processed in VLAN 11 |
|
C. |
The frame is processed in VLAN 5 |
|
D. |
The frame is dropped |
Answer: C
Refer to the exhibit. What two conclusions should be made about this configuration? (Choose two.)
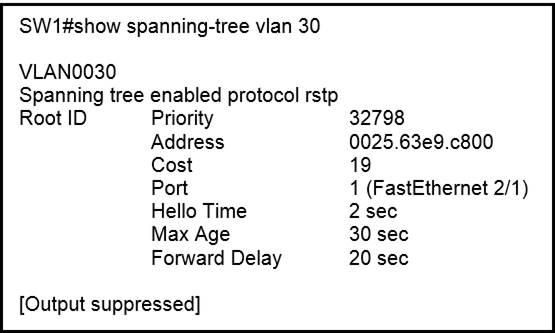
|
A. |
The root port
is FastEthernet 2/1 |
|
B. |
The designated port is FastEthernet 2/1 |
|
C. |
The spanning-tree mode is PVST+ |
|
D. |
This is a root
bridge |
|
E. |
The spanning-tree mode is Rapid
PVST+ |
Answer:
AE
A network engineer must create a diagram of a multivendor network. Which command must be configured on the Cisco devices so that the topology of the network can be mapped?
|
A. |
Device(config)#lldp run |
|
B. |
Device(config)#cdp run |
|
C. |
Device(config-if)#cdp enable |
|
D. |
Device(config)#flow-sampler-map topology |
Answer:
A
Explanation:
cdp is cisco-proprietary whereas lldp is open standard. as well as cdp is enabled by default in all cisco devices.
How do AAA operations compare regarding user identification, user services, and access control?
|
A. |
Authorization provides access
control, and authentication tracks user services |
|
B. |
Authentication identifies users, and accounting tracks user services |
|
C. |
Accounting tracks user
services, and authentication provides access control |
|
D. |
Authorization identifies users,
and authentication provides access control |
Answer:
B
Explanation:
Authentication, Identify users Authorization, access control Accounting, track user services
What is difference between RADIUS and TACACS+?
|
A. |
RADIUS logs all commands that
are entered by the administrator, but TACACS+ logs
only start, stop, and interim commands. |
|
B. |
TACACS+ separates authentication and authorization, and RADIUS merges
them. |
|
C. |
TACACS+ encrypts only password information, and RADIUS encrypts the entire payload. |
|
D. |
RADIUS is most
appropriate for dial
authentication, but TACACS+
can be used
for multiple types of authentication. |
Answer: B
Explanation:
RADIUS combines authentication and authorization. The access-accept packets sent by the RADIUS server to the client contain authorization information. This makes it difficult to decouple authentication and authorization.
TACACS+ uses the AAA architecture, which separates AAA. This allows separate authentication solutions that can still use TACACS+ for authorization and accounting. For example, with TACACS+, it is possible to use Kerberos authentication and TACACS+ authorization and accounting.
What is a difference between local AP mode and FlexConnect AP mode?
|
A. |
Local AP mode creates two
CAPWAP tunnels per
AP to the WLC |
|
B. |
Local AP mode causes
the AP to behave as if it were an autonomous AP |
|
C. |
FlexConnect AP mode fails
to function if the AP loses connectivity with the WLC |
|
D. |
FlexConnect AP mode
bridges the traffic from the AP to the
WLC when local
switching is configured |
Answer: A
Explanation:
In local mode, an AP creates two CAPWAP tunnels to the WLC. One is for management, the other is data traffic. This behavior is known as "centrally switched" because the data traffic is switched(bridged) from the ap to the controller where it is then routed by some routing device. https://community.cisco.com/t5/wireless-and-mobility/what-s-the-difference-between-local-mode- and-flex-connect-mode/td-p/2532657
Refer to the exhibit. Which configuration issue is preventing the OSPF neighbor relationship from being established between the two routers?
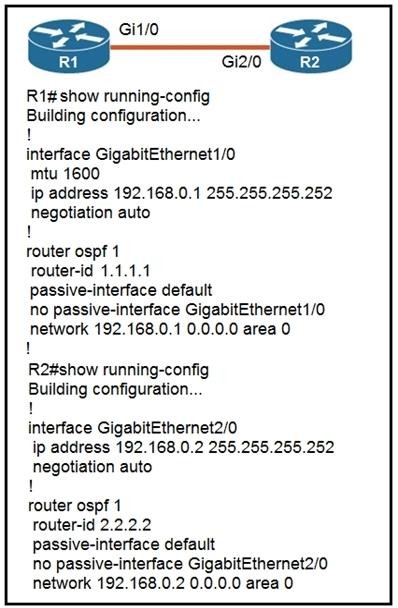
|
A. |
R1 has an incorrect network
command for interface Gi1/0. |
|
B. |
R2 should have its
network command in area 1. |
|
C. |
R1 interface Gi1/0 has
a larger MTU
size. |
|
D. |
R2 is using
the passive-interface default command. |
Answer: C
Explanation:
If the Interface MTU field in the Database Description packet indicates an IP datagram size that is larger than the router can accept on the receiving interface without fragmentation, the Database Description packet is rejected.
Refer to the exhibit. Router R1 is running three different routing protocols. Which route
characteristic is used by the router to forward the packet that it receives for destination IP 172.16.32.1?
![]()
|
A. |
longest prefix |
|
B. |
administrative distance |
|
C. |
cost |
|
D. |
metric |
Answer: A
Explanation:
/27 is the Highest prefix inclusive of the destination IP address therefore the router uses that route based on the Longest Prefix First rule.
Refer to the exhibit. Router R1 Fa0/0 cannot ping router R3 Fa0/1. Which action must be taken in router R1 to help resolve the configuration issue?
![]()
|
A. |
set the default gateway as 20.20.20.2 |
|
B. |
configure a static
route with Fa0/1
as the egress
interface to reach
the 20.20.2.0/24 network |
|
C. |
configure a static route
with 10.10.10.2 as the next
hop to reach
the 20.20.20.0/24 network |
|
D. |
set the default network as 20.20.20.0/24 |
Answer: C
By default, how does EIGRP determine the metric of a route for the routing table?
|
A. |
It uses the
bandwidth and delay
values of the path to calculate the route metric. |
|
B. |
It uses a default
metric of 10 for all routes that
are learned by the router. |
|
C. |
It counts
the number of hops between the receiving and
destination routers and
uses that value as the metric. |
|
D. |
It uses
a reference bandwidth and the actual
bandwidth of the connected link
to calculate the route metric. |
Answer:
A
Explanation:
EIGRP uses the minimum bandwidth on the path to a destination network and the total delay to compute routing metrics.
A packet is destined for 10.10.1.22. Which static route does the router choose to forward the packet?
|
A. |
ip route
10.10.1.0 255.255.255.240 10.10.255.1 |
|
B. |
ip route 10.10.1.20 255.255.255.252
10.10.255.1 |
|
C. |
ip route 10.10.1.16 255.255.255.252
10.10.255.1 |
|
D. |
ip route 10.10.1.20 255.255.255.254
10.10.255.1 |
Answer: B
Explanation:
10.10.1.20 /30
20 = .000101[00] network
21 = .000101[01] host
22 = .000101[10] host
23 = .000101[11] broadcast
Refer to the exhibit. How does the router manage traffic to 192.168.12.16?
![]()
|
A. |
It chooses the
EIGRP route because it has the lowest administrative distance. |
|
B. |
It load-balances traffic
between all three
routes. |
|
C. |
It chooses the
OSPF route because it has the
longest prefix inclusive of the destination address. |
|
D. |
It selects the RIP route
because it has the longest
prefix inclusive of the destination address. |
Answer: D
Explanation:
https://subnet.ninja/calculator-results/
192.168.12.16 is outside OSPF 192.168.12.0/28 and would not be a usable IP address in 192.168.12.16/28 network.
Would work for RIP as it is a 30 IP address range.
What are two reasons for an engineer to configure a floating static route? (Choose two.)
|
A. |
to enable fallback static routing when the dynamic
routing protocol fails |
|
B. |
to route traffic differently based on the source IP of the
packet |
|
C. |
to automatically route traffic
on a secondary path when
the primary path
goes down |
|
D. |
to support load balancing via static routing |
|
E. |
to control the return path
of traffic that is sent from the
router |
Answer: AC
Explanation:
Floating static routes are static routes that have an administrative distance greater than the administrative distance of dynamic routes. Administrative distances can be configured on a static route so that the static route is less desirable than a dynamic route. In this manner, the static route is not used when the dynamic route is available. However, if the dynamic route is lost, the static route can take over, and traffic can be sent through this alternate route. If this alternate route is provided using a DDR interface, then that interface can be used as a backup mechanism. Used when primary route is Not available.
Refer to the exhibit. How does router R1 handle traffic to 192.168.10.16?
![]()
|
A. |
It selects the IS-IS route
because it has the shortest prefix inclusive of the destination address |
|
B. |
It selects the RIP route because it has the longest prefix
inclusive of the destination address |
|
C. |
It selects the OSPF
route because it has the lowest cost |
|
D. |
It selects the EIGRP route
because it has the lowest
administrative distance |
Answer: B
Explanation:
1. Longest Prefix
2. Administrative distance
3. Metric
https://packetlife.net/blog/2010/aug/16/route-preference/
Refer to the exhibit. A router reserved these five routes from different routing information sources. Which two routes does the router install in its routing table? (Choose two)
![]()
|
A. |
OSPF route 10.0.0.0/30 |
|
B. |
IBGP route
10.0.0.0/30 |
|
C. |
OSPF route
10.0.0.0/16 |
|
D. |
EIGRP route
10.0.0.1/32 |
|
E. |
RIP route 10.0.0.0/30 |
Answer: AD
Explanation:
One will be selected among the three /30 mask, other one will be /16 mask and last one will be
/32 mask.
Among the three /30 mask routes, OSPF will be selected since OSPF has lowest AD which is 110 whereas RIP has AD value of 120 and iBGP has AD value of 200.
Refer to the exhibit. To which device does Router1 send packets that are destined to host 10.10.13.165?
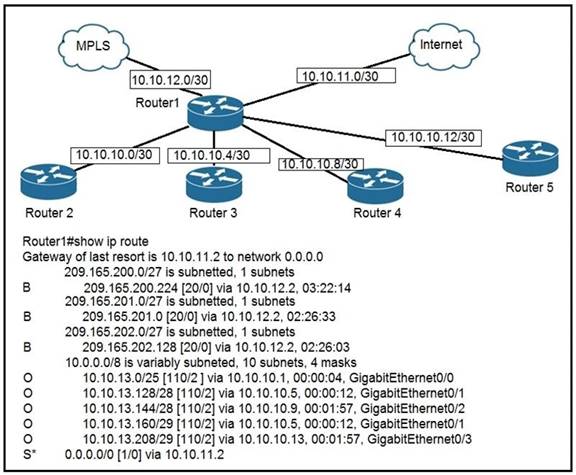
|
A. |
Router2 |
|
B. |
Router3 |
|
C. |
Router4 |
|
D. |
Router5 |
Answer: B
Explanation:
To reach the host 10.10.13.165 the router choose the route OSPF 10.10.13.160/29 (from 10.10.13.160 to 10.10.13.167) because include the destination address. Now Router 3 is the next hop for this route because the network between Router1 and Router3 it's a 10.10.10.4/30 (from 10.10.10.4 to 10.10.10.7 usable ip for host are .5 and .6) therefore Router3 is the next hop that you see in the routing table of Router1 == 10.10.10.5.
R1 has learned route 10.10.10.0/24 via numerous routing protocols. Which route is installed?
|
A. |
route with the next hop that has the highest IP |
|
B. |
route with
the lowest cost |
|
C. |
route with
the lowest administrative distance |
|
D. |
route with the shortest prefix
length |
Answer: C
Explanation:
Route Preference:
1. Longest Prefix
2. Administrative Distance
3. Metric
In this specific question, the first option is: Administrative Distance.
Which two minimum parameters must be configured on an active interface to enable OSPFV2 to operate? (Choose two.)
|
A. |
OSPF process ID |
|
B. |
OSPF MD5 authentication key |
|
C. |
OSPF stub
flag |
|
D. |
IPv6 address |
|
E. |
OSPF area |
Answer: AE
Refer to the exhibit. What commands are needed to add a subinterface to Ethernet0/0 on R1 to allow for VLAN 20, with IP address 10.20.20.1/24?
![]()
|
A. |
R1(config)#interface
ethernet0/0 R1(config)#encapsulation dot1q 20 R1(config)#ip address
10.20.20.1 255.255.255.0 |
|
B. |
R1(config)#interface ethernet0/0.20
R1(config)#encapsulation dot1q 20 R1(config)#ip address 10.20.20.1 255.255.255.0 |
|
C. |
R1(config)#interface
ethernet0/0.20 R1(config)#ip address 10.20.20.1 255.255.255.0 |
|
D. |
R1(config)#interface ethernet0/0 R1(config)#ip address 10.20.20.1 255.255.255.0 |
Answer: B
Explanation:
For a Router on a stick, you need to:
1. create a sub-interface
2. encapsulate dot1q with the VLAN ID
3. Assign an IP address
Which function does an SNMP agent perform?
|
A. |
It sends information about MIB variables in response to requests from
the NMS |
|
B. |
It manages routing between
Layer 3 devices in a network |
|
C. |
It coordinates user authentication between a network device and a TACACS+ or RADIUS server |
|
D. |
It requests information from remote network
nodes about catastrophic system events |
Answer:
A
Explanation:
https://www.cisco.com/c/en/us/td/docs/ios-xml/ios/snmp/configuration/xe-16/snmp-xe-16- book/nm-snmp-cfg-snmp-support.html
What are two roles of the Dynamic Host Configuration Protocol (DHCP)? (Choose two.)
|
A. |
The DHCP server
assigns IP addresses without requiring the
client to renew
them. |
|
B. |
The DHCP server leases
client IP addresses dynamically. |
|
C. |
The DHCP client can
request up to four DNS server addresses. |
|
D. |
The DHCP server offers
the ability to exclude specific IP addresses from
a pool of IP addresses. |
|
E. |
The DHCP client
maintains a pool
of IP addresses it can
assign. |
Answer:
BD
Which command must be entered when a device is configured as an NTP server?
|
A. |
ntp peer |
|
B. |
ntp master |
|
C. |
ntp authenticate |
|
D. |
ntp server |
Answer:
B
Explanation:
To configure a Cisco device as an Authoritative NTP Server, use the ntp master [stratum] command.To configure a Cisco device as a NTP client, use the command ntp server <IP address>. For example:Router(config)#ntp server 192.168.1.1. This command will instruct the router to query 192.168.1.1 for the time.
What event has occurred if a router sends a notice level message to a syslog server?
|
A. |
A certificate has
expired |
|
B. |
An interface line has
changed status |
|
C. |
A TCP connection has been torn
down |
|
D. |
An ICMP connection has been built |
Answer:
B
Explanation:
0 Emergencies System shutting down due to missing fan tray
1
Alerts Temperature limit exceeded
2
Critical Memory allocation failures
3
Errors Interface Up/Down
messages
4 Warnings Configuration file written to server, via SNMP request
5
Notifications Line protocol
Up/Down
6 Information Access-list violation logging
7 Debugging Debug messages
Refer to the exhibit. An engineer deploys a topology in which R1 obtains its IP configuration from DHCP. If the switch and DHCP server configurations are complete and correct.
Which two sets of commands must be configured on R1 and R2 to complete the task? (Choose two)
![]()
|
A. |
R1(config)# interface fa0/0 R1(config-if)# ip helper-address 198.51.100.100 |
|
B. |
R2(config)# interface gi0/0 R2(config-if)# ip helper-address 198.51.100.100 |
|
C. |
R1(config)#
interface fa0/0 R1(config-if)# ip address dhcp R1(config-if)# no shutdown |
|
D. |
R2(config)#
interface gi0/0 R2(config-if)# ip address dhcp |
|
E. |
R1(config)# interface fa0/0 R1(config-if)#
ip helper-address 192.0.2.2 |
Answer: BC
Explanation:
Note that DHCP server is behind R2 and R1 needs IP via DHCP. Therefore, R2 needs to be a relay agent. On R1 interface, ip address dhcp and R2 inside interface, ip helper-address 192.168.100.100 (dhcp server).
Refer to the exhibit. What configuration on RTR-1 denies SSH access from PC-1 to any RTR-1 interface and allows all other traffic?

|
A. |
|
|
B. |
|
|
C. |
|
|
D. |
|
Answer:
B
While examining excessive traffic on the network, it is noted that all incoming packets on an interface appear to be allowed even though an IPv4 ACL is applied to the interface. Which two misconfigurations cause this behavior? (Choose two.)
|
A. |
The ACL is empty |
|
B. |
A matching permit statement is too broadly
defined |
|
C. |
The packets fail to match any permit statement |
|
D. |
A matching deny statement is too high
in the access
list |
|
E. |
A matching permit
statement is too high in the access
list |
Answer: BE
Explanation:
Traffic might be permitted if the permit statement is too braid, meaning that you are allowing more traffic than what is specifically needed, or if the matching permit statement is placed ahead of the deny traffic. Routers will look at traffic and compare it to the ACL and once a match is found, the router acts accordingly to that rule.
The service password-encryption command is entered on a router. What is the effect of this configuration?
|
A. |
restricts unauthorized users
from viewing clear-text passwords in the
running configuration |
|
B. |
prevents network
administrators from configuring clear-text passwords |
|
C. |
protects the VLAN database from unauthorized PC connections on the switch |
|
D. |
encrypts the password exchange when a VPN tunnel
is established |
Answer:
A
Which WPA3 enhancement protects against hackers viewing traffic on the Wi-Fi network?
|
A. |
SAE encryption |
|
B. |
TKIP encryption |
|
C. |
scrambled encryption key |
|
D. |
AES encryption |
Answer:
A
Explanation:
WPA3 uses simultaneous authentication of equals (SAE) encryption and allows only WiFi devices that support WPA3 to join the virtual access point (VAP).
Refer to the exhibit. If the network environment is operating normally, which type of device must be connected to interface FastEthernet 0/1?
![]()
|
A. |
DHCP client |
|
B. |
access point |
|
C. |
router |
|
D. |
PC |
Answer: C
Explanation:
Routers are networki devices that are under Administrative control. Hence, they are configured Trusted in DAI and DHCP Snooping.
Refer to the exhibit. An administrator configures four switches for local authentication using passwords that are stored as a cryptographic hash. The four switches must also support SSH access for administrators to manage the network infrastructure. Which switch is configured correctly to meet these requirements?
![]()
|
A. |
SW1 |
|
B. |
SW2 |
|
C. |
SW3 |
|
D. |
SW4 |
Answer: C
Explanation:
Keyword local authentication: "login local" configuration Keyword cryptographic hash: "secret" configuration Keyword SSH access: "live vty 0 15" configuration
What benefit does controller-based networking provide versus traditional networking?
|
A. |
allows configuration and
monitoring of the network from one centralized point |
|
B. |
provides an added layer
of security to protect from
DDoS attacks |
|
C. |
combines control and data plane
functionality on a single device
to minimize latency |
|
D. |
moves from a two-tier to a three-tier network architecture to provide maximum
redundancy |
Answer:
A
How does Cisco DNA Center gather data from the network?
|
A. |
Devices use the call-home protocol to periodically send data to the controller |
|
B. |
Devices establish an IPsec tunnel
to exchange data
with the controller |
|
C. |
The Cisco
CLI Analyzer tool gathers data from each
licensed network device
and streams it to the controller |
|
D. |
Network devices use different services like SNMP, syslog, and streaming telemetry to send data to the controller |
Answer: D
Explanation:
Local Network Telemetry: Cisco DNA Center collects data from several different sources and protocols on the local network, including the following: traceroute; syslog; NetFlow; Authentication, Authorization, and Accounting (AAA); routers; Dynamic Host Configuration Protocol (DHCP); Telnet; wireless devices; Command-Line Interface (CLI); Object IDs (OIDs); IP SLA; DNS; ping; Simple Network Management Protocol (SNMP); IP Address Management (IPAM); MIB; Cisco Connected Mobile Experiences (CMX); and AppDynamics ®. The great breadth and depth of data collection allows Cisco DNA Center to give a clearer picture of the state of the network, clients, and applications. This data is kept on the Cisco DNA Center appliance locally (at your location) and is available for a period of 14 days. Local Network Telemetry is not transported to any other server nor is it sent to the cloud.
Drag and Drop Question
Drag and drop the attack-mitigation techniques from the left onto the types of attack that they mitigate on the right.
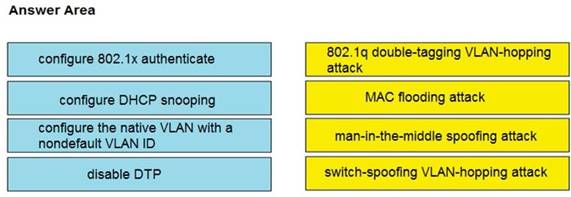
Answer:
![]()
Drag and Drop Question
Drag and drop the characteristics of networking from the left onto the correct networking types on the right.
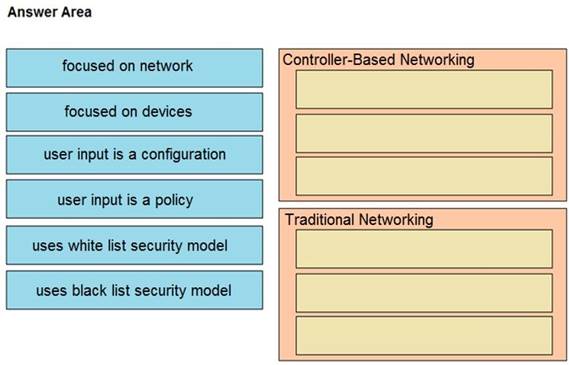
Answer:
![]()
Which statement about LLDP is true?
|
A. |
It is a Cisco proprietary protocol |
|
B. |
It is configured in global configuration mode. |
|
C. |
The LLDP update frequency is a fixed
value. |
|
D. |
It runs over
the transport layer. |
Answer: B
Explanation:
LLDP is for support with non-Cisco devices, runs on the data link layer, and lldp timer has a configurable range from 5 to 65534 sec, commands configured only from conf t.
What are two benefits of private IPv4 IP addresses? (Choose two.)
|
A. |
They are routed
the same as public IP
addresses. |
|
B. |
They are less costly
than public IP
addresses. |
|
C. |
They can be assigned to devices without Internet connections. |
|
D. |
They eliminate the necessity for NAT policies. |
|
E. |
They eliminate duplicate IP conflicts. |
Answer: BC
What is the authoritative source for an address lookup?
|
A. |
a recursive DNS
search |
|
B. |
the operating system cache |
|
C. |
the ISP local cache |
|
D. |
the browser cache |
Answer: A
What are two benefits that the UDP protocol provide for application traffic?(Choose two)
|
A. |
UDP traffic has lower overhead than TCP traffic |
|
B. |
UDP provides a built-in recovery mechanism to retransmit lost
packets. |
|
C. |
The CTL
field in the UDP packet
header enables a three-way handshake to establish the connection |
|
D. |
UDP maintains the connection state to provide
more stable connections than TCP. |
|
E. |
The application can use checksums to verify the integrity of application data |
Answer:
AE
Which two goals reasons to implement private IPv4 addressing on your network? (Choose two)
|
A. |
Comply with PCI
regulations |
|
B. |
Conserve IPv4
address |
|
C. |
Reduce the size
of the forwarding table on network
routers |
|
D. |
Reduce the risk
of a network security breach |
|
E. |
Comply with local
law |
Answer: BD
Which command is used to verify the DHCP relay agent address that has been set up on your Cisco IOS router?
|
A. |
show ip interface brief |
|
B. |
show ip dhcp bindings |
|
C. |
show ip
route |
|
D. |
show ip
interface |
|
E. |
show interface |
|
F. |
show ip dhcp
pool |
Answer: D
Explanation:
With that command you can see if the helper address (dhcp relay) is configured.
Router1#sh ip interface g0/0
GigabitEthernet0/0 is up, line protocol is up (connected) Internet address is 10.0.0.1/30
Broadcast address is 255.255.255.255 Address determined by setup command MTU is 1500 bytes
Helper address is 192.168.4.2
Drag and Drop Question
Drag and drop the characteristics of a cloud environment from the left onto the correct examples on the right.

Answer:
![]()
What is the primary purpose of a First Hop Redundancy Protocol?
|
A. |
It allows directly connected neighbors to share configuration information. |
|
B. |
It allows a router
to use bridge
priorities to create
multiple loop-free paths
to a single destination. |
|
C. |
It reduces
routing failures by allowing Layer
3 load balancing between OSPF neighbors that have the same
link metric. |
|
D. |
It reduces routing failures by allowing more than one
router to represent itself, as the
default |
gateway of a network.
Answer: D
Explanation:
A first hop redundancy protocol (FHRP) is a computer networking protocol which is designed to protect the default gateway used on a subnetwork by allowing two or more routers to provide backup for that address; in the event of failure of an active router, the backup router will take over.
Which technology must be implemented to configure network device monitoring with the highest security?
|
A. |
IP SLA |
|
B. |
syslog |
|
C. |
NetFlow |
|
D. |
SNMPv3 |
Answer: D
Explanation:
Netflow although related to security generally is just a data collection protocol whereas the whole point of SNMPv3 is that it's hardened.
What role does a hypervisor provide for each virtual machine in server virtualization?
|
A. |
infrastructure-as-a-service. |
|
B. |
Software-as-a-service |
|
C. |
control and distribution of physical resources |
|
D. |
services as a hardware controller. |
Answer: C
Explanation:
The hypervisor creates and manages virtual machines on a host computer and allocates physical system resources to them.
The SW1 interface g0/1 is in the down/down state. What are two reasons for the interface condition? (Choose two.)
|
A. |
There is a duplex mismatch |
|
B. |
There is a speed
mismatch |
|
C. |
There is a protocol mismatch |
|
D. |
The interface is shut down |
|
E. |
The interface is error-disabled |
Answer: BE
Explanation:
The interface is shut down - ADMIN DOWN / DOWN The interface is error-disabled - DOWN / DOWN There is a speed mismatch - DOWN / DOWN
Refer to Exhibit. The loopback1 interface of the Atlanta router must reach the loopback3 interface of the Washington router.
Which two static host routes must be configured on the NEW York router? (Choose two)
![]()
|
A. |
ipv6 route 2000::1/128 2012::1 |
|
B. |
ipv6 route
2000::3/128 2023::3 |
|
C. |
ipv6 route
2000::3/128 s0/0/0 |
|
D. |
ipv6 route
2000::1/128 2012::2 |
|
E. |
ipv6 route 2000::1/128 s0/0/1 |
Answer:
AB
What is the function of a server?
|
A. |
It transmits packets between hosts in the same
broadcast domain. |
|
B. |
It provides shared applications to end users. |
|
C. |
It routes traffic between
Layer 3 devices. |
|
D. |
It Creates security zones between trusted
and untrusted networks |
Answer:
B
What is a function of Wireless LAN Controller?
|
A. |
register with a single access
point that controls traffic between wired
and wireless endpoints. |
|
B. |
use SSIDs to distinguish between wireless clients. |
|
C. |
send LWAPP
packets to access
points. |
|
D. |
monitor activity on wireless and
wired LANs |
Answer: C
Explanation:
Lightweight APs (LAPs) is devices require no initial configuration. LAPs use the Lightweight Access Point Protocol (LWAPP) to communicate with a WLAN controller (WLC), as shown in the below figure. Controller-based APs are useful in situations where many APs are required in the network. As more APs are added, each AP is automatically configured and managed by the WLC.
![]()
In which two ways does a password manager reduce the chance of a hacker stealing a users password? (Choose two.)
|
A. |
It automatically provides a second authentication factor that is unknown to the original user. |
|
B. |
It uses an internal firewall to protect the password repository from unauthorized access. |
|
C. |
It protects against keystroke logging on a compromised device
or web site. |
|
D. |
It stores
the password repository on the local
workstation with built-in antivirus and anti-malware functionality |
|
E. |
It encourages users
to create stronger passwords. |
Answer: CE
Which type of information resides on a DHCP server?
|
A. |
a list of the available IP addresses in a pool |
|
B. |
a list of public
IP addresses and their corresponding names |
|
C. |
usernames and passwords for
the end users
in a domain |
|
D. |
a list of statically assigned MAC addresses |
Answer: A
Which technology is used to improve web traffic performance by proxy caching?
|
A. |
WSA |
|
B. |
Firepower |
|
C. |
ASA |
|
D. |
FireSIGHT |
Answer:
A
Which type of attack can be mitigated by dynamic ARP inspection?
|
A. |
worm |
|
B. |
malware |
|
C. |
DDoS |
|
D. |
man-in-the-middle |
Answer: D
Which goal is achieved by the implementation of private IPv4 addressing on a network?
|
A. |
provides an added
level of protection against Internet exposure |
|
B. |
provides a reduction in size of the forwarding table on network routers |
|
C. |
allows communication across the Internet to other private networks |
|
D. |
allows servers and
workstations to communicate across public network boundaries |
Answer:
A
Explanation:
For private IPv4 to cross Public networks would require some form of tunneling. Private does not route publicly.
Using direct sequence spread spectrum, which three 2.4-GHz channels are used to limit collisions?
|
A. |
1, 6, 11 |
|
B. |
1, 5, 10 |
|
C. |
1, 2, 3 |
|
D. |
5, 6, 7 |
Answer: A
A device detects two stations transmitting frames at the same time. This condition occurs after the first 64 bytes of the frame is received interface counter increments?
|
A. |
collision |
|
B. |
CRC |
|
C. |
runt |
|
D. |
late collision |
Answer: D
Explanation:
Collision occurs in the first 64 bytes.
A late collision occurs after the 512th bit (64th byte) of a frame has been transmitted by a device. Anything under 64byte frame is considered a runt.
What are two roles of Domain Name Services (DNS)? (Choose Two)
|
A. |
builds a flat
structure of DNS names for more efficient IP operations |
|
B. |
encrypts network
Traffic as it travels across
a WAN by default |
|
C. |
improves security by protecting IP addresses under
Fully Qualified Domain
Names (FQDNs) |
|
D. |
enables applications to identify resources by name instead
of IP address |
|
E. |
allows a single
host name to be shared
across more than one IP
address |
Answer: DE
When a WPA2-PSK WLAN is configured in the wireless LAN Controller, what is the minimum number of characters that in ASCll format?
|
A. |
6 |
|
B. |
8 |
|
C. |
12 |
|
D. |
18 |
Answer: B
Explanation:
WPA preshared keys must contain 8 to 63 ASCII text characters or 64 hexadecimal characters.
An engineer is configuring NAT to translate the source subnet of 10.10.0.0/24 to any one of three addresses: 192.168.3.1, 192.168.3.2, or 192.168.3.3. Which configuration should be used?
Which configuration should be used?
|
A. |
enable configure terminal ip nat pool mypool 192.168.3.1 192.168.3.3 prefix-length 30 route-map permit 10.10.0.0 255.255.255.0 |
|
|
ip nat outside destination list 1 pool
mypool interface g1/1 ip nat inside interface g1/2
ip nat outside |
|
B. |
enable configure terminal ip nat pool mypool 192.168.3.1 192.168.3.3 prefix-length 30 access-list 1 permit 10.10.0.0 0.0.0.255 ip nat outside destination list 1 pool
mypool interface g1/1 ip
nat inside interface g1/2 ip nat outside |
|
C. |
enable configure terminal ip nat pool mypool
192.168.3.1 192.168.3.3 prefix-length 30 access-list 1 permit 10.10.0.0 0.0.0.255 ip nat inside source list 1 pool mypool interface
g1/1 ip
nat inside interface g1/2 ip nat outside |
|
D. |
enable configure terminal ip nat pool mypool
192.168.3.1 192.168.3.3 prefix-length 30 access-list 1 permit 10.10.0.0 0.0.0.254 ip nat inside source list 1 pool mypool interface
g1/1 ip
nat inside interface g1/2 ip nat outside |
Answer: C
How do TCP and UDP differ in the way they guarantee packet delivery?
|
A. |
TCP uses checksum, acknowledgement, and retransmissions, and UDP uses
checksums only. |
|
B. |
TCP uses two-dimensional parity checks, checksums, and cyclic redundancy checks and UDP uses retransmissions only. |
|
C. |
TCP uses
checksum, parity checks, and retransmissions, and UDP uses
acknowledgements only. |
|
D. |
TCP uses retransmissions, acknowledgement and parity checks
and UDP uses cyclic
redundancy checks only. |
Answer:
A
Refer to the exhibit. A network administrator assumes a task to complete the connectivity between PC A and the File Server.
Switch A and Switch B have been partially configured with VLAN 10, 11, 12, and 13. What is the next step in the configuration?
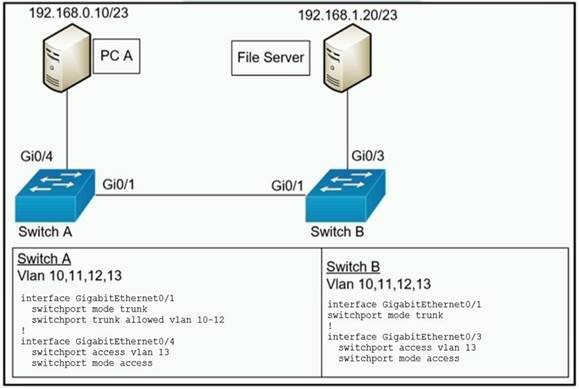
|
A. |
Add PC A to VLAN
10 and the File Server
to VLAN 11 fa VLAN
segmentation |
|
B. |
Add VLAN 13 to the trunk links
on Switch A and Switch
B for VLAN
propagation |
|
C. |
Add a router on a stick
between Switch A and Switch
B allowing for
Inter-VLAN routing. |
|
D. |
Add PC A to the same subnet
as the Fie Server allowing for intra-VLAN communication. |
Answer: B
Explanation:
They are not on different subnets. Subnet 192.168.0.0 /23 has 2^9 = 512 hosts, which spans an IP range of 192.168.0.0 - 192.168.1.255. Addresses 192.168.0.10 and 192.168.1.20 are on the same range and their respective interfaces are on the same VLAN. The only problem here is that the trunk link on Switch A doesn't allow VLAN 13, so "B" is correct.
Refer to the exhibit. What is the next hop address for traffic that is destined to host 10.0.1.5?
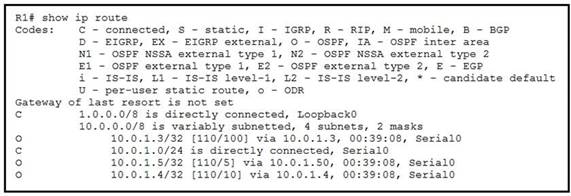
|
A. |
10.0.1.3 |
|
B. |
10.0.1.50 |
|
C. |
10.0.1.4 |
|
D. |
Loopback D |
Answer:
B
Explanation:
A /32 prefix represents a host, and this is the highest you can get with ipv4. The next hop is
10.0.1.50 as you can see where it says 'via 10.0.1.50'.
What are two benefits of controller-based networking compared to traditional networking?
|
A. |
controller-based
increases network bandwidth usage, while traditional lightens the load
on the network. |
|
B. |
controller-based inflates software costs, while
traditional decreases individual licensing costs |
|
C. |
Controller-based reduces network configuration complexity, while traditional increases the potential for errors |
|
D. |
Controller-based provides centralization of key IT functions. While traditional requires distributes management function |
|
E. |
controller-based allows for fewer network
failure, while traditional increases failure rates. |
Answer: CD
Refer to the exhibit. What action establishes the OSPF neighbor relationship without forming an adjacency?
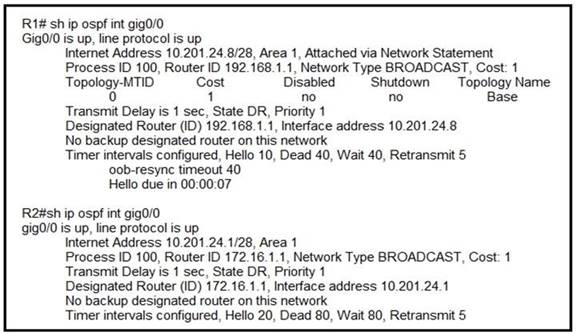
|
A. |
modify hello interval |
|
B. |
modify process
ID |
|
C. |
modify priority |
|
D. |
modify network type |
Answer:
A
What mechanism carries multicast traffic between remote sites and supports encryption?
|
A. |
ISATAP |
|
B. |
GRE over iPsec |
|
C. |
iPsec over
ISATAP |
|
D. |
GRE |
Answer:
B
Explanation:
Ipsec dosent support multicast, that is why GRE used with VPN, and as long as the GRE is not totally secure, the whole GRE. Encapsulation can be encapsulated in ipsec header so now we have both "mulitcast ability and security".
Refer to the exhibit. Which outcome is expected when PC_A sends data to PC_B after their initial communication?
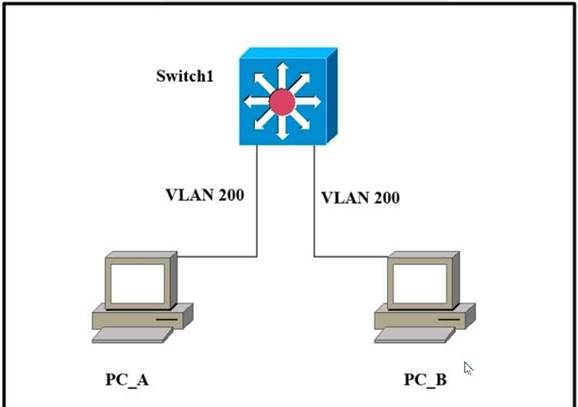
|
A. |
The switch rewrites the source and
destination MAC addresses with its own. |
|
B. |
The source MAC address is changed. |
|
C. |
The source and destination MAC addresses remain
the same. |
|
D. |
The destination MAC address is replaced with ffff.ffff.ffff. |
Answer: C
Explanation:
You have a TCP/IP network. This means that PC A and PC B have an IP address each. PC A knows PC B's address and creates an IP packet for PC B. Then, the packet (Layer 3) becomes an Ethernet frame (Layer 2): PC A gets PC B's MAC address and uses it as the destination L2 address.
When the frame arrives at SW1, the switch looks at the destination MAC address and controls (in its MAC table) to which port that address is associated. Then, the switch sends the frame to PC B through that port (forwarding phase).
The switch leaves unchanged BOTH the source and the destination MAC addresses inside the frame.
What is the purpose of the Cisco DNA Center controller?
|
A. |
to secure physical access to a data center |
|
B. |
to scan a network and generate a Layer 2 network diagram |
|
C. |
to securely manage and
deploy network devices |
|
D. |
to provide Layer
3 services to autonomous access
points |
Answer: C
Explanation:
Cisco DNA Center is a powerful network controller and management dashboard for secure access to networks and applications. It lets you take charge of your network, optimize your Cisco investment, and lower your IT spending.
Reference:
https://www.cisco.com/c/en/us/products/collateral/cloud-systems-management/dna-center/nb-06- dna-center-so-cte-en.html
An organization secures its network with multi-factor authentication using an authenticator app on employee smartphone. How is the application secured in the case of a user's smartphone being lost or stolen?
|
A. |
The application requires an administrator password to reactivate after
a configured Interval. |
|
B. |
The application requires the
user to enter
a PIN before
it provides the
second factor. |
|
C. |
The application challenges a user
by requiring an administrator password to reactivate when
the smartphone is rebooted. |
|
D. |
The application verifies that the user
is in a specific location before it provides the second factor. |
Answer: B
When the active router in an HSRP group fails, which router assumes the role and forwards packets?
|
A. |
backup |
|
B. |
standby |
|
C. |
listening |
|
D. |
forwarding |
Answer: B
Explanation:
HSRP usese Active/Standby VRRP usese Master/Backup
Refer to the exhibit. Router R2 is configured with multiple routes to reach network 10.1.1.0/24 from router R1. Which path is chosen by router R2 to reach the destination network 10.1.1.0/24?
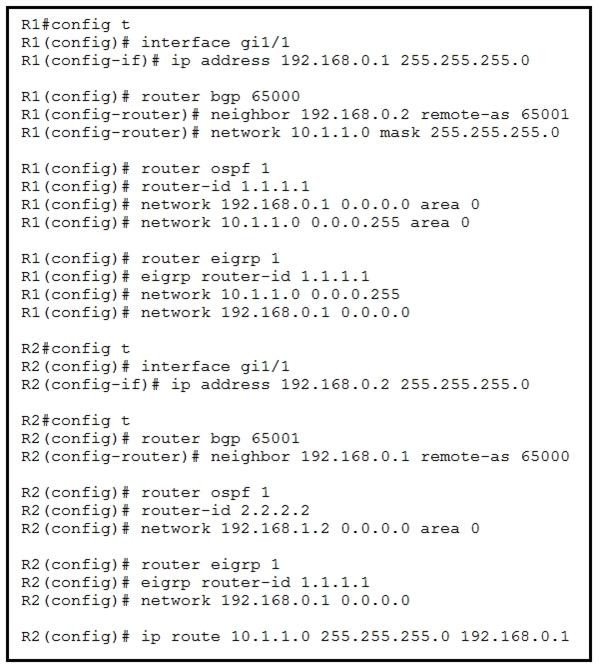
|
A. |
eBGP |
|
B. |
static |
|
C. |
OSPF |
|
D. |
EIGRP |
Answer:
B Explanation: Admin Distance: Connected - 0
Static - 1
eBGP - 5
iEIGRP - 90
OSPF - 110
IS-IS - 115
RIP - 120
So the answer is correct based from AD of a statically configured route.
An engineer needs to configure LLDP to send the port description time length value (TLV). What command sequence must be implemented?
|
A. |
switch(config-line)#IIdp port-description |
|
B. |
switch(config)#IIdp port-description |
|
C. |
switch(config-if)#IIdp port-description |
|
D. |
switch#IIdp port-description |
Answer:
B
Refer to the exhibit. Which switch in this configuration will be elected as the root bridge?
![]()
|
A. |
SW1 |
|
B. |
SW2 |
|
C. |
SW3 |
|
D. |
SW4 |
Answer: C
Explanation:
The lowest MAC address will determine which bridge becomes the root bridge. In this case SW3 in decimal is 12.15.21.26.60.157 which is the lowest MAC address.
Which device permits or denies network traffic based on a set of rules?
|
A. |
firewall |
|
B. |
switch |
|
C. |
access point |
|
D. |
wireless controller |
Answer:
A
An office has 8 floors with approximately 30-40 users per floor.
What command must be configured on the router Switched Virtual Interface to use address space efficiently?
|
A. |
ip address 192.168.0.0 255.255.0.0 |
|
B. |
ip address 192.168.0.0 255.255.254.0 |
|
C. |
ip address 192.168.0.0 255.255.255.128 |
|
D. |
ip address 192.168.0.0 255.255.255.224 |
Answer:
B
Explanation:
8 bits = (2^8 – 2) =254 IP addresses, and it’s not
enough.
9 bits = (2^9 – 2) = 510 IP addresses, and this is enough.
You have a class C subnet (192.168.0.0). This means a subnet mask like this: 255.255.255.0
But you need 9 bits for the hosts, so you’ve got left with a subnet mask like this: 255.255.1111111x.xxxxxxxx =255.255.254.0
This means you will use VLSM subnetting.
A wireless administrator has configured a WLAN; however, the clients need access to a less congested 5-GHz network for their voice quality. What action must be taken to meet the requirement?
|
A. |
enable AAA override |
|
B. |
enable RX-SOP |
|
C. |
enable DTIM |
|
D. |
enable Band Select |
Answer: D
Refer to the exhibit. A packet is being sent across router R1 to host 172.16.0.14. What is the destination route for the packet?
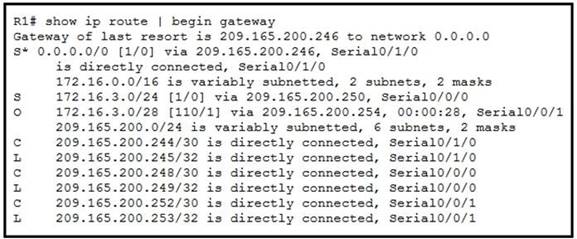
|
A. |
209.165.200.254 via
Serial0/0/1 |
|
B. |
209.165.200.254
via Serial0/0/0 |
|
C. |
209.165.200.246 via Serial0/1/0 |
|
D. |
209.165.200.250 via Serial0/0/0 |
Answer: C
Explanation:
The router will use the default route since there is no entry for the destination address/subnet entry in the routine table.
Which configuration ensures that the switch is always the root for VLAN 750?
|
A. |
Switch(config)#spanning-tree vlan
750 priority 38003685 |
|
B. |
Switch(config)#spanning-tree vlan 750 root primary |
|
C. |
Switch(config)#spanning-tree vlan
750 priority 614440 |
|
D. |
Switch(config)#spanning-tree vlan 750 priority 0 |
Answer: D
Explanation:
Although the spanning-tree vlan 10 root primary command will ensure a switch will have a bridge priority value lower than other bridges introduced to the network, the spanning-tree vlan 10 priority 0 command ensures the bridge priority takes precedence over all other priorities.
Refer to the exhibit. An engineer booted a new switch and applied this configuration via the console port. Which additional configuration must be applied to allow administrators to authenticate directly to enable privilege mode via Telnet using a local username and password?
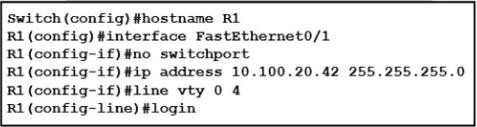
![]()
|
A. |
Option A |
|
B. |
Option B |
|
C. |
Option C |
|
D. |
Option D |
Answer:
A
Refer to the exhibit. Which switch becomes the root bridge?
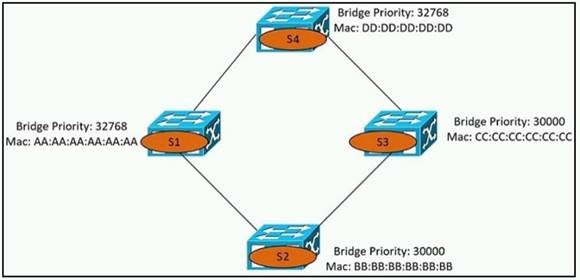
|
A. |
S1 |
|
B. |
S2 |
|
C. |
S3 |
|
D. |
S4 |
Answer:
B
Explanation:
Lower priority means it is preferred compared to a higher. If there is a tie in priority then the lowest MAC address will determine which bridge becomes the root. Because S2 has the lowest MAC address, S2 becomes the root bridge.
Refer to the exhibit. Which route type does the routing protocol Code D represent in the output?
![]()
|
A. |
internal BGP route |
|
B. |
/24 route of a locally configured IP |
|
C. |
statically assigned route |
|
D. |
route learned through EIGRP |
Answer: D
Explanation:
D = EIGRP, O = OSPF, L = Local, S = Static, C = Directly Connected
What protocol allows an engineer to back up 20 network router configurations globally while using the copy function?
|
A. |
SMTP |
|
B. |
SNMP |
|
C. |
TCP |
|
D. |
FTP |
Answer: B
Explanation:
SNMP works in conjunction with TFTP to backup configuration files. This is accomplished by downloading a current copy of your router’s configuration file to a TFTP server via SNMP.
An engineer must configure an OSPF neighbor relationship between router R1 and R3. The authentication configuration has been configured and the connecting interfaces are in the same 192.168.1.0/30 subnet. What are the next two steps to complete the configuration? (Choose two.)
|
A. |
configure the hello
and dead timers
to match on both sides |
|
B. |
configure the
same process ID for the router OSPF
process |
|
C. |
configure the same router
ID on both routing processes |
|
D. |
Configure the interfaces as OSPF active
on both sides. |
|
E. |
configure both interfaces with the same
area ID |
Answer: AE
Explanation:
Timers match by default.
The process ID can be the same or not. The router ID mustn't be the same.
What software defined architecture plane assists network devices with making packet-forwarding decisions by providing Layer 2 reachability and Layer 3 routing information?
|
A. |
data plane |
|
B. |
control plane |
|
C. |
policy plane |
|
D. |
management plane |
Answer:
B
Explanation:
The control plane is the part of a network that controls how data is forwarded, while the data plane controls the actual forwarding process.
Making packet forwarding decisions is ‘how data is forwarded’.
Which WAN access technology is preferred for a small office / home office architecture?
|
A. |
broadband cable access |
|
B. |
frame-relay packet
switching |
|
C. |
dedicated
point-to-point leased line |
|
D. |
Integrated Services Digital Network switching. |
Answer: A
Explanation:
Public WAN infrastructure: Service providers provide Internet access using broadband services such as DSL, cable, and satellite access. Broadband connections are typically used to connect small offices and telecommuting employees to a corporate site over the Internet. Data traveling between corporate sites over the public WAN infrastructure should be protected using VPNs.
A network administrator enabled port security on a switch interface connected to a printer. What is the next configuration action in order to allow the port to learn the MAC address of the printer and insert it into the table automatically?
|
A. |
enable dynamic MAC address learning |
|
B. |
implement static
MAC addressing. |
|
C. |
enable sticky
MAC addressing |
|
D. |
implement auto MAC address learning |
Answer: C
Explanation:
You can configure an interface to convert the dynamic MAC addresses to sticky secure MAC addresses and to add them to the running configuration by enabling sticky learning. To enable sticky learning, enter the switchport port-security mac-address sticky command.
Which two WAN architecture options help a business scalability and reliability for the network? (Choose two)
|
A. |
asychronous routing |
|
B. |
single-homed branches |
|
C. |
dual-homed branches |
|
D. |
static routing |
|
E. |
dynamic routing |
Answer: CE
What criteria is used first during the root port selection process?
|
A. |
local port ID |
|
B. |
lowest path
cost to the root bridge |
|
C. |
lowest neighbor's bridge ID |
|
D. |
lowest neighbor's port
ID |
Answer: B
Explanation:
Root Port selection is based on the port having lowest cost to the Root Bridge (CAT1). For PVST (Per VLAN Spanning Tree) path cost will depend on bandwidth of links and cost value is as shown below for most commonly used links.
https://mrncciew.com/2013/07/07/stp-root-port-selection/
Which state does the switch port move to when PortFast is enabled?
|
A. |
learning |
|
B. |
forwarding |
|
C. |
blocking |
|
D. |
listening |
Answer: B
Refer to the exhibit. A packet is being sent across router R1 to host 172.16.3.14. To which destination does the router send the packet?
![]()
|
A. |
207.165.200.246 via
Serial0/1/0 |
|
B. |
207.165.200.254
via Serial0/0/1 |
|
C. |
207.165.200.254 via
Serial0/0/0 |
|
D. |
207.165.200.250 via
Serial/0/0/0 |
Answer:
B
Explanation:
The longest matching route to 172.16.3.14 is the 182.16.3.0/28 route, using Serial 0/0/1 with a next hop of 207.165.200.254.
What is a benefit for external users who consume public cloud resources?
|
A. |
implemented over a dedicated WAN |
|
B. |
located in the same data center
as the users |
|
C. |
all hosted on physical servers |
|
D. |
accessed over the Internet |
Answer: D
Drag and Drop Question
Refer to the exhibit. An engineer is tasked with verifying network configuration parameters on a client workstation to report back to the team lead. Drag and drop the node identifiers from the left onto the network parameters on the right.
![]()
Answer:
![]()
Drag and Drop Question
Drag the descriptions of device management from the left onto the types of device management on the right.
![]()
Answer:
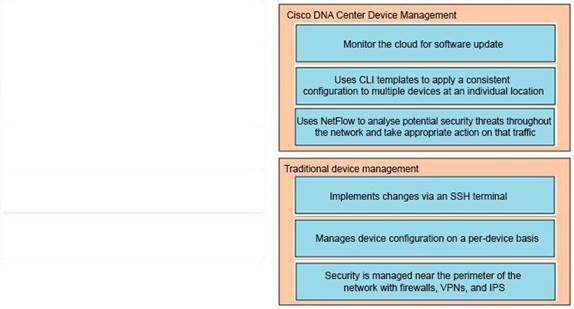
Drag and Drop Question
Drag the descriptions of IP protocol transmissions from the left onto the IP traffic types on the right.
![]()
Answer:
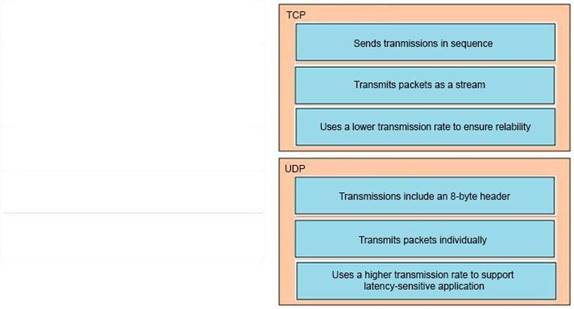
An engineer must establish a trunk link between two switches. The neighboring switch is set to trunk or desirable mode. What action should be taken?
|
A. |
configure switchport nonegotiate |
|
B. |
configure
switchport mode dynamic
desirable |
|
C. |
configure switchport mode dynamic auto |
|
D. |
configure switchport trunk
dynamic desirable |
Answer: C
A manager asks a network engineer to advise which cloud service models are used so employees do not have to waste their time installing, managing, and updating software which is only used occasionally Which cloud service model does the engineer recommend?
|
A. |
infrastructure-as-a-service |
|
B. |
platform-as-a-service |
|
C. |
business process as service to support different types of service |
|
D. |
software-as-a-service |
Answer: D
A port security violation has occurred on a switch port due to the maximum MAC address count being exceeded Which command must be configured to increment the security-violation count and forward an SNMP trap?
|
A. |
switchport port-security violation access |
|
B. |
switchport port-security violation protect |
|
C. |
switchport port-security violation restrict |
|
D. |
switchport port-security violation shutdown |
Answer: C
Refer to the exhibit. Which type of configuration is represented in the output?
![]()
|
A. |
Ansible |
|
B. |
JSON |
|
C. |
Chef |
|
D. |
Puppet |
Answer: D
What are two functions of a Layer 2 switch? (Choose two)
|
A. |
acts as a central point
for association and authentication servers |
|
B. |
selects the
best route between networks on a WAN |
|
C. |
moves packets
within a VLAN |
|
D. |
moves packets between different VLANs |
|
E. |
makes forwarding decisions based on the MAC address of a packet |
Answer: CE
Which spanning-tree enhancement avoids the learning and listening states and immediately places ports in the forwarding state?
|
A. |
BPDUfilter |
|
B. |
PortFast |
|
C. |
Backbonefast |
|
D. |
BPDUguard |
Answer:
B
Explanation:
PortFast
Spanning Tree Portfast causes layer 2 switch interfaces to enter forwarding state immediately, bypassing the listening and learning states. It should be used on ports connected directly to end hosts like servers or workstations. Note: If portfast isn't enabled, DHCP timeouts can occur while STP converges, causing more problems.
What is a recommended approach to avoid co-channel congestion while installing access points that use the 2.4 GHz frequency?
|
A. |
different nonoverlapping channels |
|
B. |
different overlapping channels |
|
C. |
one overlapping channel |
|
D. |
one nonoverlapping channel |
Answer: D
Explanation:
Each AP operates in one channel. The goal is that neighboring APs don't use the same channel, so you need multiple non-overlapping channel, or you have co-channel interference, which slows down your wireless operation. (Adjacent channel interference causes collisions)
Which function is performed by the collapsed core layer in a two-tier architecture?
|
A. |
enforcing routing policies |
|
B. |
marking interesting traffic for data polices |
|
C. |
attaching users
to the edge of the
network |
|
D. |
applying security policies |
Answer:
A
What are two functions of a server on a network? (Choose two)
|
A. |
achieves redundancy by exclusively using
virtual server clustering |
|
B. |
runs applications that send and retrieve data
for workstations that make requests |
|
C. |
handles requests from multiple workstations at the same
time |
|
D. |
runs the same operating system in order
to communicate with other servers |
|
E. |
housed solely in a data center that
is dedicated to a single
client |
Answer: BC
Refer to the exhibit. An engineer configured the New York router with static routes that point to the Atlanta and Washington sites. Which command must be configured on the Atlanta and Washington routers so that both sites are able to reach the loopback2 interface on the New York router?
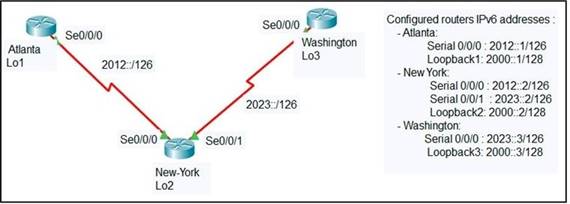
|
A. |
ipv6 route ::/0 Serial 0/0/1 |
|
B. |
ipv6 route
0/0 Serial 0/0/0 |
|
C. |
ipv6 route
::/0 Serial 0/0/0 |
|
D. |
ip route 0.0.0.0.0.0.0.0 Serial
0/0/0 |
|
E. |
ipv6 route ::/0
2000::2 |
Answer: C
Explanation:
Network + Interface (Source interface) or Next Hop (IP Address Neighbor). So, you have 4 possibilities:
Atlanta = ipv6 route::/0 2012::2/126 or
Atlanta = ipv6 route::/0 Serial 0/0/0
![]()
Washington= ipv6 route::/0 2023::2/126 or
Washington= ipv6 route::/0 Serial 0/0/0
Drag and Drop Question
Drag and drop the AAA terms from the left onto the descriptions on the right.
![]()
Answer:
![]()
An engineer is configuring switch SW1 to act an NTP server when all upstream NTP server connectivity fails. Which configuration must be used?
|
A. |
SW1# config t SW1(config)#ntp peer 192.168.1.1 SW1(config)#ntp access-group peer accesslist1 |
|
B. |
SW1#
config t SW1(config)#ntp master SW1(config)#ntp server192.168.1.1 |
|
C. |
SW1#
config t SW1(config)#ntp backup SW1(config)#ntp server192.168.1.1 |
|
D. |
SW1# config
t SW1(config)#ntp
server192.168.1.1 SW1(config)#ntp access-group peer accesslist1 |
Answer:
B
Explanation:
The "NTP Master" command sets this device (SW1) as an NTP server, the second command "NTP server 192.168.1.1" synchronises this device to 192.168.1.1's time. if the upstream connectivity to 192.168.1.1 is lost, this device will continue to act as a NTP server for the rest of the hosts in the network.
In software-defined architectures, which plane is distributed and responsible for traffic forwarding?
|
A. |
management plane |
|
B. |
control plane |
|
C. |
policy plane |
|
D. |
data plane |
Answer: D
When using Rapid PVST+, which command guarantees the switch is always the root bridge for VLAN 200?
|
A. |
spanning -tree vlan
200 priority 614440 |
|
B. |
spanning -tree
vlan 200 priority 38572422 |
|
C. |
spanning -tree
vlan 200 priority 0 |
|
D. |
spanning -tree vlan
200 root primary |
Answer: C
An engineer requires a scratch interface to actively attempt to establish a trunk link with a neighbor switch. What command must be configured?
|
A. |
switchport mode trunk |
|
B. |
switchport mode
dynamic desirable |
|
C. |
switchport mode
dynamic auto |
|
D. |
switchport nonegotiate |
Answer:
B
Explanation:
The command switchport mode dynamic desirable, which asks the switch to both negotiate as well as to begin the negotiation process, rather than waiting on another device.
Which protocol prompts the Wireless LAN Controller to generate its own local web administration SSL certificate for GUI access?
|
A. |
HTTPS |
|
B. |
RADIUS |
|
C. |
TACACS+ |
|
D. |
HTTP |
Answer:
A
Explanation:
You can protect communication with the GUI by enabling HTTPS. HTTPS protects HTTP browser sessions by using the Secure Sockets Layer (SSL) protocol.
When you enable HTTPS, the controller generates its own local web administration SSL certificate and automatically applies it to the GUI. You also have the option of downloading an externally generated certificate.
What are two recommendations for protecting network ports from being exploited when located in an office space outside of an IT closet? (Choose two)
|
A. |
configure static ARP
entries |
|
B. |
enable the PortFast feature on ports |
|
C. |
implement port-based authentication |
|
D. |
configure ports
to a fixed speed |
|
E. |
shut down unused
ports |
Answer: CE
Refer to the exhibit. After the election process what is the root bridge in the HQ LAN?
Switch 1: 0C:E0:38:81:32:58
Switch 2: 0C:0E:15:22:1A:61
Switch 3: 0C:0E:15:1D:3C:9A
Switch 4: 0C:E0:19:A1:4D:16
![]()
|
A. |
Switch 1 |
|
B. |
Switch 2 |
|
C. |
Switch 3 |
|
D. |
Switch 4 |
Answer: C
Explanation:
The root bridge is determined by the lowest bridge ID, which consists of the priority value and the MAC address. Because the priority values of all of the switches are not avalable, the MAC address is used to determine the root bridge. Because S3 has the lowest MAC address, S3 becomes the root bridge.
What is the primary function of a Layer 3 device?
|
A. |
to analyze traffic and drop unauthorized traffic from the
Internet |
|
B. |
to transmit wireless traffic between hosts |
|
C. |
to pass traffic between different networks |
|
D. |
forward traffic within
the same broadcast domain |
Answer: C
Explanation:
https://community.cisco.com/t5/networking-documents/communication-at-network-layer-layer- 3/ta-p/3128129
Router internally has two tables one for layer 2 information (MAC Address / ARP Table) and layer 3 information (Routing Table). Routing table is used for inter-network communication.
What is the same for both copper and fiber interfaces when using SFP modules?
|
A. |
They support an inline optical
attenuator to enhance
signal strength |
|
B. |
They provide minimal interruption to services by being hot-swappable |
|
C. |
They offer reliable bandwidth up to 100 Mbps in half
duplex mode |
|
D. |
They accommodate single-mode and multi-mode in a single
module |
Answer: B
Explanation:
https://www.cisco.com/c/en/us/products/collateral/interfaces-modules/gigabit-ethernet-gbic-sfp- modules/datasheet-c78-366584.html
1000BASE-T SFP for copper networks
The 1000BASE-T SFP operates on standard Category 5 unshielded twisted-pair copper cabling of link lengths up to 100 m (328 ft). Cisco 1000BASE-T SFP modules support 10/100/1000 auto negotiation and Auto MDI/MDIX.
Features and benefits
●
Hot swappable to maximize uptime
and simplify serviceability
●
Flexibility of media and interface
choice on a port-by-port basis,
so you can “pay as you
populate”
●
Robust design for enhanced reliability
●
Supports Digital Optical
Monitoring (DOM) capability
What is a function of TFTP in network operations?
|
A. |
transfers a backup
configuration file from
a server to a switch
using a username and password |
|
B. |
transfers files
between file systems
on a router |
|
C. |
transfers a configuration files
from a server
to a router on a congested link |
|
D. |
transfers IOS images
from a server
to a router for firmware upgrades |
Answer: D
Explanation:
https://geek-university.com/ccna/trivial-file-transfer-protocol-tftp/
Which CRUD operation modifies an existing table or view?
|
A. |
read |
|
B. |
create |
|
C. |
replace |
|
D. |
update |
Answer: D
An engineer must configure interswitch VLAN communication between a Cisco switch and a third- party switch. Which action should be taken?
|
A. |
configure IEEE 802.1p |
|
B. |
configure IEEE
802.1q |
|
C. |
configure ISL |
|
D. |
configure DSCP |
Answer:
B
Explanation:
VLAN trunking offers two options, ISL and 802.1Q. ISL is Cisco proprietary while 802.1Q is standards based and supported by multiple vendors.
What is a function of a remote access VPN?
|
A. |
used cryptographic tunneling to protect the privacy of data for multiple users
simultaneously |
|
B. |
used exclusively when a user
is connected to a company's internal network |
|
C. |
establishes a secure tunnel
between two branch
sites |
|
D. |
allows the users
to access company
internal network resources through a secure
tunnel |
Answer: D
What is a DHCP client?
|
A. |
a workstation that
requests a domain
name associated with
its IP address |
|
B. |
a host that is configured to request an IP address automatically |
|
C. |
a server that dynamically assigns IP addresses to hosts. |
|
D. |
a router that
statically assigns IP addresses to
hosts. |
Answer:
B
Explanation:
The "CLIENT" (Meaning a computer or device on the network) requests IP address information from the DHCP "SERVER".
Which two functions are performed by the core layer in a three-tier architecture? (Choose two)
|
A. |
Provide uninterrupted forwarding service. |
|
B. |
Police traffic
that is sent
to the edge of the
network. |
|
C. |
Provide direct
connectivity for end
user devices. |
|
D. |
Ensure timely
data transfer between layers. |
|
E. |
Inspect packets for malicious activity. |
Answer: AD
Explanation:
Cisco is very clear about the purpose of this layer. Its only role is to forward traffic, the fastest it can. Here you don’t apply any policy, as you must try to reduce the load of the core so it can focus on routing. https://www.cisco.com/c/en/us/td/docs/solutions/Enterprise/Campus/campover.html#wp708831
Refer to the exhibit. A network administrator must permit SSH access to remotely manage routers in a network. The operations team resides on the 10.20.1.0/25 network. Which command will accomplish this task?
![]()
|
A. |
access-list 2699 permit
udp 10.20.1.0 0.0.0.255 |
|
B. |
no access-list 2699 deny
tcp any 10.20.1.0 0.0.0.127 eq 22 |
|
C. |
access-list 2699 permit tcp any 10.20.1.0 0.0.0.255 eq 22 |
|
D. |
no access-list 2699 deny ip any 10.20.1.0 0.0.0.255 |
Answer: D
Explanation:
Already a statement is there in last to allow SSH Traffic for network 10.20.1.0 0.0.0.127, but Second statement says deny ip any 10.20.1.0 0.0.0.255, so how it will work once it is denied. So the right answer is remove the --- no access-list 2699 deny ip any 10.20.1.0 0.0.0.255.
Which configuration management mechanism uses TCP port 22 by default when communicating with managed nodes?
|
A. |
Ansible |
|
B. |
Python |
|
C. |
Puppet |
|
D. |
Chef |
Answer:
A
What is a practice that protects a network from VLAN hopping attacks?
|
A. |
Enable dynamic ARP inspection |
|
B. |
Configure an ACL to prevent traffic
from changing VLANs |
|
C. |
Assign all access ports
to VLANs other
than the native
VLAN |
|
D. |
Implement port security on internet-facing VLANs |
Answer: C
Refer to the exhibit. If OSPF Is running on this network, how does Router2 handle traffic from Site B to 10.10.13.128/25 at Site A?
![]()
|
A. |
It load-balances traffic
out of Fa0/1
and Fa0/2. |
|
B. |
It is unreachable and discards the traffic. |
|
C. |
It sends packets out
of interface FaO/2. |
|
D. |
It sends packets
out of interface Fa0/1. |
Answer:
B
What is the purpose of traffic shaping?
|
A. |
to mitigate delays
over slow links |
|
B. |
to provide fair queuing
for buffered flows |
|
C. |
to limit the bandwidth that a flow
can use to |
|
D. |
be a marking mechanism that identifies different flows |
Answer: B
Explanation:
Traffic shaping retains excess packets in a queue and then schedules the excess for later transmission over increments of time.
https://www.cisco.com/c/en/us/support/docs/quality-of-service-qos/qos-policing/19645- policevsshape.html#policingvsshaping
Refer to the exhibit. Which command configures a floating static route to provide a backup to the primary link?
![]()
|
A. |
ip route 0.0.0.0
0.0.0.0 209.165.202.131 |
|
B. |
ip route 209.165.201.0 255.255.255.224 209.165.202.130 |
|
C. |
ip route 0.0.0.0 0.0.0.0 209.165.200.224 |
|
D. |
ip route 209.165.200.224 255.255.255.224 209.165.202.129 254 |
Answer: D
Explanation:
D is the only answer that is a static floating route.
Where does the configuration reside when a helper address is configured to support DHCP?
|
A. |
on the router
closest to the
server |
|
B. |
on the router closest to the client |
|
C. |
on every router
along the path |
|
D. |
on the switch
trunk interface |
Answer: B
Explanation:
https://techhub.hpe.com/eginfolib/networking/docs/switches/K-KA-KB/15-18/5998- 8164_mrg/content/ch12s04.html
https://community.cisco.com/t5/routing/configure-dhcp-relay-ip-helper-address-need-help/td- p/4127915
the IP helper goes on the first layer 3 device in the path towards the DHCP server. In your case, that appears to be the 3850. Put the helper address on the Vlan interfaces, e.g.:
interface Vlan60
ip address 10.233.190.254 255.255.255.0
--> ip helper-address x.x.x.x
no ip redirects
no ip unreachables
How does the dynamically-learned MAC address feature function?
|
A. |
The CAM table
is empty until
ingress traffic arrives
at each port |
|
B. |
Switches dynamically learn MAC addresses of each connecting CAM table. |
|
C. |
The ports are restricted and learn up to a maximum of 10 dynamically-learned addresses |
|
D. |
It requires a minimum number
of secure MAC addresses to be filled
dynamically |
Answer:
A
What facilitates a Telnet connection between devices by entering the device name?
|
A. |
SNMP |
|
B. |
DNS lookup |
|
C. |
syslog |
|
D. |
NTP |
Answer:
B
Drag and Drop Question
Drag the IPv6 DNS record types from the left onto the description on the right.
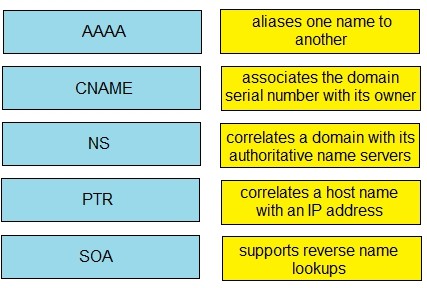
Answer:
![]()
Drag and Drop Question
Drag and drop the SNMP components from the left onto the descriptions on the right.
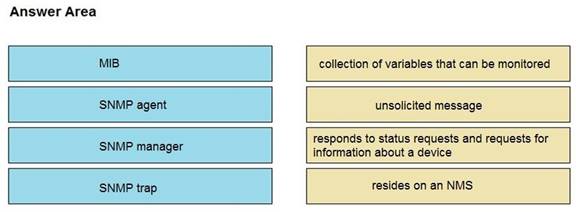
Answer:
![]()
Explanation:
MIB: collection of variables that can be monitored
SNMP agent: responds to status requests and requests for information about a device SNMP manager: The SNMP manager is part of an NMS
SNMP trap: unsolicited messages that are sent by the SNMP agent and alert the NMS to a condition on the network
Drag and Drop Question
Refer to the exhibit. An engineer is required to verify that the network parameters are valid for the users wireless LAN connectivity on a /24 subnet. Drag and drop the values from the left onto the network parameters on the right. Not all values are used.
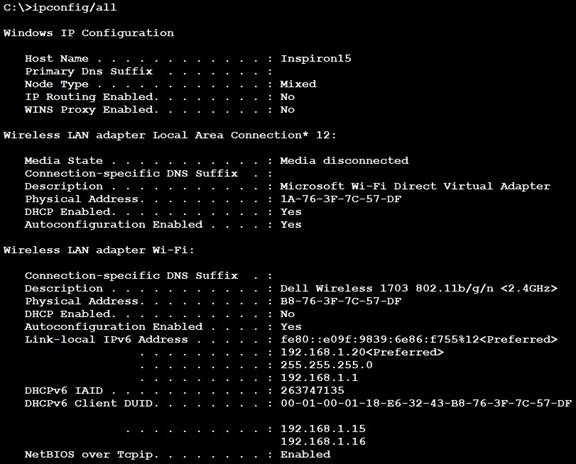
![]()
Answer:
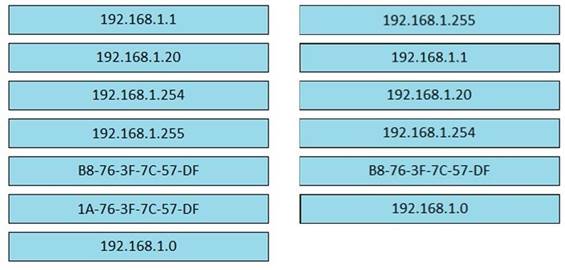
Refer to the exhibit. An access list is required to permit traffic from any host on interface G0/0 and deny traffic from interface G/0/1. Which access list must be applied?
![]()
|
A. |
ip
access-list standard 99 permit 10.100.100.0 0.0.0.255 deny 192.168.0.0 0.0.255.255 |
|
B. |
ip
access-list standard 99 permit 10.100.100.0 0.0.0.255 deny 192.168.0.0 0.255.255.255 |
|
C. |
ip
access-list standard 199 permit 10.100.100.0 0.0.0.255 deny 192.168.0.0 0.255.255.255 |
|
D. |
ip
access-list standard 199 permit 10.100.100.0 0.0.0.255 deny 192.168.0.0 0.0.255.255 |
Answer:
A
What does a switch use to build its MAC address table?
|
A. |
VTP |
|
B. |
DTP |
|
C. |
egress traffic |
|
D. |
ingress traffic |
Answer: D
Which device tracks the state of active connections in order to make a decision to forward a packet through?
|
A. |
wireless access point |
|
B. |
firewall |
|
C. |
wireless LAN
controller |
|
D. |
router |
Answer:
B
How do servers connect to the network in a virtual environment?
|
A. |
wireless to an access point
that is physically connected to the
network |
|
B. |
a cable connected to a physical switch on the
network |
|
C. |
a virtual switch that
links to an access point
that is physically connected to the
network |
|
D. |
a software switch
on a hypervisor that is physically connected to the network |
Answer: D
What is recommended for the wireless infrastructure design of an organization?
|
A. |
group access points
together to increase throughput on a given channel |
|
B. |
configure the
first three access
points are configured to use Channels 1, 6, and 11 |
|
C. |
include a least two access points
on nonoverlapping channels to support load
balancing |
|
D. |
assign physically adjacent access points to the same
Wi-Fi channel |
Answer:
B
Which 802.11 frame type is indicated by a probe response after a client sends a probe request?
|
A. |
action |
|
B. |
management |
|
C. |
control |
|
D. |
data |
Answer:
B
Explanation:
Management frames: Used for joining and leaving a wireless cell. Management frame types include association request, association response, and reassociation request, just to name a few. Control frames: Used to acknowledge when data frames are received.
Data frames: Frames that contain data.
Which network plane is centralized and manages routing decisions?
|
A. |
policy plane |
|
B. |
management plane |
|
C. |
control plane |
|
D. |
data plane |
Answer: C
Refer to the exhibit. Which route type is configured to reach the internet?
![]()
|
A. |
host route |
|
B. |
default route |
|
C. |
floating static
route |
|
D. |
network route |
Answer: B
Explanation:
It can reach the internet with the directly connected route but only if it's specified to go directly to 10.10.10.18. The internet itself is filled with unknown addresses, so any other unknown address will need to use the default route.
How does a switch process a frame received on Fa0/1 with the destination MAC address of 0e38.7363.657b when the table is missing the address?
|
A. |
lt drops the frame immediately. |
|
B. |
It forwards the frame
back out of interface Fa0/1. |
|
C. |
It floods the frame
to all interfaces except Fa0/1. |
|
D. |
It holds the frame until
the MAC address
timer expires and then drops
the frame. |
Answer: C
Which function does the range of private IPv4 addresses perform?
|
A. |
allows multiple companies to each use the same addresses without
conflicts |
|
B. |
provides a direct connection for hosts from outside of the enterprise network |
|
C. |
ensures that
NAT is not required to reach the internet with
private range addressing |
|
D. |
enables secure communications to the internet for all external hosts |
Answer:
A
Refer to the exhibit. An access list is created to deny Telnet access from host PC-1 to RTR-1 and allow access from all other hosts A Telnet attempt from PC-2 gives this message:"% Connection refused by remote host" Without allowing Telnet access from PC-1, which action must be taken to permit the traffic?
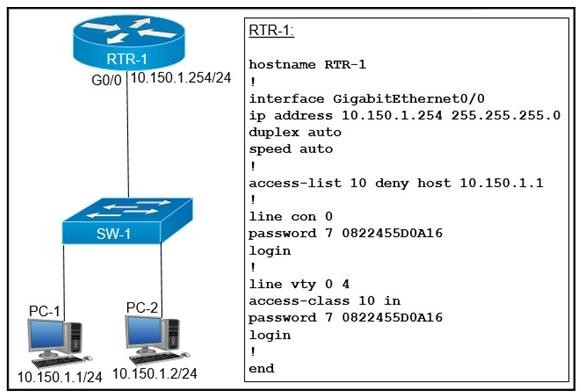
|
A. |
Add the access-list 10 permit any command to the configuration |
|
B. |
Remove the access-class 10 in command from line vty 0.4. |
|
C. |
Add the ip access-group 10 out command
to interface g0/0. |
|
D. |
Remove the password command from line vty 0 4. |
Answer: A
Explanation:
At the bottom of any ACL there is an Implicit DENY ALL (DENY ANY ANY) rule. So after specifying the first ACL rule we should include and explicit PERMIT ALL (PERMT ANY ANY) to explicitly permit other Traffic.
Which protocol does an IPv4 host use to obtain a dynamically assigned IP address?
|
A. |
ARP |
|
B. |
DHCP |
|
C. |
CDP |
|
D. |
DNS |
Answer:
B
What is a benefit of VRRP?
|
A. |
It provides traffic load balancing to destinations that
are more than
two hops from
the source. |
|
B. |
It provides the default gateway redundancy on a LAN using
two or more
routers. |
|
C. |
It allows neighbors to share routing table information between
each other. |
|
D. |
It prevents loops
in a Layer 2 LAN by forwarding all traffic to a root bridge, which
then makes the final forwarding decision. |
Answer:
B
Refer to the exhibit. What is the result if Gig1/11 receives an STP BPDU?
![]()
|
A. |
The port transitions to STP blocking |
|
B. |
The port transitions to the root
port |
|
C. |
The port immediately transitions to STP forwarding. |
|
D. |
The port goes into error-disable state |
Answer: D
Explanation:
BPDU Guard feature protects the port from receiving STP BPDUs, however the port can transmit STP BPDUs. When a STP BPDU is received on a BPDU Guard enabled port, the port is shutdown and the state of the port changes to ErrDis (Error-Disable) state.
Which type of security program is violated when a group of employees enters a building using the ID badge of only one person?
|
A. |
intrusion detection |
|
B. |
user awareness |
|
C. |
physical access
control |
|
D. |
network authorization |
Answer: C
Refer to the exhibit. PC1 is trying to ping PC3 for the first time and sends out an ARP to S1 Which action is taken by S1?
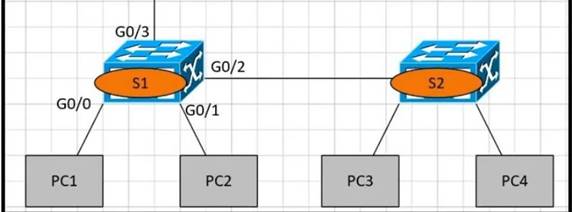
|
A. |
It forwards it out G0/3
only |
|
B. |
It is flooded out every port except G0/0. |
|
C. |
It drops the frame. |
|
D. |
It forwards it out interface G0/2 only. |
Answer:
B
Which technology can prevent client devices from arbitrarily connecting to the network without state remediation?
|
A. |
802.1x |
|
B. |
IP Source Guard |
|
C. |
MAC Authentication Bypass |
|
D. |
802.11n |
Answer: A
Explanation:
802.1X is a network authentication protocol that opens ports for network access when an organization authenticates a user's identity and authorizes them for access to the network. The user's identity is determined based on their credentials or certificate, which is confirmed by the RADIUS server.
In which situation is private IPv4 addressing appropriate for a new subnet on the network of an organization?
|
A. |
There is limited unique address space,
and traffic on the new subnet will
stay local within
the organization. |
|
B. |
The network has multiple endpoint listeners, and it is desired to limit the number of broadcasts. |
|
C. |
Traffic on the subnet
must traverse a site-to-site VPN to an outside organization. |
|
D. |
The ISP requires the new subnet
to be advertised to the internet for
web services. |
Answer: A
Refer to the exhibit. A network administrator has been tasked with securing VTY access to a router Which access-list entry accomplishes this task?
![]()
|
A. |
access-list 101 permit
tcp 10.1.10 0.0.0.255 172.16.10 0.0.0.255 eq ssh |
|
B. |
access-list 101 permit tcp 10.11.0 0.0.0.255 172.16.10 0.0.0.255 eq scp |
|
C. |
access-list 101 permit tcp 10.11.0 0.0.0.255 172.16.10 0.0.0.255 eq telnet |
|
D. |
access-list 101 permit
tcp 10.1.10 0.0.0.255 172.16.10 0.0.0.255 eq https |
Answer:
A
Aside from discarding, which two states does the switch port transition through while using RSTP (802.1w)? (Choose two)
|
A. |
listening |
|
B. |
blocking |
|
C. |
forwarding |
|
D. |
learning |
|
E. |
speaking |
Answer: CD
Explanation:
STP goes from blocked, listening, learning, and forwarding and RSTP goes from Discarding, Learning, and Forwarding.
When implementing a router as a DHCP server, which two features must be configured? (Choose two)
|
A. |
relay agent information |
|
B. |
database agent |
|
C. |
address pool |
|
D. |
smart-relay |
|
E. |
manual bindings |
Answer: BC
An engineer must configure traffic for a VLAN that is untagged by the switch as it crosses a trunk link. Which command should be used?
|
A. |
switchport trunk allowed vlan 10 |
|
B. |
switchport trunk
native vlan 10 |
|
C. |
switchport mode
trunk |
|
D. |
switchport trunk encapsulation dot1q |
Answer:
B
Explanation:
The switchport trunk native vlan command specifies the native (untagged) VLAN for a Layer 2 interface operating in trunk mode on a Cisco IOS device. This command only takes effect for interfaces that are operating in trunk mode.
What is a role of wireless controllers in an enterprise network?
|
A. |
centralize the management of access points
in an enterprise network |
|
B. |
support standalone or controller-based architectures |
|
C. |
serve as the first
line of defense
in an enterprise network |
|
D. |
provide secure user logins to devices on the network. |
Answer:
A
What is the maximum bandwidth of a T1 point-to-point connection?
|
A. |
1.544 Mbps |
|
B. |
2.048 Mbps |
|
C. |
34.368 Mbps |
|
D. |
43.7 Mbps |
Answer:
A
Explanation:
A Point to Point T1 service is a private data connection securely connecting two or more locations with T1 data speeds (1.54Mbps).
Refer to the exhibit. Which switch becomes the root of the spanning tree for VLAN 110?
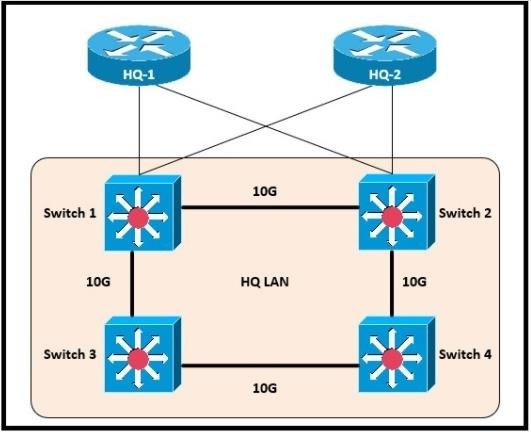
![]()
|
A. |
Switch 1 |
|
B. |
Switch 2 |
|
C. |
Switch 3 |
|
D. |
Switch 4 |
Answer: B
Explanation:
The root bridge is the bridge with the lowest Bridge ID. All the decisions like which ports are the root ports (the port with the best path to the root bridge) are made from the perspective of the root bridge. In case of a tie (not the case in this example) then the root bridge will be the switch with the lowest MAC address.
Where does a switch maintain DHCP snooping information?
|
A. |
in the MAC address table |
|
B. |
in the CAM table |
|
C. |
in the binding database |
|
D. |
in the frame
forwarding database |
Answer: C
Explanation:
A DHCP table is built that includes the source MAC address of a device on an untrusted port and the IP address assigned by the DHCP server to that device. The MAC address and IP address are bound together. Therefore, this table is called the DHCP snooping binding table.
Refer to the exhibit. What is represented by "R1" and "SW1" within the JSON output?
![]()
|
A. |
key |
|
B. |
array |
|
C. |
value |
|
D. |
object |
Answer: C
Refer to the exhibit. Which configuration must be applied to the router that configures PAT to translate all addresses in VLAN 200 while allowing devices on VLAN
100 to use their own IP addresses?
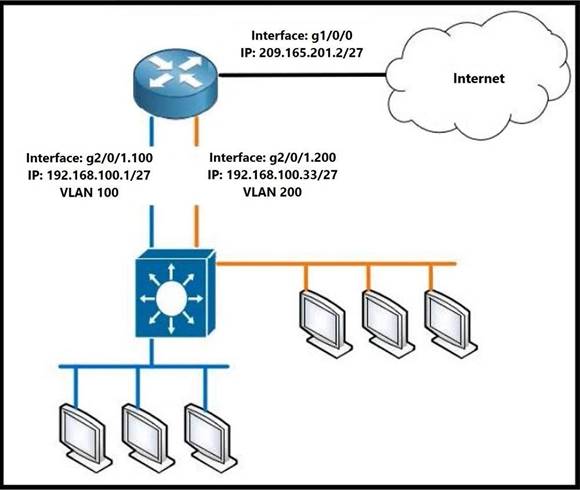
|
A. |
Router1(config)#access-list
99 permit 192.168.100.32 0.0.0.31 Router1(config)#ip nat inside source
list 99 interface gi1/0/0 overload
Router1(config)#interface gi2/0/1.200 Router1(config)#ip nat inside
Router1(config)#interface gi1/0/0
Router1(config)#ip nat outside |
|
B. |
Router1(config)#access-list
99 permit 192.168.100.0 0.0.0.255 Router1(config)#ip nat inside source
list 99 interface gi1/0/0 overload
Router1(config)#interface gi2/0/1.200 Router1(config)#ip nat inside Router1(config)#interface gi1/0/0 Router1(config)#ip nat outside |
|
C. |
Router1(config)#access-list 99 permit 209.165.201.2 255.255.255.255 Router1(config)#ip nat inside source list 99
interface gi1/0/0 overload Router1(config)#interface gi2/0/1.200 Router1(config)#ip nat inside Router1(config)#interface gi1/0/0 Router1(config)#ip nat outside |
|
D. |
Router1(config)#access-
list 99 permit 209.165.201.2 0.0.0.0 Router1(config)#ip nat inside source
list 99 interface gi1/0/0 overload
Router1(config)#interface gi2/0/1.200 Router1(config)#ip nat inside |
Router1(config)#interface gi1/0/0 Router1(config)#ip nat outside
Answer: D
Which CRUD operation corresponds to the HTTP GET method?
|
A. |
read |
|
B. |
update |
|
C. |
create |
|
D. |
delete |
Answer:
A
Explanation:
GET: This method retrieves the information identified by the request URI. In the context of the RESTful web services, this method is used to retrieve resources. This is the method used for read operations (the R in CRUD).
https://hub.packtpub.com/crud-operations-rest/
Refer to the exhibit. Which prefix did router R1 learn from internal EIGRP?
![]()
|
A. |
192.168.10/24 |
|
B. |
192.168.3.0/24 |
|
C. |
192.168.2.0/24 |
|
D. |
172.16 1.0/24 |
Answer: C
Refer to the exhibit. After the configuration is applied, the two routers fail to establish an OSPF neighbor relationship. what is the reason for the problem?
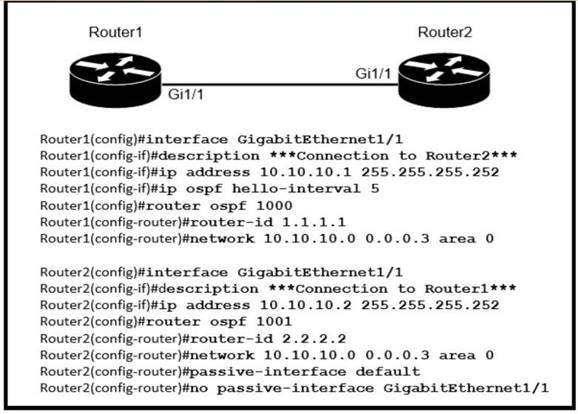
|
A. |
The OSPF router
IDs are mismatched. |
|
B. |
Router2 is using the default hello
timer. |
|
C. |
The network statement on Router1 is
misconfigured. |
|
D. |
The OSPF process
IDs are mismatched. |
Answer: B
Explanation:
Ospf processes can differ on each router and neighborship will form Ospf area must be the same to form adjacency Hello and dead timers must match to form adjacency.
Ospf Default hello timer is 10 and dead timer is 40.
In This case R1 hello timer was modified to 5 seconds, Timers was not changed on R2 hence using the default timers.
What does a router do when configured with the default DNS lookup settings, and a URL is entered on the CLI?
|
A. |
initiates a ping request to the URL |
|
B. |
prompts the user to specify the
desired IP address |
|
C. |
continuously attempts to resolve the URL until
the command is cancelled |
|
D. |
sends a broadcast message in an attempt to resolve the URL |
Answer: D
Refer to the exhibit. An administrator must configure interfaces Gi1/1 and Gi1/3 on switch SW11 PC-1 and PC- 2 must be placed in the Data VLAN and Phone-1 must be placed in the Voice VLAN.
Which configuration meets these requirements?
![]()

|
A. |
Option A |
|
B. |
Option B |
|
C. |
Option C |
|
D. |
Option D |
Answer: C
Which condition must be met before an NMS handles an SNMP trap from an agent?
|
A. |
The NMS software must be loaded
with the MIB
associated with the trap. |
|
B. |
The NMS must be configured on the same router as the SNMP
agent |
|
C. |
The NMS must
receive a trap
and an inform
message from the
SNMP agent within
a configured interval |
|
D. |
The NMS must
receive the same
trap from two different SNMP
agents to verify
that it is reliable. |
Answer:
A
What is the effect when loopback interfaces and the configured router ID are absent during the OSPF Process configuration?
|
A. |
No router ID is set,
and the OSPF
protocol does not run. |
|
B. |
The highest up/up physical interface IP address
is selected as the router
ID. |
|
C. |
The lowest IP address
is incremented by 1 and selected as the router
ID. |
|
D. |
The router ID 0.0.0.0 is selected and placed in the OSPF
process. |
Answer:
B
Which device controls the forwarding of authentication requests for users when connecting to the network using a lightweight access point?
|
A. |
TACACS server |
|
B. |
wireless access
point |
|
C. |
RADIUS server |
|
D. |
wireless LAN controller |
Answer: D
A network administrator must enable DHCP services between two sites. What must be configured for the router to pass DHCPDISCOVER messages on to the server?
|
A. |
a DHCP Relay
Agent |
|
B. |
DHCP Binding |
|
C. |
a DHCP Pool |
|
D. |
DHCP Snooping |
Answer:
A
A network administrator needs to aggregate 4 ports into a single logical link which must negotiate layer 2 connectivity to ports on another switch.
What must be configured when using active mode on both sides of the connection?
|
A. |
802.1q trunks |
|
B. |
Cisco vPC |
|
C. |
LLDP |
|
D. |
LACP |
Answer: D
Refer to the exhibit. Which path is used by the router for internet traffic?
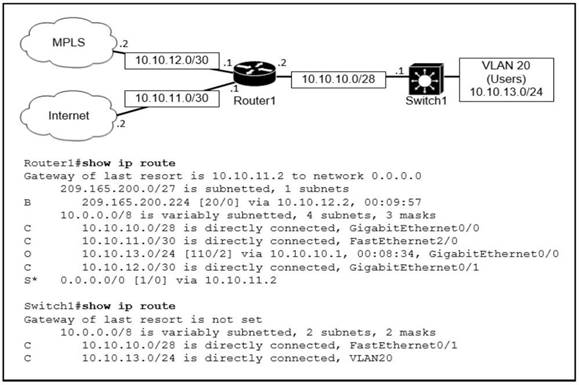
|
A. |
209.165.200.0/27 |
|
B. |
10.10.10.0/28 |
|
C. |
0.0.0.0/0 |
|
D. |
10.10.13.0/24 |
Answer: C
Explanation:
For internet traffic... the destination IP's can vary. Hence in this topology, it is using the default gateway 0.0.0.0. Path selection does not meet any other criteria so it has to use gateway of last resort.
How does a Cisco Unified Wireless network respond to Wi-Fi channel overlap?
|
A. |
It alternates automatically between 2.4 GHz and 5 GHz on adjacent access
points |
|
B. |
It allows the administrator to assign channels on a per-device or per-interface basis. |
|
C. |
It segregates devices from different manufacturers onto different channels. |
|
D. |
It analyzes client
load and background noise and dynamically assigns a channel. |
Answer: D
Explanation: https://www.cisco.com/c/en/us/td/docs/wireless/controller/technotes/8- 3/b_RRM_White_Paper/dca.html
What is the difference regarding reliability and communication type between TCP and UDP?
|
A. |
TCP is reliable and is a connection-oriented protocol; UDP is not reliable and
is a connectionless protocol |
|
B. |
TCP is not reliable and
is a connection-oriented protocol; UDP is reliable and is a connectionless
protocol |
|
C. |
TCP is not reliable and is a connectionless protocol; UDP is reliable and is a connection- oriented protocol |
|
D. |
TCP is reliable and is a connectionless protocol; UDP is not reliable and is a connection- oriented protocol |
Answer:
A
Drag and Drop Question
Refer to the exhibit. An engineer is configuring the router to provide static NAT for the webserver. Drag and drop the configuration commands from the left onto the letters that correspond to its position in the configuration on the fight.
Answer:
![]()
Drag and Drop Question
Drag and drop the QoS congestion management terms from the left onto the description on the right.
![]()
Answer:
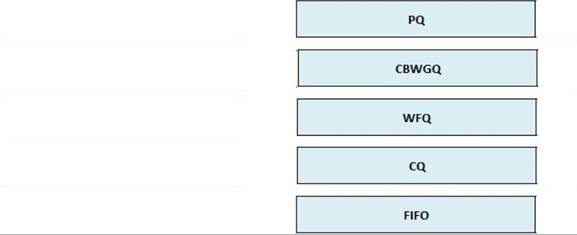
Drag and Drop Question
Drag and drop the network protocols from the left onto the correct transport services on the right.
![]()
Answer:
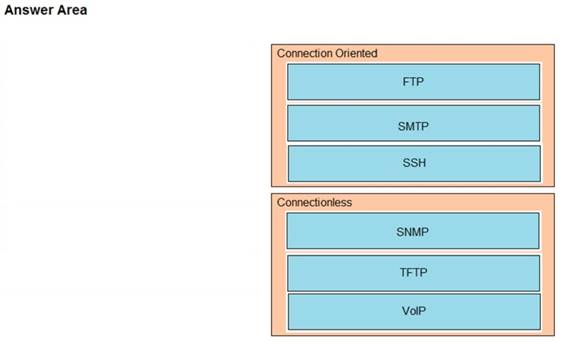
With REST API, which standard HTTP header tells a server which media type is expected by the client?
|
A. |
Accept-Encoding:
gzip. deflate |
|
B. |
Accept-Patch: text/example; charset=utf-8 |
|
C. |
Content-Type: application/json; charset=utf-8 |
|
D. |
Accept: application/json |
Answer: D
Explanation:
Accept header is a way for a client to specify the media type of the response content it is expecting and Content-type is a way to specify the media type of request being sent from the client to the server.
Drag and Drop Question
Drag and drop the SNMP manager and agent identifier commands from the left onto the functions on the right
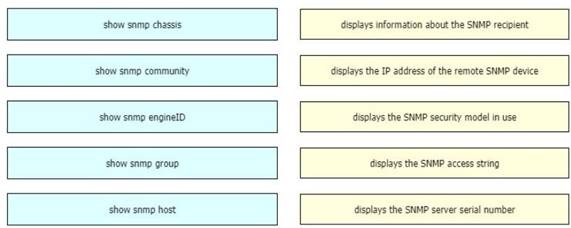
Answer:
![]()
Drag and Drop Question
Drag and drop the DHCP snooping terms from the left onto the descriptions on the right.
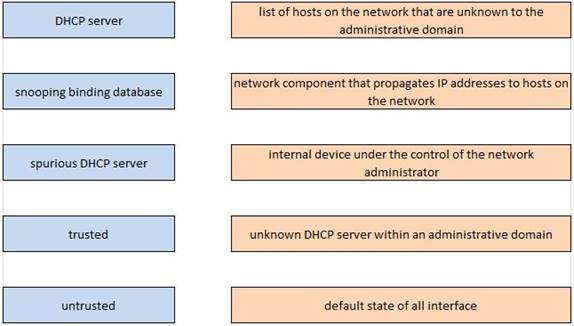
Answer:
![]()
Drag and Drop Question
Drag and drop the characteristics of network architectures from the left onto the type of architecture on the right.
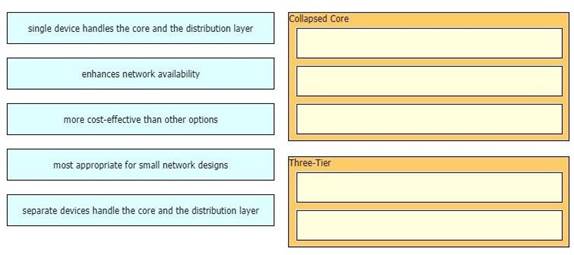
Answer:
![]()
What is a DNS lookup operation?
|
A. |
DNS server pings
the destination to verify that
it is available |
|
B. |
serves requests over destination port
53 |
|
C. |
DNS server forwards the client to an alternate IP address when
the primary IP is down |
|
D. |
responds to a request for IP address to domain name
resolution to the DNS server |
Answer: D
Refer to the exhibit. A network engineer must configured communication between PC A and the File Server. To prevent interruption for any other communications, which command must be configured?
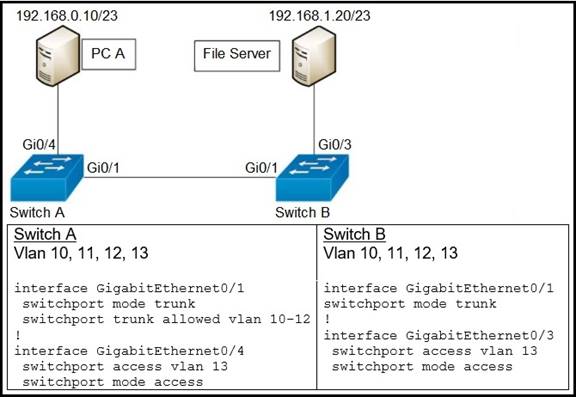
|
A. |
Switch trunk allowed
vlan 12 |
|
B. |
Switchport
trunk allowed vlan
none |
|
C. |
Switchport trunk
allowed vlan add 13 |
|
D. |
Switchport trunk allowed vlan remove 10-11 |
Answer: C
Explanation:
The switchport trunk allowed vlan command is used to specify the list of VLANs that are allowed on a trunk port. When a Layer 2 interface on a Cisco IOS device is configured to operate in trunk mode, the default setting is for the interface to carry all of the VLANs defined on the switch.
Which implementation provides the strongest encryption combination for the wireless environment?
|
A. |
WPA2 + AES |
|
B. |
WPA + AES |
|
C. |
WEP |
|
D. |
WPA + TKIP |
Answer:
A
What is a characteristic of a SOHO network?
|
A. |
connects each switch
to every other
switch in the network |
|
B. |
enables multiple users to share
a single broadband connection |
|
C. |
provides high
throughput access for 1000 or more users |
|
D. |
includes at least
three tiers of devices to provide load
balancing and redundancy |
Answer: B
Refer to the exhibit. After running the code in the exhibit, which step reduces the amount of data that the NETCONF server returns to the NETCONF client, to only the interface's configuration?
![]()
|
A. |
Use the Ixml library to parse the data returned by the NETCONF
server for the interface's configuration. |
|
B. |
Create an XML filter
as a string and pass
it to get_config() method as an argument. |
|
C. |
Create a JSON filter
as a string and pass
it to the get_config() method
as an argument. |
|
D. |
Use the
JSON library to parse the data returned by the NETCONF server for the
interface's configuration. |
Answer: D
Which resource is able to be shared among virtual machines deployed on the same physical server?
|
A. |
disk |
|
B. |
applications |
|
C. |
VM configuration file |
|
D. |
operating system |
Answer:
A
Which WAN topology provides a combination of simplicity quality, and availability?
|
A. |
partial mesh |
|
B. |
full mesh |
|
C. |
point-to-point |
|
D. |
hub-and-spoke |
Answer:
A
Explanation:
Full mesh and more so partial mesh from an enterprise perspective is anything but simple. Simplicity is the key word as in it's something a SOHO for example would prefer.
A dedicated point-to-point connection is still more available than a normal (consumer) broadband connection, which most people and companies use (with VPN).
Which command on a port enters the forwarding state immediately when a PC is connected to it?
|
A. |
switch(config)#spanning-tree portfast default |
|
B. |
switch(config)#spanning-tree portfast bpduguard default |
|
C. |
switch(config-if)#spanning-tree portfast trunk |
|
D. |
switch(config-if)#no spanning-tree portfast |
Answer:
A
Explanation:
Portfast (spanning-tree portfast command) does two things for us:
•
Interfaces with portfast
enabled that come up will go to forwarding mode immediately, the interface will skip the listening and
learning state.
•
A switch will never generate
a topology change notification for an interface
that has portfast enabled.
https://networklessons.com/switching/cisco-portfast-configuration https://www.dummies.com/programming/networking/cisco/spanning-tree-protocol-stp-and- portfast/
What are two functions of an SDN controller? (Choose two)
|
A. |
Layer 2 forwarding |
|
B. |
coordinating VTNs |
|
C. |
tracking hosts |
|
D. |
managing the
topology |
|
E. |
protecting against DDoS
attacks |
Answer:
BD
What is a network appliance that checks the state of a packet to determine whether the packet is legitimate?
|
A. |
Layer 2 switch |
|
B. |
load balancer |
|
C. |
firewall |
|
D. |
LAN controller |
Answer: C
When DHCP is configured on a router, which command must be entered so the default gateway is automatically distributed?
|
A. |
default-router |
|
B. |
default-gateway |
|
C. |
ip helper-address |
|
D. |
dns-server |
Answer:
A
Refer to the exhibit. The ntp server 192.168.0.3 command has been configured on router 1 to make it an NTP client of router 2. Which command must be configured on router 2 so that it operates in server-only mode and relies only on its internal clock?
![]()
|
A. |
Router2(config)#ntp passive |
|
B. |
Router2(config)#ntp server
172.17.0.1 |
|
C. |
Router2(config)#ntp master 4 |
|
D. |
Router2(config)#ntp server 192.168.0.2 |
Answer: C
Explanation:
ntp master {stratum-level}: NTP server mode - the device acts only as an NTP server, and not as an NTP client. The device gets its time information from the internal clock on the device.
ntp server {address | hostname}: NTP client/server mode - the device acts as both client and server. First, it acts as an NTP client, to synchronize time with a server. Once syn- chronized, the device can then act as an NTP server, to supply time to other NTP clients.
What is an appropriate use for private IPv4 addressing?
|
A. |
on the public-facing interface of a firewall |
|
B. |
to allow hosts inside
to communicate in both directions with hosts outside
the organization |
|
C. |
on internal hosts that stream data
solely to external resources |
|
D. |
on hosts that
communicates only with
other internal hosts |
Answer: D
Why does a switch flood a frame to all ports?
|
A. |
The frame has zero destination MAC addresses. |
|
B. |
The source MAC address of the frame
is unknown |
|
C. |
The source and destination MAC addresses of the frame
are the same |
|
D. |
The destination MAC
address of the frame is unknown. |
Answer: D
Explanation:
Switches tend to flood frame with the Unknown Destination MAC Address out all ports apart from the Originating (apart from the one it received) port.
If a switch port receives a new frame while it is actively transmitting a previous frame, how does it process the frames?
|
A. |
The new frame
is delivered first,
the previous frame
is dropped, and a retransmission request is sent. |
|
B. |
The previous frame
is delivered, the new frame
is dropped, and
a retransmission request
is sent. |
|
C. |
The new frame is placed in a queue
for transmission after
the previous frame. |
|
D. |
The two frames
are processed and
delivered at the
same time. |
Answer: C
How is the native VLAN secured in a network?
|
A. |
separate from other
VLANs within the administrative domain |
|
B. |
give it a value
in the private VLAN range |
|
C. |
assign it as VLAN
1 |
|
D. |
configure it as a different VLAN ID on each end of the link |
Answer: A
What is the purpose of a southbound API in a control based networking architecture?
|
A. |
Facilities communication between the controller and
the applications |
|
B. |
Facilities communication between the controller and the networking hardware |
|
C. |
allows application developers to interact with the network |
|
D. |
integrates a controller with other automation and orchestration tools. |
Answer:
B
Explanation:
In a controller-based network architecture, the controller needs to communicate to the networking devices.
What causes a port to be placed in the err-disabled state?
|
A. |
latency |
|
B. |
port security violation |
|
C. |
shutdown command issued on the port |
|
D. |
nothing plugged into
the port |
Answer: B
Explanation:
This mode is the default violation mode; when in this mode, the switch will automatically force the switchport into an error disabled (err-disable) state when a violation occurs. While in this state, the switchport forwards no traffic. The switchport can be brought out of this error disabled state by issuing the errdisable recovery cause CLI command or by disabling and reenabling the switchport.
Which switch technology establishes a network connection immediately when it is plugged in?
|
A. |
PortFast |
|
B. |
BPDU guard |
|
C. |
UplinkFast |
|
D. |
BackboneFast |
Answer: A
Explanation:
PortFast causes a switch or trunk port to enter the spanning tree forwarding state immediately, bypassing the listening and learning states.
You can use PortFast on switch or trunk ports that are connected to a single workstation, switch, or server to allow those devices to connect to the network immediately, instead of waiting for the port to transition from the listening and learning states to the forwarding state. https://www.ccexpert.us/routing-switching/portfast-uplinkfast-and-backbonefast.html
Which technology is appropriate for communication between an SDN controller and applications running over the network?
|
A. |
OpenFlow |
|
B. |
REST API |
|
C. |
NETCONF |
|
D. |
Southbound API |
Answer:
B
Explanation:
use nortbound (REST API) in communication between your applications and controller. use southbound (OpenFlow, OpFlex, RESTCONF, NETCONF) in communication between controller and network devices.
What is a characteristic of private IPv4 addressing?
|
A. |
traverse the Internet when an outbound ACL is applied |
|
B. |
issued by IANA in conjunction with
an autonomous system
number |
|
C. |
composed of up to 65.536
available addresses |
|
D. |
used without tracking or registration |
Answer: D
Which security program element involves installing badge readers on data-center doors to allow workers to enter and exit based on their job roles?
|
A. |
role-based access control |
|
B. |
biometrics |
|
C. |
multifactor authentication |
|
D. |
physical access control |
Answer: D
Explanation:
Access control readers give access to the building based on established credentials. Things like a key card, key fob, or biometrics like fingerprints are all considered established credentials.
Which network action occurs within the data plane?
|
A. |
compare the destination IP address to the IP routing table. |
|
B. |
run routing protocols (OSPF,
EIGRP, RIP, BGP) |
|
C. |
make a configuration change
from an incoming NETCONF RPC |
|
D. |
reply to an incoming ICMP
echo request |
Answer: A
Explanation:
The role of ICMP is to provide information about the path the data is taking from its point of origin to its destination. It has the same basic structure as an IP packet, but despite that, it's not really goodput. It's there to control 'how things are done', therefore, is part of the control plane.
When should an engineer implement a collapsed-core architecture?
|
A. |
for small networks with minimal need
for growth |
|
B. |
the access and distribution layers must be on the
same device |
|
C. |
for large networks that
are connected to multiple remote
sites |
|
D. |
only when using
VSS technology |
Answer: C
What uses HTTP messages to transfer data to applications residing on different hosts?
|
A. |
OpenFlow |
|
B. |
OpenStack |
|
C. |
OpFlex |
|
D. |
REST |
Answer: D
Explanation:
A RESTful API is an architectural style for an application program interface (API) that uses HTTP requests to access and use data. That data can be used to GET, PUT, POST and DELETE data types, which refers to the reading, updating, creating and deleting of operations concerning resources.
https://searchapparchitecture.techtarget.com/definition/RESTful-API
What is a role of access points in an enterprise network?
|
A. |
connect wireless devices to a wired
network |
|
B. |
support secure
user logins to devices or the network |
|
C. |
integrate with SNMP in preventing DDoS attacks |
|
D. |
serve as a first line
of defense in an enterprise network |
Answer:
A
Which protocol does an access point use to draw power from a connected switch?
|
A. |
Internet Group Management Protocol |
|
B. |
Adaptive Wireless Path Protocol |
|
C. |
Cisco Discovery Protocol |
|
D. |
Neighbor Discovery Protocol |
Answer: C
Explanation:
PoE switches support Cisco pre-standard PD detection mechanisms, and any Standards based compliant PDs. Most Cisco made PDs, pre-standard or standard, support Cisco Discovery Protocol (CDP). Once power is applied to a port that contains a pre-standard or standard Cisco PD, CDP is used in order to determine the actual power requirement, and the system power budget is adjusted accordingly.
Refer to the exhibit. An engineer must configure GigabitEthernet1/1 to accommodate voice and data traffic. Which configuration accomplishes this task?
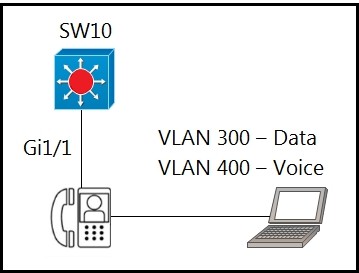
|
A. |
interface gigabitethernet1/1 switchport mode
access switchport access vlan
300 switchport voice vlan 400 |
|
B. |
interface gigabitethernet1/1 switchport mode trunk
switchport trunk vlan 300 switchport trunk
vlan 400 |
|
C. |
interface gigabitethernet1/1 switchport mode
access switchport voice vlan 300 switchport access
vlan 400 |
|
D. |
interface gigabitethernet1/1 switchport mode trunk
switchport trunk vlan 300 switchport voice vlan
400 |
Answer: A
When a WLAN with WPA2 PSK is configured in the Wireless LAN Controller GUI which format is supported?
|
A. |
Unicode |
|
B. |
base64 |
|
C. |
decimal |
|
D. |
ASCII |
Answer: D
Which networking function occurs on the data plane?
|
A. |
forwarding remote client/server traffic |
|
B. |
facilitates spanning-tree elections |
|
C. |
processing inbound
SSH management traffic |
|
D. |
sending and receiving OSPF Hello packets |
Answer: A
Explanation:
Networking devices operate in two planes; the data plane and the control plane. The control plane maintains Layer 2 and Layer 3 forwarding mechanisms using the CPU. The data plane forwards traffic flows
An engineer needs to add an old switch back into a network.
To prevent the switch from corrupting the VLAN database which action must be taken?
|
A. |
Add the switch
in the VTP domain with
a lower revision number |
|
B. |
Add the switch with
DTP set to dynamic desirable |
|
C. |
Add the switch in the VTP domain with
a higher revision number |
|
D. |
Add the switch
with DTP set to desirable |
Answer:
A
Explanation:
Before adding a VTP client to a VTP domain, always verify that its VTP configuration revision number is lower than the configuration revision number of the other switches in the VTP domain. Switches in a VTP domain always use the VLAN configuration of the switch with the highest VTP configuration revision number.
What does an SDN controller use as a communication protocol to relay forwarding changes to a southbound API?
|
A. |
OpenFlow |
|
B. |
Java |
|
C. |
REST |
|
D. |
XML |
Answer:
A
Explanation:
Southbound APIs facilitate control over the network and enable the SDN Controller to dynamically make changes according to real-time demands and needs.
OpenFlow, which was developed by the Open Networking Foundation (ONF), is the first and probably most well-known southbound interface. OpenFlow defines the way the SDN Controller should interact with the forwarding plane to make adjustments to the network, so it can better adapt to changing business requirements. With OpenFlow, entries can be added and removed to the internal flow-table of switches and routers to make the network more responsive to real-time traffic demands.
What is a similarity between OM3 and OM4 fiber optic cable?
|
A. |
Both have a 50 micron
core diameter |
|
B. |
Both have a 9 mic on
core diameter |
|
C. |
Both have
a 62 5 micron core
diameter |
|
D. |
Both have a 100 micron
core diameter |
Answer:
A
Which JSON data type is an unordered set of attribute-value pairs?
|
A. |
array |
|
B. |
string |
|
C. |
object |
|
D. |
Boolean |
Answer: C
A network engineer must configure the router R1 GigabitEthernet1/1 interface to connect to the router R2 GigabitEthernet1/1 interface. For the configuration to be applied the engineer must compress the address 2001:0db8:0000:0000:0500:000a:400F:583B.
Which command must be issued on the interface?
|
A. |
ipv6 address 2001:0db8::5:a:4F:583B |
|
B. |
ipv6 address
2001:db8::500:a:400F:583B |
|
C. |
ipv6 address 2001
db8:0::500:a:4F:583B |
|
D. |
ipv6 address 2001::db8:0000::500:a:400F:583B |
Answer: B
What is the benefit of using FHRP?
|
A. |
reduced management overhead on network routers |
|
B. |
balancing traffic across multiple gateways in proportion to their loads |
|
C. |
higher degree
of availability |
|
D. |
reduced ARP traffic
on the network |
Answer: C
Which two QoS tools provides congestion management? ( Choose two )
|
A. |
CAR |
|
B. |
CBWFQ |
|
C. |
PQ |
|
D. |
PBR |
|
E. |
FRTS |
Answer:
BC
Explanation:
Type of queuing methods are available:
-
First-In-First-Out (FIFO)
- Priority Queuing
(PQ)
- Custom Queuing
(CQ)
- Weighted Fair Queuing (WFQ)
-
Class-Based Weighted Fair Queuing (CBWFQ)
- Low-Latency Queuing
(LLQ)
https://www.orbit-computer-solutions.com/qos-congestion-management-tools/
Refer to the exhibit. Which command must be executed for Gi1.1 on SW1 to become a trunk port if Gi1/1 on SW2 is configured in desirable or trunk mode?
![]()
|
A. |
switchport mode trunk |
|
B. |
switchport mode
dot1-tunnel |
|
C. |
switchport mode
dynamic auto |
|
D. |
switchport mode dynamic
desirable |
Answer: C
Refer to the exhibit. Only four switches are participating in the VLAN spanning-tree process.
Branch-1 priority
614440
Branch-2: priority
39082416
Branch-3:
priority 0 Branch-4: root primary
Which switch becomes the permanent root bridge for VLAN 5?
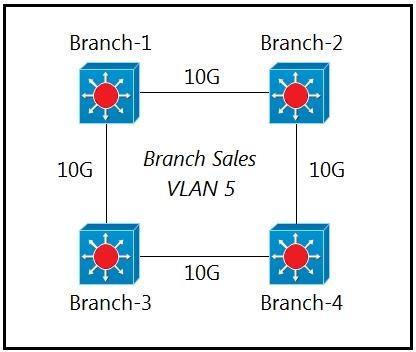
|
A. |
Branch-1 |
|
B. |
Branch-2 |
|
C. |
Branch-3 |
|
D. |
Branch-4 |
Answer: C
Explanation:
Ideally the root bridge is placed on a core switch, and a secondary root bridge is designated to minimize changes to the overall spanning tree. Root bridge placement is accomplished by lowering the system priority on the root bridge to the lowest value possible, raising the secondary root bridge to a value slightly higher than that of the root bridge, and (ideally) increasing the system priority on all other switches. This ensures consistent placement of the root bridge.
A network administrator must to configure SSH for remote access to router R1. The requirement is to use a public and private key pair to encrypt management traffic to and from the connecting client. Which configuration, when applied, meets the requirements?
|
A. |
R1#enable
R1#configure terminal R1(config)#ip domain-name cisco.com R1(config)#crypto key generate ec keysize 1024 |
|
B. |
R1#enable
R1#configure terminal R1(config)#ip domain-name cisco.com R1(config)#crypto key generate ec keysize 2048 |
|
C. |
R1#enable R1#configure terminal R1(config)#ip domain-name cisco.com
R1(config)#crypto key encrypt
rsa name myKey |
|
D. |
R1#enable R1#configure terminal R1(config)#ip domain-name cisco.com |
R1(config)#crypto key generate rsa modulus 1024
Answer: D
Explanation:
crypto key generate rsa [general-keys | usage-keys | signature | encryption] [label key-label] [exportable] [modulus modulus-size] [storage devicename :] [redundancy] [on devicename :]
modulus modulus-size
By default, the modulus of a certification authority (CA) key is 1024 bits. The recommended modulus for a CA key is 2048 bits. The range of a CA key modulus is from 350 to 4096 bits. As the default key is 1024 bits.
When deploying syslog, which severity level logs informational message?
|
A. |
0 |
|
B. |
2 |
|
C. |
4 |
|
D. |
6 |
Answer: D
Explanation:
Number of the desired severity level at which messages should be logged. Messages at or numerically lower than the specified level are logged. Severity levels are as follows:
0
—emergency: System unusable
1 —alert: Immediate
action needed
2
—critical: Critical condition—default level
3
—error: Error condition
4
—warning: Warning condition
5 —notification: Normal
but significant condition
6
—informational: Informational message
only
7
—debugging: Appears during debugging only
An engineer observes high usage on the 2.4GHz channels and lower usage on the 5GHz channels. What must be configured to allow clients to preferentially use 5GH2 access points?
|
A. |
Re-Anchor Roamed Clients |
|
B. |
11ac MU-MIMO |
|
C. |
OEAP Split
Tunnel |
|
D. |
Client Band Select |
Answer: D
Explanation:
Band Select is Cisco's terminology for Band Steering. When enabled it encourages stations onto the 5 GHz band. This is achieved by suppressing 2.4 GHz probe response frames to station probe requests and by responding with 5 GHz probe response frames first.
An administrator must secure the WLC from receiving spoofed association requests.
Which steps must be taken to configure the WLC to restrict the requests and force the user to wait 10 ms to retry an association request?
|
A. |
Enable Security Association Teardown Protection a d set
the SA Query
timeout to 10 |
|
B. |
Enable MAC filtering and set the SA Query
timeout to 10 |
|
C. |
Enable 802.1x
Layer 2 security and set me Comeback timer
to 10 |
|
D. |
Enable the Protected Management Frame service
and set the
Comeback timer to
10 |
Answer: C
Explanation:
Step 1. You need to enable protected management frame under the SSID configured with 802.1x/PSK. You have three options as shown in the image.
Step 2. You then need to specify the Comeback timer and SA query timeout. Comeback timer specifies the time which an associated client must wait before the association can be tried again when first denied with a status code 30. SA query timeout specifies the amount of time the WLC waits for a response from the client for the query process. If there is no response from the client, its association is deleted from the controller. This is done as shown in the image. https://www.cisco.com/c/en/us/support/docs/wireless-mobility/wireless-lan-wlan/212576- configure-802-11w-management-frame-prote.html#anc8
What are two improvements provided by automation for network management in an SDN environment? (Choose two)
|
A. |
Data collection and analysis tools
establish a baseline for the network |
|
B. |
Artificial intelligence identifies and prevents potential design failures. |
|
C. |
Machine learning minimizes the overall error
rate when automating troubleshooting processes |
|
D. |
New devices are onboarded with minimal effort |
|
E. |
Proprietary Cisco APIs
leverage multiple network management tools. |
Answer:
BE
Refer to the exhibit. Shortly after SiteA was connected to SiteB over a new single-mode fiber path, users at SiteA report intermittent connectivity issues with applications hosted at SiteB. What is the cause of the intermittent connectivity issue?
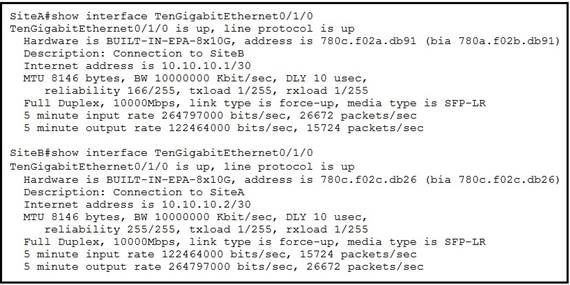
|
A. |
Interface errors are
incrementing |
|
B. |
An incorrect SFP media
type was used at SiteA |
|
C. |
High usage
is causing high latency |
|
D. |
The sites were connected with
the wrong cable
type |
Answer: A
Explanation:
reliability 255/255: When the input and output errors increase, they affect the reliability counter. This indicates how likely it is that a packet can be delivered or received successfully. Reliability is calculated like this: reliability = number of packets / number of total frames. The value of 255 is the highest value meaning that the interface is very reliable at the moment. The calculation above is done every 5 minutes.
Which technology allows for multiple operating systems to be run on a single host computer?
|
A. |
virtual routing and
forwarding |
|
B. |
network port
ID v sualization |
|
C. |
virtual device
on exts |
|
D. |
server
visualization |
Answer: D
How does authentication differ from authorization?
|
A. |
Authentication verifies the identity of a person
accessing a network, and authorization determines what resource a user can access. |
|
B. |
Authentication
is used to record what
resource a user accesses, and authorization is used to determine what resources a user can
access |
|
C. |
Authentication is used to determine what
resources a user
is allowed to access, and
authorization is used to track what equipment is allowed access to the
network |
|
D. |
Authentication is used
to verify a person's identity, and authorization is used to create syslog messages for logins. |
Answer: A
What occurs when overlapping Wi-Fi channels are implemented?
|
A. |
The wireless network
becomes vulnerable to unauthorized access. |
|
B. |
Wireless devices are unable to distinguish between different SSIDs |
|
C. |
Users experience poor wireless network
performance. |
|
D. |
Network communications are open to eavesdropping. |
Answer: C
Refer to the exhibit. An administrator must turn off the Cisco Discovery Protocol on the port configured with address last usable address in the 10.0.0.0/30 subnet.
Which command set meets the requirement?
![]()
|
A. |
interface gi0/1 no cdp enable |
|
B. |
interface
gi0/1 clear cdp table |
|
C. |
interface gi0/0 no cdp advertise-v2 |
|
D. |
interface gi0/0 no cdp run |
Answer: D
Refer to the exhibit. The entire contents or the MAC address table are shown. Sales-4 sends a data frame to Sales-1.
![]()
What does the switch do as it receives the frame from Sales-4?
|
A. |
Perform a lookup
in the MAC address table
and discard the frame due
to a missing entry. |
|
B. |
Insert the
source MAC address and port into the forwarding table and forward
the frame to Sales- 1. |
|
C. |
Map the Layer 2 MAC address
to the Layer
3 IP address and forward
the frame. |
|
D. |
Flood the fr me out of all ports except
on the port where Sales-1
is connected. |
Answer:
B
Which 802.11 management frame type is sent when a client roams between access points on the same SSID?
|
A. |
Reassociation Request |
|
B. |
Probe Request |
|
C. |
Authentication Request |
|
D. |
Association Request |
Answer: A
Drag and Drop Question
Drag and drop the TCP/IP protocols from the left onto their primary transmission protocols on the right.
![]()
Answer:
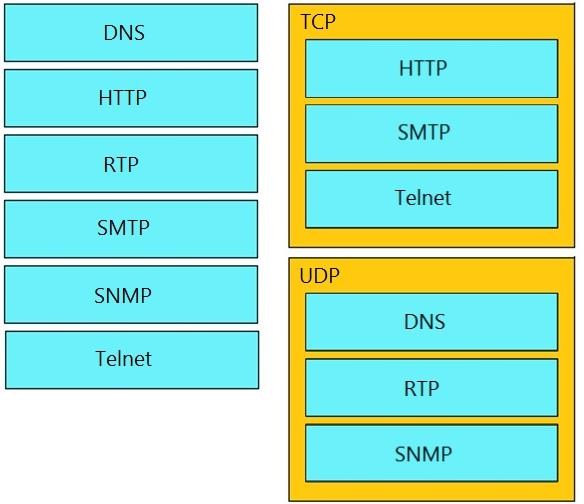
An engineer must configure the IPv6 address 2001:0db8:0000:0000:0700:0003:400F:572B on the serial0/0 interface of the HQ router and wants to compress it for easier configuration.
Which command must be issued on the router interface?
|
A. |
ipv6 address 2001:db8::700:3:400F:572B |
|
B. |
ipv6 address
2001:db8:0::700:3:4F:572B |
|
C. |
ipv6 address
2001:Odb8::7:3:4F:572B |
|
D. |
ipv6 address 2001::db8:0000::700:3:400F:572B |
Answer:
A
What describes the operation of virtual machines?
|
A. |
Virtual machines are responsible for managing and allocating host
hardware resources |
|
B. |
In a virtual machine
environment, physical servers must run one
operating system at a time. |
|
C. |
Virtual machines are the physical hardware that support
a virtual environment. |
|
D. |
Virtual machines are operating system
instances that are decoupled from
server hardware |
Answer: D
Which WLC port connects to a switch to pass normal access-point traffic?
|
A. |
redundancy |
|
B. |
console |
|
C. |
distribution system |
|
D. |
service |
Answer: C
Which IPv6 address type provides communication between subnets and is unable to route on the Internet?
|
A. |
global unicast |
|
B. |
unique local |
|
C. |
link-local |
|
D. |
multicast |
Answer:
B
An engineering team asks an implementer to configure syslog for warning conditions and error conditions.
Which command does the implementer configure to achieve the desired result?
|
A. |
logging trap 5 |
|
B. |
logging trap 2 |
|
C. |
logging trap 4 |
|
D. |
logging trap 3 |
Answer: C
Drag and Drop Question
Drag and drop the 802.11 wireless standards from the left onto the matching statements on the right.
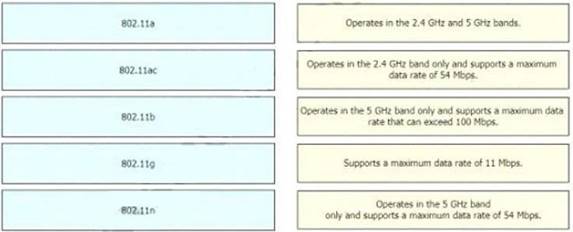
Answer:
![]()
What are two characteristics of the distribution layer in a three-tier network architecture? (Choose two.)
|
A. |
serves as the network aggregation point |
|
B. |
provides a boundary between Layer 2 and Layer 3 communications |
|
C. |
designed to meet continuous, redundant uptime requirements |
|
D. |
is the backbone for the network topology |
|
E. |
physical connection point
for a LAN
printer |
Answer: AB
Explanation:
The distribution layer aggregates the data received from the access layer switches before it is transmitted to the core layer for routing to its final destination. In Figure 1-6, the distribution layer is the boundary between the Layer 2 domains and the Layer 3 routed network. https://www.ciscopress.com/articles/article.asp?p=2202410&seqNum=4
What is the purpose of using First Hop Redundancy Protocol in a specific subnet?
|
A. |
Filter traffic based
on destination IP addressing |
|
B. |
Sends the default route
to the hosts
on a network |
|
C. |
ensures a loop-free physical topology |
|
D. |
forwards multicast hello
messages between routers |
Answer: D
Explanation:
FHRP is layer 3 protocol whose purpose is to protect the default gateway by offering redundancy of the gateway in a subnet. This is achieved by allowing two or more routers to provide a backup for the first-hop IP router address. If a failure of an active router occurs, the backup router will take over the address. The routers negotiate their roles (Active/Standby) with each other by multicast hello messages to share the VIP (virtual IP address) between the FHRP routers. The terms Active/Standby vary between the different types of FHRP. The active router will act as the default gateway and the standby router acts as a backup the active router.
Which access layer threat-mitigation technique provides security based on identity?
|
A. |
Dynamic ARP Inspection |
|
B. |
using a non-default native
VLAN |
|
C. |
802.1x |
|
D. |
DHCP snooping |
Answer: C
What must be considered when using 802:11 ta?
|
A. |
It is compatible with 802 lib-
and 802 11-compliant wireless devices |
|
B. |
It is used in place of 802 11b/g
when many nonoverlapping channels are required |
|
C. |
It is susceptible to interference from 2 4 GHz devices
such as microwave ovens. |
|
D. |
It is chosen
over 802 11b/g
when a lower-cost solution is necessary |
Answer: B
Explanation:
802.11a and 802.11b are not compatible since 802.11a operates at the 5GHz frequency band and 802.11b operates at the 2.4GHz band. The 2.4 GHz frequency band with a channel width of 22 MHz only has 3 non-overlapping channels (1, 6 and 11) whereas the 5 GHz band has 23 non- overlapping channels with a 20 MHz channel width. Therefore, 802.11a is preferred over 802.11b and 802.11g when many non-overlapping channels are required since they both operate at
2.4GHz unlike 802.11a.
When a site-to-site VPN is configured which IPsec mode provides encapsulation and encryption of the entire original IP packet?
|
A. |
IPsec tunnel mode
with AH |
|
B. |
IPsec transport mode with AH |
|
C. |
IPsec tunnel mode
with ESP |
|
D. |
IPsec transport mode with ESP |
Answer: C
What does physical access control regulate?
|
A. |
access to spec
fie networks based
on business function |
|
B. |
access to servers to prevent malicious activity |
|
C. |
access to computer networks and file systems |
|
D. |
access to networking equipment and facilities |
Answer: D
On workstations running Microsoft Windows, which protocol provides the default gateway for the device?
|
A. |
DHCP |
|
B. |
STP |
|
C. |
SNMP |
|
D. |
DNS |
Answer:
A
How are VLAN hopping attacks mitigated?
|
A. |
enable dynamic ARP
inspection |
|
B. |
manually implement trunk ports and disable DTP |
|
C. |
activate all ports and place in the default
VLAN |
|
D. |
configure extended VLANs |
Answer:
B
What is the role of a firewall in an enterprise network?
|
A. |
Forwards packets based
on stateless packet
inspection |
|
B. |
Processes unauthorized packets and allows
passage to less
secure segments of the network |
|
C. |
determines which
packets are allowed
to cross from
unsecured to secured
networks |
|
D. |
explicitly denies all
packets from entering an administrative domain |
Answer: C
Which two primary drivers support the need for network automation? (Choose two.)
|
A. |
Eliminating training needs |
|
B. |
Increasing reliance on self-diagnostic and self-healing |
|
C. |
Policy-derived provisioning of resources |
|
D. |
Providing a ship entry
point for resource provisioning |
|
E. |
Reducing hardware footprint |
Answer: CD
What is a function of the Cisco DNA Center Overall Health Dashboard?
|
A. |
It provides a summary of the top 10 global
issues. |
|
B. |
It provides detailed activity logging for the 10 devices and users on the network. |
|
C. |
It summarizes the operational status of each
wireless devise on the network. |
|
D. |
It summarizes daily
and weekly CPU usage for
servers and workstations in the network. |
Answer:
A
Which protocol requires authentication to transfer a backup configuration file from a router to a remote server?
|
A. |
DTP |
|
B. |
FTP |
|
C. |
SMTP |
|
D. |
TFTP |
Answer: B
After installing a new Cisco ISE server, which task must the engineer perform on the Cisco WLC to connect wireless clients on a specific VLAN based on their credentials?
|
A. |
Enable the allow
AAA Override |
|
B. |
Enable the Even: Driven
RRM. |
|
C. |
Disable the
LAG Mode or Next Reboot. |
|
D. |
Enable the Authorized MIC APs against auth-list or AAA. |
Answer:
A
Explanation:
In order to support centralized access control through a centralized AAA server such as the Cisco Identity Services Engine (ISE) or ACS, the IPv6 ACL can be provisioned on a per-client basis using AAA Override attributes. In order to use this feature, the IPv6 ACL must be configured on the controller and the WLAN must be configured with the AAA Override feature enabled. https://www.cisco.com/c/en/us/td/docs/wireless/controller/7-6/configuration- guide/b_cg76/b_cg76_chapter_0111001.pdf
Which QoS tool is used to optimize voice traffic on a network that is primarily intended for data traffic?
|
A. |
FIFO |
|
B. |
WFQ |
|
C. |
PQ |
|
D. |
WRED |
Answer: C
Explanation:
Many popular QoS techniques that serve data traffic very well, such as WFQ and RED, are ineffective for voice applications.
FIFO (first-in, first-out). FIFO entails no concept of priority or classes of traffic. With FIFO, transmission of packets out the interface occurs in the order the packets arrive.
Drag and Drop Question
An engineer is configuring an encrypted password for the enable command on a router where the local user database has already been configured. Drag and drop the configuration commands from the left into the correct sequence on the right Not all commands are used
![]()
Answer:
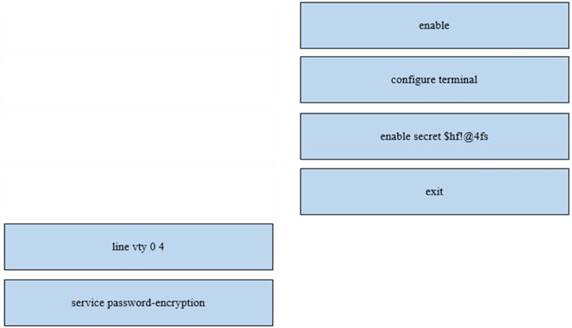
Where is the interface between the control plane and data plane within the software-defined architecture?
|
A. |
control layer and the infrastructure layer |
|
B. |
application layer
and the infrastructure layer |
|
C. |
application layer
and the management layer |
|
D. |
control layer and the application layer |
Answer:
A
An implementer is preparing hardware for virtualization to create virtual machines on a host. What is needed to provide communication between hardware and virtual machines?
|
A. |
hypervisor |
|
B. |
router |
|
C. |
straight cable |
|
D. |
switch |
Answer:
A
Explanation:
A computer that hosts VMs requires specialized software called a hypervisor. The hypervisor emulates the computer's CPU, memory, hard disk, network and other hardware resources, creating a pool of resources that can be allocated to the individual VMs according to their specific requirements. The hypervisor can support multiple virtual hardware platforms that are isolated from each other, enabling VMs to run Linux and Windows Server OSes on the same physical host.
A network analyst is tasked with configured the date and time on a router using EXEC mode. The date must be set to 12:00am. Which command should be used?
|
A. |
Clock timezone |
|
B. |
Clock summer-time-recurring |
|
C. |
Clock summer-time date |
|
D. |
Clock set |
Answer: D
Refer to the exhibit. What is the subnet mask of the route to the 10.10.13.160 prefix?
![]()
|
A. |
255.255.255.240 |
|
B. |
255.255.255.128 |
|
C. |
255.255.248.0 |
|
D. |
255.255.255.248 |
Answer: D
A network administrator is asked to configure VLANS 2, 3 and 4 for a new implementation. Some ports must be assigned to the new VLANS with unused remaining. Which action should be taken for the unused ports?
|
A. |
configure port in the native
VLAN |
|
B. |
configure ports
in a black hole VLAN |
|
C. |
configure in a nondefault native VLAN |
|
D. |
configure ports as access ports |
Answer:
B
Refer to the exhibit. Router R4 is dynamically learning the path to the server. If R4 is connected to R1 via OSPF Area 20, to R2 via R2 BGP, and to R3 via EIGRP 777, which path is installed in the routing table of R4?
![]()
|
A. |
the path through
R1, because the OSPF administrative distance is 110 |
|
B. |
the path through R2. because the IBGP administrative distance is 200 |
|
C. |
the path through R2 because the EBGP administrative distance is 20 |
|
D. |
the path through R3. because the EIGRP administrative distance is lower
than OSPF and
BGP |
Answer: C
Why was the RFC 1918 address space defined?
|
A. |
conserve public IPv4
addressing |
|
B. |
preserve public
IPv6 address space |
|
C. |
reduce instances of overlapping IP addresses |
|
D. |
support the NAT
protocol |
Answer: A
Explanation:
An RFC1918 address is an IP address that is assigned by an enterprise organization to an internal host. These IP addresses are used in private networks, which are not available, or reachable, from the Internet.
Which HTTP status code is returned after a successful REST API request?
|
A. |
200 |
|
B. |
301 |
|
C. |
404 |
|
D. |
500 |
Answer:
A
Refer to the exhibit. R5 is the current DR on the network, and R4 is the BDR. Their interfaces are flapping, so a network engineer wants the OSPF network to elect a different DR and BDR. Which set of configurations must the engineer implement?
![]()
|
A. |
R4(config)#interface
gi0/0 R4(config-if)#ip ospf priority 20 R5(config)#interface gi0/0 R5(config-if)#ip ospf
priority 10 |
|
B. |
R5(config)#interface
gi0/0 R5(config-if)#ip ospf priority 120 R4(config)#interface gi0/0 R4(config-if)#ip ospf
priority 110 |
|
C. |
R3(config)#interface gi0/0 R3(config-if)#ip ospf priority 255 R2(config)#interface gi0/0 R2(config-if)#ip
ospf priority 240 |
|
D. |
R2(config)#interface
gi0/0 R2(config-if)#ip ospf priority 259 R3(config)#interface gi0/0 R3(config-if)#ip
ospf priority 256 |
Answer: C
What are network endpoints?
|
A. |
act as routers
to connect a user to the service prowler network |
|
B. |
a threat to the network if they are compromised |
|
C. |
support inter-VLAN connectivity |
|
D. |
enforce policies for campus-wide traffic
going to the internet |
Answer:
B
Refer to the exhibit. Which two prefixes are included in this routing table entry? (Choose two.)
![]()
|
A. |
192.168.1.17 |
|
B. |
192.168.1.61 |
|
C. |
192.168.1.64 |
|
D. |
192.168.1.127 |
|
E. |
192.168.1.254 |
Answer: AB
Explanation:
192.168.0-63 because /26 = 64 IP addresses per subnet and 4 subnets (256/64), 0-63, 64-127,
128-191, 192-255.
Which two components are needed to create an Ansible script that configures a VLAN on a switch? (Choose two.)
|
A. |
cookbook |
|
B. |
task |
|
C. |
playbook |
|
D. |
model |
|
E. |
recipe |
Answer:
BC
Explanation:
Ansible playbooks: “files that provide actions and logic about what Ansible should do.”
“The playbook will list tasks and choices based on those results, like “Configure all branch routers in these locations, and if errors occur for any device, do these extra tasks for that device”.”
Which two events occur automatically when a device Is added to Cisco DNA Center? (Choose two. )
|
A. |
The device is assigned to the Global
site. |
|
B. |
The device is placed
into the Unmanaged state. |
|
C. |
The device is placed
into the Provisioned state. |
|
D. |
The device is placed
into the Managed state. |
|
E. |
The device is assigned to the Local
site. |
Answer: AD
Explanation:
Device in Global Site: When you successfully add, import, or discover a device, Cisco DNA Center places the device in the Managed state and assigns it to the Global site by default. Even if you have defined SNMP server, Syslog server, and NetFlow collector settings for the Global site, Cisco DNA Center does not change these settings on the device. https://www.cisco.com/c/en/us/td/docs/cloud-systems-management/network-automation-and- management/dna-center/2-1- 2/admin_guide/b_cisco_dna_center_admin_guide_2_1_2/b_cisco_dna_center_admin_guide_2_1
_1_chapter_010.html
Which virtual MAC address is used by VRRP group 1?
|
A. |
0050.0c05.ad81 |
|
B. |
0007.c061.bc01 |
|
C. |
0000.5E00.0101 |
|
D. |
0500.3976.6401 |
Answer: C
Explanation:
A virtual MAC address is generated by the virtual router based on the virtual router ID. The virtual MAC address format is 00-00-5E-00-01-{VRID} (VRRP) and 00-00-5E-00-02-{VRID}.
Refer to the exhibit. Which two commands, when configured on router R1, fulfill these requirements? (Choose two.)
- Packets toward the entire network
2001:db8:23::/64 must be forwarded
through router R2.
- Packets toward host 2001:db8:23::14 preferably must be forwarded through R3.
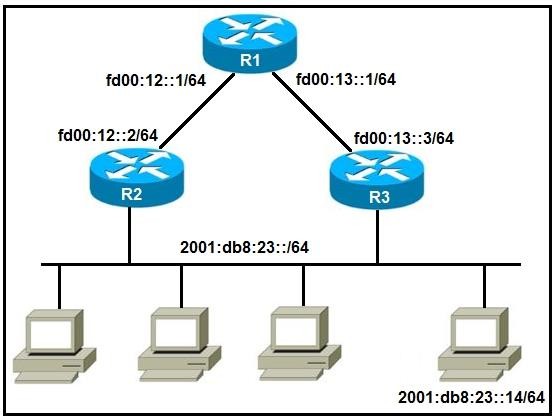
|
A. |
Ipv6 route 2001:db8:23::/128 fd00:12::2 |
|
B. |
Ipv6 route
2001:db8:23::14/128 fd00:13::3 |
|
C. |
Ipv6 route
2001:db8:23::14/64 fd00:12::2 |
|
D. |
Ipv6 route
2001:db8:23::/64 fd00:12::2 |
|
E. |
Ipv6 route 2001:db8:23::14/64 fd00:12::2 200 |
Answer:
BD
Explanation:
Therefore, we use a host route meaning that all bits of the ipv6 destination address must match (prefix-length of /128). Also, the next hop address should be that of R3 (fd00:13::3) since the question asks that packets for the host must be forwarded through it.
Refer to the exhibit. When PC-A sends traffic to PC-B, which network component is in charge of receiving the packet from PC-A verifying the IP addresses, and forwarding the packet to PC-B?
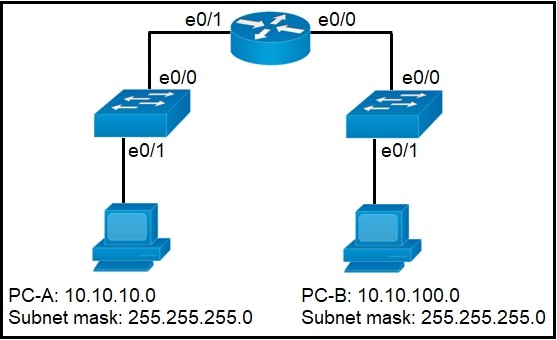
|
A. |
Layer 2 switch |
|
B. |
Router |
|
C. |
Load balancer |
|
D. |
firewall |
Answer:
B
In software-defined architecture, which place handles switching for traffic through a Cisco router?
|
A. |
Control |
|
B. |
Management |
|
C. |
Data |
|
D. |
application |
Answer: C
Which level of severity must be set to get informational syslogs?
|
A. |
alert |
|
B. |
critical |
|
C. |
notice |
|
D. |
debug |
Answer: D
Explanation:
Specifying a level causes messages at that level and numerically lower levels to be displayed at the destination.
From Table 3 : informational level = 6, debugging level = 7, notice/notifications level = 5 https://www.cisco.com/c/en/us/td/docs/routers/access/wireless/software/guide/SysMsgLogging.ht ml
When a switch receives a frame for a known destination MAC address, how is the frame handed?
|
A. |
sent to the port identified for the known
MAC address |
|
B. |
broadcast to all ports |
|
C. |
forwarded to the first
available port |
|
D. |
flooded to all ports except
the one from
which it originated |
Answer:
A
Explanation:
A switch builds its MAC address table by recording the MAC address of each device connected to each of its ports. The switch uses the information in the MAC address table to send frames destined for a specific device out the port, which has been assigned to that device. https://www.ciscopress.com/articles/article.asp?p=2181835&seqNum=5
How does QoS optimize voice traffic?
|
A. |
reducing bandwidth usage |
|
B. |
by reducing packet loss |
|
C. |
by differentiating voice and video traffic |
|
D. |
by increasing jitter |
Answer: C
What is the function of a controller in controller-based networking?
|
A. |
It serves as the centralized management point of an SDN
architecture. |
|
B. |
It centralizes the data
plane for the
network. |
|
C. |
It is the card on a core router
that maintains all routing decisions for a campus. |
|
D. |
It is a pair of core routers that maintain all routing decisions for a campus |
Answer:
A
Which action does the router take as it forwards a packet through the network?
|
A. |
The router replaces the original source
and destination MAC addresses with
the sending router MAC address as the source and neighbor MAC address as the destination |
|
B. |
The router
encapsulates the original packet and then
includes a tag that identifies the source router
MAC address and transmits it transparently to the destination |
|
C. |
The router
encapsulates the source
and destination IP addresses with
the sending router
IP address as the source and the neighbor IP address as the
destination |
|
D. |
The router replaces the source and destination labels
with the sending
router interface label
as a |
source and the next hop router label as a destination
Answer: A
Explanation:
Only mac address gets changed when forwarding, IP address always stays the same.
What are two similarities between UTP Cat 5e and Cat 6a cabling? (Choose two.)
|
A. |
Both operate at a frequency of 500 MHz. |
|
B. |
Both support
runs of up to 55 meters. |
|
C. |
Both support
runs of up to 100
meters. |
|
D. |
Both support
speeds of at least 1 Gigabit. |
|
E. |
Both support speeds
up to 10 Gigabit. |
Answer: CD
What is a characteristic of cloud-based network topology?
|
A. |
wireless connections provide
the sole access
method to services |
|
B. |
onsite network services are provided with physical Layer
2 and Layer 3 components |
|
C. |
services are provided by a public, private, or hybrid
deployment |
|
D. |
physical workstations are
configured to share
resources |
Answer: C
What is the difference in data transmission delivery and reliability between TCP and UDP?
|
A. |
TCP transmits data
at a higher rate and ensures packet
delivery. UDP retransmits lost data to ensure applications receive the data on the remote end. |
|
B. |
UDP sets
up a connection between both
devices before transmitting data. TCP uses
the three- way handshake to
transmit data with a reliable connection. |
|
C. |
UDP is used for multicast and broadcast communication. TCP is used
for unicast communication and transmits data at a
higher rate with error checking. |
|
D. |
TCP requires the connection to be established before transmitting data.
UDP transmits data
at a higher rate without
ensuring packet delivery. |
Answer: D
Explanation:
UDP speeds up transmissions by enabling the transfer of data before an agreement is provided by the receiving party. As a result, UDP is beneficial in time- sensitive communications, including voice over IP (VoIP), domain name system (DNS) lookup, and video or audio playback.
How are the switches in a spine-and-leaf topology interconnected?
|
A. |
Each leaf switch
is connected to one of the spine
switches. |
|
B. |
Each leaf switch
is connected to two spine
switches, making a loop. |
|
C. |
Each leaf
switch is connected to each spine
switch. |
|
D. |
Each leaf switch
is connected to a central leaf switch, then uplinked to a core spine switch. |
Answer: C
Explanation:
Each leaf switch connects to all spine switches, which creates a large non-blocking fabric, increasing the level of redundancy and reducing traffic bottlenecks.
Refer to the exhibit. What is the metric of the route to the 192.168.10.33/28 subnet?
![]()
|
A. |
84 |
|
B. |
110 |
|
C. |
128 |
|
D. |
192 |
|
E. |
193 |
Answer:
E
Explanation:
What route would you use to send traffic to the 192.168.10.33/28 subnet. 192.168.10.33 is part of the 192.168.10.32/28 subnet and would use that OSPF route. These IPs would also use that same route (.33 - .47)/ (AD/METRIC) (110/193).
Which two protocols must be disabled to increase security for management connections to a Wireless LAN Controller? (Choose two )
|
A. |
Telnet |
|
B. |
SSH |
|
C. |
HTTP |
|
D. |
HTTPS |
|
E. |
TFTP |
Answer:
AC
Explanation:
HTTP and Telnet both are unsecure. That’s why we have HTTPS and SSH. TFTP isn’t used for WLC topics. Only simple file transferring unencrypted.
What are two benefits of using the PortFast feature? (Choose two)
|
A. |
Enabled interfaces are automatically placed
in listening state |
|
B. |
Enabled interfaces come up and move to the forwarding state immediately |
|
C. |
Enabled interfaces never generate topology change notifications. |
|
D. |
Enabled interfaces that move to the learning state generate switch
topology change notifications |
|
E. |
Enabled interfaces wait
50 seconds before
they move to the forwarding state |
Answer: BC
Explanation:
“A switch will never generate a topology change notification for an interface that has portfast enabled.”
https://networklessons.com/switching/cisco-portfast-configuration
“Another major benefit of the STP portfast feature is that the access ports bypass the earlier 802.1D STP states (learning and listening) and forward traffic immediately.” https://www.ciscopress.com/articles/article.asp?p=2995351&seqNum=3
Which function is performed by DHCP snooping?
|
A. |
propagates VLAN information between switches |
|
B. |
listens to multicast traffic for packet forwarding |
|
C. |
provides DDoS
mitigation |
|
D. |
rate-limits certain traffic |
Answer: D
Explanation:
DHCP snooping is a security feature that acts like a firewall between untrusted hosts and trusted DHCP servers. The DHCP snooping feature performs the following activities: Validates DHCP messages received from untrusted sources and filters out invalid messages.
When a client and server are not on the same physical network, which device is used to forward requests and replies between client and server for DHCP?
|
A. |
DHCP relay agent |
|
B. |
DHCP server |
|
C. |
DHCPDISCOVER |
|
D. |
DHCPOFFER |
Answer: A
Explanation:
A DHCP relay agent is any host that forwards DHCP packets between clients and servers. Relay agents are used to forward requests and replies between clients and servers when they are not on the same physical subnet.
Drag and Drop Question
Drag and drop the functions of DHCP from the left onto any of the positions on the right Not all functions are used.
![]()
Answer:
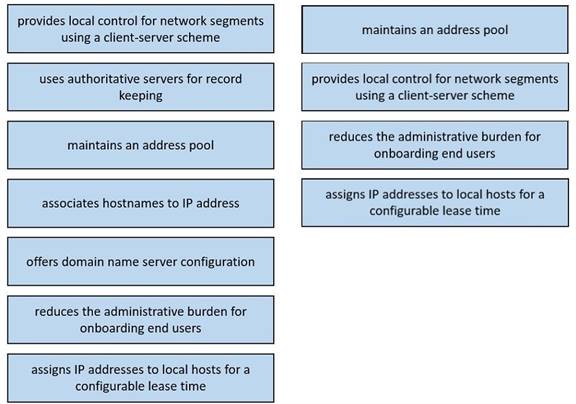
Which plane is centralized by an SON controller?
|
A. |
management-plane |
|
B. |
control-plane |
|
C. |
data-plane |
|
D. |
services-plane |
Answer:
B
An engineer configures interface Gi1/0 on the company PE router to connect to an ISP Neighbor discovery is disabled.
![]()
Which action is necessary to complete the configuration if the ISP uses third-party network
devices?
|
A. |
Enable LLDP globally |
|
B. |
Disable autonegotiation |
|
C. |
Disable Cisco
Discovery Protocol on the interface |
|
D. |
Enable LLDP-MED on the ISP
device |
Answer: A
Explanation:
LDDP-MED is used only between
network devices (such
as switches) and endpoint devices (such as phones). For network-to-network connections, LLDP is used.
Check table 2, protocol uses: https://www.cisco.com/en/US/technologies/tk652/tk701/technologies_white_paper0900aecd804c d46d.html
What is the benefit of configuring PortFast on an interface?
|
A. |
After the cable
is connected, the interface uses
the fastest speed
setting available for
that cable type |
|
B. |
After the
cable is connected, the interface is available faster
to send and
receive user data |
|
C. |
The frames
entering the interface are marked with
higher priority and
then processed faster
by a switch. |
|
D. |
Real-time voice and video frames
entering the interface are processed faster |
Answer: B
Explanation:
Portfast causes a switch or trunk port to enter the spanning tree forwarding state immediately, bypassing the listening and learning states.
Drag and Drop Question
Drag and drop the DNS lookup components from the left onto the functions on the right.
![]()
Answer:
![]()
Drag and Drop Question
Drag and drop the statement about networking from the left into the Corresponding networking types on the right. Not all statements are used.
![]()
Answer:
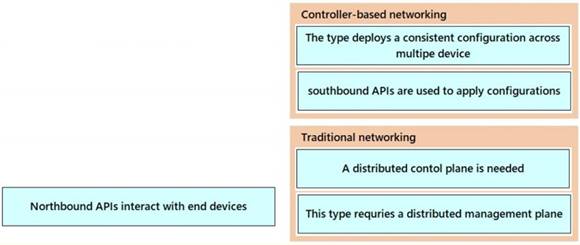
Explanation:
On a SND network the control plane is centralized on the the SND controller not distributed on the networking devices.
Northbound APIs do not interact with end devices. They allow the SND controller to interact with applications on the application plane.
On a SND network the management plane is not centralized, it is distributed. Network management protocols, such as Telnet, SSH, SNMP, and Syslog operate in the management plane on both traditional network and controller-based network.
Drag and Drop Question
Drag and drop the IPv6 address type characteristics from the left to the right.
![]()
Answer:
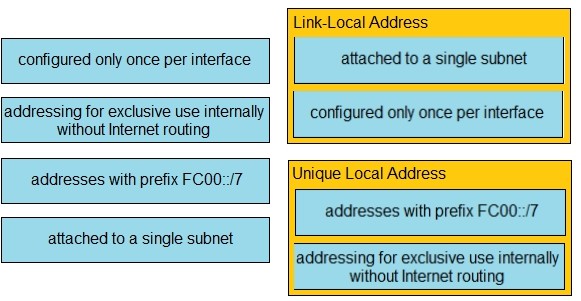
Explanation:
“A link-local address is a unicast address that is confined to a single link, a single subnet.” “There can be only one link-local address per interface.”
“ULA addresses are for devices that never need access to the Internet and never need to be accessible from the Internet.” https://www.ciscopress.com/articles/article.asp?p=2803866&seqNum=4
Refer to the exhibit. Between which zones do wireless users expect to experience intermittent connectivity?
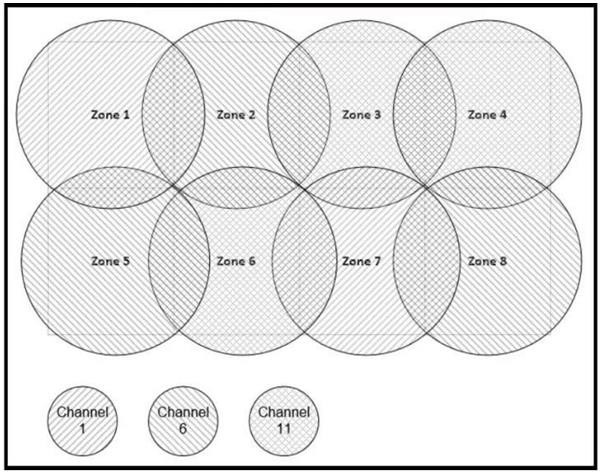
|
A. |
between zones
1 and 2 |
|
B. |
between
zones 2 and 5 |
|
C. |
between
zones 3 and 4 |
|
D. |
between zones
3 and 6 |
Answer: C
Explanation:
Zones 3 and 4 both have Channel 11 that is overlapped. Zones 3 and 6 do not overlap at all.
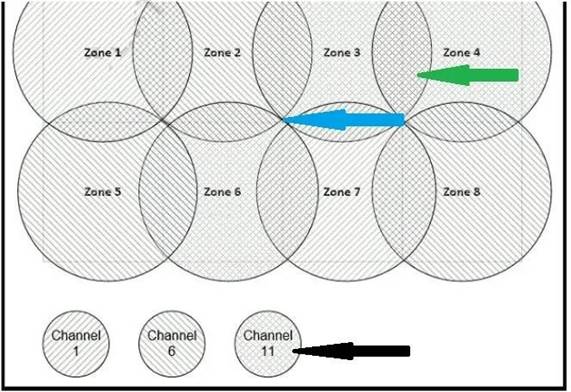
Refer to the exhibit. A network engineer is in the process of establishing IP connectivity between two sites.
Routers R1 and R2 are partially configured with IP addressing.
Both routers have the ability to access devices on their respective LANs.
Which command set configures the IP connectivity between devices located on both LANs in each site?
![]()
|
A. |
R1 ip route
192.168.1.1 255.255.255.0 GigabitEthernet0/1 R2 ip route 10.1.1.1 255.255.255.0
GigabitEthernet0/1 |
|
B. |
R1 ip route 192.168.1.0 255.255.255.0
GigabitEthernet0/0 R2 ip route
10.1.1.1 255.255.255.0 GigabitEthernet0/0 |
|
C. |
R1 ip route 0.0.0.0 0.0.0.0 209.165.200.225 R2 ip route 0.0.0.0
0.0.0.0 209.165.200.226 |
|
D. |
R1 ip route 0.0.0.0
0.0.0.0 209.165.200.226 R2 ip route 0.0.0.0
0.0.0.0 209.165.200.225 |
Answer: D
Explanation:
D is correct as it is stating any route goes through next hop of 2019.165.200.226 (on R1) while any route next hops to 209.165.200.225 (On R2).
Refer to the exhibit. Which IPv6 configuration is required for R17 to successfully ping the WAN interface on R18?
![]()
|
A. |
|
|
B. |
|
|
C. |
|
|
D. |
|
Answer: B
Explanation:
ipv6 unicast-routing statement included (IPv6 is enabled on the router). Compared to the exhibit, Fa0/0 and Fa0/1 have correct configurations. The route to subnet 2001:db8:4::/64 points to R18's Fa1/0 (correct next-hop).
Which type of organization should use a collapsed-core architecture?
|
A. |
large and requires a flexible, scalable network design |
|
B. |
large and must minimize downtime when hardware fails |
|
C. |
small and
needs to reduce
networking costs currently |
|
D. |
small but is expected to grow dramatically in the near
future |
Answer: C
Explanation:
A collapsed-core architecture is a limited investment for a small company, and may be efficient and productive for a limited time.
What is a capability of FTP in network management operations?
|
A. |
encrypts data before
sending between data resources |
|
B. |
devices are
directly connected and
use UDP to pass file
information |
|
C. |
uses separate control and data connections to move files
between server and client |
|
D. |
offers proprietary support at the session layer when transferring data |
Answer: C
Explanation:
The File Transfer Protocol (FTP) is a standard communication protocol used for the transfer of computer files from a server to a client on a computer network. FTP is built on a client - server model architecture using separate control and data connections between the client and the server.
Refer to the exhibit. For security reasons, automatic neighbor discovery must be disabled on the R5 Gi0/1 interface.
![]()
These tasks must be completed:
- Disable all neighbor
discovery methods on R5 interface
Gi0/1.
- Permit neighbor discovery
on R5's interface
Gi0/2.
- Verify there are no dynamically learned neighbors on R5 interface Gi0/1.
- Display the IP address of R6's interface Gi0/2.
Which configuration must be used?
|
A. |
R5(config)#int
Gi0/1 R5(config-if)#no cdp enable R5(config-if)#exit
R5(config)#lldp run R5(config)#no cdp run R5#sh cdp neighbor detail R5#sh lldp neighbor |
|
B. |
R5(config)#int
Gi0/1 R5(config-if)#no cdp enable R5(config-if)#exit
R5(config)#no lldp run R5(config)#cdp run R5#sh cdp neighbor R5#sh lldp neighbor |
|
C. |
R5(config)#int
Gi0/1 R5(config-if)#no cdp run R5(config-if)#exit
R5(config)#lldp run R5(config)#cdp enable R5#sh cdp neighbor R5#sh lldp neighbor |
|
D. |
R5(config)#int
Gi0/1 R5(config-if)#no cdp enable R5(config-if)#exit
R5(config)#no lldp run R5(config)#cdp run R5#sh cdp neighbor detail R5#sh lldp neighbor |
Answer: B
What is a function of a Layer 3 switch?
|
A. |
move frames between endpoints limited to IP addresses |
|
B. |
transmit broadcast traffic when operating in Layer 3 mode exclusively |
|
C. |
forward Ethernet frames between VLANs
using only MAC addresses |
|
D. |
flood broadcast traffic
within a VLAN |
Answer:
A
Which type of API allows SDN controllers to dynamically make changes to the network?
|
A. |
northbound API |
|
B. |
REST API |
|
C. |
SOAP API |
|
D. |
southbound API |
Answer: D
Explanation:
https://www.cisco.com/c/en/us/td/docs/solutions/Enterprise/Data_Center/VMDC/SDN/SDN.html
Drag and Drop Question
Drag and drop the lightweight access point operation modes from the left onto the descriptions on the right.
![]()
Answer:

Which protocol is used in Software Defined Access (SDA) to provide a tunnel between two edge nodes in different fabrics?
|
A. |
Generic Router Encapsulation (GRE) |
|
B. |
Virtual Local
Area Network (VLAN) |
|
C. |
Virtual Extensible LAN (VXLAN) |
|
D. |
Point-to-Point Protocol (PPP) |
Answer: C
Explanation:
The SD(Cisco® Software-Defined Access)-Access fabric uses the VXLAN data plane to provide transport of the full original Layer 2 frame and additionally uses LISP as the control plane to resolve endpoint-to-location (EID-to-RLOC) mappings. The SD-Access fabric replaces sixteen
(16) of the reserved bits in the VXLAN header to transport up to 64,000 SGTs using a modified VXLAN-GPO (sometimes called VXLAN-GBP) format described in https://tools.ietf.org/html/draft- smith-vxlan-group-policy-04.
Which plane is centralized by an SDN controller?
|
A. |
management-plane |
|
B. |
data-plane |
|
C. |
services-plane |
|
D. |
control-plane |
Answer: D
Refer to the exhibit. Which next-hop IP address does Router1 use for packets destined to host 10.10.13.158?
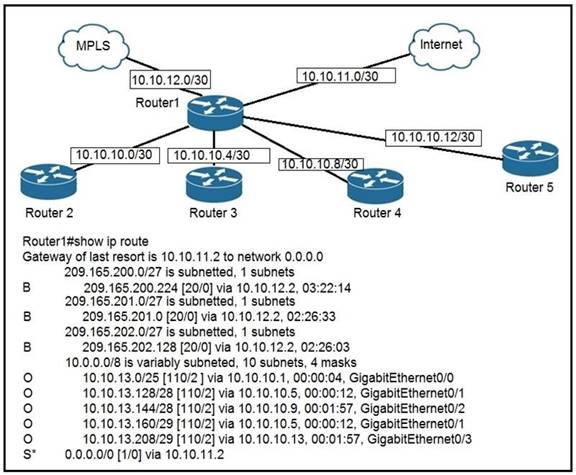
|
A. |
10.10.10.5 |
|
B. |
10.10.11.2 |
|
C. |
10.10.12.2 |
|
D. |
10.10.10.9 |
Answer: D
A Cisco engineer must configure a single switch interface to meet these requirements:
- accept untagged frames
and place them in VLAN 20
- accept tagged frames in VLAN 30 when CDP detects
a Cisco IP phone
Which command set must the engineer apply?
|
A. |
switchport mode
dynamic desirable switchport
access vlan 20 switchport trunk allowed vlan 30 switchport voice
vlan 30 |
|
B. |
switchport mode
dynamic auto switchport trunk
native vlan 20 |
|
|
switchport trunk allowed vlan 30 switchport voice
vlan 30 |
|
C. |
switchport
mode access switchport access vlan
20 switchport voice vlan 30 |
|
D. |
switchport
mode trunk switchport access vlan
20 switchport voice vlan 30 |
Answer: C
Refer to the exhibit. An engineer is configuring the HO router.
Which IPv6 address configuration must be applied to the router fa0/1 interface for the router to assign a unique 64-brt IPv6 address to Itself?
![]()
|
A. |
ipv6 address
2001:DB8:0:1:C601:42FF:FE0F:7/64 |
|
B. |
ipv6 address
2001:DB8:0:1:C601:42FE:800F:7/64 |
|
C. |
ipv6 address
2001:DB8:0:1:FFFF:C601:420F:7/64 |
|
D. |
ipv6 address 2001:DB8:0:1:FE80:C601:420F:7/64 |
Answer:
A
Which WLC management connection type is vulnerable to man-in-the-middle attacks?
|
A. |
SSH |
|
B. |
HTTPS |
|
C. |
Telnet |
|
D. |
console |
Answer: C
Which action is taken by the data plane within a network device?
|
A. |
forwards traffic to the next
hop |
|
B. |
constructs a routing table
based on a routing protocol |
|
C. |
provides CLI access to the network device |
|
D. |
looks up an egress interface in the forwarding information base |
Answer:
A
What is a function of a Next-Generation IPS?
|
A. |
makes forwarding decisions based on learned
MAC addresses |
|
B. |
serves as a controller within a controller-based network |
|
C. |
integrates with
a RADIUS server
to enforce Layer
2 device authentication rules |
|
D. |
correlates user activity with network events |
Answer: D
Which characteristic differentiates the concept of authentication from authorization and accounting?
|
A. |
user-activity logging |
|
B. |
service limitations |
|
C. |
consumption-based billing |
|
D. |
identity verification |
Answer: D
Which value is the unique identifier that an access point uses to establish and maintain wireless connectivity to wireless network devices?
|
A. |
VLANID |
|
B. |
SSID |
|
C. |
RFID |
|
D. |
WLANID |
Answer:
B
An engineer is configuring remote access to a router from IP subnet 10.139.58.0/28. The domain name, crypto keys, and SSH have been configured.
Which configuration enables the traffic on the destination router?
|
A. |
|
|
B. |
|
|
C. |
|
|
D. |
|
Answer:
B
Which QoS per-hop behavior changes the value of the ToS field in the IPv4 packet header?
|
A. |
shaping |
|
B. |
classification |
|
C. |
policing |
|
D. |
marking |
Answer: D
Refer to the exhibit. Which route must be configured on R1 so that OSPF routing is used when OSPF is up, but the server is still reachable when OSPF goes down?
![]()
|
A. |
ip route 10.1.1.10 255.255.255.255 172.16.2.2 100 |
|
B. |
ip route 10.1.1.0 255.255.255.0 gi0/1 125 |
|
C. |
ip route 10.1.1.0 255.255.255.0 172.16.2.2 100 |
|
D. |
ip route 10.1.1.10 255.255.255.255 gi0/0 125 |
Answer: D
Explanation:
This is an example of a floating static route when the Administrative Distance must be greater than the primary route. Currently the OSPF AD for the route is 110, so if that route was to go away then this route with an AD of 125 would be used.
Refer to the exhibit. Users need to connect to the wireless network with IEEE 802. 11r-compatible devices. The connection must be maintained as users travel between floors or to other areas in
the building. What must be the configuration of the connection?
![]()
|
A. |
Select the WPA
Policy option with
the CCKM option. |
|
B. |
Disable AES encryption. |
|
C. |
Enable Fast Transition and select the FT 802.1x
option. |
|
D. |
Enable Fast Transition and select the FT PSK option. |
Answer: C
Refer to the exhibit. What is a reason for poor performance on the network interface?
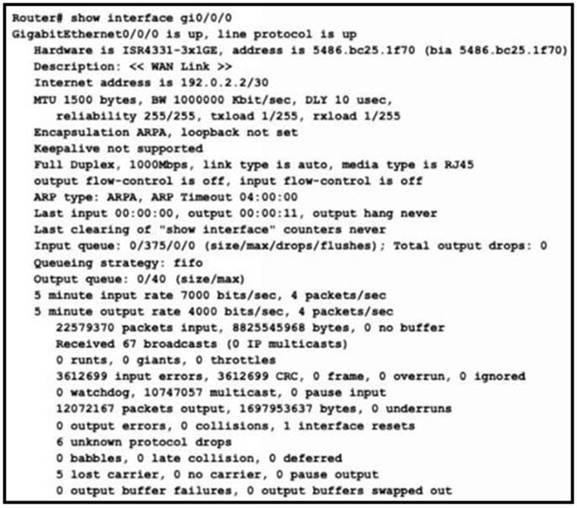
|
A. |
The interface is receiving excessive broadcast traffic. |
|
B. |
The cable connection between
the two devices is faulty. |
|
C. |
The interface is operating at a different speed than the connected device. |
|
D. |
The bandwidth setting of the interface is misconfigured |
Answer: B
Explanation:
Here we see a large number of input errors and CRC errors.
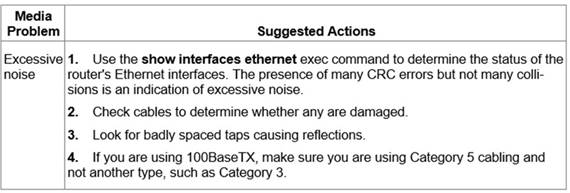
Refer to the exhibit. A network engineer must update the configuration on Switch2 so that it sends LLDP packets every minute and the information sent via LLDP is refreshed every 3 minutes.
Which configuration must the engineer apply?
![]()
|
A. |
Switch2(config)#lldp timer 60 Switch2(config)#lldp holdtime 180 |
|
B. |
Switch2(config)#lldp timer
60 Switch2(config)#lldp tlv-select 180 |
|
C. |
Switch2(config)#lldp timer
1 Switch2(config)#lldp holdtime 3 |
|
D. |
Switch2(config)#lldp timer 1 Switch2(config)#lldp tlv-select 3 |
Answer: A
Explanation:
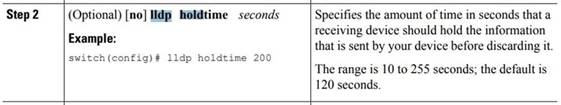
Reference: https://www.cisco.com/c/en/us/td/docs/switches/datacenter/nexus9000/sw/6- x/system_management/configuration/guide/ b_Cisco_Nexus_9000_Series_NX- OS_System_Management_Configuration_Guide/sm_lldp.pdf
Refer to the exhibit. Users on existing VLAN 100 can reach sites on the Internet. Which action must the administrator take to establish connectivity to the Internet for users in VLAN 200?
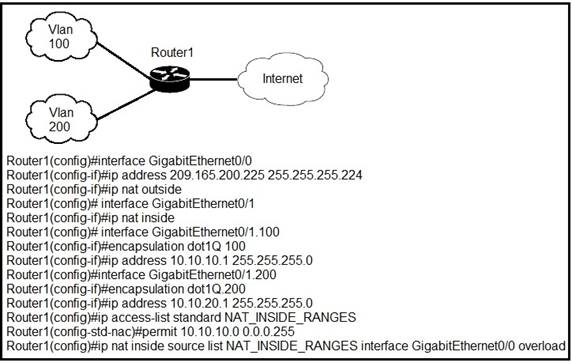
|
A. |
Define a NAT pool on the router. |
|
B. |
Configure static
NAT translations for
VLAN 200. |
|
C. |
Configure the ip nat outside command on another interface for VLAN 200. |
|
D. |
Update the NAT_INSIDE_RANGES ACL. |
Answer: D
Explanation:
ip nat inside source list NAT_INSIDE_RANGES interfaces G0/0 Overload
This command essentially tells the router all ip addresses specified from the access list "NAT_INSIDE_RANGES" will be translated via port address translation (PAT) using the ip address of G0/0.
By reconfiguring the ACL to include the 200 vlan it will provide the easiest way to get VLAN 200 access to the internet.
Refer to the exhibit. Packets received by the router from BGP enter via a serial interface at 209.165.201.1. Each route is present within the routing table.
Which interface is used to forward traffic with a destination IP of 10.1.1.19?
![]()
|
A. |
F0/4 |
|
B. |
F0/0 |
|
C. |
F0/1 |
|
D. |
F0/3 |
Answer:
B
Refer to the exhibit. An engineer is configuring an EtherChannel using LACP between Switches 1 and 2. Which configuration must be applied so that only Switch 1 sends LACP initiation packets?
![]()
|
A. |
Switch1(config-if)#channel-group 1 mode on Swrtch2(config-if)#channel-group 1 mode passive |
|
B. |
Switch1(config-if)#channel-group 1 mode passive
Switch2(config-if)#channel-group 1 mode active |
|
C. |
Switch1(config-if)#channel-group 1 mode active
Switch2(config-if)#channel-group 1 mode
passive |
|
D. |
Switch1(config-if)#channel-group
1 mode on Switch2(config-if)#channel-group
1 mode active |
Answer: C
Refer to the exhibit. R1 learns all routes via OSPF. Which command configures a backup static route on R1 to reach the 192.168.20.0/24 network via R3?
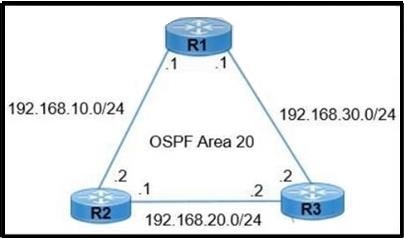
|
A. |
R1(config)#ip route 192.168.20.0 255.255.0.0 192.168.30.2 |
|
B. |
R1(config)#ip route
192.168.20.0 255.255.255.0 192.168.30.2 90 |
|
C. |
R1(config)#ip route
192.168.20.0 255.255.255.0 192.168.30.2 111 |
|
D. |
R1(config)#ip route 192.168.20.0 255.255.255.0 192.168.30.2 |
Answer: C
What is the difference between IPv6 unicast and anycast addressing?
|
A. |
IPv6 anycast nodes
must be explicitly configured to recognize the anycast address, but IPv6 unicast nodes
require no special
configuration |
|
B. |
IPv6 unicast nodes
must be explicitly configured to recognize the unicast address, but IPv6 anycast
nodes require no special configuration |
|
C. |
An individual IPv6 unicast address is supported on a single
interface on one node but an IPv6 anycast address is assigned to a
group of interfaces on multiple nodes. |
|
D. |
Unlike an IPv6 anycast address, an IPv6 unicast address is assigned to a group
of interfaces on multiple nodes |
Answer: C
Refer to the exhibit. The router has been configured with a super net to accommodate the requirements for 380 users on a Subnet. The requirement already considers 30% future growth. Which configuration verifies the IP subnet on router R4?
![]()
|
A. |
Subnet:
10.7.54.0 Subnet mask: 255.255.128.0 Broadcast address: 10.5.55.255 |
|
|
Usable IP address range: 10.7.54.1 -
10.7.55.254 |
|
B. |
Subnet: 10.7.54.0 Subnet mask:
255.255.255.0 Broadcast address: 10.7.54.255 Usable IP address range:
10.7.54.1 - 10.7.55.254 |
|
C. |
Subnet: 10.7.54.0 Subnet mask: 255.255.254.0 Broadcast address: 10.7.54.255 Usable IP address range:
10.7.54.1 - 10.7.55 |
|
D. |
Subnet: 10.7.54.0 Subnet mask: 255.255.254.0 Broadcast address: 10.7.55.255 Usable IP address range: 10.7.54.1 -
10.7.55 |
Answer: D
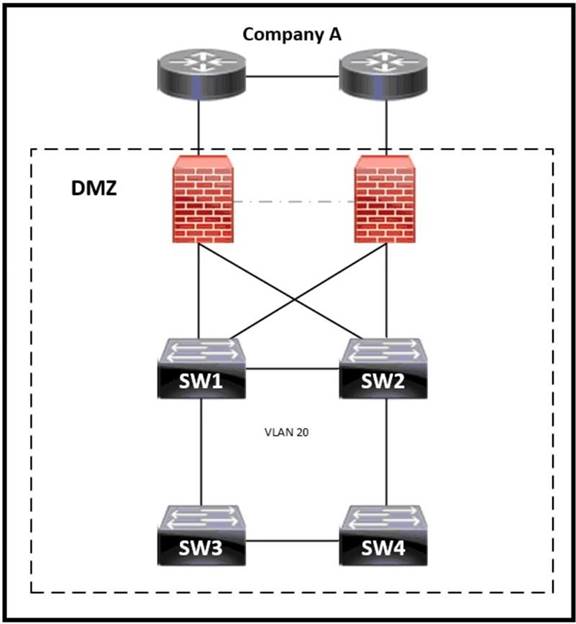
![]()
|
A. |
SW1 |
|
B. |
SW2 |
|
C. |
SW3 |
|
D. |
SW4 |
Answer: A
Which protocol uses the SSL?
|
A. |
HTTP |
|
B. |
SSH |
|
C. |
HTTPS |
|
D. |
Telnet |
Answer: C
Explanation:
HTTPS (port 443, TCP): HTTPS combines HTTP with a security protocol (Secure Sockets Layer [SSL]/Transport Layer Security[TLS]). DNS (port 53, TCP, and UDP): DNS is used to resolve Internet names to IP addresses.
Which two spanning-tree states are bypassed on an interface running PortFast? (Choose two.)
|
A. |
disabled |
|
B. |
listening |
|
C. |
forwarding |
|
D. |
learning |
|
E. |
blocking |
Answer: BD
A Cisco engineer is configuring a factory-default router with these three passwords:
- The user EXEC password for console access
is p4ssw0rd1
- The user EXEC password for Telnet access
is s3cr3t2
- The password for privileged EXEC mode is pnv4t3p4ss
Which command sequence must the engineer configured?
|
A. |
enable secret priv4t3p4ss ! line con 0 password p4ssw0rd1 ! line vty 0
15 password s3cr3t2 |
|
B. |
enable secret
priv4t3p4ss ! line con 0 password p4ssw0rd1 login ! line vty 0 15 password s3cr3t2 login |
|
C. |
enable secret priv4t3p4ss ! |
|
|
line con 0 password login p4ssw0rd1 ! line vty 0 15 password login s3cr3t2 login |
|
D. |
enable secret privilege 15 priv4t3p4ss ! line con 0 password p4ssw0rd1 login ! line vty 0 15 password s3cr3t2 login |
Answer: D
How does Rapid PVST+ create a fast loop-free network topology?
|
A. |
lt requires multiple links between core
switches |
|
B. |
It generates one spanning-tree instance for each
VLAN |
|
C. |
It maps multiple VLANs
into the same
spanning-tree instance |
|
D. |
It uses multiple active paths between
end stations. |
Answer:
B
Refer to the exhibit. The link between PC1 and the switch is up, but it is performing poorly. Which interface condition is causing the performance problem?
![]()
|
A. |
There is a duplex mismatch on the interface |
|
B. |
There is an issue with the fiber
on the switch
interface. |
|
C. |
There is a speed
mismatch on the
interface. |
|
D. |
There is an interface type
mismatch |
Answer: A
Explanation:
The PC's port runs in full duplex, while the Fa0/1 port on the switch is in auto-negotiate mode. This results in a duplex mismatch that causes the switchport to operate as half-duplex, which culminates in poor performance on the link.
"A duplex mismatch occurs when two connected devices are configured in different duplex modes.
This may happen, for example, if one is configured for autonegotiation while the other one has a fixed mode of operation that is full duplex (no autonegotiation). In such conditions, the autonegotiation device correctly detects the speed of operation, but is unable to correctly detect the duplex mode.
As a result, it sets the correct speed but assumes half-duplex mode.
When a device is operating in full duplex while the other one operates in half duplex, the connection works reliably only at a very low throughput."
Reference: https://en.wikipedia.org/wiki/Autonegotiation#Duplex_mismatch
Which PoE mode enables powered-device detection and guarantees power when the device is detected?
|
A. |
dynamic |
|
B. |
static |
|
C. |
active |
|
D. |
auto |
Answer:
B
What is an expected outcome when network management automation is deployed?
|
A. |
A distributed management plane must be used. |
|
B. |
Software upgrades are performed from
a central controller |
|
C. |
Complexity increases when new device
configurations are added |
|
D. |
Custom applications are needed to configure network
devices |
Answer:
B
Refer to the exhibit. Which action must be taken to ensure that router A is elected as the DR for OSPF area 0?
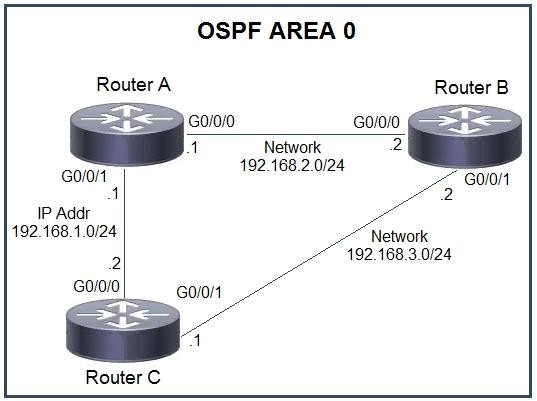
|
A. |
Configure the OSPF priority on router A with the
lowest value between the three routers. |
|
B. |
Configure
router B and router C as OSPF
neighbors of router
A. |
|
C. |
Configure the router A interfaces with
the highest OSPF
priority value within
the area. |
|
D. |
Configure router A with a fixed OSPF
router ID |
Answer: C
Refer to the exhibit. Web traffic is coming in from the WAN interface. Which route takes precedence when the router is processing traffic destined for the LAN network at 10 0.10.0/24?
![]()
|
A. |
via next-hop 10.0.1.5 |
|
B. |
via next-hop 10 0 1.4 |
|
C. |
via next-hop 10.0 1.50 |
|
D. |
via next-hop 10.0
1 100 |
Answer: A
Which two components comprise part of a PKI? (Choose two.)
|
A. |
preshared key that
authenticates connections |
|
B. |
RSA token |
|
C. |
CA that grants certificates |
|
D. |
clear-text password that authenticates connections |
|
E. |
one or more
CRLs |
Answer: BC
What are two benefits of FHRPs? (Choose two.)
|
A. |
They enable automatic failover of the default gateway. |
|
B. |
They allow
multiple devices to serve as a single
virtual gateway for clients in the network. |
|
C. |
They are
able to bundle
multiple ports to increase bandwidth. |
|
D. |
They prevent loops in the Layer 2
network. |
|
E. |
They allow encrypted traffic. |
Answer:
AB
Refer to the exhibit. Which command configures OSPF on the point-to-point link between routers R1 and R2?
![]()
|
A. |
router-id 10.0.0.15 |
|
B. |
neighbor 10.1.2.0 cost 180 |
|
C. |
ipospf priority 100 |
|
D. |
network 10.0.0.0 0.0.0.255 area 0 |
Answer: D
What causes a port to be placed in the err-disabled state?
|
A. |
nothing plugged into
the port |
|
B. |
link flapping |
|
C. |
shutdown command issued on the port |
|
D. |
latency |
Answer: B
Explanation:
The Errdisable error disable feature was designed to inform the administrator when there is a port problem or error. The reasons a catalyst switch can go into Errdisable mode and shutdown a port are many and include:
Duplex Mismatch Loopback Error
Link Flapping (up/down) Port Security Violation Unicast Flodding
UDLD Failure Broadcast Storms BPDU Guard
Refer to the exhibit. An engineer is configuring a new router on the network and applied this configuration. Which additional configuration allows the PC to obtain its IP address from a DHCP server?
![]()
|
A. |
Configure the ip dhcp relay
information command under
interface Gi0/1. |
|
B. |
Configure the ip dhcp
smart-relay command globally on the router |
|
C. |
Configure the ip helper-address 172.16.2.2 command under
interface Gi0/0 |
|
D. |
Configure the ip address dhcp
command under interface Gi0/0 |
Answer: C
Which Layer 2 switch function encapsulates packets for different VLANs so that the packets traverse the same port and maintain traffic separation between the VLANs?
|
A. |
VLAN numbering |
|
B. |
VLAN DSCP |
|
C. |
VLAN tagging |
|
D. |
VLAN marking |
Answer: C
Refer to the exhibit. The following must be considered:
- SW1 is fully configured for all traffic
- The SW4 and SW9 links to SW1 have been configured
- The SW4 interface
Gi0/1 and Gi0/0 on SW9 have been configured
- The remaining switches
have had all VLANs added to their VLAN
database
Which configuration establishes a successful ping from PC2 to PC7 without interruption to traffic flow between other PCs?
![]()
|
A. |
SW4 interface
Gi0/7 switchport mode trunk switchport trunk allowed
vlan 108 ! interface
Gi/0/2 switchport mode access
switchport access vlan
14 SW11# interface
Gi0/2 switchport mode trunk switchport trunk allowed
vlan 14,108 ! interface
Gi0/1 switchport mode trunk switchport trunk allowed
vlan 14,108 SW9# interface
Gi0/2 switchport mode access switchport
access vlan 14 |
|
B. |
SW4 interface
Gi0/2 switchport mode trunk switchport trunk allowed
vlan 14,108 SW11# interface
Gi0/2 switchport mode trunk switchport trunk
allowed vlan 14,108 !! interface
Gi0/1 switchport mode trunk switchport trunk
allowed vlan 14,108 SW9# interface
Gi0/2 switchport mode trunk switchport
trunk allowed vlan
14 |
|
C. |
SW4 interface
Gi0/2 switchport mode trunk switchport trunk
allowed vlan 14 SW11# interface
Gi0/1 switchport mode trunk switchport trunk allowed
vlan 14 SW9# interface
Gi0/2 switchport mode trunk switchport
trunk allowed vlan
108 |
|
D. |
SW4 |
interface
Gi/0/2 switchport mode access
switchport access vlan 14
SW11#
interface
Gi0/2 switchport mode trunk
switchport trunk allowed vlan 14
!
interface
Gi0/0 switchport mode access
switchport access vlan 14
!
interface
Gi0/1 switchport mode trunk
SW9#
interface
Gi0/2 switchport mode access
switchport access
vlan 14 Answer: B
R1 as an NTP server must have:
- NTP authentication enabled
- NTP packets sourced
from Interface loopback
0
- NTP stratum 2
- NTP packets only permitted to client IP 209.165.200.225
How should R1 be configured?
|
A. |
ntp authenticate ntp authentication-key 2 sha1 CISCO123 ntp source Loopback0 ntp access-group server-only 10 ntp
master 2 ! access-list
10 permit udp host 209.165.200.225 any eq 123 |
|
B. |
ntp authenticate ntp authentication-key 2 md5 CISCO123 ntp interface Loopback0 ntp access-group server-only 10 ntp
stratum 2 ! access-list
10 permit 209.165.200.225 |
|
C. |
ntp authenticate ntp authentication-key 2 md5 CISCO123 ntp source Loopback0 ntp access-group server-only 10 ntp
master 2 ! access-list 10 permit
209.165.200.225 |
|
D. |
ntp authenticate ntp authentication-key 2 md5 CISCO123 ntp source Loopback0 ntp access-group server-only 10 ntp
stratum 2 ! access-list 10 permit
udp host 209.165.200.225 any eq 123 |
Answer: C
Refer to the exhibit. Which two configurations must the engineer apply on this network so that R1 becomes the DR? (Choose two.)
![]()
|
A. |
R3(config)#interface fastethernet 0/0 R3(config-if)#ip ospf priority 0 |
|
B. |
R1(config)#router ospf 1 R1(config-router)#router-id
192.168.100.1 |
|
C. |
R1(config)#interface
fastethernet 0/0 R1(config-if)#ip ospf priority 200 |
|
D. |
R1(config)#interface fastethernet 0/0 R1(config-if)#ip ospf priority 0 |
|
E. |
R3(config)#interface
fastethernet 0/0 R3(config-if)#ip ospf priority 200 |
Answer:
AC
Explanation:
R1 must have the Highest priority, and thus R3 a low or lowest Priority.
Which type of IPv6 address is similar to a unicast address but is assigned to multiple devices on the same network at the same time?
|
A. |
global unicast address |
|
B. |
anycast address |
|
C. |
multicast address |
|
D. |
link-local address |
Answer: B
Explanation:
An IPv6 anycast address is any IPv6 unicast address that can be assigned to multiple devices.
Which two network actions occur within the data plane? (Choose two.)
|
A. |
Add or remove
an 802.1Q trunking header. |
|
B. |
Make a configuration change
from an incoming NETCONF RPC. |
|
C. |
Run routing protocols. |
|
D. |
Match the destination MAC address to the MAC
address table. |
|
E. |
Reply to an incoming ICMP
echo request. |
Answer: AD
Explanation:
Data Plane:
- De-encapsulating and re-encapsulating a packet in a data-link
frame (routers, Layer 3 switches)
- Adding or removing an 802.1Q trunking
header (routers and switches)
-
Matching an Ethernet
frame’s destination Media
Access Control (MAC)
address to the MAC
address table (Layer 2 switches)
-
Matching an IP packet’s destination IP address to the IP routing table
(routers, Layer 3 switches)
-
Encrypting the data and adding
a new IP header (for virtual private
network [VPN] processing)
-
Changing the source or destination IP address (for Network Address
Translation [NAT] processing)
- Discarding a message due to a filter (access
control lists [ACLs],
port security)
Which QoS traffic handling technique retains excess packets in a queue and reschedules these packets for later transmission when the configured maximum bandwidth has been surpassed?
|
A. |
weighted random early
detection |
|
B. |
traffic policing |
|
C. |
traffic shaping |
|
D. |
traffic prioritization |
Answer: C
Explanation:
Policing drops or remarks traffic that exceeds limits, but shaping regulates the traffic back to a defined rate by delaying or queuing the traffic.
Refer to the exhibit. All traffic enters the CPE router from interface Serial0/3 with an IP address of 192.168.50.1. Web traffic from the WAN is destined for a LAN network where servers are load- balanced. An IP packet with a destination address of the HTTP virtual IP of 192.168.1.250 must
be forwarded. Which routing table entry does the router use?
![]()
|
A. |
192.168.1.0/24
via 192.168.12.2 |
|
B. |
192.168.1.128/25 via
192.168.13.3 |
|
C. |
192.168.1.192/26 via
192.168.14.4 |
|
D. |
192.168.1.224/27 via 192.168.15.5 |
Answer: D
Explanation:
Longest Prefix route inclusive of the IP Address. /27 = 32, which is inclusive in this case.
Which interface mode must be configured to connect the lightweight APs in a centralized architecture?
|
A. |
WLAN dynamic |
|
B. |
management |
|
C. |
trunk |
|
D. |
access |
Answer: D
Explanation:
While the Cisco WLCs always connect to 802.1Q trunks, Cisco lightweight APs do not understand VLAN tagging and should only be connected to the access ports of the neighbor switch.
This is an example switch port configuration from the Catalyst 3750: interface GigabitEthernet1/0/22 description Access Port Connection to Cisco Lightweight AP switchport access vlan 5 switchport mode access no shutdown
Reference:
https://www.cisco.com/c/en/us/support/docs/wireless/4400-series-wireless-lan-controllers/69719- wlc-lwap-config.html
Refer to the exhibit. Which two commands must be configured on router R1 to enable the router to accept secure remote-access connections? (Choose two)
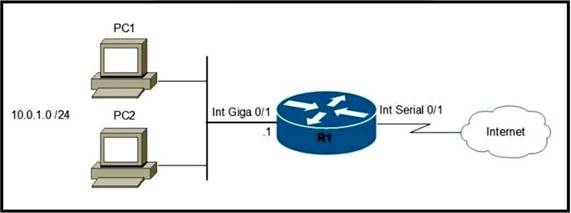
|
A. |
transport input telnet |
|
B. |
crypto key
generate rsa |
|
C. |
ip ssh pubkey-chain |
|
D. |
login console |
|
E. |
username cisco password 0 Cisco |
Answer: BE
Which type of network attack overwhelms the target server by sending multiple packets to a port until the half-open TCP resources of the target are exhausted?
|
A. |
SYIM flood |
|
B. |
reflection |
|
C. |
teardrop |
|
D. |
amplification |
Answer:
A
Refer to the exhibit. An engineer assumes a configuration task from a peer. Router A must establish an OSPF neighbor relationship with neighbor 172.1.1.1. The output displays the status of the adjacency after 2 hours.
What is the next step in the configuration process for the routers to establish an adjacency?
![]()
|
A. |
Configure router A to use the same
MTU size as router
B. |
|
B. |
Set the router B OSPF ID to a nonhost address. |
|
C. |
Configure a point-to-point link
between router A and router
B. |
|
D. |
Set the router
B OSPF ID to the same value
as its IP
address |
Answer: A
Explanation:
In Exstart/Exchange State, when attempting to run OSPF between a Cisco router and another vendor's router. If the router with the higher MTU sends a packet larger that the MTU set on the neighboring router, the neighboring router ignores the packet.
Refer to the exhibit. Routers R1 and R3 have the default configuration. The router R2 priority is set to 99.
Which commands on R3 configure it as the DR in the 10.0 4.0/24 network?
![]()
|
A. |
R3(config)#interface Gig0/1 R3(config-if)#ip ospf
priority 100 |
|
B. |
R3(config)#interface
Gig0/0 R3(config-if)#ip ospf priority 100 |
|
C. |
R3(config)#interface
Gig0/0 R3(config-if)#ip ospf priority 1 |
|
D. |
R3(config)#interface Gig0/1 R3(config-if)#ip ospf
priority 0 |
Answer: A
Explanation:
In the case of OSPF, 0 means you will never be elected as DR or BDR. Default priority is 1. Highest priority will be elected as the DR.
Refer to the exhibit. A company is configuring a failover plan and must implement the default routes in such a way that a floating static route will assume traffic forwarding when the primary link goes down. Which primary route configuration must be used?
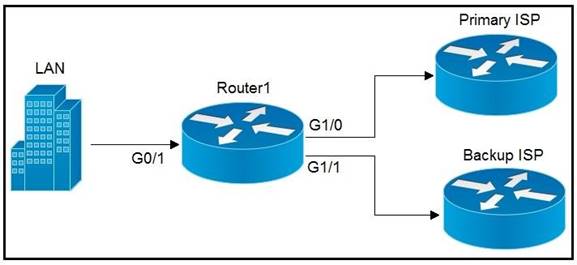
|
A. |
ip route 0.0.0.0
0.0.0.0 192.168.0.2 GigabitEthernetl/0 |
|
B. |
ip route 0.0.0.0 0.0.0.0 192.168.0.2 tracked |
|
C. |
ip route 0.0.0.0 0.0.0.0 192.168.0.2 floating |
|
D. |
ip route 0.0.0.0
0.0.0.0 192.168.0.2 |
Answer: D
Explanation:
The primary route should use the default administrative distance, since the AD for static routes is 1.
What is one reason to implement LAG on a Cisco WLC?
|
A. |
to increase security and encrypt management frames |
|
B. |
to provide link redundancy and load balancing |
|
C. |
to allow for stateful and link-state failover |
|
D. |
to enable connected switch ports to failover and use different VLANs |
Answer:
B
Which action implements physical access control as part of the security program of an organization?
|
A. |
configuring a password for the console port |
|
B. |
backing up syslogs at a remote
location |
|
C. |
configuring enable
passwords on network devices |
|
D. |
setting up IP cameras to monitor key
infrastructure |
Answer:
A
Refer to the exhibit. An engineer is asked to insert the new VLAN into the existing trunk without
modifying anything previously configured. Which command accomplishes this task?
![]()
|
A. |
switchport trunk allowed vlan 100-104 |
|
B. |
switchport trunk
allowed vlan add 104 |
|
C. |
switchport trunk
allowed vlan all |
|
D. |
switchport trunk allowed vlan 104 |
Answer:
B
Which field within the access-request packet is encrypted by RADIUS?
|
A. |
authorized services |
|
B. |
authenticator |
|
C. |
username |
|
D. |
password |
Answer: D
Explanation:
RADIUS by itself provides no encryption of all traffic. It protects only a small part of the traffic, notably the passwords.
A network administrator is setting up a new IPv6 network using the 64-bit address 2001:0EB8:00C1:2200:0001:0000:0000:0331/64. To simplify the configuration, the administrator has decided to compress the address. Which IP address must the administrator configure?
|
A. |
ipv6 address 21:EB8:C1:2200:1::331/64 |
|
B. |
ipv6 address
2001:EB8:C1:22:1::331/64 |
|
C. |
ipv6 address
2001:EB8:C1:2200:1::331/64 |
|
D. |
ipv6 address 2001:EB8:C1:2200:1:0000:331/64 |
Answer: C
A network engineer is configuring a switch so that it is remotely reachable via SSH. The engineer has already configured the host name on the router. Which additional command must the engineer configure before entering the command to generate the RSA key?
|
A. |
password password |
|
B. |
crypto key generate rsa modulus 1024 |
|
C. |
ip domain-name domain |
|
D. |
ip ssh authentication-retries 2 |
Answer: C
Refer to the exhibit. Which two commands must be added to update the configuration of router R1 so that it accepts only encrypted connections? (Choose two)
![]()
|
A. |
username CNAC secret
R!41!4319115@ |
|
B. |
ip ssh version 2 |
|
C. |
line vty 0 4 |
|
D. |
crypto key
generate rsa 1024 |
|
E. |
transport input ssh |
Answer: DE
A network engineer must configure two new subnets using the address block 10.70.128.0/19 to meet these requirements:
- The first subnet
must support 24
hosts
- The second subnet
must support 472 hosts
- Both subnets must use the longest subnet mask possible
from the address block
Which two configurations must be used to configure the new subnets and meet a requirement to use the first available address in each subnet for the router interfaces? (Choose two )
|
A. |
interface vlan 1234 ip address 10.70.159.1 255.255.254.0 |
|
B. |
interface vlan 1148 ip address 10.70.148.1 255.255.254.0 |
|
C. |
interface vlan
4722 ip address 10.70.133.17 255.255.255.192 |
|
D. |
interface vlan
3002 ip address 10.70.147.17 255.255.255.224 |
|
E. |
interface vlan
155 ip address 10.70.155.65 255.255.255.224 |
Answer: BE
Explanation:
These two are the only ones that have the first IP in their range and meet the requirement of 472 hosts (B) and 24 hosts (E) respectively.
What is a function of Opportunistic Wireless Encryption in an environment?
|
A. |
offer compression |
|
B. |
increase security by using a WEP connection |
|
C. |
provide authentication |
|
D. |
protect traffic on open networks |
Answer: D
Refer to the exhibit. Which two commands when used together create port channel 10? (Choose two.)
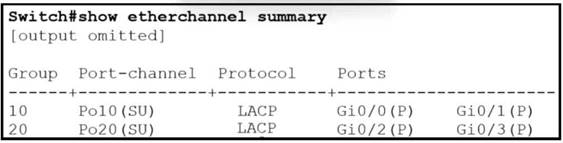
|
A. |
int range g0/0-1
channel-group 10 mode
active |
|
B. |
int range g0/0-1 channel-group 10 mode desirable |
|
C. |
int range g0/0-1 channel-group 10 mode passive |
|
D. |
int range g0/0-1 channel-group 10 mode auto |
|
E. |
int range g0/0-1
channel-group 10 mode
on |
Answer: AC
Refer to the exhibit. A static route must be configured on R14 to forward traffic for the 172.21.34.0/25 network that resides on R86.
Which command must be used to fulfill the request?
![]()
|
A. |
ip route 172.21.34.0 255.255.255.192 10.73.65.65 |
|
B. |
ip route 172.21.34.0 255.255.255.0 10.73.65.65 |
|
C. |
ip route 172.21.34.0 255.255.128.0 10.73.65.64 |
|
D. |
ip route 172.21.34.0 255.255.255.128 10.73.65.66 |
Answer: D
A network engineer must implement an IPv6 configuration on the vlan 2000 interface to create a routable locally-unique unicast address that is blocked from being advertised to the internet.
Which configuration must the engineer apply?
|
A. |
interface
vlan 2000 ipv6 address
ffc0:0000:aaaa::1234:2343/64 |
|
B. |
interface vlan 2000 Ipv6 address fc00:0000:aaaa:a15d:1234:2343:8aca/64 |
|
C. |
interface vlan
2000 ipv6 address fe80:0000:aaaa::1234:2343/64 |
|
D. |
interface vlan 2000 ipv6 address fd00::1234:2343/64 |
Answer: D
Refer to the exhibit. Host A sent a data frame destined for host D.
![]()
What does the switch do when it receives the frame from host A?
|
A. |
It drops the frame from
the switch CAM
table. |
|
B. |
It floods the frame
out of all ports except
port Fa0/1. |
|
C. |
It shuts down the
port Fa0/1 and places it in err-disable mode. |
|
D. |
It experiences a broadcast storm. |
Answer:
B
What is the function of the controller in a software-defined network?
|
A. |
multicast replication at the hardware level |
|
B. |
fragmenting and reassembling packets |
|
C. |
making routing decisions |
|
D. |
forwarding packets |
Answer: C
Refer to the exhibit. An engineer built a new L2 LACP EtherChannel between SW1 and SW2 and executed these show commands to verify the work.
Which additional task allows the two switches to establish an LACP port channel?
![]()
|
A. |
Change the channel-group mode on SW2 to auto |
|
B. |
Change the channel-group mode
on SW1 to desirable. |
|
C. |
Configure the interface port-channel 1 command on both switches. |
|
D. |
Change the channel-group mode on SW1 to active
or passive. |
Answer: D
What is a requirement for nonoverlapping Wi-Fi channels?
|
A. |
different security settings |
|
B. |
discontinuous frequency ranges |
|
C. |
different transmission speeds |
|
D. |
unique SSIDs |
Answer:
B
A network engineer is Installing an IPv6-only capable device.
The client has requested that the device IP address be reachable only from the internal network. Which type of IPv6 address must the engineer assign?
|
A. |
unique local address |
|
B. |
link-local address |
|
C. |
aggregatable global
address |
|
D. |
IPv4-compatible IPv6 address |
Answer:
A
Explanation:
A link-local address is a network address that is valid only for communications within the subnetwork.
Refer to the exhibit. Which plan must be Implemented to ensure optimal QoS marking practices on this network?
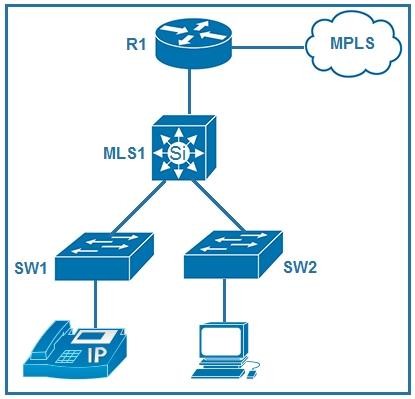
|
A. |
As traffic traverses MLS1 remark the traffic, but trust all markings at the access
layer. |
|
B. |
Trust the IP phone
markings on SW1 and mark traffic entering SW2 at SW2. |
|
C. |
Remark traffic as it traverses R1 and trust
all markings at the access
layer. |
|
D. |
As traffic enters
from the access
layer on SW1 and SW2 trust all
traffic markings. |
Answer: B
Explanation:
Tell the switch to trust CoS markings from a Cisco IP phone on the access port. Cisco IP phones use 802.1q tags, these .1q tags contain the CoS value, to mark voice traffic at layer 2. When it's forwarded upstream, the DSCP value is trusted (on the uplink port) and unchanged, but the .1q tag (and with it the CoS value) is stripped off by the upstream switch when received over the trunk.
Refer to the exhibit. Traffic that is flowing over interface TenGigabitEthernet0/0 experiences slow transfer speeds.
What is the reason for the issue?
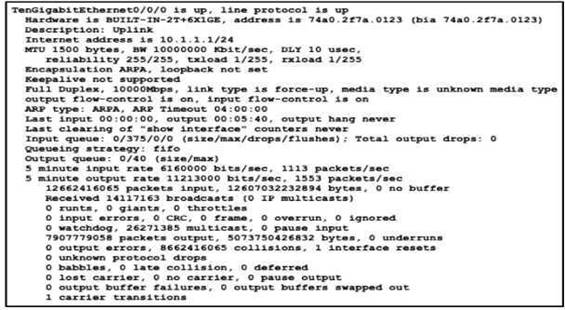
|
A. |
heavy traffic congestion |
|
B. |
a duplex incompatibility |
|
C. |
a speed conflict |
|
D. |
queuing drops |
Answer: C
Refer to the exhibit. Site A was recently connected to site B over a new single-mode fiber path. Users at site A report Intermittent connectivity Issues with applications hosted at site B.
What is the reason for the problem?
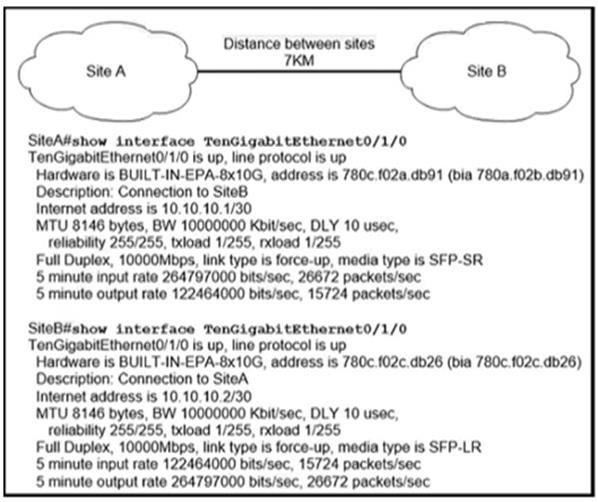
|
A. |
Heavy usage is causing high
latency. |
|
B. |
An incorrect type of transceiver has been inserted into a device
on the link. |
|
C. |
physical network errors are being
transmitted between the two sites. |
|
D. |
The wrong cable
type was used to make
the connection. |
Answer:
B
Refer to the exhibit. Switch A is newly configured. All VLANs are present in the VLAN database. The IP phone and PC A on Gi0/1 must be configured for the appropriate VLANs to establish connectivity between the PCs.
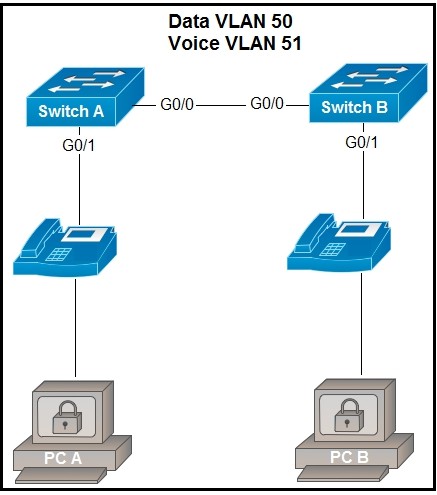
Which command set fulfills the requirement?
|
A. |
SwitchA(config-if)#switchport
mode access SwitchA(config-if)#switchport
access vlan 50 SwitchA(config-if)#switchport voice
vlan 51 |
|
B. |
SwitchA(config-if)#switchport mode
trunk SwitchA(config-if)#switchport trunk
allowed vlan add 50, 51 SwitchA(config-if)#switchport voice
vlan dot1p |
|
C. |
SwitchA(config-if)#switchport
mode trunk SwitchA(config-if)#switchport trunk allowed vlan 50, 51 SwitchA(config-if)#mis qos trust cos |
|
D. |
SwitchA(config-if)#switchport
mode access SwitchA(config-if)#switchport access vlan 50
SwitchA(config-if)#switchport voice vlan
untagged |
Answer:
A
An engineer must configure R1 for a new user account. The account must meet these requirements:
- It must be configured in the local database.
- The username is engineer.
- It must use the strongest password configurable.
Which command must the engineer configure on the router?
|
A. |
R1 (config)# username engineer2 algorithm-type scrypt
secret test2021 |
|
B. |
R1(config)# username engineer2 secret 5 password S1$b1Ju$kZbBS1Pyh4QzwXyZ |
|
C. |
R1(config)# username engineer2 privilege 1 password 7 test2021 |
|
D. |
R1(config)# username englneer2 secret 4 S1Sb1Ju$kZbBS1Pyh4QzwXyZ |
Answer:
A
Refer to the exhibit. Router R1 resides in OSPF Area 0. After updating the R1 configuration to influence the paths that it will use to direct traffic, an engineer verified that each of the four Gigabit interfaces has the same route to 10.10.0.0/16.
Which interface will R1 choose to send traffic to reach the route?
![]()
|
A. |
GigabitEthernet0/0 |
|
B. |
GigabltEthornet0/1 |
|
C. |
GigabitEthernet0/2 |
|
D. |
GigabitEthernet0/3 |
Answer:
B
What is a requirement when configuring or removing LAG on a WLC?
|
A. |
The incoming and outgoing ports
for traffic flow
must be specified if LAG is
enabled. |
|
B. |
The controller must be rebooted after enabling or reconfiguring LAG. |
|
C. |
The management interface must
be reassigned if LAG disabled. |
|
D. |
Multiple untagged interfaces on the same
port must be supported. |
Answer: C
Explanation:
When you enable LAG or change the LAG configuration, you must immediately reboot the controller.
http://what-when-how.com/deploying-and-troubleshooting-cisco-wireless-lan-controllers/lag-cisco- wireless-lan-controllers/
Refer to the exhibit. The DHCP server and clients are connected to the same switch.
What is the next step to complete the DHCP configuration to allow clients on VLAN 1 to receive addresses from the DHCP server?
![]()
|
A. |
Configure the ip dhcp snooping trust command on the interlace that is connected to the DHCP client. |
|
B. |
Configure the ip dhcp
relay information option
command on the
interface that is connected to the
DHCP client. |
|
C. |
Configure the ip dhcp snooping trust command on the interface that is connected to the DHCP server. |
|
D. |
Configure the Ip dhcp
relay information option
command on the
interface that is connected to the
DHCP server. |
Answer: C
Explanation:
If a Layer 2 LAN port is connected to a DHCP server, configure the port as trusted by entering the ip dhcp snooping trust interface configuration command. https://www.cisco.com/en/US/docs/general/Test/dwerblo/broken_guide/snoodhcp.html#wp10733 67
What provides centralized control of authentication and roaming in an enterprise network?
|
A. |
a lightweight access
point |
|
B. |
a firewall |
|
C. |
a wireless LAN controller |
|
D. |
a LAN switch |
Answer: C
Refer to the exhibit. Traffic sourced from the loopback0 Interface is trying to connect via ssh to the host at 10.0.1.15.
What is the next hop to the destination address?
![]()
|
A. |
192.168.0.7 |
|
B. |
192.168.0.4 |
|
C. |
192.168.0.40 |
|
D. |
192.168.3.5 |
Answer:
B
Refer to the exhibit. All interfaces are configured with duplex auto and ip ospf network broadcast. Which configuration allows routers R14 and R86 to form an OSPFv2 adjacency and act as a central point for exchanging OSPF information between routers?
![]()
|
A. |
|
|
B. |
|
|
C. |
|
|
D. |
|
Answer:
A
Refer to the exhibit. Which network prefix was learned via EIGRP?
![]()
|
A. |
172.16.0.0/16 |
|
B. |
192.168.2.0/24 |
|
C. |
207.165.200.0/24 |
|
D. |
192.168.1.0/24 |
Answer:
B
Refer to the exhibit. How should the configuration be updated to allow PC1 and PC2 access to the Internet?
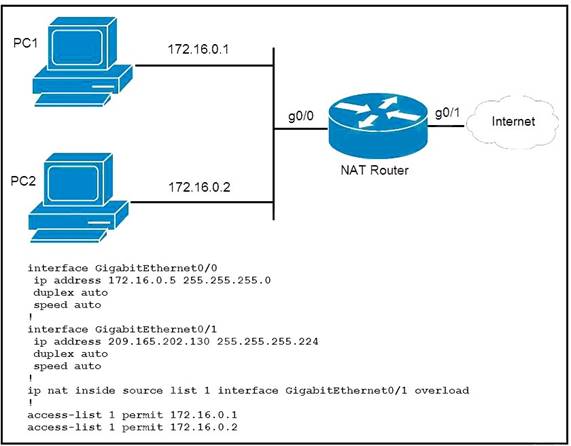
|
A. |
Modify the configured number of the second access
list. |
|
B. |
Add either the ip nat {inside|outside} command under both
interfaces. |
|
C. |
Remove the
overload keyword from
the ip nat inside source
command. |
|
D. |
Change the ip nat inside
source command to use interface GigabitEthernet0/0. |
Answer:
B
Refer to the exhibit. An engineer is updating the R1 configuration to connect a new server to the management network. The PCs on the management network must be blocked from pinging the default gateway of the new server.
Which command must be configured on R1 to complete the task?

|
A. |
R1(config)#ip route 172.16.2.2 255.255.255.248 gi0/1 |
|
B. |
R1(config)#ip route
172.16.2.2 255.255.255.255 gi0/0 |
|
C. |
R1(config)#ip route
172.16.2.0 255.255.255.0 192.168.1.15 |
|
D. |
R1(conflg)#ip route 172.16.2.0 255.255.255.0 192.168.1.5 |
Answer: B
Explanation:
By specifying the outgoing interface and not the next hop IP address, the Management devices will be able to ping the new server, but not the default gateway of the server.
Refer to the exhibit. Which command must be issued to enable a floating static default route on router A?
![]()
|
A. |
ip route 0.0.0.0
0.0.0.0 192.168.1.2 |
|
B. |
ip default-gateway 192.168.2.1 |
|
C. |
ip route 0.0.0.0 0.0.0.0 192.168.2.1 10 |
|
D. |
ip route 0.0.0.0
0.0.0.0 192.168.1.2 10 |
Answer: D
Which protocol is used for secure remote CLI access?
|
A. |
HTTPS |
|
B. |
HTTP |
|
C. |
Telnet |
|
D. |
SSH |
Answer: D
Refer to the exhibit. All VLANs are present in the VLAN database.
Which command sequence must be applied to complete the configuration?
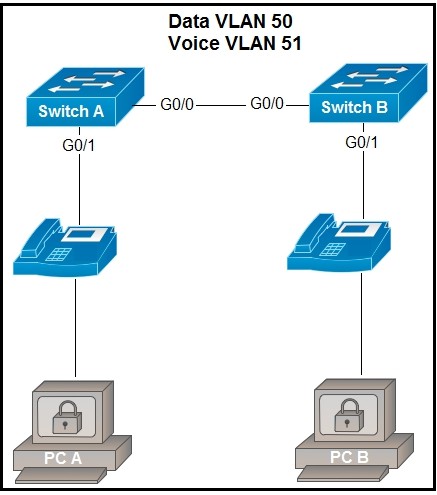
|
A. |
|
|
B. |
|
|
C. |
|
|
D. |
|
Answer: C
Refer to the exhibit. Which minimum configuration items are needed to enable Secure Shell version 2 access to R15?
![]()
|
A. |
|
|
B. |
|
|
C. |
|
|
D. |
|
Answer: C
What is the purpose of the ip address dhcp command?
|
A. |
to configure an Interface as a DHCP
server |
|
B. |
to configure an interface as a DHCP
helper |
|
C. |
to configure an interface as a DHCP
relay |
|
D. |
to configure an interface as a DHCP
client |
Answer: D
Explanation:
This command enables the DHCP client on the interface and removes all manually-configured addresses on the interface. https://www.cisco.com/c/en/us/td/docs/routers/nfvis/switch_command/b-nfvis-switch-command- reference/ip_addressing_commands.pdf
Refer to the exhibit. Router R1 currently is configured to use R3 as the primary route to the Internet, and the route uses the default administrative distance settings. A network engineer must configure R1 so that it uses R2 as a backup, but only if R3 goes down.
Which command must the engineer configure on R1 so that it correctly uses R2 as a backup route, without changing the administrative distance configuration on the link to R3?
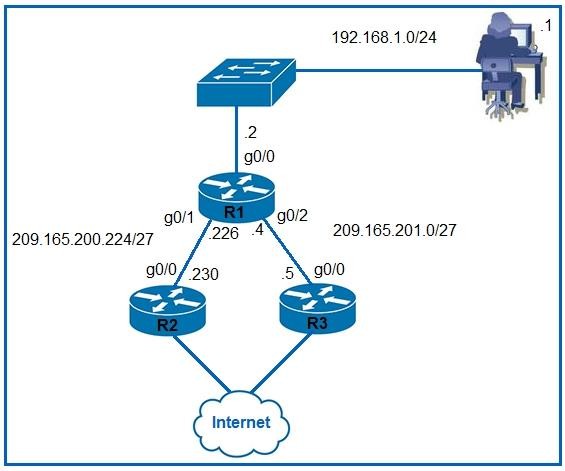
|
A. |
ip route 0.0.0.0
0.0.0.0 g0/1 1 |
|
B. |
ip route 0.0.0.0 0.0.0.0
209.165.201.5 10 |
|
C. |
ip route 0.0.0.0 0.0.0.0
209.165.200.226 1 |
|
D. |
ip route 0,0.0.0
0.0.0.0 g0/1 6 |
Answer: D
Refer to the exhibit. Which configuration enables DHCP addressing for hosts connected to interface FastEthernet0/1 on router R4?
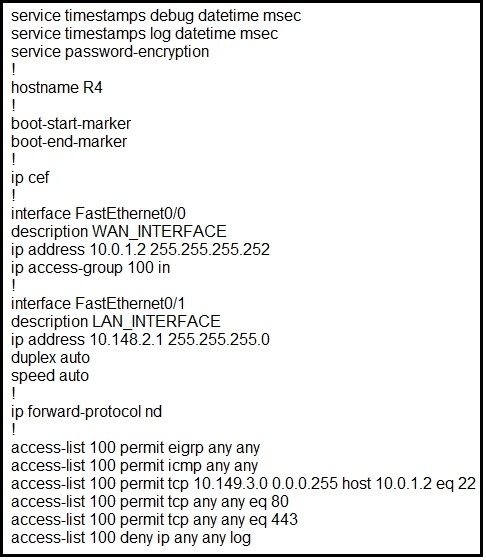
|
A. |
interface
FastEthernet0/0 ip helper-address 10.0.1.1 i access-list 100 permit udp host 10.0.1.1 eq bootps host
10.148.2.1 |
|
B. |
interface FastEthernot0/1 ip helper-address 10.0.1.1 ! access-list 100 permit tcp host 10.0.1.1 eq 67 host
10.148.2.1 |
|
C. |
interface FastEthernetO/0 ip helper-address 10.0.1.1 I access-list 100 permit host
10.0.1.1 host 10.148.2.1 eq bootps |
|
D. |
interface FastEthernet0/1 ip helper-address 10.0.1.1 ! access-list 100 permit
udp host 10.0.1.1 eq bootps host
10.148.2.1 |
Answer: D
Explanation:
BOOTP is implemented using the User Datagram Protocol (UDP) for transport protocol, port number 67 is used by the (DHCP) server for receiving client-requests and port number 68 is used by the client for receiving (DHCP) server responses. BOOTP operates only on IPv4 networks.
OSPF must be configured between routers R1 and R2.
Which OSPF configuration must be applied to router R1 to avoid a DR/BDR election?
|
A. |
router ospf 1 network 192.168.1.1 0.0.0.0 area 0 interface e1/1 ip address 192.168.1.1 255.255.255.252 ip ospf network broadcast |
|
B. |
router ospf
1 network 192.168.1.1 0.0.0.0 area 0 interface e1/1 ip address 192.168.1.1 255.255.255.252 ip ospf network point-to-point |
|
C. |
router ospf
1 network 192.168.1.1 0.0.0.0 area 0 interface e1/1 ip address 192.168.1.1 255.255.255.252 ip ospf cost 0 |
|
D. |
router ospf 1 network 192.168.1.1 0.0.0.0 area 0 hello interval 15 interface e1/1 Ip address 192.168.1.1 255.255.255.252 |
Answer:
B
Refer to the exhibit. An IP subnet must be configured on each router that provides enough addresses for the number of assigned hosts and anticipates no more than 10% growth for now hosts. Which configuration script must be used?

|
A. |
|
|
B. |
|
|
C. |
|
|
D. |
|
Answer: C
Explanation:
Can pinpoint this easily by only looking at R8:
255.255.255.0 is enough = Answer is C
Which wireless security protocol relies on Perfect Forward Secrecy?
|
A. |
WPA3 |
|
B. |
WPA |
|
C. |
WEP |
|
D. |
WPA2 |
Answer:
A
Explanation:
WPA3 (Wi-Fi Protected Access 3) is the newest wireless security protocol designed to encrypt data using a frequent and automatic encryption type called Perfect Forward Secrecy.
What is a function of an endpoint on a network?
|
A. |
forwards traffic between VLANs on a network |
|
B. |
connects server
and client devices
to a network |
|
C. |
allows users
to record data and transmit to a file
server |
|
D. |
provides wireless services to users in a building |
Answer: C
Explanation:
An endpoint is a remote computing device that communicates back and forth with a network to which it is connected. Examples of endpoints include:
- Desktops
- Laptops
- Smartphones
- Tablets
- Servers
- Workstations
- Internet-of-things (IoT) devices
Refer to the exhibit. Packets received by the router from BGP enter via a serial interface at 209.165.201.10. Each route is present within the routing table.
Which interface is used to forward traffic with a destination IP of 10.10.10.24?
![]()
|
A. |
F0/10 |
|
B. |
F0/11 |
|
C. |
F0/12 |
|
D. |
F0/13 |
Answer: B
Refer to the exhibit. An engineer has started to configure replacement switch SW1.
To verify part of the configuration, the engineer issued the commands as shown and noticed that the entry for PC2 is missing.
Which change must be applied to SW1 so that PC1 and PC2 communicate normally?
![]()
|
A. |
SW1(config)#interface fa0/2 SW1(config-if)#no switchport mode trunk
SW1(config-if)#no switchport trunk
allowed vlan 3 SW1(config-if)#switchport mode access |
|
B. |
SW1(config)#interface fa0/2 SW1(config-if)#no switchport access vlan 2 SW1(config-if)#no
switchport trunk allowed vlan 3
SW1(config-if)#switchport trunk allowed vlan 2 |
|
C. |
SW1(config)#interface fa0/2 SW1(config-if)#no
switchport access vlan 2 SW1(config-if)#switchport trunk native vlan 2 SW1(config-if)#switchport trunk
allowed vlan 3 |
|
D. |
SW1(config)#interface fa0/1 SW1(config-if)#no switchport access vlan 2 SW1(config-if)#switchport access vlan 3
SW1(config-if)#switchport trunk allowed vlan 2 |
Answer: A
Explanation:
access port - a port that can be assigned to a single VLAN. This type of interface is configured on switch ports that are connected to end devices such as workstations, printers, or access points. trunk port - a port that is connected to another switch. This type of interface can carry traffic of multiple VLANs, thus enabling you to extend VLANs across your entire network. Frames are tagged by assigning a VLAN ID to each frame as they traverse between switches.
Drag and Drop Question
Drag and drop the statements about networking from the left onto the corresponding networking types on the right.
![]()
Answer:
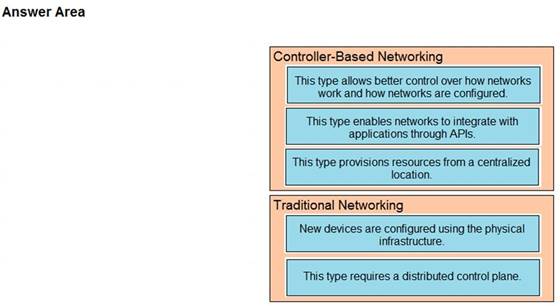
Drag and Drop Question
Drag and drop the facts about wireless architectures from the left onto the types of access point on the right. Not all options are used.
![]()
Answer:
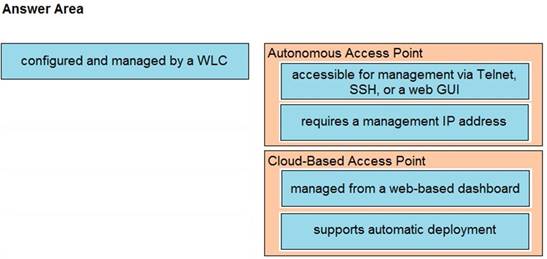
Drag and Drop Question
An engineer is tasked to configure a switch with port security to ensure devices that forward unicasts multicasts and broadcasts are unable to flood the port. The port must be configured to permit only two random MAC addresses at a time.
Drag and drop the required configuration commands from the left onto the sequence on the right Not all commands are used.
![]()
Answer:
Drag and Drop Question
Drag and drop the characteristics of networking from the left onto the networking types on the right.
![]()
Answer:
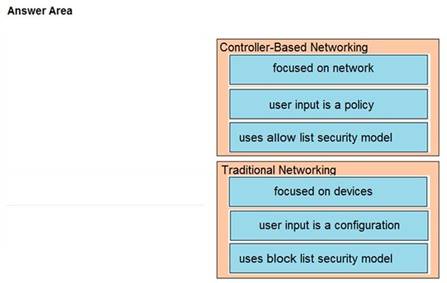
Drag and Drop Question
Drag and drop the Rapid PVST+ forwarding slate actions from the loft to the right. Not all actions are used.
![]()
Answer:
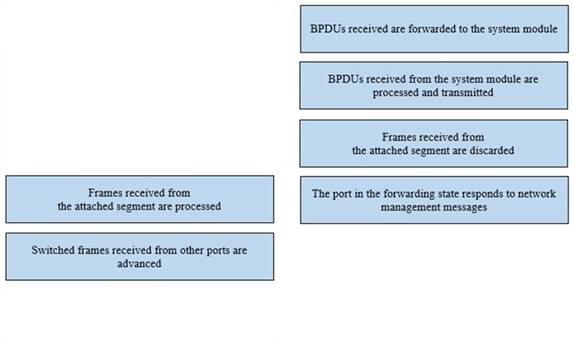
Drag and Drop Question
Drag and drop the TCP or UDP details from the left onto their corresponding protocols on the right.
![]()
Answer:
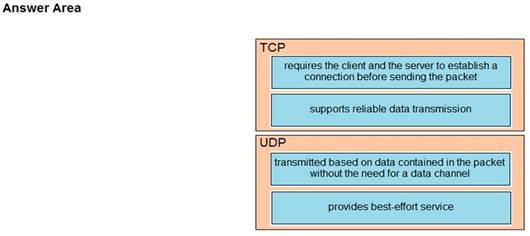
Drag and Drop Question
Drag and drop the descriptions of AAA services from the left onto the corresponding services on the right.
![]()
Answer:
![]()
What differentiates device management enabled by Cisco DNA Center from traditional campus device management?
|
A. |
CLI-oriented device |
|
B. |
centralized |
|
C. |
device-by-device hands-on |
|
D. |
per-device |
Answer:
B
Explanation:
When using Cisco DNA Center to manage network device, device management is centralized and is managed from the DNA center GUI. Using DNA Center allows for us to have a more centralized management of network infrastructure as configuration changes can be applied to an many devices at once when these changes are done through DNA Center.
Refer to the exhibit. What is represented beginning with line 1 and ending with line 5?
![]()
|
A. |
object |
|
B. |
value |
|
C. |
key |
|
D. |
array |
Answer: D
Explanation:
These are some of the characteristics of JSON:
It uses a hierarchical structure and contains nested values.
It uses braces { } to hold objects and square brackets [ ] hold arrays. Its data is written as key/value pairs.
Drag and Drop Question
Drag and drop the AAA features from the left onto the corresponding AAA security services on the right. Not all options are used.
![]()
Answer:
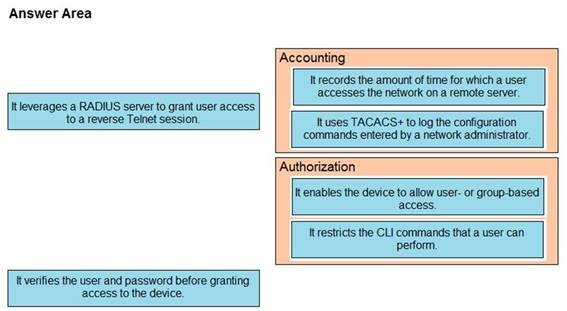
Refer to the exhibit. Clients on the WLAN are required to use 802.11r. What action must be taken to meet the requirement?
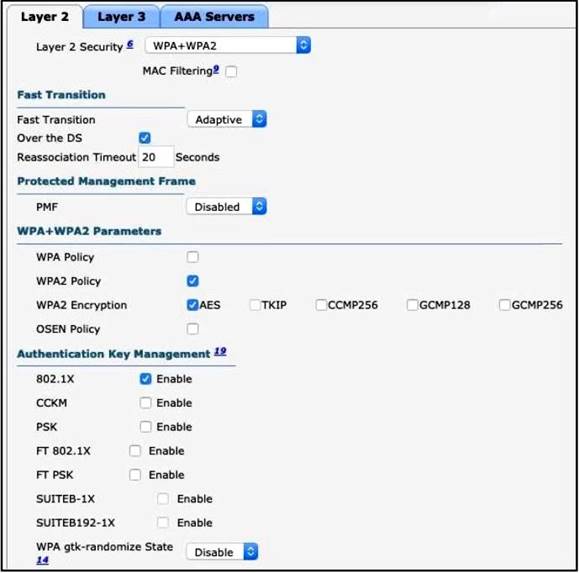
|
A. |
Under Protected Management Frames, set the PMF option
to Required. |
|
B. |
Enable CCKM
under Authentication Key Management. |
|
C. |
Set the Fast Transition option and the
WPA gtk-randomize State
to disable. |
|
D. |
Set the Fast
Transition option to Enable and
enable FT 802.1X
under Authentication Key Management. |
Answer: D
Refer to the exhibit. What must be configured to enable 802.11w on the WLAN?
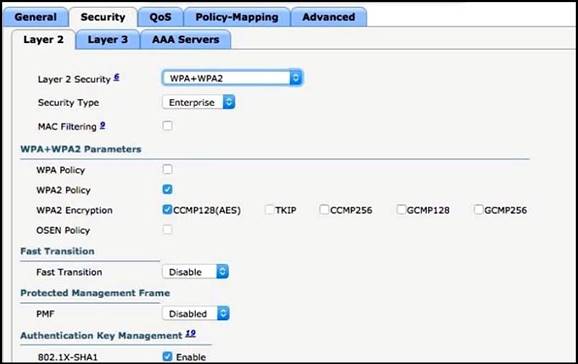
|
A. |
Set Fast Transition to Enabled. |
|
B. |
Enable WPA
Policy. |
|
C. |
Set PMF to Required. |
|
D. |
Enable MAC Filtering. |
Answer: C
Explanation:
IEEE 802.11w is the Protected Management Frames standard.
Which service is missing when RADIUS is selected to provide management access to the WLC?
|
A. |
authorization |
|
B. |
authentication |
|
C. |
accounting |
|
D. |
confidentiality |
Answer: D
Explanation:
Remote Authentication Dial-In User Service (RADIUS) is a networking protocol that provides centralized authentication, authorization, and accounting (AAA) management for users who connect and use a network service.
With RADIUS only the password is encrypted while the other information such as username, accounting information, etc are not encrypted. Encryption is "the process of converting information or data into a code, especially to prevent unauthorized access". So since RADIUS only encrypts the passwords, there is no confidentiality.
Drag and Drop Question
Drag and drop the IPv6 addresses from the left onto the corresponding address types on the right.
![]()
Answer:
![]()
Refer to the exhibit. When router R1 is sending traffic to IP address 10.56.192.1, which interface or next hop address does it use to route the packet?
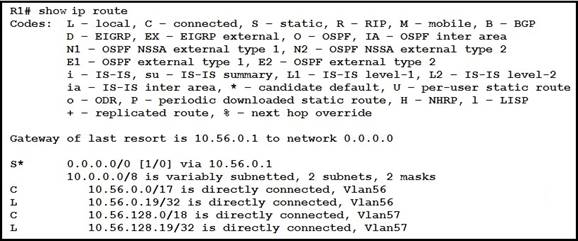
|
A. |
10.56.0.1 |
|
B. |
0.0.0.0/0 |
|
C. |
Vlan57 |
|
D. |
10.56.128.19 |
Answer:
A
Refer to the exhibit. Load-balanced traffic is coming in from the WAN destined to a host at 172.16.1.190. Which next-hop is used by the router to forward the request?
![]()
|
A. |
192.168.7.4 |
|
B. |
192.168.7.7 |
|
C. |
192.168.7.35 |
|
D. |
192.168.7.40 |
Answer: C
Refer to the exhibit. A network engineer must configure R1 so that it sends all packets destined to the 10.0.0.0/24 network to R3, and all packets destined to PC1 to R2. Which configuration must
the engineer implement?
![]()
|
A. |
R1(config)#ip route 10.0.0.0 255.255.255.0 172.16.0.2 R1(config)#ip route 10.0.0.5 255.255.255.255 192.168.0.2 |
|
B. |
R1(config)#ip route 10.0.0.0 255.255.0.0 172.16.0.2 R1(config)#ip route 10.0.0.5 255.255.255.255 192.168.0.2 |
|
C. |
R1(config)#ip route 10.0.0.0 255.255.255.0 192.168.0.2 R1(config)#ip route 10.0.0.5 255.255.255.255 172.16.0.2 |
|
D. |
R1(config)#ip route 10.0.0.0 255.255.0.0 192.168.0.2 R1(config)#ip route 10.0.0.5 255.255.255.0 172.16.0.2 |
Answer: C
Which command must be entered to configure a DHCP relay?
|
A. |
ip dhcp relay |
|
B. |
ip dhcp
pool |
|
C. |
ip address dhcp |
|
D. |
ip helper-address |
Answer: D
What is a zero-day exploit?
|
A. |
It is when a new network vulnerability is discovered before
a fix is available |
|
B. |
It is when the
perpetrator inserts itself
in a conversation between two
parties and captures or alters data. |
|
C. |
It is when the network is saturated with
malicious traffic that
overloads resources and
bandwidth |
|
D. |
It is when
an attacker inserts malicious code into a SQL
server. |
Answer:
A
A network engineer is replacing the switches that belong to a managed-services client with new Cisco Catalyst switches. The new switches will be configured for updated security standards including replacing.
Telnet services with encrypted connections and doubling the modulus size from 1024. Which two commands must the engineer configure on the new switches? (Choose two.)
|
A. |
crypto key generate rsa general-keys modulus 1024 |
|
B. |
transport input
all |
|
C. |
crypto key generate rsa usage-keys |
|
D. |
crypto key generate rsa modulus 2048 |
|
E. |
transport input ssh |
Answer: DE
Which QoS queuing method discards or marks packets that exceed the desired bit rate of traffic flow?
|
A. |
shaping |
|
B. |
policing |
|
C. |
CBWFQ |
|
D. |
LLQ |
Answer:
B
Explanation:
Use the police command to mark a packet with different quality of service (QoS) values based on conformance to the service-level agreement. Traffic policing allows you to control the maximum rate of traffic transmitted or received on an interface.
Reference: https://www.cisco.com/c/en/us/td/docs/ios/qos/configuration/guide/12_2sr/qos_12_2sr_book/traffi c_policing.html
What is the role of disaggregation in controller-based networking?
|
A. |
It divides the control-plane and data-plane functions. |
|
B. |
It summarizes the routes
between the core
and distribution layers
of the network
topology. |
|
C. |
It enables a network topology to quickly
adjust from a ring network
to a star network |
|
D. |
It streamlines traffic handling by assigning individual devices to perform either
Layer 2 or Layer 3 functions. |
Answer: A
Refer to the exhibit. What is the next hop for traffic entering R1 with a destination of 10.1.2.126?
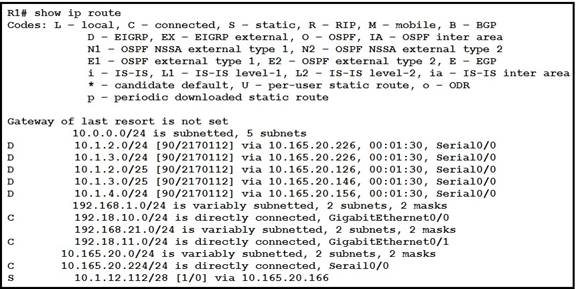
|
A. |
10.165 20.126 |
|
B. |
10.165.20.146 |
|
C. |
10.165.20.166 |
|
D. |
10.165 20.226 |
Answer:
A
Refer to the exhibit. The given Windows PC is requesting the IP address of the host at www.cisco.com. To which IP address is the request sent?
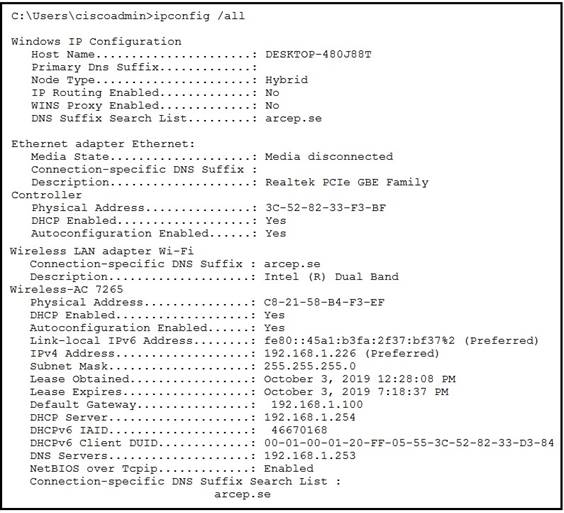
|
A. |
192.168.1.226 |
|
B. |
192.168.1.100 |
|
C. |
192.168.1.254 |
|
D. |
192.168.1.253 |
Answer: D
Explanation:
Send for DNS serve, because url should be translate to IP address.
Why would VRRP be implemented when configuring a new subnet in a multivendor environment?
|
A. |
when a gateway
protocol is required that support more
than two Cisco
devices for redundancy |
|
B. |
to enable
normal operations to continue after
a member failure
without requiring a change In a
host ARP cache |
|
C. |
to ensure that the spanning-tree forwarding path to the
gateway is loop-free |
|
D. |
to interoperate normally with all vendors
and provide additional security features for Cisco devices |
Answer:
B
Explanation:
VRRP does not provide additonal security features for Cisco devices.
When VRRP is implemented the virtual mac-addres of the VRRP group remains the same so the host does not need to make an arp request to learn another mac-address for the gateway.
An engineer has configured the domain name, user name, and password on the local router. What is the next step to complete the configuration tor a Secure Shell access RSA key?
|
A. |
crypto key Import
rsa pem |
|
B. |
crypto key pubkey-chain rsa |
|
C. |
crypto key
generate rsa |
|
D. |
crypto key zeroize rsa |
Answer: C
An engineer is configuring SSH version 2 exclusively on the R1 router.
What is the minimum configuration required to permit remote management using the cryptographic protocol?
|
A. |
hostname R1 service password-encryption crypto key generate rsa general-keys modulus 1024 username cisco privilege 15 password 0 cisco123 ip ssh
version 2 line vty 0 15 transport input ssh login local |
|
B. |
hostname R1 ip domain name
cisco crypto key generate rsa general-keys modulus 1024 username cisco privilege 15 password 0 cisco123 ip ssh
version 2 line vty 0 15 transport input ssh login local |
|
C. |
hostname
R1 crypto key generate rsa general-keys modulus 1024 username cisco privilege 15 password 0 cisco123 ip ssh
version 2 line vty 0
15 transport input ssh login
local |
|
D. |
hostname R1 ip domain name
cisco crypto key generate rsa general-keys modulus 1024 username cisco privilege 15 password 0 cisco123 ip ssh
version 2 line vty 0
15 transport input all login local |
Answer: B
After a recent security breach and a RADIUS failure, an engineer must secure the console port of each enterprise router with a local username and password.
Which configuration must the engineer apply to accomplish this task?
|
A. |
aaa new-model line con 0 password plaintextpassword
privilege level 15 |
|
B. |
aaa new-model aaa
authorization exec default local aaa authentication login
default radius username localuser privilege 15 secret plaintextpassword |
|
C. |
username localuser secret plaintextpassword
line con 0 no login local privilege level 15 |
|
D. |
username localuser secret plaintextpassword
line con 0 login authentication default privilege level 15 |
Answer: D
Which REST method updates an object in the Cisco DNA Center Intent API?
|
A. |
CHANGE |
|
B. |
UPDATE |
|
C. |
POST |
|
D. |
PUT |
Answer: D
Which two practices are recommended for an acceptable security posture in a network? (Choose two)
|
A. |
Backup device configurations to encrypted USB drives for secure retrieval |
|
B. |
Maintain network
equipment in a secure location |
|
C. |
Use a cryptographic keychain to authenticate to network devices |
|
D. |
Place internal email and file
servers in a designated DMZ |
|
E. |
Disable unused or unnecessary ports,
interfaces and services |
Answer: BE
An administrator must use the password complexity not manufacturer-name command to prevent
users from adding "cisco" as a password. Which command must be issued before this command?
|
A. |
Password complexity enable |
|
B. |
confreg 0x2142 |
|
C. |
Login authentication my-auth-list |
|
D. |
service password-encryption |
Answer: A
An engineer is configuring router R1 with an IPv6 static route for prefix 2019:C15C:0CAF:E001::/64.
The next hop must be 2019:C15C:0CAF:E002::1. The route must be reachable via the R1 Gigabit 0/0 interface.
Which command configures the designated route?
|
A. |
R1(config)#ipv6
route 2019:C15C:0CAF:E001::/64 2019:C15C:0CAF:E002::1 |
|
B. |
R1(config-if)#ipv6 route
2019:C15C:0CAF:E001::/64 2019:C15C:0CAF:E002::1 |
|
C. |
R1(config-if)#ip route
2019:C15C:0CAF:E001::/64 GigabitEthernet0/0 |
|
D. |
R1(config)#ip route 2019:C15C:0CAF:E001::/64 GigabitEthernet0/0 |
Answer:
A
Drag and Drop Question
Drag and drop the QoS terms from the left onto the descriptions on the right.
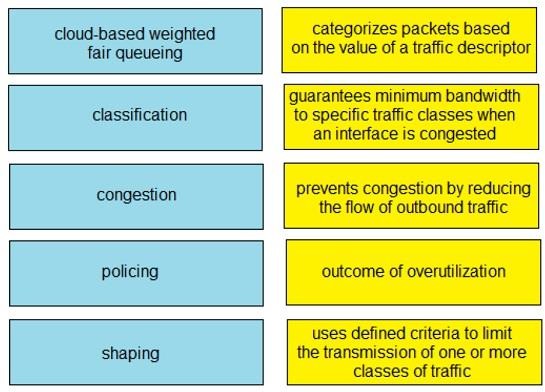
Answer:
![]()
Refer to the exhibit. A network engineer configures the Cisco WLC to authenticate local wireless clients against a RADIUS server.
Which task must be performed to complete the process?
![]()
|
A. |
Change the Server
Status to Disabled |
|
B. |
Select Enable
next to Management |
|
C. |
Select Enable
next to Network User |
|
D. |
Change the Support for CoA to
Enabled. |
Answer: C
Explanation:
Network users is for authenticating the people connected to the wireless network. Management is for authentication people who try to login to the WLC.
What is a function of Cisco Advanced Malware Protection for a Next-Generation IPS?
|
A. |
authorizing potentially compromised wireless traffic |
|
B. |
inspecting specific files and file
types for malware |
|
C. |
authenticating end users |
|
D. |
URL filtering |
Answer:
B
Refer to the exhibit. How many JSON objects are represented?
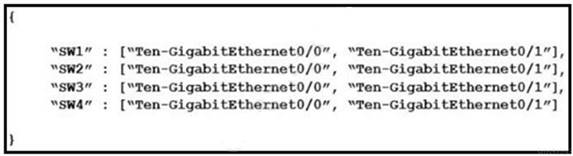
|
A. |
1 |
|
B. |
2 |
|
C. |
3 |
|
D. |
4 |
Answer:
A
Explanation:
By definition a object structure is {}.
Refer to the exhibit. Router R1 must be configured to reach the 10.0.3.0/24 network from the 10.0.1.0/24 segment.
Which command must be used to configure the route?
![]()
|
A. |
ip route 10.0.3.0 0.255.255.255 10.0.4.2 |
|
B. |
route add 10.0.3.0 mask 255.255.255.0 10.0.4.3 |
|
C. |
ip route 10.0.3.0 255.255.255.0 10.0.4.3 |
|
D. |
route add 10.0.3.0 0.255.255.255 10.0.4.2 |
Answer: C
Refer to the exhibit. The administrator must configure a floating static default route that points to 2001:db8:1234:2::1 and replaces the current default route only if it fails. Which command must the engineer configure on the CPE?
![]()
|
A. |
ipv6 route ::/0 2001:db8:1234:2::1 3 |
|
B. |
ipv6 route
::/128 2001:db8:1234:2::1 3 |
|
C. |
ipv6 route
::/0 2001:db8:1234:2::1 1 |
|
D. |
ipv6 route ::/0 2001:db8:1234:2::1 2 |
Answer:
B
What is the function of "off-the-shell" switches in a controller-based network?
|
A. |
providing a central view of the deployed network |
|
B. |
forwarding packets |
|
C. |
making routing decisions |
|
D. |
setting packet-handling policies |
Answer:
B
Which command entered on a switch configured with Rapid PVST+ listens and learns for a specific time period?
|
A. |
switch(config)#spanning-tree vlan
1 max-age 6 |
|
B. |
switch(config)#spanning-tree vlan
1 hello-time 10 |
|
C. |
switch(config)#spanning-tree vlan
1 priority 4096 |
|
D. |
switch(config)#spanning-tree vlan 1 forward-time 20 |
Answer: D
Drag and Drop Question
Drag and drop the functions of AAA supporting protocols from the left onto the protocols on the right.
![]()
Answer:
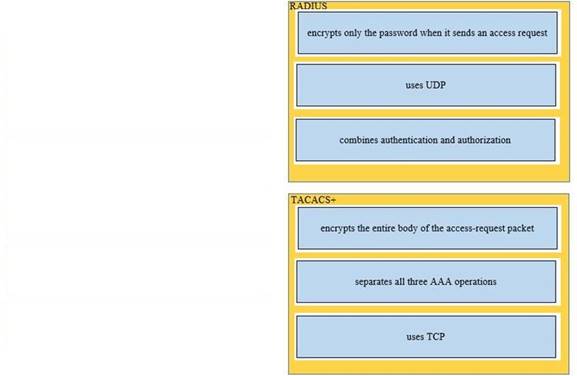
Drag and Drop Question
Drag and drop the IPv6 address details from the left onto the corresponding types on the right.
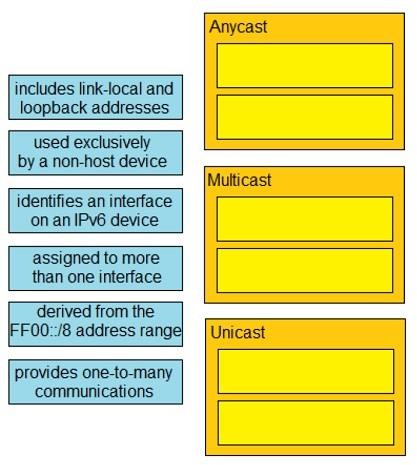
Answer:
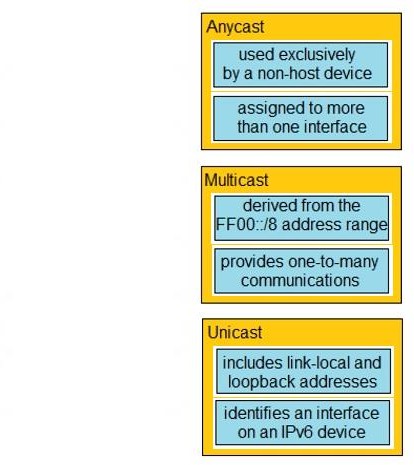
Drag and Drop Question
Drag and drop the TCP or UDP details from the left onto their corresponding protocols on the right.
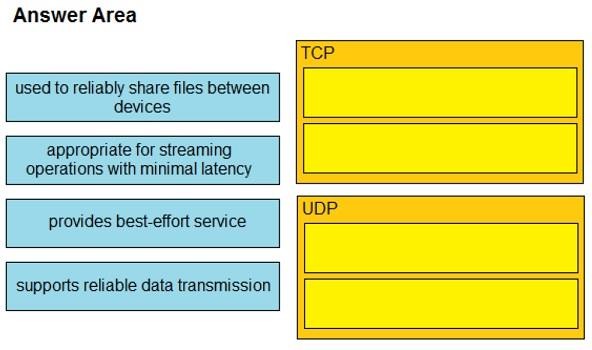
Answer:
![]()
Drag and Drop Question
Drag and drop each characteristic of device-management technologies from the left onto the deployment type on the right.
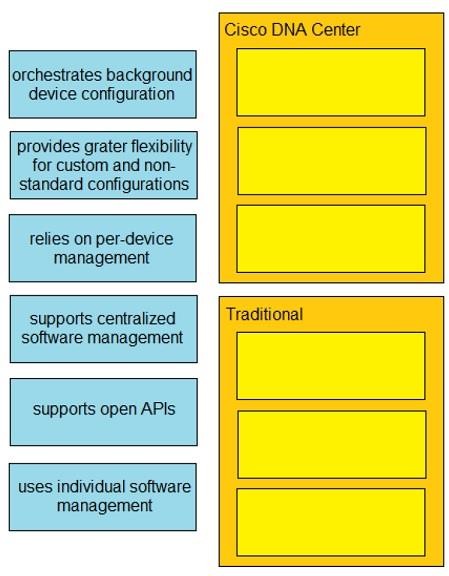
Answer:
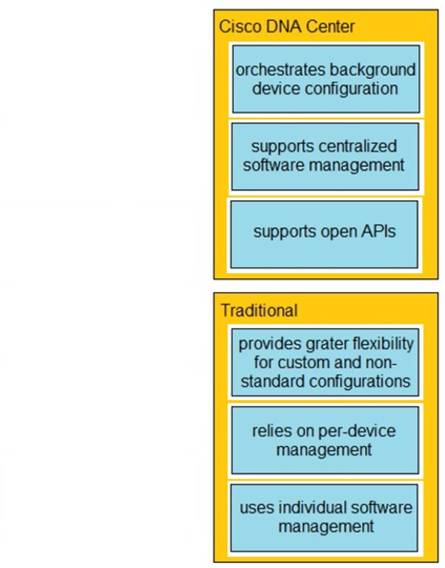
Drag and Drop Question
Drag and drop the elements of a security program from the left onto the corresponding descriptions on the right.
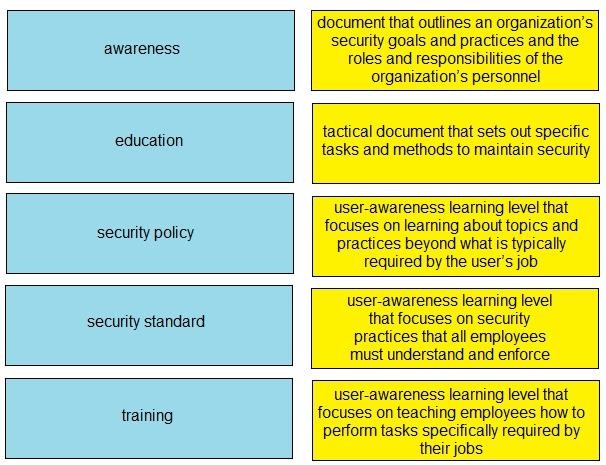
Answer:
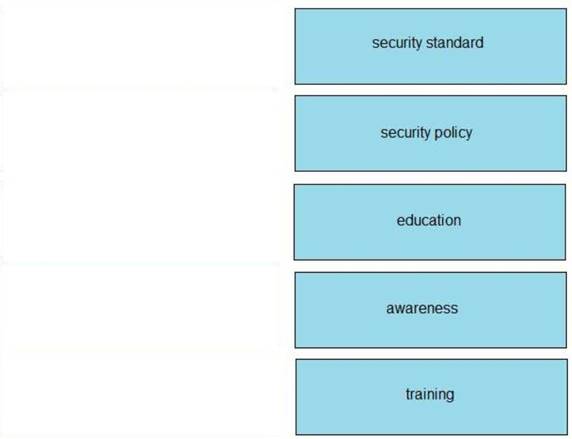
Drag and Drop Question
Drag and drop the Cisco IOS attack mitigation features from the left onto the types of network attack they mitigate on the right.
![]()
Answer:
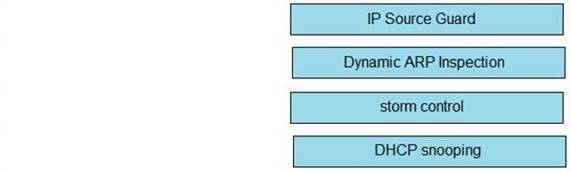
Which command implies the use of SNMPv3?
|
A. |
snmp-server host |
|
B. |
snmp-server community |
|
C. |
snmp-server enable
traps |
|
D. |
snmp-server user |
Answer: D
Explanation:
Adds a new user to an SNMPv3 group and configures a plain text password for the user.
Example:
Device(config)# snmp-server user user1 group1 v3 auth md5 password123 priv passwd123654
Drag and Drop Question
Refer to Exhibit. The IP address configurations must be completed on the DC-1 and HQ-1 routers based on these requirements:
![]() DC-1 Gi1/0 must be the last usable address
on a /30
DC-1 Gi1/0 must be the last usable address
on a /30 ![]() DC-1 Gi1/1
must be the first usable
address on a /29
DC-1 Gi1/1
must be the first usable
address on a /29
![]() DC-1 Gi1/2 must be the last usable address
on a /28
DC-1 Gi1/2 must be the last usable address
on a /28 ![]() HQ-1
Gil/3 must be the last usable address on a /29
HQ-1
Gil/3 must be the last usable address on a /29
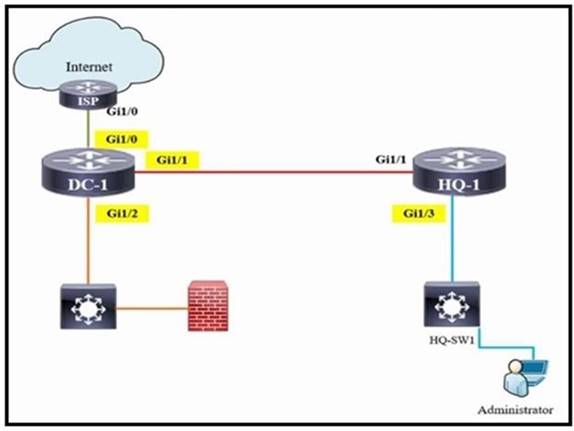
Drag and drop the commands from the left onto the destination interfaces on the right. Not all commands are used.
![]()
Answer:
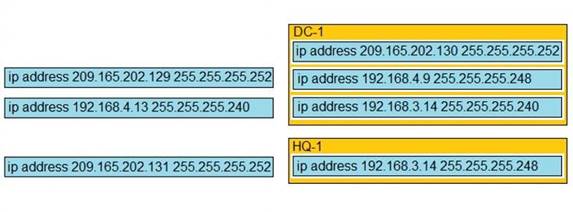
Drag and Drop Question
Drag and drop the IPv6 address descriptions from the left onto the IPv6 address types on the right. Not all options are used.
![]()
Answer:
![]()
Drag and Drop Question
Drag and drop the IPv6 addresses from the left onto the corresponding address types on the right.
![]()
Answer:
![]()
Refer to the exhibit. R1 has taken the DROTHER role in the OSPF DR/BDR election process. Which configuration must an engineer implement so that R1 is elected as the DR?
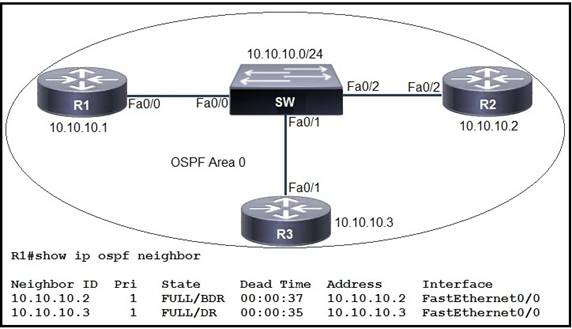
|
A. |
R1(config)#interface FastEthernet 0/0 R1(config-if)#ip ospf
priority 1 R1#clear ip ospf
process |
|
B. |
R3(config)#interface FastEthernet 0/1 R3(config-if)#ip ospf priority 200 R3#clear ip ospf
process |
|
C. |
R2(config)#interface FastEthernet 0/2 R2(config-if)#ip ospf priority 1 R2#clear ip ospf process |
|
D. |
R1(config)#interface FastEthernet 0/0 R1(config-if)#ip
ospf priority 200 R1#clear ip ospf process |
Answer: D
What is a feature of WPA?
|
A. |
802.1x authentication |
|
B. |
preshared key |
|
C. |
TKIP/MIC encryption |
|
D. |
small Wi-Fi application |
Answer: C
Refer to the exhibit. The network administrator must prevent the switch Cat9K-2 IP address from being visible in LLDP without disabling the protocol.
Which action must be taken must be taken to complete the task?
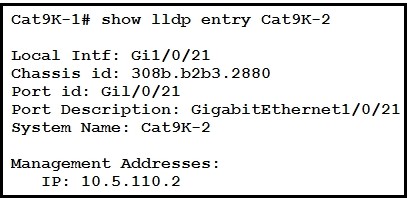
|
A. |
Configure the no lldp tlv-select-management-address command
globally on Cat9K-2 |
|
B. |
Configure the no lldp
transmit command on interface G1/0/21 in Cat9K-1 |
|
C. |
Configure the no lldp
receive command on interface G1/0/21
on Cat9K-1 |
|
D. |
Configure the no lldp mac-phy-cfg command globally on Cat9K-2 |
Answer:
A
Explanation:
This example shows how to enable LLDP to send or receive IPv4 management address TLVs: switch# configure terminal
switch(config)# lldp tlv-select management-address v4
Source: https://www.cisco.com/c/en/us/td/docs/switches/datacenter/nexus3000/sw/layer2/602_U1_1/b_Ci sco_n3k_Layer_2_Switching_Config_602_u1_1/b_Cisco_n3k_Layer_2_Switching_Config_602_u 1_1_chapter_01001.pdf
Refer to the exhibit. What are the two steps an engineer must take to provide the highest encryption and authentication using domain credentials from LDAP?
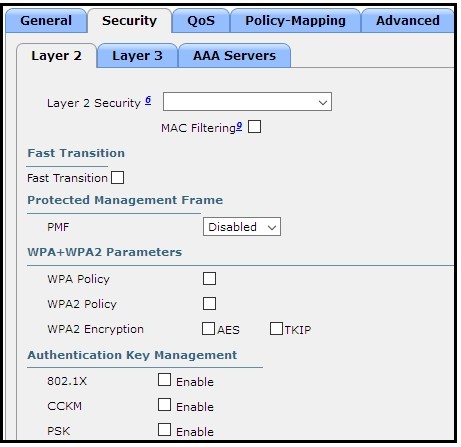
|
A. |
Select PSK under
Authentication Key Management |
|
B. |
Select WPA+WPA2 on Layer 2
Security |
|
C. |
Select Static-WEP + 802.1X on Layer 2
Security |
|
D. |
Select WPA Policy with
TKIP Encryption |
|
E. |
Select 802.1X from
under Authentication Key
Management |
Answer: BE
Which WAN topology has the highest degree of reliability?
|
A. |
full mesh |
|
B. |
Point-to-point |
|
C. |
hub-and-spoke |
|
D. |
router-on-a-stick |
Answer:
A
Refer to the exhibit. Which change to the configuration on Switch2 allows the two switches to establish an EtherChannel?
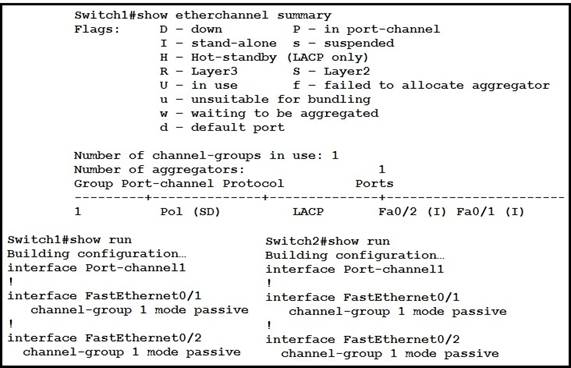
|
A. |
Change the protocol to EtherChannel mode
on. |
|
B. |
Change the
LACP mode to active |
|
C. |
Change the LACP
mode to desirable |
|
D. |
Change the protocol to PAqP and use auto
mode |
Answer: B
Refer to the exhibit. An engineer is asked to configure router R1 so that it forms an OSPF single- area neighbor relationship with R2.
Which command sequence must be implemented to configure the router?
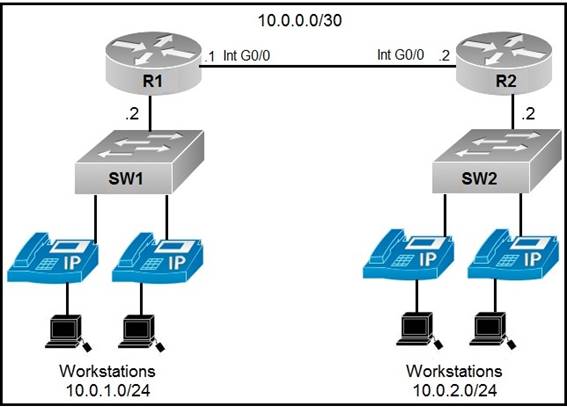
|
A. |
router ospf 100 network 10.0.0.0 0.0.0.252 area0 network
10.0.1.0 0.0.0.255 area0 |
|
B. |
router ospf 100 network 10.0.0.0 0.0.0.3 area0 network
10.0.2.0 255.255.255.0 area0 |
|
C. |
router ospf
10 network 10.0.0.0 0.0.0.3 area0 network 10.0.1.0 0.0.0.255 area0 |
|
D. |
router ospf
10 network 10.0.0.0 0.0.0.3 area0 network 10.0.2.0 0.0.0.255 area0 |
Answer: C
What is a function performed by a web server?
|
A. |
provide an application that is transmitted over HTTP |
|
B. |
send and
retrieve email from client devices |
|
C. |
authenticate and
authorize a user's
identity |
|
D. |
securely store flies
for FTP access |
Answer:
A
What is the collapsed layer in collapsed core architectures?
|
A. |
core and WAN |
|
B. |
access and
WAN |
|
C. |
distribution and access |
|
D. |
core and distribution |
Answer: D
Explanation:
A collapsed core architecture takes the normal three-tier hierarchical network and collapses it into a two-tier network. In a two-tier network, the function of the switches in the core layer and distribution layer are “collapsed” into a combined core and distribution layer on a single switch.
Which set of 2.4 GHz nonoverlapping wireless channels is standard in the United States?
|
A. |
channels 2, 7, 9, and 11 |
|
B. |
channels 1, 6, 11,
and 14 |
|
C. |
channels 2, 7, and 11 |
|
D. |
channels 1, 6, and 11 |
Answer: D
An engineer is installing a new wireless printer with a static IP address on the Wi-Fi network. Which feature must be enabled and configured to prevent connection issues with the printer?
|
A. |
client exclusion |
|
B. |
passive client |
|
C. |
DHCP address assignment |
|
D. |
static IP tunneling |
Answer: B
Explanation:
Passive clients are wireless devices, such as scales and printers that are configured with a static IP address. These clients do not transmit any IP information such as IP address, subnet mask, and gateway information when they associate with an access point. As a result, when passive clients are used, the controller never knows the IP address unless they use the DHCP.
Refer to the exhibit. Each router must be configured with the last usable IP address in the subnet. Which configuration fulfills this requirement?
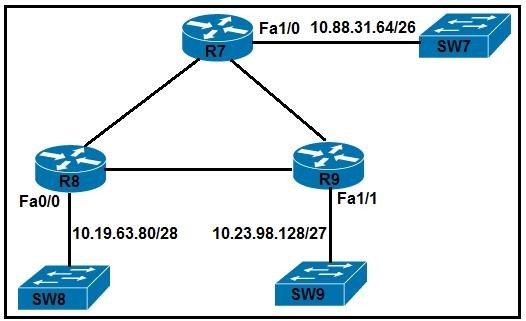
|
A. |
R7# interface FastEthernet1/0 ip address 10.88.31.127 255.255.255.192 R8#
interface FastEthernet0/0 ip address 10.19.63.95 255.255.255.240 R9# interface FastEthernet1/1 ip address
10.23.98.159 255.255.255.224 |
|
B. |
R7# interface FastEthernet1/0 ip address
10.88.31.126 255.255.255.240
R8# interface FastEthernet0/0 ip address 10.19.63.94 255.255.255.192 R9# interface FastEthernet1/1 ip address
10.23.98.158 255.255.255.248 |
|
C. |
R7# interface FastEthernet1/0 ip address 10.88.31.127
255.255.255.240 R8#
interface FastEthernet0/0 ip address 10.19.63.95 255.255.255.192 R9# interface FastEthernet1/1 ip address
10.23.98.159 255.255.255.248 |
|
D. |
R7# interface FastEthernet1/0 ip address 10.88.31.126
255.255.255.192 R8# interface FastEthernet0/0 ip address
10.19.63.94 255.255.255.240 R9# interface FastEthernet1/1 ip address 10.23.98.158 255.255.255.224 |
Answer: D
Refer to the exhibit. All routers in the network are configured. R2 must be the DR. After the engineer connected the devices, R1 was elected as the DR. Which command sequence must be configured on R2 to be elected as the DR in the network?
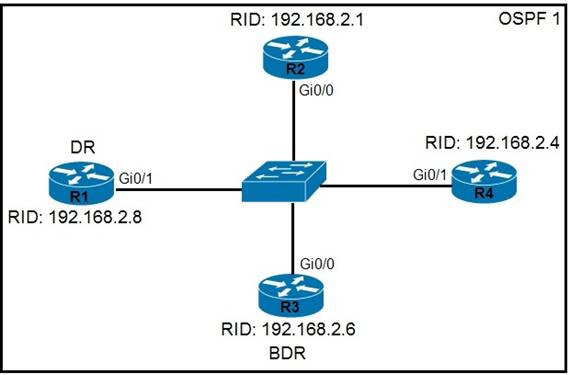
|
A. |
R2(config)#intergface gi0/0 R2(config-if)#ip ospf
priority 100 |
|
B. |
R2(config)#router
ospf 1 R2(config-router)#router-id 192.168.2.7 |
|
C. |
R2(config)#router ospf
1 R2(config-router)#router-id 10.100.100.100 |
|
D. |
R2(config)#intergface
gi0/0 R2(config-if)#ip ospf priority 1 |
Answer:
A
An engineer is configuring data and voice services to pass through the same port. The designated switch interface fastethernet0/1 must transmit packets using the same priority for data when they are received from the access port of the IP phone.
Which configuration must be used?
|
A. |
interface fastethernet0/1 switchport voice
vlan dot1p |
|
B. |
interface
fastethernet0/1 switchport priority extend
cos 7 |
|
C. |
interface fastethernet0/1 switchport voice
vlan untagged |
|
D. |
interface
fastethernet0/1 switchport priority extend
trust |
Answer: D
Explanation:
Set the priority of data traffic received from the Cisco IP Phone access port:
cos value - Configure the "phone" to override the priority received from the "PC or the attached device" with the specified CoS value. The value is a number from 0 to 7, with 7 as the highest priority. The default priority is cos 0.
So, If we set the value 7 here it means, port will prioritize the voice traffic over data traffic.
trust - Configure the phone access port to trust the priority received from the "PC or the attached device".
When traffic from pc is trusted, it will consider both voice and data traffic as same priority. (Since voice traffic is prioritised over data traffic by default.)
Refer to the exhibit. Routers R1 and R2 have been configured with their respective LAN interfaces.
The two circuits are operational and reachable across WAN.
Which command set establishes failover redundancy if the primary circuit goes down?
![]()
|
A. |
R1(config)#ip route 0.0.0.0 0.0.0.0 10.10.10.6 R2(config)#ip route
0.0.0.0 0.0.0.0 10.10.10.5 |
|
B. |
R1(config)#ip route 10.10.13.10 255.255.255.255 10.10.10.2 R2(config)#ip route
192.168.0.100 255.255.255.255 10.10.10.1 |
|
C. |
R1(config)#ip route
10.10.13.10 255.255.255.255 10.10.10.6 R2(config)#ip route
192.168.0.100 255.255.255.255 10.10.10.5 |
|
D. |
R1(config)#ip route
0.0.0.0 0.0.0.0 10.10.10.6 2 R2(config)#ip route 0.0.0.0 0.0.0.0 10.10.10.5 2 |
Answer: D
What is the MAC address used with VRRP as a virtual address?
|
A. |
00-00-0C-07-AD-89 |
|
B. |
00-00-5E-00-01-0a |
|
C. |
00-07-C0-70-AB-01 |
|
D. |
00-C6-41-93-90-91 |
Answer: B
Which port type supports the spanning-tree portfast command without additional configuration?
|
A. |
access ports |
|
B. |
Layer 3 main Interfaces |
|
C. |
Layer 3 suninterfaces |
|
D. |
trunk ports |
Answer:
A
Which type of traffic Is sent with pure iPsec?
|
A. |
broadcast packets from
a switch that
is attempting to locate a MAC address at one of several remote
sites |
|
B. |
multicast traffic from a server
at one site
to hosts at another location |
|
C. |
spanning-tree updates
between switches that
are at two different sites |
|
D. |
unicast messages from
a host at a remote
site to a server at
headquarters |
Answer: D
What are two examples of multifactor authentication? (Choose two.)
|
A. |
single sign-on |
|
B. |
unique user
knowledge |
|
C. |
passwords that
expire |
|
D. |
soft tokens |
|
E. |
shared password responsibility |
Answer: BC
Explanation:
Single sign-on allows users to access multiple applications, websites, resources with one set of login credentials.
It is not a part of a MFA, it actually needs MFA to be secured. A soft (or hard) token can be a part of a MFA
A password that expires can be a part of a MFA
How many bits represent network id in a IPv6 address?
|
A. |
32 |
|
B. |
48 |
|
C. |
64 |
|
D. |
128 |
Answer: C
Lab Simulation 1
Refer to the exhibit.
![]()
Guidelines
This is a lab item in which tasks will be performed on virtual devices.
- Refer to the Tasks tab to view the tasks for this lab item
- Refer to the Topology
tab to access the device
console(s) and perform
the tasks.
-
Console access is available for all required
devices by clicking
the device icon or using
the tab(s) above the console window.
- All necessary preconfiguralions have been applied.
- Do not change the enable password
or hostname for any device.
- Save your configurations to NVRAM before
moving to the next item.
- Click Next at the bottom of the screen to submit
this lab and move to the next
question
- When Next is clicked,
the lab closes and cannot
be reopened
IP connectivity between the three routers is configured. OSPF adjacencies must be established.
1. Configure R1 and R2 Router IDs using the interface IP addresses from the link that is shared
between them.
2. Configure the R2 links with a max value facing R1 and R3. R2 must become the DR. R1 and
R3 links facing R2 must remain with the default OSPF configuration for DR
election. Verify the configuration after clearing the OSPF process.
3. Using a host wildcard
mask, configure all three routers
to advertise their
respective Loopback1 networks.
4. Configure the link between
R1 and R3 to disable
their ability to add other
OSPF routers.
Answer:
on R1
conf terminal interface Loopback0
ip address 10.10.1.1 255.255.255.255
!
interface Loopback1
ip address 192.168.1.1 255.255.255.0
!
interface Ethernet0/0 no shut
ip address 10.10.12.1 255.255.255.0
ip ospf 1 area 0 duplex auto
!
interface Ethernet0/1 no shut
ip address 10.10.13.1 255.255.255.0
ip ospf 1 area 0 duplex auto
!
router ospf 1
router-id 10.10.12.1
network 10.10.1.1 0.0.0.0 area 0
network 192.168.1.0 0.0.0.255 area 0
!
copy run star
![]()
On R2
conf terminal interface Loopback0
ip address 10.10.2.2 255.255.255.255
!
interface Loopback1
ip address 192.168.2.2 255.255.255.0
!
interface Ethernet0/0 no shut
ip address 10.10.12.2 255.255.255.0
ip ospf priority 255 ip ospf 1 area 0 duplex auto
!
interface Ethernet0/2 no shut
ip address 10.10.23.2 255.255.255.0
ip ospf priority 255 ip ospf 1 area 0 duplex auto
!
router ospf 1
network 10.10.2.2 0.0.0.0 area 0
network 192.168.2.0 0.0.0.255 area 0
!
copy runs start
![]()
On R3
conf ter
interface Loopback0
ip address 10.10.3.3 255.255.255.255
!
interface Loopback1
ip address 192.168.3.3 255.255.255.0
!
interface Ethernet0/1 no shut
ip address 10.10.13.3 255.255.255.0
ip ospf 1 area 0 duplex auto
!
interface Ethernet0/2 no shut
ip address 10.10.23.3 255.255.255.0
ip ospf 1 area 0 duplex auto
!
router ospf 1
network 10.10.3.3 0.0.0.0 area 0
network 192.168.3.0 0.0.0.255 area 0
!
copy run start
!
Lab Simulation 2
Physical connectivity is implemented between the two Layer 2 switches, and the network connectivity between them must be configured:
1. Configure an LACP EtherChannel and number it as 1; configure it between switches
SW1 and SVV2 using interfaces
Ethernet0/0 and Ethernet0/1 on both sides. The LACP mode must match on both
ends.
2 Configure the EtherChannel as a trunk link.
3. Configure the trunk link with 802.1
q tags.
4. Configure the native VLAN of the EtherChannel as VLAN 15.
![]()
Answer:
On SW1:
conf terminal vlan 15
exit
interface range eth0/0 - 1 channel-group 1 mode active exit
interface port-channel 1
switchport trunk encapsulation dot1q switchport mode trunk
switchport trunk native vlan 15 end
copy run start
on SW2:
conf terminal vlan 15
exit
interface range eth0/0 - 1 channel-group 1 mode active exit
interface port-channel 1
switchport trunk encapsulation dot1q switchport mode trunk
switchport trunk native vlan 15 end
copy run start
Lab Simulation 3
Configure IPv4 and IPv6 connectivity between two routers. For IPv4, use a /28 network from the 192.168.1.0/24 private range. For IPv6, use the first /64 subnet from the 2001:0db8:aaaa::/48 subnet.
1. Using Ethernet0/1 on routers
R1 and R2, configure the next usable/28
from the 192.168.1.0/24 range. The network
192.168.1.0/28 is unavailable.
2. For the IPv4 /28 subnet, router
R1 must be configured with the first usable host address.
3. For the IPv4 /28 subnet, router
R2 must be configured with the last usable host address.
4. For the IPv6 /64 subnet, configure
the routers with the IP addressing provided
from the topology.
5. A ping must work between the routers on the IPv4 and IPv6 address ranges.
![]()
Answer:
on R1
config terminal
ipv6 unicast-routing inter eth0/1
ip addre 192.168.1.1 255.255.255.240
ipv6 addre 2001:db8:aaaa::1/64
not shut end
copy running start
on R2
config terminal
ipv6 unicast-routing inter eth0/1
ip address 192.168.1.14 255.255.255.240
ipv6 address 2001:db8:aaaa::2/64 not shut
end
copy running start
![]()
for test from R1
ping ipv6 2001:db8:aaaa::1
for test from R2
ping ipv6 2001:db8:aaaa::2
Lab Simulation 4
Connectivity between four routers has been established. IP connectivity must be configured in the order presented to complete the implementation. No dynamic routing protocols are included.
1. Configure static
routing using host routes to establish connectivity from router R3 to the router
R1 Loopback address using the source IP of 209.165.200.230.
2. Configure an IPv4 default
route on router
R2 destined for router R4.
3.
Configure an IPv6 default router
on router R2 destined for router R4.
![]()
Answer:
1.- on R3
config terminal
ip route 192.168.1.1 255.255.255.255 209.165.200.229
end
copy running start
2.- on R2
config terminal
ip route 0.0.0.0 0.0.0.0 209.165.202.130
end
copy running start
3.- on R2
config terminal
ipv6 route ::/0 2001:db8:abcd::2 end
copy running start
Lab Simulation 5
All physical cabling between the two switches is installed. Configure the network connectivity between the switches using the designated VLANs and interfaces.
1. Configure VLAN 100 named
Compute and VLAN 200 named
Telephony where required
for each task.
2. Configure Ethernet0/1 on SW2 to use the existing VLAN named Available.
3.
Configure the connection between the switches
using access ports.
4. Configure Ethernet0/1 on SW1 using
data and voice VLANs.
5. Configure Ethemet0/1 on SW2 so that the Cisco proprietary neighbor discovery protocol
is turned off for the designated interface only.
![]()
Answer:
on sw1 enable conf t vlan 100
name Compute vlan 200
name Telephony int e0/1
switchport voice vlan 200 switchport access vlan 100
int e0/0
switchport mode access do wr
on sw2 Vlan 99
Name Available Int e0/1
Switchport access vlan 99 do wr
Lab Simulation 6
Refer to the exhibit.
![]()
Three switches must be configured for Layer 2 connectivity. The company requires only the designated VLANs to be configured on their respective switches and permitted accross any links between switches for security purposes. Do not modify or delete VTP configurations.
The network needs two user-defined VLANs configured:
VLAN 110: MARKETING
VLAN 210: FINANCE
1. Configure the VLANs on the designated switches and assign
them as access ports to the
interfaces connected to the PCs.
2. Configure the e0/2 interfaces on Sw1 and Sw2 as 802.1q trunks
with only the required VLANs permitted.
3. Configure the e0/3 interfaces on Sw2 and Sw3 as 802.1q trunks
with only the required VLANs permitted.
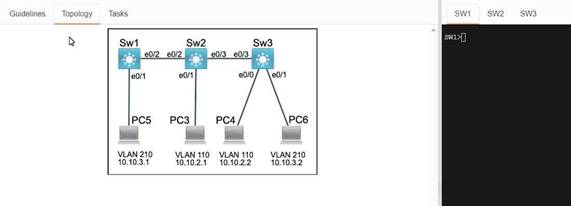
Answer:
Sw1 enbale config t Vlan 210
Name FINANCE
Inter e0/1
Switchport access vlan 210 do wr
Sw2 Enable config t Vlan 110
Name MARKITING
Int e0/1
Switchport acees vlan 110 do wr
Sw3 Enable config t Vlan 110
Name MARKITING
Vlan 210
Name FINANCE
Int e0/0
Switchport access vlan 110 Int e0/1
Switchport access vlan 210
Sw1 Int e0/1
Switchport allowed vlan 210
Sw2 Int e0/2
Switchport trunk allowed vlan 210 Sw3
Int e0/3
Switchport trunk allowed vlan 210 Switchport trunk allowed vlan 210,110
Lab Simulation 7
![]()
Connectivity between three routers has been established, and IP services must be configured jn the order presented to complete the implementation Tasks assigned include configuration of NAT, NTP, DHCP, and SSH services.
1. All traffic sent from R3 to the R1 Loopback address must be configured for NAT on R2. All source addresses must be translated from R3 to the IP address of Ethernet0/0 on R2, while using only a standard access list named NAT To verify, a ping must be successful to the R1 Loopback address sourced from R3. Do not use NVI NAT configuration.
2. Configure R1 as an NTP server
and R2 as a client,
not as a peer, using the IP address of the
R1 Ethernet0/2 interface. Set the clock on the NTP server for midnight on
January 1, 2019.
3. Configure R1 as a DHCP server for the network 10.1.3.0/24 in a pool named TEST. Using
a single command, exclude
addresses 1-10 from the range. Interface Ethernet0/2 on R3 must be
issued the IP address of 10.1.3.11 via DHCP.
4. Configure SSH connectivity from R1 to R3, while excluding access
via other remote
connection protocols. Access for user root and password Cisco must be
set on router R3 using RSA and
1024 bits. Verify connectivity using an SSH session from router R1 using a destination address of
10.1.3.11. Do NOT modify console access or line numbers to accomplish this task.
Answer:
conf t
R1(config)#ntp master 1
R2(config)#ntp server 10.1.2.1 Exit
Router#clock set 00:00:00 jan 1 2019 ip dhcp pool TEST
network 10.1.3.0 255.255.255.0
ip dhcp exluded-address 10.1.3.1 10.1.3.10 R3(config)#int e0/3
R3(config)#int e0/2 ip address dhcp no shut
crypto key generate RSA Copy run start
Lab Simulation 8
Refer to the exhibit.
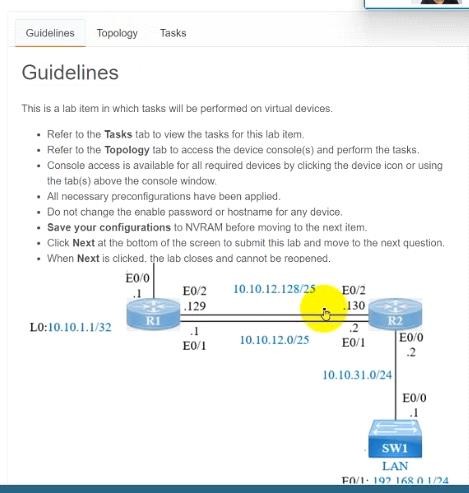
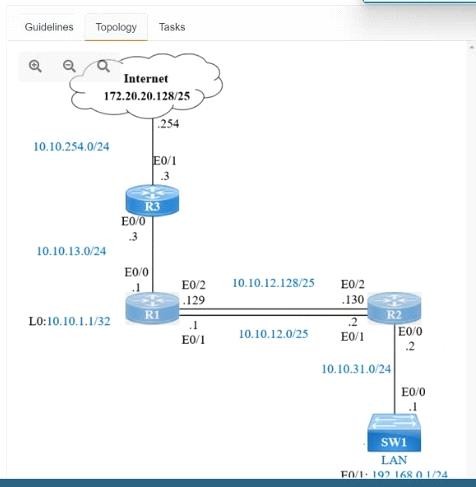
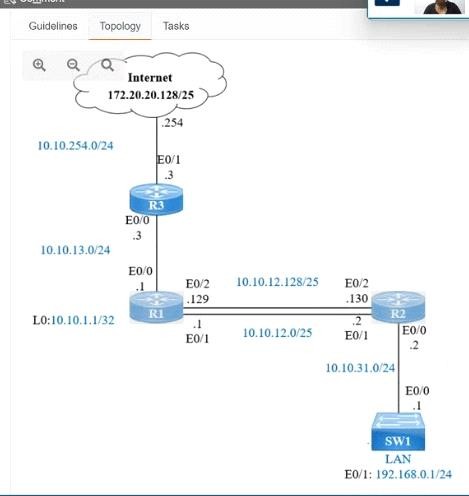
IP connectivity and OSPF are preconfigured on all devices where necessary. Do not make any changes to the IP addressing or OSPF. The company policy uses connected interfaces and next hops when configuring static routes except for load balancing or redundancy without floating static. Connectivity must be established between subnet 172.20.20.128/25 on the Internet and the LAN at 192.168.0.0/24 connected to SW1:
1.
Configure reachability to the switch
SW1 LAN subnet in router
R2.
2. Configure default
reachability to the Internet subnet in router R1.
3. Configure a single static route in router R2 to reach
to the Internet subnet considering both redundant links between routers R1 and R2. A default route
is NOT allowed in router R2.
4. Configure a static route in router
R1 toward the switch SW1 LAN subnet where the primary link must be through Ethernet0/1. and the
backup link must be through Ethernet0/2 using a floating route. Use the minimal
administrative distance value when required.
Answer:
On R2:
Enable Conf t
Ip route 192.168.1.0 255.255.255.0 10.10.31.1
On R1:
Enable
Conf t
Ip route 0.0.0.0 0.0.0.0 10.10.13.3
On R2
Ip route 172.20.20.128 255.255.255.128 e0/2
Ip route 172.20.20.128 255.255.255.128 e0/1
On R1
Ip route 192.168.0.0 255.255.255.0 e0/1
Ip route 192.168.0.0 255.255.255.0 10.10.12.2 3
Save all configurations after every router from anyone of these command Do wr Or
Copy run start
Drag and Drop Question
Drag and drop the HTTP methods used with REST-Based APIs from the left onto the descriptions on the right.
![]()
Answer:
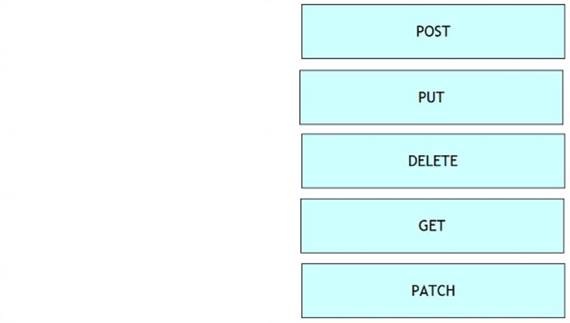
Explanation:
The most commonly used HTTP methods POST, GET, PUT, PATCH, DELETE are similar to CURD (create, update, read, delete) operations in the database. Just try to remember below the key Points:
![]() Create
NEW record =>POST
Create
NEW record =>POST ![]() read=>GET
read=>GET
![]() If the record exists
then update else create a new record=>PUT
If the record exists
then update else create a new record=>PUT ![]() update/modify=>PATCH
update/modify=>PATCH
![]() delete=>DELETE
delete=>DELETE
Which WAN topology is most appropriate for a centrally located server farm with several satellite branches?
|
A. |
star |
|
B. |
hub and spoke |
|
C. |
point-to-point |
|
D. |
full mesh |
Answer:
B
Which two types of information are held in the mac address table ?
|
A. |
destination ip addresses |
|
B. |
protocols |
|
C. |
port numbers |
|
D. |
mac address |
|
E. |
source ip address |
Answer: CD
Which three options are benefits of using TACACS+ on a device? (Choose three)
|
A. |
It ensures that
user activity is untraceable |
|
B. |
It provides a secure
accounting facility on the device. |
|
C. |
device-administration packets
are encrypted in their entirely. |
|
D. |
It allows the user
to remotely access
devices from other
vendors. |
|
E. |
It allows the users
to be authenticated against a remote
server. |
|
F. |
It supports access-level authorization for commands. |
Answer: CEF
What layer of the OSI Model is included in TCP/IP Model's INTERNET layer?
|
A. |
Application |
|
B. |
Session |
|
C. |
Data Link |
|
D. |
Presentation |
|
E. |
Network |
Answer: E
A security administrator wants to profile endpoints and gain visibility into attempted authentications. Which 802.1x mode allows these actions?
|
A. |
Monitor mode |
|
B. |
High-Security mode |
|
C. |
Low-impact mode |
|
D. |
Closed mode |
Answer:
A
How to verify SSH connections was secured?
|
A. |
ssh -v 1 -l admin
IP |
|
B. |
ssh -v 2 -l admin IP |
|
C. |
ssh -l admin
IP |
Answer:
B
How many usable host are there per subnet if you have the address of 192.168.10.0 with a
subnet mask of 255.255.255.240?
|
A. |
4 |
|
B. |
8 |
|
C. |
16 |
|
D. |
14 |
Answer: D
What interconnection cable can you use when you use a MDI connection?
|
A. |
cut-through |
|
B. |
straight-through |
|
C. |
crossover |
|
D. |
rollover |
Answer: C
which command is used to know the duplex speed of serial link?
|
A. |
show line |
|
B. |
show interface |
|
C. |
show protocol |
|
D. |
show run |
Answer:
B
When troubleshooting client DNS issues, which two tasks must you perform? (Choose two)
|
A. |
Ping a public
website IP address. |
|
B. |
Ping the
DNS Server. |
|
C. |
Determine whether a DHCP address has been assigned. |
|
D. |
Determine whether
the hardware address
is correct. |
|
E. |
Determine whether the
name servers have
been configured |
Answer: BE
Explanation:
In order for DNS to work you have to have a name server configured (either statically or dynamically) and you must be able to reach it (which, presumably, could be verified via ping).
What does traffic shaping do to reduce congestion in a network?
|
A. |
buffers and queues
packets |
|
B. |
buffers without queuing packets |
|
C. |
queqes without buffering packets |
|
D. |
drops packets |
Answer:
A
Which NTP type designates a router without an external referee clock as an authoritative time source ?
|
A. |
Client |
|
B. |
Server |
|
C. |
peer |
|
D. |
master |
Answer: D
Which statement about SNMPv2 is true?
|
A. |
Its privacy algorithms use MD5 encryption by default. |
|
B. |
it requires passwords to be encrypyed |
|
C. |
Its authetication and privacy
algorithms are enable
without default values. |
|
D. |
It requires passwords at least eight
characters en length. |
Answer: C
which type of IP address of ipv6 that also exist in IPv4 but barely used?
|
A. |
unicast |
|
B. |
multicast |
|
C. |
anycast |
|
D. |
broadcast |
Answer: C
What are two characteristics of Telnet? (Choose two.)
|
A. |
It sends data
in clear text
format. |
|
B. |
It is no longer
supported on Cisco
network devices. |
|
C. |
It is more secure
than SSH. |
|
D. |
It requires an enterprise license in order
to be implemented. |
|
E. |
It requires that
the destination device
be configured to support Telnet
connections. |
Answer: AE
Which type of broadcast barely used in IPv4 which also exist in IPv6 like?
|
A. |
unicast |
|
B. |
multicast |
|
C. |
broadcast |
|
D. |
anycast |
Answer: D
When troubleshooting ethernet connectivity issues how can you verify that an ip address is known to a router?
|
A. |
Check Whether the ip address is in the
routing table |
|
B. |
Check Whether an ACL is blocking the
ip address |
|
C. |
Check Whether the ip address
is in the CAM Table |
|
D. |
Check Whether the ip address
is in the ARP Table |
Answer: D
Which command can you enter to verify that a router is synced with a configures time source?
|
A. |
show ntp authenticate |
|
B. |
ntp associations |
|
C. |
ntp server time |
|
D. |
ntp authenticate |
|
E. |
show ntp associations |
Answer:
E
What are the two minimum required components of a DHCP binding? (Choose two.)
|
A. |
a DHCP pool |
|
B. |
an exclusion list |
|
C. |
a hardware address |
|
D. |
an IP address |
|
E. |
an ip-helper statement |
Answer: CD
Which path does a router choose when it receives a packet with multiple possible paths to the destination over different routing protocols?
|
A. |
the path with
both the lowest
administrative distance and the highest metric |
|
B. |
the path with the lowest administrative distance |
|
C. |
the path with
the lowest metric |
|
D. |
the path with
both the lowest
administrative distance and lowest metric |
Answer:
B
Which two statements about firewalls are true ?
|
A. |
They can be used with
an intrusion prevention system |
|
B. |
They can
limit unauthorized user access to protect data |
|
C. |
Each wireless access point requires its own firewall |
|
D. |
They must
be placed only
at locations where
the private network connects to the
internet |
|
E. |
They can prevent attacks from the
internet only |
Answer: AB
Which two statements about data VLANs on access ports are true ? ( Choose two)
|
A. |
They can be configured as trunk ports |
|
B. |
Two or more VLANs
can be configured on the interface |
|
C. |
802.1Q encapsulation must be configured on the interface |
|
D. |
Exactly one VLAN can be configured on the interface. |
|
E. |
They can be configured as host ports. |
Answer: DE
Where does the configuration reside when a helper address is configured to support DHCP ?
|
A. |
on the switch
trunk interface. |
|
B. |
on the router closest to the client. |
|
C. |
on the router closest
to the server. |
|
D. |
on every router
along the path. |
Answer:
B
How does NAT overloading provide one-to-many address translation?
|
A. |
It uses a pool of addresses |
|
B. |
It converts IPV4 addresses to unused IPv6
Addresses |
|
C. |
It assigns a unique
TCP/UDP port to each session |
|
D. |
It uses virtual MAC Address and Virtual IP Addresses |
Answer: C
Which IEEE mechanism is responsible for the authentication of devices when they attempt to
connect to a local network?
|
A. |
802.1x |
|
B. |
802.11 |
|
C. |
802.2x |
|
D. |
802.3x |
Answer: A
If router R1 knows a static route to a destination network and then learns about the same destination network through a dynamic routing protocol, how does R1 respond?
|
A. |
It refuses to advertise the dynamic route
to other neighbors |
|
B. |
It sends a withdrawal signal to the
neighboring router |
|
C. |
It disables the routing
protocol |
|
D. |
It prefers
the static route |
Answer: D
Explanation:
By default the administrative distance of a static route is 1, meaning it will be preferred over all dynamic routing protocols. If you want to have the dynamic routing protocol used and have the static route be used only as a backup, you need to increase the AD of the static route so that it is higher than the dynamic routing protocol.
Which two statements about floating static routes are true? (Choose two)
|
A. |
They are routes
to the exact
/32 destination address |
|
B. |
They are used when a route
to the destination network is missing |
|
C. |
They have
a higher administrative distance than the default static
route administrative distance |
|
D. |
They are
used as back-up routes when the
primary route goes down |
|
E. |
They are dynamic
routes that are learned from
a server |
Answer: CD
When you enable PortFast on a switch port, the port immediately transitions to which state?
|
A. |
Blocking |
|
B. |
Forwarding |
|
C. |
Learning |
|
D. |
Listening |
Answer:
B
When is the most appropriate time to escalate an issue that you are troubleshooting?
|
A. |
when you lack
proper resources to resolve the
issue |
|
B. |
when you have gathered all available information about the issue |
|
C. |
when you
have been unable
to resolve the
issue after 30 minutes |
|
D. |
when a more
urgent issue that
requires your intervention is detected |
Answer: B
What is the command to see assigned address in DHCP?
|
A. |
show ip DHCP
statistic |
|
B. |
show ip dhcp pool |
|
C. |
show ip dhcp binding |
|
D. |
show ip dhcp
database |
Answer: C
Refer to the exhibit, you determine that Computer A cannot ping Computer Which reason for the problem is most likely true?
![]()
|
A. |
The Subnet mask
for Computer A is incorrect |
|
B. |
The default gateway address
for Computer A is incorrect |
|
C. |
The subnet mask for computer B is incorrect. |
|
D. |
The default gateway
address for computer B is incorrect |
Answer:
A
For which two protocols can PortFast alleviate potential host startup issues? (Choose two.)
|
A. |
DHCP |
|
B. |
DNS |
|
C. |
OSPF |
|
D. |
RIP |
|
E. |
CDP |
Answer:
AB
Which three encapsulation layers in the OSI model are combined into the TCP/IP application layer? (Choose three)
|
A. |
Session |
|
B. |
transport |
|
C. |
presentation |
|
D. |
application |
|
E. |
data-link |
|
F. |
network |
Answer:
ACD
When is the most appropriate time to escalate an issue that you troubleshooting?
|
A. |
When you lack
the proper to resolve the
issue. |
|
B. |
When a more urgent
issue that requires your intervention is
detected |
|
C. |
When you
have gathered all information about
an issue |
|
D. |
When you have
been unable to resolve the issue after
30 min |
Answer: C
Which two command can you enter to display the current time sources statistics on devices ? (Choose two)
|
A. |
Show ntp associations. |
|
B. |
Show clock
details |
|
C. |
Show clock. |
|
D. |
Show time. |
|
E. |
Show ntp status |
Answer: AE
Which command can you enter in a network switch configuration so that learned mac addresses are saved in configuration as they connect ?
|
A. |
Switch(confg-if)#Switch port-security |
|
B. |
Switch(confg-if)#Switch port-security Mac-address sticky |
|
C. |
Switch(confg-if)#Switch port-security maximum 10 |
|
D. |
Switch(confg-if)#Switch mode access |
Answer:
B
Which statement about snmpv2 is true?
|
A. |
it requires password at least eight
characters in length |
|
B. |
it requires passwords to be encrypted |
|
C. |
its privacy algorithms use md5 encryption by default |
|
D. |
its authentic and privacy algorithms are enabled without
default values |
Answer: D
Which two steps must you perform to enable router-on-a-stick on a switch? (Choose two.)
|
A. |
Configure an IP route to the VLAN
destination network. |
|
B. |
Connect the
Router to a trunk port. |
|
C. |
Configure full
duplex. |
|
D. |
Configure the subinterface number
exactly the same as the matching VLAN. |
|
E. |
Assign the access
port to a VLAN. |
Answer:
BE
Which feature can you use to restrict SNMP queries to a specific OID tree?
|
A. |
server group |
|
B. |
a community |
|
C. |
a view record |
|
D. |
an access group |
Answer: C
In which two circumstances are private IPv4 addresses appropriate? (Choose two)
|
A. |
on internal hosts
that stream data
solely to external resources |
|
B. |
on hosts that communicates only with other
internal hosts |
|
C. |
on the public-facing interface of a firewall |
|
D. |
on hosts that require
minimal access to external resources |
|
E. |
to allow hosts
inside an enterprise to communicate in both directions with hosts outside
the enterprise |
Answer:
BD
Which NTP command configures the local device as an NTP reference clock source?
|
A. |
ntp peer |
|
B. |
ntp broadcast |
|
C. |
ntp master |
|
D. |
ntp server |
Answer: C
Which statement about static routes is true?
|
A. |
The source interface can be configured to make routing
decisions. |
|
B. |
A subnet mask is entered for the next-hop address. |
|
C. |
The subnet mask is 255.255 255.0
by default |
|
D. |
The exit interface can be specified to indicate where
the packets will
be routed. |
Answer: D
Explanation:
Static routing can be used to define an exit point from a router when no other routes are available or necessary. This is called a default route.
In which two situations should you use out-of-band management?
|
A. |
when a network
device fails to forward packets |
|
B. |
when you require ROMMON
access |
|
C. |
when management applications need concurrent access to the
device |
|
D. |
when you require administrator access from multiple locations |
|
E. |
when the control
plane fails to respond |
Answer: AB
What happens when an 802.11a node broadcasts within the range of an 802.11g access point?
|
A. |
The access point
transmits, but the node is unable to receive. |
|
B. |
A connection occurs |
|
C. |
Both the node and the access
point are unable
to transmit. |
|
D. |
The node transmits, but the access
point is unable
to receive. |
Answer: D
Which value indicate the distance from the ntp authoritative time source?
|
A. |
priority |
|
B. |
location |
|
C. |
layer |
|
D. |
stratum |
Answer: D
Which NTP type designates a router without an external reefrence clock as an authoritative time source?
|
A. |
server |
|
B. |
peer |
|
C. |
master |
|
D. |
client |
Answer: C
Which 3 feature are represented by A letter in AAA? (Choose Three)
|
A. |
authorization |
|
B. |
accounting |
|
C. |
authentication |
|
D. |
accountability |
|
E. |
accessibility |
|
F. |
authority |
Answer:
ABC
Which component of a routing table entry represents the subnet mask?
|
A. |
routing protocol code |
|
B. |
prefix |
|
C. |
metric |
|
D. |
network mask |
Answer: D
Which two tasks can help you gather relevant facts when you troubleshoot a network problem? (Choose two)
|
A. |
Eliminate known issues
first |
|
B. |
Define the
problem in terms
of symptoms and causes |
|
C. |
Ask questions of the users who are affected by the problem |
|
D. |
Change one setting
or component and then analyze
the result |
|
E. |
Collect technical data from network
management systems and logging servers |
Answer:
BE
Which NTP command configures the local devices as an NTP reference clock source?
|
A. |
NTP Peer |
|
B. |
NTP Broadcast |
|
C. |
NTP Master |
|
D. |
NTP Server |
Answer: C
Which two statements about wireless LAN controllers are true? (Choose two.)
|
A. |
They can simplify the management and deployment of wireless LANs. |
|
B. |
They rely
on external firewalls for WLAN security. |
|
C. |
They are
best suited to smaller wireless networks. |
|
D. |
They must
be configured through
a GUI over HTTP or HTTPS. |
|
E. |
They can manage
mobility policies at a systemwide level. |
Answer: AE
Which command is necessary to permit SSH or Telnet access to a cisco switch that is otherwise configured for these vty line protocols?
|
A. |
transport type all |
|
B. |
transport output
all |
|
C. |
transport preferred all |
|
D. |
transport input all |
Answer: D
Which two statements about TACACS+ are true? (Choose two.)
|
A. |
It can run
on a UNIX server. |
|
B. |
It authenticates against the user database on the local
device. |
|
C. |
It is more secure
than AAA authentication. |
|
D. |
It is enabled on Cisco routers
by default. |
|
E. |
It uses a managed database. |
Answer: AE
Which two statements correctly describe RADIUS? (Choose two)
|
A. |
It separates authentication, authorization, and accounting functions |
|
B. |
It uses TCP
as its transport protocol |
|
C. |
It encrypts only the
password |
|
D. |
It combines authentication and authorization |
|
E. |
I can authorize specific router commands |
Answer: CD
Which API use HTTP meddages to tansfer data to applications residing on different host ?
|
A. |
OpFlex |
|
B. |
REST |
|
C. |
OpenStack |
|
D. |
OpenFlow |
Answer:
B
Which command can you enter on a Cisco IOS device to enable a scheduled algorithm that directs lookup calls to multiple DNS hosts?
|
A. |
ip domain round-robin |
|
B. |
ip name-server 192.168.10.14 192.168.10.15 |
|
C. |
ip domain lookup |
|
D. |
ip domain list |
Answer: B
Which two services can be provided by a wireless controller? (Choose two)
|
A. |
issuing IP addresses to wired devices |
|
B. |
mitigating threats from the internet |
|
C. |
providing authentication services to users |
|
D. |
managing interference in a dense
network |
|
E. |
Layer 3 routing
between wired and wireless devices |
Answer: CD
Which two statements correctly describe distance-vector routing protocols? (Choose two)
|
A. |
they specify the next hop toward the destination subnet |
|
B. |
they require quick network convergence to support normal
operations |
|
C. |
they generate a complete topology of the network |
|
D. |
they update other
devices on the
network when one
device detects a topogy chage |
|
E. |
they use a variety of metrics to identify the distance to a destination network. |
Answer: AE
Which type of access list compares source and destination IP address?
|
A. |
standard |
|
B. |
extended |
|
C. |
IP named |
|
D. |
reflexive |
Answer:
B
Which two descriptions of TACACS+ are true? (Choose two.)
|
A. |
It encrypts only
the password. |
|
B. |
It uses UDP as its transport protocol. |
|
C. |
It separates authentication authorization, and accounting functions. |
|
D. |
It can authorize specific router commands. |
|
E. |
It combines authentication and authorization |
Answer: CD
What are two enhancements that OSPFv3 supports over OSPFv2? (Choose two.)
|
A. |
It requires the
use of ARP. |
|
B. |
It can support multiple IPv6 subnets on a single
link. |
|
C. |
It supports up to 2 instances of OSPFv3 over
a common link. |
|
D. |
It routes over
links rather than over networks. |
Answer:
BD
When a router undergoes the exchange protocol within OSPF, in what order does it pass through each state?
|
A. |
exstart state
> loading state
> exchange state
> full state |
|
B. |
exstart state >
exchange state >
loading state >
full state |
|
C. |
exstart state >
full state >
loading state >
exchange state |
|
D. |
loading state
> exchange state
> full state
> exstart state |
Answer:
B
A network administrator creates a layer 3 EtherChannel, bundling four interfaces into channel group 1. On what interface is the IP address configured?
|
A. |
the port-channel 1 interface |
|
B. |
the highest number member
interface |
|
C. |
all member interfaces |
|
D. |
the lowest number
member interface |
Answer: A
Refer to the exhibit. If the router Cisco returns the given output and has not had its router ID set manually, what value will OSPF use as its router ID?
![]()
|
A. |
192.168.1.1 |
|
B. |
172.16.1.1 |
|
C. |
1.1.1.1 |
|
D. |
2.2.2.2 |
Answer: D
What command sequence will configure a router to run OSPF and add network 10.1.1.0 /24 to area 0?
|
A. |
router ospf area
0 network 10.1.1.0 255.255.255.0 area 0 |
|
B. |
router ospf network 10.1.1.0 0.0.0.255 |
|
C. |
router ospf 1 network 10.1.1.0 0.0.0.255 area
0 |
|
D. |
router ospf area 0 network 10.1.1.0 0.0.0.255 area
0 |
|
E. |
router ospf network 10.1.1.0 255.255.255.0 area 0 |
|
F. |
router ospf 1 network 10.1.1.0 0.0.0.255 |
Answer: C
What OSPF command, when configured, will include all interfaces into area 0?
|
A. |
network 0.0.0.0 255.255.255.255 area 0 |
|
B. |
network 0.0.0.0 0.0.0.0 area 0 |
|
C. |
network 255.255.255.255 0.0.0.0 area 0 |
|
D. |
network all-interfaces area
0 |
Answer:
A
Which statement describes the process ID that is used to run OSPF on a router?
|
A. |
It is globally significant and is used to represent the
AS number. |
|
B. |
It is locally significant and is used to identify an instance of the OSPF
database. |
|
C. |
It is globally significant and is used
to identify OSPF stub areas. |
|
D. |
It is locally
significant and must
be the same
throughout an area. |
Answer:
B
Which three are the components of SNMP? (Choose three)
|
A. |
MIB |
|
B. |
SNMP Manager |
|
C. |
SysLog Server |
|
D. |
SNMP Agent |
|
E. |
Set |
Answer:
ABD
What is the alert message generated by SNMP agents called ?
|
A. |
TRAP |
|
B. |
INFORM |
|
C. |
GET |
|
D. |
SET |
Answer: AB
Explanation:
A TRAP is a SNMP message sent from one application to another (which is typically on a remote host). Their purpose is merely to notify the other application that something has happened, has been noticed, etc. The big problem with TRAPs is that they're unacknowledged so you don't actually know if the remote application received your oh-so-important message to it. SNMPv2 PDUs fixed this by introducing the notion of an INFORM, which is nothing more than an acknowledged TRAP.
Which three features are added in SNMPv3 over SNMPv2?
|
A. |
Message Integrity |
|
B. |
Compression |
|
C. |
Authentication |
|
D. |
Encryption |
|
E. |
Error Detection |
Answer:
ACD
Which additional configuration step is necessary in order to connect to an access point that has SSID broadcasting disabled?
|
A. |
Set the SSID
value in the
client software to public. |
|
B. |
Configure open
authentication on the AP and the client. |
|
C. |
Set the SSID value
on the client
to the SSID configured on the AP. |
|
D. |
Configured MAC address filtering to permit
the client to connect to the AP. |
Answer: C
What are two characteristics of SSH? (Choose two.)
|
A. |
most common remote-access method |
|
B. |
unsecured |
|
C. |
encrypted |
|
D. |
uses port 22 |
|
E. |
operates at the
transport layer |
Answer: CD
As a CCNA candidate, you must have a firm understanding of the IPv6 address structure. Refer to IPv6 address, could you tell me how many bits are included in each filed?
|
A. |
24 |
|
B. |
4 |
|
C. |
3 |
|
D. |
16 |
Answer: D
Which name describes an IPV6 host-enable tunneling technique that uses IPV4 UDP,does not require dedicated gateway tunnels,and can pass through existing IPV4 NAT gateways?
|
A. |
dual stack |
|
B. |
dynamic |
|
C. |
Teredo |
|
D. |
Manual 6to4 |
Answer: C
Assuming a subnet mask of 255.255.248.0, three of the following addresses are valid host addresses. Which are these addresses? (Choose three.)
|
A. |
172.16.9.0 |
|
B. |
172.16.8.0 |
|
C. |
172.16.31.0 |
|
D. |
172.16.20.0 |
Answer:
ACD
In which situation would the use of a static route be appropriate?
|
A. |
To configure a route to the first
Layer 3 device
on the network segment. |
|
B. |
To configure a route
from an ISP router into
a corporate network. |
|
C. |
To configure a route
when the administrative distance of the
current routing protocol is too low. |
|
D. |
To reach a network is more than
15 hops away. |
|
E. |
To provide access
to the Internet for enterprise hosts. |
Answer:
B
Which of the following services use UDP? (Choose three.)
|
A. |
Telnet |
|
B. |
TFTP |
|
C. |
SNMP |
|
D. |
DNS |
|
E. |
SMTP |
|
F. |
HTTP |
Answer:
BCD
If a router has four interfaces and each interface is connected to four switches, how many broadcast domains are present on the router?
|
A. |
1 |
|
B. |
2 |
|
C. |
4 |
|
D. |
8 |
What is the correct routing match to reach 172.16.1.5/32?
|
A. |
172.16.1.0/26 |
|
B. |
172.16.1.0/25 |
|
C. |
172.16.1.0/24 |
|
D. |
the default route |
Answer:
A
Which technology allows a large number of private IP addresses to be represented by a smaller number of public IP addresses?
|
A. |
NAT |
|
B. |
NTP |
|
C. |
RFC 1631 |
|
D. |
RFC 1918 |
Answer:
A
What is the effect of the overload keyword in a static NAT translation configuration?
|
A. |
It enables
port address translation. |
|
B. |
It enables the use of a secondary pool of IP addresses when the first
pool is depleted. |
|
C. |
It enables the inside
interface to receive traffic. |
|
D. |
It enables the outside interface to forward traffic. |
Answer:
A
Which technology can enable multiple VLANs to communicate with one another?
|
A. |
inter-VLAN routing
using a Layer
3 switch |
|
B. |
inter-VLAN
routing using a Layer 2 switch |
|
C. |
intra-VLAN routing using router on a stick |
|
D. |
intra-VLAN routing using a Layer
3 switch |
Answer:
A
Which command can you enter to set the default route for all traffic to an interface?
|
A. |
router(config)#ip
route 0.0.0.0 0.0.0.0 GigabitEthernet0/1 |
|
B. |
router(config)#ip
route 0.0.0.0 255.255.255.255 GigabitEthernet0/1 |
|
C. |
router(config-router)#default-information originate |
|
D. |
router(config-router)#default-information originate always |
Answer:
A
Which two types of NAT addresses are used in a Cisco NAT device? (Choose two.)
|
A. |
inside local |
|
B. |
inside global |
|
C. |
inside private |
|
D. |
outside private |
|
E. |
external global |
|
F. |
external local |
Answer:
AB
What is the danger of the permit any entry in a NAT access list?
|
A. |
It can lead
to overloaded resources on the router. |
|
B. |
It can cause too many addresses to be assigned to the same
interface. |
|
C. |
It can disable the
overload command. |
|
D. |
It prevents the correct translation of IP addresses on the inside
network. |
Answer: A
Refer to the exhibit. What is the effect of the given configuration?
![]()
|
A. |
It configures an inactive switch
virtual interface. |
|
B. |
It configures an active
management interface. |
|
C. |
It configures the native
VLAN. |
|
D. |
It configures the
default VLAN. |
Answer:
A
Which command can you enter to view the ports that are assigned to VLAN 20?
|
A. |
Switch#show vlan id 20 |
|
B. |
Switch#show ip interface brief |
|
C. |
Switch#show interface vlan 20 |
|
D. |
Switch#show ip interface vlan 20 |
Answer: A
If primary and secondary root switches with priority 16384 both experience catastrophic losses, which tertiary switch can take over?
|
A. |
a switch
with priority 20480 |
|
B. |
a switch with priority 8192 |
|
C. |
a switch with priority 4096 |
|
D. |
a switch
with priority 12288 |
Answer:
A
Which two features can dynamically assign IPv6 addresses? (Choose two.)
|
A. |
IPv6 stateless autoconfiguration |
|
B. |
DHCP |
|
C. |
NHRP |
|
D. |
IPv6 stateful autoconfiguration |
|
E. |
ISATAP tunneling |
Answer:
AD
What is the default port-security behavior on a trunk link?
|
A. |
It causes a network loop
when a violation occurs. |
|
B. |
It disables the native
VLAN configuration as soon as port security is enabled. |
|
C. |
It places the port in the err-disabled state
if it learns
more than one MAC address. |
|
D. |
It places the
port in the err-disabled slate
after 10 MAC addresses are statically configured. |
Answer:
B
Which command can you enter to display the hits counter for NAT traffic?
|
A. |
show ip nat
statistics |
|
B. |
debug ip nat |
|
C. |
show ip debug nat |
|
D. |
clear ip nat
statistics |
Answer: A
Which two statements about IPv6 router advertisement messages are true? (Choose two.)
|
A. |
They use ICMPv6
type 134. |
|
B. |
The advertised prefix length
must be 64 bits. |
|
C. |
The advertised prefix length
must be 48 bits. |
|
D. |
They are sourced from
the configured IPv6
interface address. |
|
E. |
Their destination is always the
link-local address of the neighboring node. |
Answer: AB
Which three statements about IPv6 prefixes are true? (Choose three.)
|
A. |
FF00:/8 is used
for IPv6 multicast. |
|
B. |
FE80::/10 is used for link-local unicast. |
|
C. |
FC00::/7 is used in private networks. |
|
D. |
2001::1/127 is used for loopback addresses. |
|
E. |
FE80::/8 is used for link-local unicast. |
|
F. |
FEC0::/10 is used
for IPv6 broadcast. |
Answer:
ABC
After you configure the Loopback0 interface, which command can you enter to verify the status of the interface and determine whether fast switching is enabled?
|
A. |
Router#show ip interface loopback 0 |
|
B. |
Router#show run |
|
C. |
Router#show interface loopback 0 |
|
D. |
Router#show ip interface brief |
Answer:
A
Which three statements about link-state routing are true? (Choose three.)
|
A. |
Routes are updated
when a change
in topology occurs. |
|
B. |
Updates are sent to a multicast address by default. |
|
C. |
OSPF is a link-state protocol. |
|
D. |
Updates are sent to a broadcast address. |
|
E. |
RIP is a link-state protocol. |
|
F. |
It uses split
horizon. |
Answer:
ABC
Which NAT function can map multiple inside addresses to a single outside address?
|
A. |
PAT |
|
B. |
SFTP |
|
C. |
RARP |
|
D. |
ARP |
|
E. |
TFTP |
Answer:
A
What is the first step in the NAT configuration process?
|
A. |
Define inside and outside interfaces. |
|
B. |
Define public
and private IP addresses. |
|
C. |
Define IP address pools. |
|
D. |
Define global and local interfaces. |
Answer:
A
Which version of SNMP first allowed user-based access?
|
A. |
SNMPv3 with RBAC |
|
B. |
SNMPv3 |
|
C. |
SNMPv1 |
|
D. |
SNMPv2 |
Answer: B
Which option is the benefit of implementing an intelligent DNS for a cloud computing solution?
|
A. |
It reduces the need for a backup
data center. |
|
B. |
It can redirect user
requests to locations that are using
fewer network resources. |
|
C. |
It enables the ISP
to maintain DNS records automatically. |
|
D. |
It eliminates the need for
a GSS. |
Answer:
B
Which protocol supports sharing the VLAN configuration between two or more switches?
|
A. |
multicast |
|
B. |
STP |
|
C. |
VTP |
|
D. |
split-horizon |
Answer: C
What is the default VLAN on an access port?
|
A. |
0 |
|
B. |
1 |
|
C. |
10 |
|
D. |
1024 |
Answer:
B
Which statement about QoS default behavior is true?
|
A. |
Ports are untrusted by default. |
|
B. |
VoIP traffic
is passed without being tagged. |
|
C. |
Video traffic is passed with
a well-known DSCP
value of 46. |
|
D. |
Packets are classified internally with an environment. |
|
E. |
Packets that arrive
with a tag are untagged at the edge
of an administrative domain. |
Answer: E
Which statement about slow inter VLAN forwarding is true?
|
A. |
The VLAN is experiencing slowness in the point-to-point collisionless connection. |
|
B. |
The VLANs are experiencing slowness because multiple devices are connected to the same
hub. |
|
C. |
The local VLAN
is working normally, but traffic to the alternate VLAN is forwarded slower than expected. |
|
D. |
The entire VLAN is experiencing slowness. |
|
E. |
The VLANs are experiencing slowness due to a duplex mismatch. |
Answer:
E
Which technology supports the stateless assignment of IPv6 addresses? (Choose two)
|
A. |
DNS |
|
B. |
DHCPv6 |
|
C. |
DHCP |
|
D. |
autoconfiguration |
Answer:
BD
Which statement about the inside interface configuration in a NAT deployment is true?
|
A. |
It is defined globally |
|
B. |
It identifies the location of source addresses for outgoing packets to be translated using access or route maps. |
|
C. |
It must be configured if static NAT is used |
|
D. |
It identifies the public IP address that
traffic will use
to reach the internet. |
Answer: B
Explanation:
This module describes how to configure Network Address Translation (NAT) for IP address conservation and how to configure inside and outside source addresses. This module also provides information about the benefits of configuring NAT for IP address conservation.
NAT enables private IP internetworks that use nonregistered IP addresses to connect to the Internet. NAT operates on a device, usually connecting two networks, and translates the private (not globally unique) addresses in the internal network into legal addresses before packets are forwarded onto another network. NAT can be configured to advertise to the outside world only one address for the entire network. This ability provides additional security by effectively hiding the entire internal network behind that one address. NAT is also used at the enterprise edge to allow internal users access to the Internet and to allow Internet access to internal devices such as mail servers.
Which NAT type is used to translate a single inside address to a single outside address?
|
A. |
dynamic NAT |
|
B. |
NAT overload |
|
C. |
PAT |
|
D. |
static NAT |
Answer: D
Explanation:
Network address translation (NAT) is the process of modifying IP address information in IP packet headers while in transit across a traffic routing device.
There are two different types of NAT:
NAT PAT
What is the default lease time for a DHCP binding?
|
A. |
24 hours |
|
B. |
12 hours |
|
C. |
48 hours |
|
D. |
36 hours |
Answer: A
Explanation:
By default, each IP address assigned by a DHCP Server comes with a one- day lease, which is the amount of time that the address is valid. To change the lease value for an IP address, use the following command in DHCP pool configuration mode:
Which RFC was created to alleviate the depletion of IPv4 public addresses?
|
A. |
RFC 4193 |
|
B. |
RFC 1519 |
|
C. |
RFC 1518 |
|
D. |
RFC 1918 |
Answer: D
What are three characteristics of the TCP protocol? (Choose three.)
|
A. |
It uses a single SYN-ACK message to establish a connection. |
|
B. |
The connection is established before data is transmitted. |
|
C. |
It ensures that all data is transmitted and
received by the
remote device. |
|
D. |
It supports significantly higher
transmission speeds than
UDP. |
|
E. |
It requires applications to determine when
data packets must
be retransmitted. |
|
F. |
It uses separate SYN and ACK messages to establish a
connection. |
Answer:
BCF
Which statement about RADIUS security is true?
|
A. |
It supports EAP authentication for connecting to wireless networks. |
|
B. |
It provides encrypted multiprotocol support. |
|
C. |
Device-administration packets
are encrypted in their entirety. |
|
D. |
It ensures that
user activity is fully anonymous. |
Answer: A
Which two statements about IPv4 multicast traffic are true? (Choose two.)
|
A. |
It burdens the
source host without
affecting remote hosts. |
|
B. |
It uses a minimum amount of network
bandwidth. |
|
C. |
It is bandwidth-intensive. |
|
D. |
It simultaneously delivers multiple streams of data. |
|
E. |
It is the
most efficient way to deliver data to multiple receivers. |
Answer: BE
Which type of device can be replaced by the use of subinterfaces for VLAN routing?
|
A. |
Layer 2 bridge |
|
B. |
Layer 2 switch |
|
C. |
Layer 3 switch |
|
D. |
router |
Answer: C
Which command can you enter to display duplicate IP addresses that the DHCP server assigns?
|
A. |
show ip dhcp
conflict 10.0.2.12 |
|
B. |
show ip dhcp database 10.0.2.12 |
|
C. |
show ip dhcp server
statistics |
|
D. |
show ip dhcp
binding 10.0.2.12 |
Answer:
A
What is the subnet address of 192.168.1.42 255.255.255.248?
|
A. |
192.168.1.16/28 |
|
B. |
192.168.1.32/27 |
|
C. |
192.168.1.40/29 |
|
D. |
192.168.1.8/29 |
|
E. |
192.168.1.48/29 |
Answer: C
Which command can you enter to configure an IPv6 floating static route?
|
A. |
router(config)#ipv6 route FE80:0202::/32 serial
0/1 1 |
|
B. |
router (config)#ipv6 route ::/0 serial
0/1 |
|
C. |
router(config)#ipv6 route
static resolve default |
|
D. |
router(config)#ipv6 route FE80.0202::/32serial 0/1 201 |
Answer: D
Which sequence begins a unique local IPv6 address in binary notation?
|
A. |
1111110 |
|
B. |
1111111 |
|
C. |
00000000 |
|
D. |
1111100 |
Answer: D
Explanation:
A IPv6 Unique Local Address is an IPv6 address in the block FC00::/7, which means that IPv6 Unique Local addresses begin with 7 bits with exact binary pattern as 1111 110 -> Answer B is correct.
Note: IPv6 Unique Local Address is the approximate IPv6 counterpart of the IPv4 private address. It is not routable on the global Internet.
Which two statements about fiber cable are true? (Choose two)
|
A. |
Single-mode fiber supports SC and LC connectors only. |
|
B. |
Multimode cable
supports speeds between
100 Mbps and 9.92 Gbps. |
|
C. |
Single-mode cable
is most appropriate for installations longer
than 10 km. |
|
D. |
Fiber cable
is relatively inexpensive and supports a higher data rate than
coaxial cable. |
|
E. |
Mulitimode cable supports speeds between 100 Mbps and 100 Gpbs. |
Answer: DE
Which information is used to install the best route to a destination in IP routing table?
|
A. |
the tunnel ID |
|
B. |
the prefix length |
|
C. |
the interface number |
|
D. |
the autonomous system |
Answer:
B
An administrator has connected devices to a switch and, for security reasons, wants the dynamically learned MAC addresses from the address table added to the running configuration. Which action must be taken to accomplish this?
|
A. |
Use theno switchport port-security command to allow MAC
addresses to be added to the configuration. |
|
B. |
Enable port security and use the keyword sticky. |
|
C. |
Set the switchport mode
to trunk and save the running configuration. |
|
D. |
Use theswitchport protectedcommand to have the
MAC addresses added
to the configuration. |
Answer: B
Which two of these functions do routers perform on packets? (Choose two.)
|
A. |
update the Layer
3 headers of outbound packets so that the packets are
properly directed to
valid next hops |
|
B. |
update the Layer 2 headers of outbound packets
with the MAC addresses of the next
hops |
|
C. |
examine the
Layer 3 headers of inbound packets and use that
information to determine the complete paths along which the packets will be routed to
their ultimate destinations |
|
D. |
examine the Layer
3 headers of inbound packets and use that
information to determine the next hops for
the packets |
|
E. |
examine the Layer
2 headers of inbound packets and use that
information to determine the next hops for
the packets |
|
F. |
update the Layer
3 headers of outbound packets so that the packets are
properly directed to
their ultimate destinations |
Answer: BD
Which two options will help to solve the problem of a network that is suffering a broadcast storm? (Choose two.)
|
A. |
a Layer
3 switch |
|
B. |
a hub |
|
C. |
a bridge |
|
D. |
an access point |
|
E. |
a router |
Answer: AE
A switch has 48 ports and 4 VLANs. How many collision and broadcast domains exist on the switch (collision, broadcast)?
|
A. |
4,48 |
|
B. |
48,4 |
|
C. |
48,1 |
|
D. |
4,1 |
|
E. |
1,48 |
Answer:
B
Which statement describes the effect of the overload keyword in the ip nat inside source list 90 interface ethernet 0/0 overload command?
|
A. |
Addresses
that match access
listinsideare translated to the IP address of the Ethernet 0/0 interface. |
|
B. |
Hosts that
match access listinsideare translated to an address in the Ethernet 0/0 network. |
|
C. |
Hosts on the Ethernet 0/0 LAN are translated to the address pool in access list90. |
|
D. |
Addressesthat match
access list90are translated through PAT to the IP address of the Ethernet 0/0 interface. |
Answer: D
How many host addresses are available on the network 192.168.1.0 subnet 255.255.255.240 ?
|
A. |
6 |
|
B. |
8 |
|
C. |
14 |
|
D. |
16 |
Answer: C
Which two statements are true for multicast MAC address directions?
|
A. |
01:00:5E:xx:xx:xx |
|
B. |
one to one |
|
C. |
01 00 xx xxxxxxx |
|
D. |
02 xx xxxxxxx |
|
E. |
one to many |
Answer: AE
Explanation:
The Internet authorities have reserved the multicast address range of 01:00:5E:00:00:00 to 01:00:5E:7F:FF:FF for Ethernet and Fiber Distributed Data Interface (FDDI) media access control (MAC) addresses.
Which subnet address is for the IP address 172.19.20.23/28?
|
A. |
172.19.20.20 |
|
B. |
172.19.20.0 |
|
C. |
172.19.20.32 |
|
D. |
172.19.20.15 |
|
E. |
172.19.20.16 |
Answer:
E
The command ip route 192.168.100.160 255.255.255.224 192.168.10.2 was issued on a router. No routing protocols or other static routes are configured on the router. Which statement is true about this command?
|
A. |
The interface with
IP address 192.168.10.2 is on this
router. |
|
B. |
The command sets a gateway of last resort
for the router. |
|
C. |
Packets that
are destined for host 192.168.100.160 will be sent
to 192.168.10.2. |
|
D. |
The command creates a static route
for all IP traffic with
the source address 192.168.100.160. |
Answer: C
Which feature can validate address requests and filter out invalid messages?
|
A. |
IP Source Guard |
|
B. |
port security |
|
C. |
DHCP snooping |
|
D. |
dynamic ARP inspection |
An administrator is working with the 192.168.4.0 netwrok, which has been subnetted with a /26 mask. Which two addresses can be assigned to hosts within the same subnet? (Choose two.)
|
A. |
192.168.4.67 |
|
B. |
192.168.4.61 |
|
C. |
192.168.4.128 |
|
D. |
192.168.4.132 |
|
E. |
192.168.4.125 |
|
F. |
192.168.4.63 |
Answer:
AE
On a live network, which two commands will verify the operational status of router interfaces? (Choose two.)
|
A. |
Router# show ip interface brief |
|
B. |
Router# debug
interface |
|
C. |
Router# show
ip protocols |
|
D. |
Router# show
interfaces |
|
E. |
Router# show start |
Answer:
AD
In which STP state does MAC address learning take place on a PortFast-enabled port?
|
A. |
learning |
|
B. |
listening |
|
C. |
discarding |
|
D. |
forwarding |
Answer: D
Which command can you enter to assign an interface to the default VLAN?
|
A. |
Switch(config-if)# switchport access vlan 1 |
|
B. |
Switch(config-if)# switchport trunk native vlan
1 |
|
C. |
Switch(config-if)# vlan
1 |
|
D. |
Switch(config)#
int vlan 1 |
Answer:
A
configured with IP addresses on the same subnet?
|
A. |
The destination host
receives an echo
reply from the source host
within one second
and the source host receives an echo request from the destination host. |
|
B. |
The destination host receives an echo request from the source
host within one second. |
|
C. |
The destination host
receives an echo
replyfrom the source
host within one second and
the source host receives an echo reply from the destination host
within two seconds. |
|
D. |
The destination host receives an echo request from the source
host and the
source host receives an echo request from the
destination host within one second. |
|
E. |
The destination host receives an echo request from the source
host and the
source host receives an echo reply from the
destination host within two seconds. |
Answer:
E
Which command can you enter to configure an IPv6 static route?
|
A. |
router(config)#ipv6 route FE80:0202::/32 serial
0/1 1 |
|
B. |
router(config)#ipv6 route
FE80:0202::/32 serial 0/1
201 |
|
C. |
router(config)#ipv6 route
::/0 serial 0/1 |
|
D. |
router(config)#ipv6 route static
resolve default |
Answer:
B
Which three options are types of slow VLAN connectivity? (Choose three.)
|
A. |
slow broadcast domain
connectivity |
|
B. |
slow routing
domain connectivity |
|
C. |
slow default
gateway connectivity |
|
D. |
slow application domain connectivity |
|
E. |
slow collision domain connectivity |
|
F. |
slow inter-VLAN connectivity |
Answer:
ADE
Which two statements about the spanning-tree bridge ID are true? (Choose two.)
|
A. |
It is composed of a 4-bit
bridge priority and a 12-bit
system ID extension. |
|
B. |
The bridge ID is transmitted in the IP header to elect the root bridge. |
|
C. |
Thesystem ID extension is a value
between 1 and 4095. |
|
D. |
It is composed of an 8-bit
bridge priority and a 16-bit
system ID extension. |
|
E. |
The bridge priority must be incremented in blocks of 4096. |
Answer: AE
Why do large OSPF networks use a hierarchical design? (Choose three.)
|
A. |
to decrease latency by increasing bandwidth |
|
B. |
to reduce routing overhead |
|
C. |
to speed up convergence |
|
D. |
to confine network instability to single areas
of the network |
|
E. |
to reduce the complexity of router configuration |
|
F. |
to lower costs
by replacing routers with distribution layer
switches |
Answer: BCD
Explanation:
OSPF implements a two-tier hierarchical routing model that uses a core or backbone tier known as area zero (0). Attached to that backbone via area border routers (ABRs) are a number of secondary tier areas. The hierarchical approach is used to achieve the following:
Rapid convergence because of link and/or switch failures Deterministic traffic recovery
Scalable and manageable routing hierarchy, reduced routing overhead.
Which command must you use to test DNS connectivity?
|
A. |
telnet |
|
B. |
show hosts |
|
C. |
ipconfig |
|
D. |
show interfaces |
Answer: B
Which two command sequences must you configure on a switch to establish a Layer 3 EtherChannel with an open-standard protocol? (Choose two.)
|
A. |
interface
GigabitEthernet0/0/1 channel-group 10 mode on |
|
B. |
interface GigabitEthernet0/0/1 channel-group 10 mode active |
|
C. |
interface GigabitEthernet0/0/1 channel-group 10
mode auto |
|
D. |
interface port-channel 10 switchport switchport mode
trunk |
|
E. |
interface port-channel 10 no switchport ip address 172.16.0.1.255.255.255.0 |
Answer:
BD
According to security best practices, which two actions must you take to protect an unused switch port? (Choose two.)
|
A. |
Administratively
shut down the
port. |
|
B. |
Configure the port as a trunk
port. |
|
C. |
Configure the
port to automatically come online. |
|
D. |
Enable CDP. |
|
E. |
Configure the port
as an access port on a VLAN
other than VLAN
1. |
Answer:
AE
Which IOS troubleshooting tool should you use to direct system messages to your screen?
|
A. |
log events |
|
B. |
terminal monitor |
|
C. |
local SPAN |
|
D. |
APIC-EM |
Answer:
B
Which feature or protocol must you enable so that the output of the show interfaces trunk command includes information about native VLAN mismatches?
|
A. |
RSTP |
|
B. |
CDP |
|
C. |
PortFast |
|
D. |
DTP |
Answer:
B
Which two protocols does the internet layer in the TCP/IP model encapsulate? (Choose two.)
|
A. |
DNS |
|
B. |
TCP |
|
C. |
SMTP |
|
D. |
ARP |
|
E. |
ICMP |
Answer: DE
Which two VLAN IDs indicate a default VLAN? (Choose two.)
|
A. |
0 |
|
B. |
1 |
|
C. |
1005 |
|
D. |
1006 |
|
E. |
4096 |
Answer:
BC
Explanation:
VLAN 1 is a system default VLAN, you can use this VLAN but you cannot delete it. By default VLAN 1 is use for every port on the switch.
Standard VLAN range from 1002-1005 it’s Cisco default for FDDI and Token Ring. You cannot delete VLANs 1002-1005. mostly we don’t use VLAN in this range.
Which two TCP messages use a 32-bit number as part of the initial TCP handshake? (Choose two.)
|
A. |
SYN |
|
B. |
RST |
|
C. |
SYN-ACK |
|
D. |
FIN |
|
E. |
ACK |
Answer: AE
Which port security violation mode drops traffic from unknown MAC addresses and sends an SNMP trap?
|
A. |
protect |
|
B. |
restrict |
|
C. |
shutdown |
|
D. |
shutdown VLAN |
Answer: B
What is the difference between 1000BASE-LX/LH and 1000BASE-ZX interfaces?
|
A. |
1000BASE-ZX is supported on links up to 1000km,
and 1000BASE-LX/LH operates over links up to 70 km. |
|
B. |
1000BASE-LX/LH interoperates with multimode and single-mode fiber,
and 10008ASE-ZX needs a conditioning patch cable with a
multimode. |
|
C. |
1000BASE-LX/LH is supported on links up to 10km,
and 1000BASE-ZX operates over links up to
70 km |
|
D. |
1000BASE-ZX interoperates with
dual-rate 100M/1G 10Km
SFP over multimode fiber, and
1000BASE-LX/LH supports only single-rate. |
Answer: C
Explantion:
https://www.cables-solutions.com/are-there-any-differences-between-lx-lh-and-lxlh.html
Refer to the exhibit. Which VLAN ID is associated with the native VLAN?
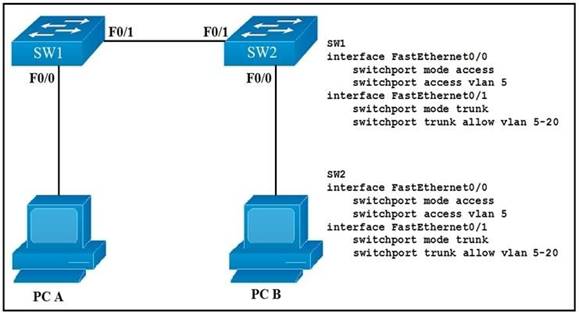
|
A. |
VLAN 1 |
|
B. |
VLAN 5 |
|
C. |
VLAN 10 |
|
D. |
VLAN 20 |
Answer:
A
How does a Cisco IP phone handle untagged traffic that it receives from an attached PC?
|
A. |
It allows the traffic to pass through unchanged. |
|
B. |
It drops the traffic. |
|
C. |
It tags the traffic
with the default
VLAN. |
|
D. |
It tags the traffic with the native
VLAN. |
Answer:
A
Refer to the exhibit. Which VLAN ID is associated with the default VLAN in the given environment?
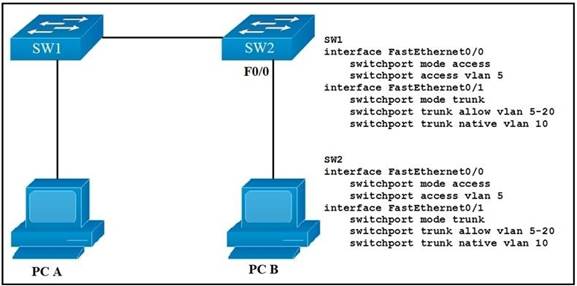
|
A. |
VLAN 1 |
|
B. |
VLAN 5 |
|
C. |
VLAN 10 |
|
D. |
VLAN 20 |
Answer:
A
Which two statements about DNS lookup operations are true? (Choose two.)
|
A. |
When the primary
IP address of the destination is down, the DNS server
can forward the client to an alternate IP address. |
|
B. |
The client sends a request for IP address to domain name
resolution to the DNS server. |
|
C. |
The DNS server pings
the destination to verify that
is available. |
|
D. |
They use destination port
53. |
|
E. |
The client sends
a request for domain name
to IP address resolution to the DNS server. |
Answer: DE
Refer to the exhibit. Users in your office are complaining that they cannot connect to the severs at a remote site.
When troubleshooting,you find that you can successfully reach the severs from router R2. What is the most likely reason that the other users are experiencing connection failure?
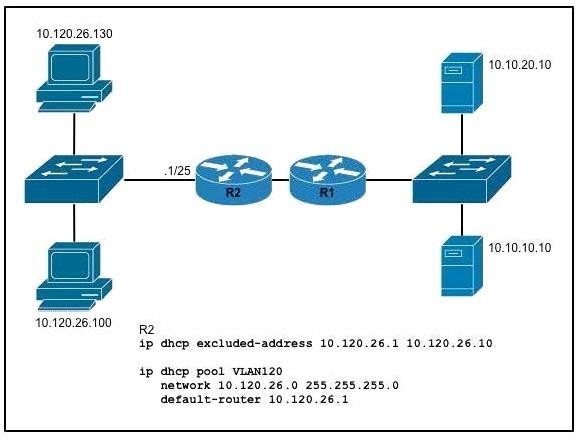
|
A. |
interface ports are shut down
on the remote
servers |
|
B. |
The DHCP address pool
has been exhausted |
|
C. |
The ip helper-address command is missing on the R2 interface that
connects to the
switch |
|
D. |
VLSM is misconfigured between the router
interface and the
DHCP pool. |
Answer: D
What are two common types of copper cable?
|
A. |
unshielded twisted pair |
|
B. |
single-mode |
|
C. |
shielded twisted pair |
|
D. |
OM4 |
|
E. |
multimode |
Answer: AC
Which effect does the switchport trunk vlan 10 command have?
|
A. |
It sets VLAN
10 as the native VLAN
on the trunk. |
|
B. |
It configures the
interface as a trunk port. |
|
C. |
It allows traffic
from native VLAN
10 on the trunk. |
|
D. |
It prevents traffic on VLAN 1 from passing
on the trunk. |
Answer: B
Which two wireless security stewards use Counter Mode Cipher Block Chaining Message Authentication Code Protocol for encryption and data integrity? (Choose two.)
|
A. |
WPA2 |
|
B. |
WPA3 |
|
C. |
Wi-Fi 6 |
|
D. |
WEP |
|
E. |
WPA |
Answer: AB
Which layer of the TCP/IP model manages the transmission of binary digits across an Ethernet cable?
|
A. |
network |
|
B. |
physical |
|
C. |
data link |
|
D. |
transport |
Answer: B
Which two characteristics are representative of a link-state routing protocol? (Choose two.)
|
A. |
provides common view
of entire topology |
|
B. |
exchanges routing
tables for its own routes
with neighbor |
|
C. |
calculates feasible path |
|
D. |
utilizes event-triggered updates |
|
E. |
utilizes frequent periodic updates |
Answer: AD
Refer to the exhibit. An engineer is configuring a Layer 3 port-channel interface with LACP. The configuration on the first device is complete, and it is verified that both interfaces have registered the neighbor device in the CDP table.
Which task on the neighbor device enables the new port channel to come up without negotiating the channel?
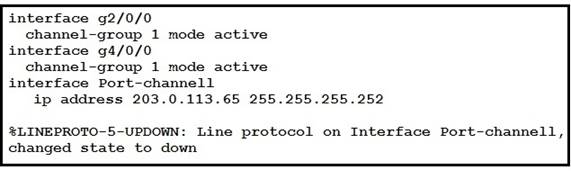
|
A. |
Change the EtherChannel mode on the neighboring interfaces to auto. |
|
B. |
Configure the IP address
of the neighboring device. |
|
C. |
Bring up the neighboring interfaces using the no shutdown command. |
|
D. |
Modify the static
EtherChannel configuration of the device
to passive mode. |
Answer: D
Which encryption method is used by WPA3?
|
A. |
PSK |
|
B. |
TKIP |
|
C. |
SAE |
|
D. |
AES |
Answer: D
Explanation:
When using WPA3 only, the access point will transmit in the beacon the capability to only accept STA using WPA3 SAE. When using transition mode, the access point will broadcast in the beacon capabilities to accept STA using both WPA2 and WPA3. In this configuration, STA that do not support WPA3 can still connect to the SSID.
Which technology is a critical component of a cloud-based architecture?
|
A. |
DNS |
|
B. |
MPLS |
|
C. |
DHCP |
|
D. |
IPv6 |
Answer:
A
Which two benefits of implementing a full-mesh WAN topology are true? (Choose two.)
|
A. |
increased latency |
|
B. |
redundancy |
|
C. |
reduced jitter |
|
D. |
reliability |
|
E. |
improved scalability |
Answer: BD
Refer to the exhibit. An engineer must configure router R2 so it is elected as the DR on the WAN subnet.
Which command sequence must be configured?
![]()
|
A. |
interface
gigabitethernet0/0 ip address 10.0.0.34 255.255.255.248 ip ospf priority 0 |
|
B. |
interface gigabitethernet0/0 ip address 10.0.0.34 255.255.255.224 ip ospf priority 100 |
|
C. |
interface gigabitethernet0/0 ip address 10.0.1.1 255.255.255.0 ip ospf priority 255 |
|
D. |
interface gigabitethernet0/0 ip address 10.0.1.1 255.255.255.224 ip ospf priority 98 |
Answer:
B
You have the Class B network 172.16.0.0/16 and want to create 16 subnets.
What will the new subnet mask be for the 16 subnets?
|
A. |
/18 |
|
B. |
/19 |
|
C. |
/21 |
|
D. |
/17 |
|
E. |
/22 |
|
F. |
/20 |
Answer:
F
Drag and Drop Question
Drag and drop the Wi-Fi terms from the left onto the descriptions on the right.
![]()
Answer:
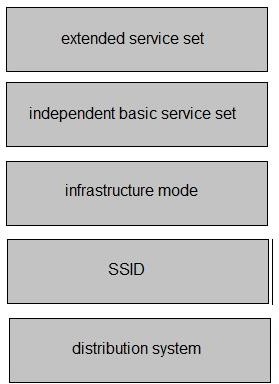
Explanation:
https://networklessons.com/cisco/ccna-200-301/wireless-lan-802-11-service-sets
Which of the following protocols are used to auto negotiate trunk formation between two switches?
|
A. |
CDP |
|
B. |
VTP |
|
C. |
DTP |
|
D. |
STP |
Answer: C
Refer to the exhibit. How many objects are present in the given JSON-encoded data?

|
A. |
one |
|
B. |
four |
|
C. |
seven |
|
D. |
nine |
Answer: D
Explanation:
Simply count all the opening or closing curly brackets that represent the start or closing of an object value. NOTE: there's an error on that exhibit, the opening bracket in the array is supposed to be an opening bracket.
Which command is used to verify your OSPFv3 neighbor adjacencies?
|
A. |
show ospf neighbor |
|
B. |
show ipv6 brief |
|
C. |
show ipv6 ospf |
|
D. |
show ipv6 ospf
neighbor |
Answer: D
By default, which port is the following telnet command going to? C:\Windows\system32> telnet 2001:DB8:172:16::100
|
A. |
23 |
|
B. |
21 |
|
C. |
80 |
|
D. |
43 |
Answer:
A
What is the Layer 2 encapsulation for Ethernet?
|
A. |
802.1q |
|
B. |
ARPA |
|
C. |
SSL |
|
D. |
RTP |
Answer:
B
When a switch receives a frame for an unknown destination MAC address, how is the frame handled?
|
A. |
broadcast to all ports on the switch |
|
B. |
flooded to all ports
except the origination port |
|
C. |
forwarded to the first
available port |
|
D. |
inspected and dropped
by the switch |
Answer: B
Explanation:
Switches tend to flood frame with the Unknown Destination MAC Address out all ports apart from the Originating (apart from the one it received) port.
Refer to the exhibit. An OSPF neighbor relationship must be configured using these guidelines:
![]()
- R1 is only permitted to establish a neighbor with R2
- R1 will never participate in DR elections
- R1 will use a router-id of 101.1.1.
Which configuration must be used?
|
A. |
|
|
B. |
|
|
C. |
|
|
D. |
|
Answer: A
Under which condition is TCP preferred over UDP?
|
A. |
UDP is used
when low latency is optimal, and TCP is used when latency is tolerable. |
|
B. |
TCP is used
when dropped data
is more acceptable, and UDP is used when
data is accepted out- of-order. |
|
C. |
TCP is used when data reliability is critical, and UDP is used when missing packets
are acceptable. |
|
D. |
UDP is used
when data is highly interactive, and TCP is used when
data is time-sensitive. |
Answer: C
Refer to the exhibit. R1 has just received a packet from host A that is destined to host B. Which route in the routing table is used by R1 to reach host B?
![]()
|
A. |
10.10.13.0/25 [1/0] via
10.10.10.2 |
|
B. |
10.10.13.0/25 [108/0] via 10.10.10.10 |
|
C. |
10.10.13.0/25 [110/2] via 10.10.10.6 |
|
D. |
10.10.13.0/25 [110/2] via
10.10.10.2 |
Answer:
B
Explanation:
OSFP routing, indicated by area 0 routing command, has AD of 110. There is a floating static route configured with 108 AD. As the configured static route's AD is lower (108) than the OSPF's default AD (110) it will route the traffic via 10.10.10.10 because it has the lowest AD and thus will be put into the routing table.
What is a similarity between 1000BASE-LX and 1000BASE-T standards?
|
A. |
Both use the same data-link header and trailer
formats. |
|
B. |
Both cable
types support RJ-45
connectors. |
|
C. |
Both support up to 550 meters between
nodes. |
|
D. |
Both cable types
support LR connectors. |
Answer:
A
Which function forwards frames to ports that have a matching destination MAC address?
|
A. |
frame flooding |
|
B. |
frame filtering |
|
C. |
frame pushing |
|
D. |
frame switching |
Answer: D
Explanation:
Flooding means that the switch sends the incoming frame to all occupied and active ports (except for the one from which it was received
In forwarding, it first looks up the destination address in the MAC Address Table. It then forwards the frame to that specific port.
How do TCP and UDP fit into a query-responsible model?
|
A. |
TCP avoids using
sequencing and UDP avoids using
acknowledgments |
|
B. |
TCP establishes a connection prior to sending
data, and UDP
sends immediately |
|
C. |
TCP encourages out-of-order packet
delivery, and UDP
prevents re-ordering |
|
D. |
TCP uses error
detection for packets, and UDP uses error recovery. |
Answer: B
What are two characteristics of an SSID? (Choose two.)
|
A. |
It uniquely identifies a client in a WLAN. |
|
B. |
It is at most 32 characters long |
|
C. |
It uniquely identifies an access point
in a WLAN |
|
D. |
It provides secured access
to a WLAN. |
|
E. |
It can be hidden or broadcast in a WLAN. |
Answer: BE
Why is UDP more suitable than TCP for applications that require low latency such as VoIP?
|
A. |
UDP reliably guarantees delivery of all packets: TCP
drops packets under
heavy load |
|
B. |
UDP uses
sequencing data for
packets to arrive
in order TCP
offers the capability to receive packets
in random order |
|
C. |
TCP uses congestion control for efficient packet delivery: UDP uses flow
control mechanisms for the delivery of packets |
|
D. |
TCP sends an acknowledgement for every packet
received: UDP operates without acknowledgments |
Answer: D
What are the two functions of SSIDs? (Choose two.)
|
A. |
uses the maximum of 32 alphanumeric characters |
|
B. |
controls the
speed of the
Wi-Fi network |
|
C. |
used exclusively with controller-based Wi-Fi
networks |
|
D. |
supports a single access
point |
|
E. |
broadcasts by default |
Answer: AE
Which PoE mode enables powered-devices detection and guarantees power when the device detected?
|
A. |
auto |
|
B. |
static |
|
C. |
dynamic |
|
D. |
active |
Answer:
B
Explanation:
static - Enables powered-device detection; pre-allocate (reserve) power for a port before the switch discovers the powered device; the switch reserves power for this port even when no device is connected and guarantees that power will be provided upon device detection.
Refer to the exhibit. Configurations for the switch and PCs are complete. Which configuration must be applied so that VLANs 2 and 3 communicate back and forth?
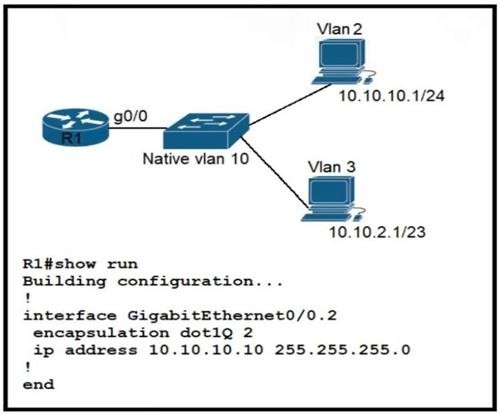
|
A. |
interface GigabitEthernet0/0 ip address 10.10.2.10 255.255.252.0 |
|
B. |
interface GigabitEthernet0/0.10 encapsulation dot1Q 3 ip address 10.10.2.10 255.255.254.0 |
|
C. |
interface GigabitEthernet0/0.3 encapsulation dot1Q 3 native
ip address 10.10.2.10 255.255.252.0 |
|
D. |
interface GigabitEthernet0/0.3 encapsulation dot1Q 10 ip address 10.10.2.10 255.255.255.252 |
Answer: B
Explanation:
R1 Subinterface Configuration (4.2.4)
The router-on-a-stick method requires you to create a subinterface for each VLAN to be routed.
A subinterface is created using the interface interface_id.subinterface_id global configuration mode command. The subinterface syntax is the physical interface followed by a period and a subinterface number. Although not required, it is customary to match the subinterface number with the VLAN number.
Drag and Drop Question
Drag and drop the IPv6 address type characteristics from the left to the right.
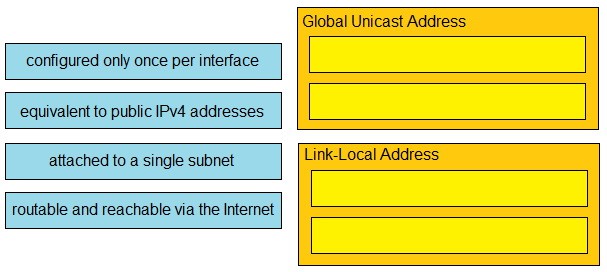
Answer:
![]()
Explanation:
https://www.ciscopress.com/articles/article.asp?p=2803866&seqNum=4
How is RFC 1918 addressing used in a network?
|
A. |
They are used
to access the
Internet from the
internal network without
conversion. |
|
B. |
They are used in place of public addresses for Increased security. |
|
C. |
They are used with
NAT to preserve public IPv4 addresses. |
|
D. |
They are used
by Internet Service Providers to route
over the Internet. |
Answer: C
Explanation:
This document describes address allocation for private internets. The allocation permits full network layer connectivity among all hosts inside an enterprise as well as among all public hosts
of different enterprises. The cost of using private internet address space is the potentially costly effort to renumber hosts and networks between public and private. https://datatracker.ietf.org/doc/html/rfc1918
Drag and Drop Question
Drag and drop the IPv6 address types from the left onto their description on the right.
![]()
Answer:
![]()
Drag and Drop Question
Drag and drop the characteristics of transport layer protocols from the left onto the corresponding
protocols on the right.
![]()
Answer:
![]()
A network engineer must configure an interface with IP address 10.10.10.145 and a subnet mask equivalent to 11111111.11111111.11111111.11111000. Which subnet mask must the engineer use?
|
A. |
/29 |
|
B. |
/30 |
|
C. |
/27 |
|
D. |
/28 |
Answer:
A
Refer to the exhibit. The switches are connected via a Cat5 Ethernet cable that is tested successfully. The interfaces are configured as access ports and are both in a down status. What is the cause of the issue?
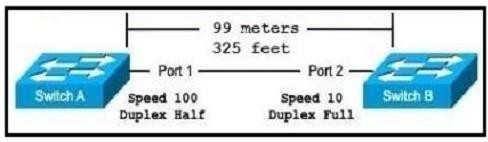
|
A. |
The speed settings on the switches are mismatched |
|
B. |
The distance between the two switches is not supported by Cat5 |
|
C. |
The switches are configured with incompatible duplex
settings |
|
D. |
The portfast command is missing from
the configuration |
Answer:
A
Which two IP addressing schemes provide internet access to users on the network while preserving the public IPv4 address space? (Choose two.)
|
A. |
IPv6 addressing |
|
B. |
PAT with private internal addressing |
|
C. |
single public
Class A network |
|
D. |
private networks only |
|
E. |
custom addresses from
ARIN |
Answer:
AB
Explanation:
PAT with private internal addressing is the usual method of allowing Internet access while preserving IPv4 addresses. Another alternative is using IPV6, which will allow internet access without using any IPv4 addresses. The other answer choices will consume a great deal of public IPV4 addresses, or will not allow for internet access.
The address block 192.168.32.0/24 must be subnetted into smaller networks. The engineer must meet these requirements:
- Create 8 new subnets.
- Each subnet must accommodate 30 hosts.
- Interface VLAN 10 must use the last usable IP in the first new subnet.
- A Layer 3 interface is used.
Which configuration must be applied to the interface?
|
A. |
no switchport mode
trunk ip address 192.168.32.97 255.255.255.224 |
|
B. |
switchport ip address 192.168.32.65 255.255.255.240 |
|
C. |
no switchport |
|
|
ip address 192.168.32.30 255.255.255.224 |
|
D. |
no switchport mode
access ip address 192.168.32.62 255.255.255.240 |
Answer: C
Explanation:
Requirement is 8 networks with 30 hosts
255.255.255.0 = 11111111.11111111.11111111.00000000
8
networks = 1111 with increment of 16 which
is less host number than require.
30 hosts = 11100000 with increment of 32
255.255.255.224 or 11111111.11111111.11111111.11100000
8 networks for /27 are 0,32,64,96,128,160,192,224
What are two reasons to deploy private addressing on a network? (Choose two.)
|
A. |
to subnet addresses in an organized hierarchy |
|
B. |
to reduce network maintenance costs |
|
C. |
to segment local IP addresses from
the global routing table |
|
D. |
to hide sensitive data
from access users
within an enterprise |
|
E. |
to route protected data securely via an Internet service provider |
Answer: BC
Which property is shared by 10GBase-SR and 10GBase-LR interfaces?
|
A. |
Both use the
single-mode fiber type. |
|
B. |
Both require UTP cable media
for transmission. |
|
C. |
Both require
fiber cable media
for transmission. |
|
D. |
Both use the multimode fiber
type. |
Answer: C
What is a function spine-and-leaf architecture?
|
A. |
Offers predictable latency
of the traffic path between end devices. |
|
B. |
Exclusively sends
multicast traffic between
servers that are directly connected to the spine. |
|
C. |
Mitigates oversubscription by adding a layer of leaf switches. |
|
D. |
Limits payload size
of traffic within
the leaf layer. |
Answer:
A
Explanation:
With a spine-and-leaf architecture, no matter which leaf switch to which a server is connected, its traffic always has to cross the same number of devices to get to another server (unless the other server is located on the same leaf). This approach keeps latency at a predictable level because a payload only has to hop to a spine switch and another leaf switch to reach its destination.
Reference:
https://www.cisco.com/c/en/us/products/collateral/switches/nexus-7000-series-switches/white-
paper-c11-737022.html
What is the function of the control plane?
|
A. |
It exchanges routing
table information. |
|
B. |
It provides CLI access
to the network device. |
|
C. |
It looks up an egress interface in the forwarding information base. |
|
D. |
It forwards traffic to the next
hop. |
Answer: A
Explanation:
The control plane is the part of a network that controls how data packets are forwarded — meaning how data is sent from one place to another. The process of creating a routing table, for example, is considered part of the control plane. Routers use various protocols to identify network paths, and they store these paths in routing tables.
Refer to the exhibit. An engineer assigns IP addressing to the current VLAN with three PCs. The configuration must also account for the expansion of 30 additional VLANS using the same Class C subnet for subnetting and host count. Which command set fulfills the request while reserving address space for the expected growth?
![]()
|
A. |
Switch(config)#interface vlan 10 Switch(config-if)#ip address 192.168.0.1 265 255.255.252 |
|
B. |
Switch(config)#interface vlan 10 Switch(config-if)#ip address 192.168.0.1 255 255.255.248 |
|
C. |
Switch(config)#interface vlan 10 Switch(config-if)#ip address 192.168.0.1 255 255.255.0 |
|
D. |
Switch(config)#interface vlan 10 Switch(config-if)#ip address 192.168.0.1 255.255.255.128 |
Answer: B
Drag and Drop Question
Drag and drop the statements about wireless architectures from the left onto the architectures on the right.
![]()
Answer:
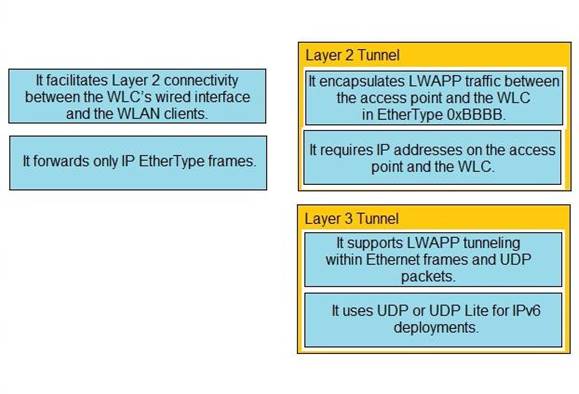
Refer to the exhibit. Which configuration establishes a Layer 2 LACP EtherChannel when applied to both switches?
![]()
|
A. |
Interface range G1/1
- 1/3 switchport mode trunk channel-group 1 mode active
no shutdown |
|
B. |
Interface range
G1/1 - 1/3
switchport mode access
channel-group 1 mode
passive no shutdown |
|
C. |
Interface range
G1/1 - 1/3
switchport mode trunk
channel-group 1 mode
desirable no shutdown |
|
D. |
Interface range G1/1
- 1/3 switchport mode access
channel-group 1 mode
on no shutdown |
Answer:
A
Refer to the exhibit. Which action must be taken so that neighboring devices rapidly discover switch Cat9300?
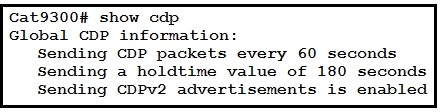
|
A. |
Enable portfast on the ports
that connect to neighboring devices. |
|
B. |
Configure the cdp timer
10 command on switch Cat9300. |
|
C. |
Configure the cdp holdtime 10 command on switch Cat9300 |
|
D. |
Configure the cdp timer 10 command on the neighbors of switch Cat9300 |
Answer:
B
Drag and Drop Question
Drag and drop the management connection types from the left onto the definitions on the right.
![]()
Answer:
![]()
Refer to the exhibit. An engineer must configure the interface that connects to PC1 and secure it in a way that only PC1 is allowed to use the port. No VLAN tagging can be used except for a voice VLAN. Which command sequence must be entered to configure the switch?
![]()
|
A. |
SW1(config-if)#switchport mode
dynamic auto
SW1(config-if)#switchport port-security SW1(config-if)#switchport port-security violation restrict |
|
B. |
SW1(config-if)#switchport mode nonegotiate
SW1(config-if)#switchport port-security SW1(config-if)#switchport port-security maximum 1 |
|
C. |
SW1(config-if)#switchport mode access
SW1(config-if)#switchport port-security SW1(config-if)#switchport port-security mac-address 0050.7966.6800 |
|
D. |
SW1(config-if)#switchport mode dynamic desirable SW1(config-if)#switchport port-security mac-address 0050.7966.6800
SW1(config-if)#switchport port-security mac-address sticky |
Answer: C
Refer to the exhibit. The EtherChannel is configured with a speed of 1000 and duplex as full on both ends of channel group 1. What is the next step to configure the channel on switch A to respond to but not initiate LACP communication?
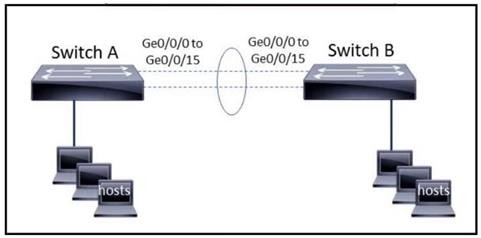
|
A. |
interface range gigabitethernet0/0/0-15 channel-group 1 mode on |
|
B. |
interface range
gigabitethernet0/0/0-15 channel-group 1 mode desirable |
|
C. |
interface port-channel 1 channel-group 1 mode auto |
|
D. |
interface port-channel 1 channel-group 1 mode passive |
Answer: D
Refer to the exhibit. Switch AccSw1 has just been added to the network along with PC2. All VLANs have been implemented on AccSw2. How must the ports on AccSw2 be configured to establish Layer 2 connectivity between PC1 and PC2?
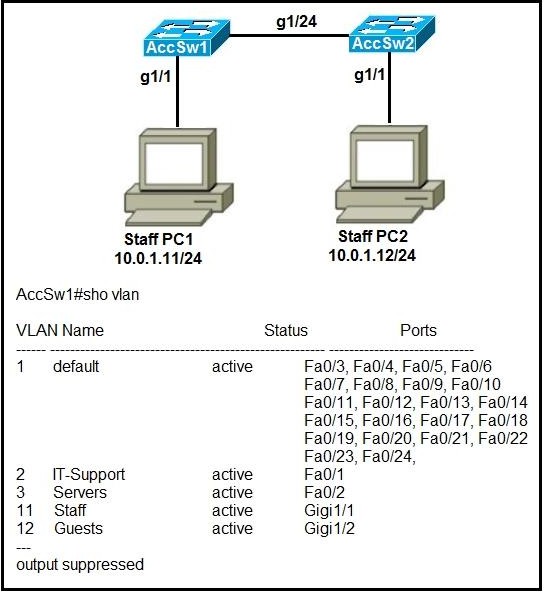
|
A. |
interface GigabitEthernet1/2 switchport mode
access switchport access vlan 2 ! interface GigabitEthernet1/24 switchport mode
trunk |
|
B. |
interface GigabitEthernet1/1 switchport mode
access switchport access vlan 11 ! interface GigabitEthernet1/24 switchport mode
trunk |
|
C. |
interface GigabitEthernet1/24 switchport mode
trunk switchport trunk allowed vlan 11, 12 |
|
|
! interface GigabitEthernet1/1
switchport access vlan 11 |
|
D. |
interface GigabitEthernet1/2 switchport mode
access switchport access vlan 12 ! interface GigabitEthernet1/24 switchport mode
trunk switchport trunk allowed vlan 11, 12 |
Answer: B
Refer to the exhibit. Two new switches are being installed. The remote monitoring team uses the support network to monitor both switches. Which configuration is the next step to establish a Layer 2 connection between the two PCs?
![]()
|
A. |
SwitchA(config)#interface
GigabitEthernet0/1 SwitchA(config-if)#switchport access vlan 500 SwitchB(config)#interface
GigabitEthernet0/1 SwitchB(config-if)#switchport access
vlan 500 |
|
B. |
SwitchA(config)#interface GigabitEthernet0/1
SwitchA(config-if)#switchport mode trunk SwitchB(config)#interface GigabitEthernet0/1 SwitchB(config-if)#switchport mode
trunk |
|
C. |
SwitchA(config)#interface GigabitEthernet0/0 SwitchA(config-if)#switchport trunk
allowed vlan 500,
550 SwitchB(config)#interface GigabitEthernet0/0 |
|
|
SwitchB(config-if)#switchport trunk
allowed vlan 500,
550 |
|
D. |
SwitchA(config)#interface
GigabitEthernet0/0 SwitchA(config-if)#spanning-tree portfast
SwitchA(config-if)#spanning-tree bpduguard enable SwitchB(config)#interface
GigabitEthernet0/0 SwitchB(config-if)#spanning-tree portfast SwitchB(config-if)#spanning-tree bpduguard enable |
Answer: A
Refer to the exhibit. An engineer is configuring a new Cisco switch, NewSW, to replace SW2. The details have been provided:
- Switches SW1 and SW2 are third-party devices
without support for trunk ports.
- The existing connections must be maintained between PC1, PC2, and
PC3.
- Allow the switch
to pass traffic
from future VLAN 10.
Which configuration must be applied?
![]()
|
A. |
NewSW(config)#interface
f0/0 NewSW(config-if)#switchport mode trunk NewSW(config-if)#switchport trunk native vlan 10
NewSW(config-if)#switchport trunk native
vlan 10 |
|
B. |
NewSW(config)#interface
f0/0 NewSW(config-if)#switchport mode access NewSW(config-if)#switchport trunk allowed vlan
2, 10
NewSW(config-if)#switchport trunk native vlan 2 |
|
C. |
NewSW(config)#interface
f0/0 NewSW(config-if)#switchport mode access NewSW(config-if)#switchport trunk allowed vlan
2, 10
NewSW(config-if)#switchport trunk native vlan 10 |
|
D. |
NewSW(config)#interface
f0/0 NewSW(config-if)#switchport mode trunk NewSW(config-if)#switchport trunk allowed vlan
2, 10
NewSW(config-if)#switchport trunk native vlan 2 |
Answer: B
Refer to the exhibit. The network engineer is configuring a new WLAN and is told to use a setup password for authentication instead of the RADIUS servers.
Which additional set of tasks must the engineer perform to complete the configuration?
![]()
|
A. |
Disable PMF Enable
PSK Enable 802.1x |
|
B. |
Select WPA
Policy Enable CCKM
Enable PSK |
|
C. |
Select WPA Policy
Select WPA2 Policy
Enable FT PSK |
|
D. |
Select WPA2 Policy
Disable PMF Enable
PSK |
Answer: D
Refer to the exhibit. The entire MAC address table for SW1 is shown here:
![]()
What does SW1 do when Br-4 sends a frame for Br-2?
|
A. |
It performs a lookup in the MAC address table
for Br-4 and discards toe frame due to a missing entry. |
|
B. |
It floods the
frame out or all ports
except on the port where
Br-2 is connected. |
|
C. |
It Inserts the source MAC address and port into
the forwarding table
and forwards the frame to Br- 2. |
|
D. |
It maps the Layer 2 MAC address for Fa0/3 to the Layer
3 IP address and towards the frame. |
Answer: C
Refer to the exhibit. The entire Marketing-SW1 MAC address table is shown here:
![]()
What does the switch do when PC-4 sends a frame to PC-1?
|
A. |
It performs a lookup in the MAC address table
and discards the frame due to a missing entry. |
|
B. |
It maps the Layer
2 MAC address to the Layer 3 IP address and forwards the frame. |
|
C. |
It inserts the source
MAC address and port into the table
and forwards the frame to PC-1. |
|
D. |
It floods the
frame out of all ports
except on the port where
PC-1 is connected. |
Answer: C
Refer to the exhibit. Which switch becomes the root of a spanning tree for VLAN 10 if the primary switch fails and all links are of equal speed?
![]()
|
A. |
SW1 |
|
B. |
SW2 |
|
C. |
SW3 |
|
D. |
SW4 |
Answer: C
Explanation:
Switch 2 is primary. But in this context, that is to say when it fails, the primary is chosen between SW1, SW3 and SW4. Thus, SW3 becomes the root.
Drag and Drop Question
Drag and drop the statements about access-point modes from the left onto the corresponding modes on the right.
![]()
Answer:
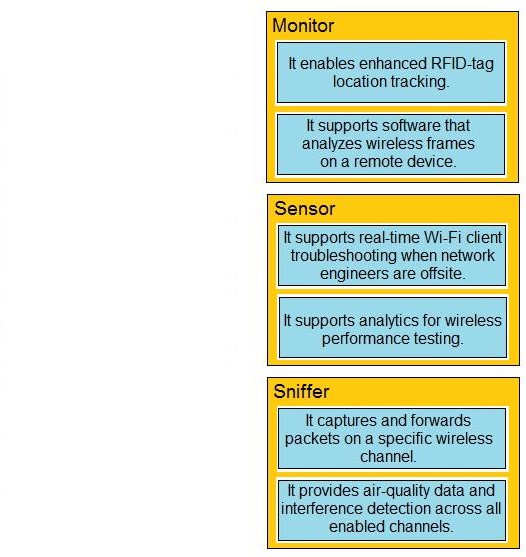
Refer to the exhibit. A packet sourced from 10.10.10.1 is destined for 10.10.8.14. What is the subnet mask of the destination route?
![]()
|
A. |
255.255.254.0 |
|
B. |
255.255.255.240 |
|
C. |
255.255.255.248 |
|
D. |
255.255.255.252 |
Answer:
B
Refer to the exhibit. When an administrator executes the show ip route command on router D to view its routing table, which value is displayed for the administrative distance for the route to network 192.168.1.0?
![]()
|
A. |
110 |
|
B. |
120 |
|
C. |
170 |
|
D. |
90 |
Answer: A
Explanation:
When EIGRP is redistributed the new AD will be 170 (external EIGRP) making OSPF the lowest AD available.
Refer to the exhibit. Which interface is chosen to forward traffic to the host at 192.168.0.55?
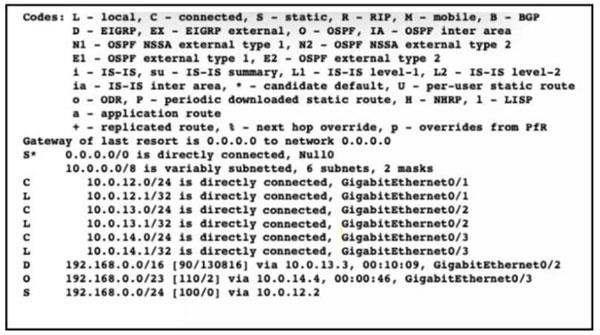
|
A. |
GigabitEthernet0/3 |
|
B. |
Null0 |
|
C. |
GigabitEthernet0/1 |
|
D. |
GigabitEthernet0/2 |
Answer: C
Refer to the exhibit. Router OldR is replacing another router on the network with the intention of having OldR and R2 exchange routes. After the engineer applied the initial OSPF configuration, the routes were still missing on both devices. Which command sequence must be issued before the clear IP ospf process command is entered to enable the neighbor relationship?
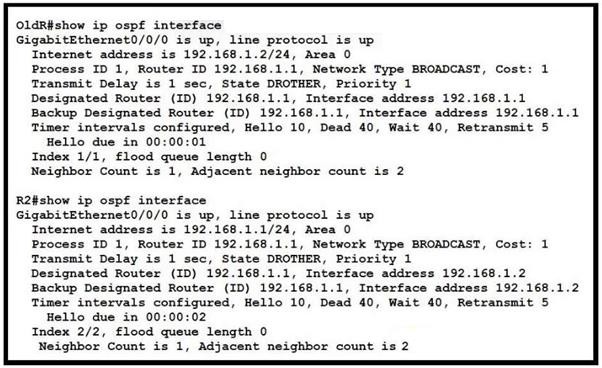
|
A. |
OldR(config)#interface g0/0/0 OldR(config-if)#ip ospf hello-interval 15 |
|
B. |
OldR(config)#router ospf
1 OldR(config-router)#network 192.168.1.0 255.255.255.0 area 2 |
|
C. |
OldR(config)#interface
g0/0/0 OldR(config-if)#ip ospf dead-interval 15 |
|
D. |
OldR(config)#router ospf 1 OldR(config-router)#no router-id 192.168.1.1 |
Answer: D
Explanation:
With OSPF each router must have a unique router ID. Here we see that both routers have a router ID of 192.168.1.1. Removing the router-id command on the
OldR will force it to use one of its actual interface IP addresses as the router ID.
Drag and Drop Question
Refer to the exhibit. Drag and drop the prefix lengths from the left onto the corresponding prefixes on the right. Not all prefixes are used.
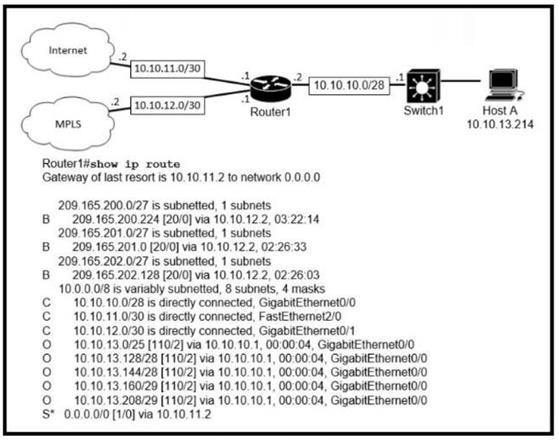
![]()
Answer:
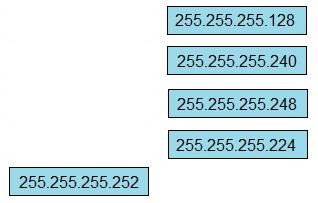
Refer to the exhibit. What is the subnet mask for route 172.16.4.0?
![]()
|
A. |
255.255.255.192 |
|
B. |
255.255.254.0 |
|
C. |
255.255.248.0 |
|
D. |
255.255.240.0 |
Answer: C
Refer to the exhibit. The network engineer is configuring router R2 as a replacement router on the network. After the initial configuration is applied, it is determined that R2 failed to show R1 as a neighbor. Which configuration must be applied to R2 to complete the OSPF configuration and enable it to establish the neighbor relationship with R1?
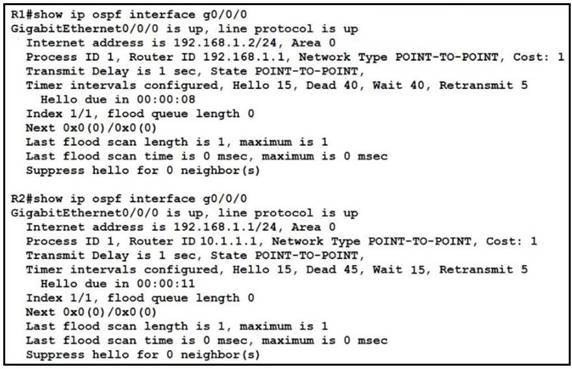
|
A. |
R2(config)#router
ospf 1 R2(config-router)#network 192.168.1.0 255.255.255.0 area 2 |
|
B. |
R2(config)#interface
g0/0/0 R2(config-if)#ip ospf hello-interval 10 |
|
C. |
R2(config)#interface g0/0/0 R2(config-if)#ip ospf dead-interval 40 |
|
D. |
R2(config)#router ospf
1 R2(config-router)#router-id 192.168.1.2 |
Answer: C
Explanation:
For OSPF the hello and dead timers must match to become neighbors. R1 is configured with a dead time of 40 seconds, while R2 is set to 45 seconds.
Refer to the exhibit. The router R1 is in the process of being configured. Routers R2 and R3 are configured correctly for the new environment. Which two commands must be configured on R1 for PC1 to communicate to all PCs on the 10.10.10.0/24 network? (Choose two.)

|
A. |
ip route 10.10.10.0 255.255.255.0 192.168.2.3 |
|
B. |
ip route 10.10.10.10 255.255.255.255 192.168.2.2 |
|
C. |
ip route 10.10.10.10 255.255.255.255 g0/1 |
|
D. |
ip route 10.10.10.8 255.255.255.248 g0/1 |
|
E. |
ip route 10.10.10.0 255.255.255.248 192.168.2.2 |
Answer: AB
Refer to the exhibit. Traffic from R1 to the 10.10.2.0/24 subnet uses 192.168.1.2 as its next hop. A network engineer wants to update the R1 configuration so that traffic with destination 10.10.2.1 passes through router R3, and all other traffic to the 10.10.2.0/24 subnet passes through R2.
Which command must be used?
![]()
|
A. |
ip route 10.10.2.1 255.255.255.255 192.168.1.4115 |
|
B. |
ip route 10.10.2.0 255.255.255.0 192.168.1.4115 |
|
C. |
ip route 10.10.2.0 255.255.255.0 192.168.1.4100 |
|
D. |
ip route 10.10.2.1 255.255.255.255192.168.1.4100 |
Answer: D
Explanation:
Here we need to add a host route for the specific 10.10.2.1 host, which means using a subnet mask of 255.255.255.255. We also need to configure an Administrative Distance that is less than the default OSPF AD of 115.
Refer to the exhibit. The image server and client A are running an application that transfers an extremely high volume of data between the two. An engineer is configuring a dedicated circuit between R1 and R2. Which set of commands must the engineer apply to the routers so that only traffic between the image server and client A is forces to use the new circuit?
![]()
|
A. |
R1(config)#ip route 10.10.13.10 255.255.255.255 10.10.10.6 R2(config)#ip route
192.168.0.100 255.255.255.255 10.10.10.5 |
|
B. |
R1(config)#ip route
10.10.13.10 255.255.255.128 10.10.10.6 R2(config)#lp route
192.168.0.100 255.255.255.0 10.10.10.5 |
|
C. |
R1(config)#ip route
10.10.13.10 255.255.255.252 10.10.10.6 R2(config)#tp route
192.168.0.100 255.255.255.252 10.10.10.5 |
|
D. |
R1(config)#ip route 10.10.13.10 255.255.255.255 10.10.10.2 R2(config)#ip route 192.168.0.100 255.255.255.255 10.10.10.1 |
Answer: A
Refer to the exhibit. An engineer is checking the routing table in the main router to identify the
path to a server on the network. Which route does the router use to reach the server at 192.168.2.2?
![]()
|
A. |
S 192.168.0.0/20 [1/0] via 10.1.1.1 |
|
B. |
S 192.168.2.0/29 [1/0]
via 10.1.1.1 |
|
C. |
S 192.168.2.0/28 [1/0]
via 10.1.1.1 |
|
D. |
S 192.168.1.0/30 [1/0] via 10.1.1.1 |
Answer:
B
Refer to the exhibit. What is the prefix length for the route that router1 will use to reach host A?
![]()
|
A. |
/25 |
|
B. |
/27 |
|
C. |
/28 |
|
D. |
/29 |
Answer: D
Refer to the exhibit. After applying this configuration to router R1, a network engineer is verifying the implementation. If all links are operating normally, and the engineer sends a series of packets from PC1 to PC3, how are the packets routed?
![]()
|
A. |
They are distributed sent round robin
to interfaces S0/0/0
and S0/0/1 |
|
B. |
They are
routed to 10.0.0.2 |
|
C. |
They are
routed to 192.168.100.2 |
|
D. |
They are routed
to 172.16.20.2 |
Answer: D
Refer to the exhibit. How much OSPF be configured on the GigabitEthernet0/0 interface of the neighbor device to achieve the destined neighbor relationship?
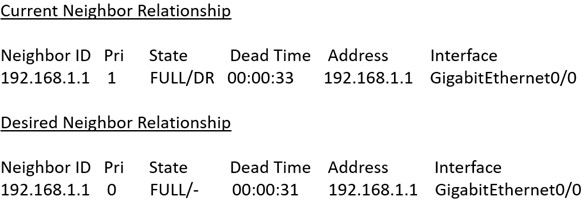
|
A. |
Router(config)#interface GigabitEthernet 0/0 Router(config-if)#ip ospf
cost 5 |
|
B. |
Router(config)#interface GigabitEthernet 0/0
Router(config-if)#ip ospf priority 1 |
|
C. |
Router(config)#interface GigabitEthernet 0/0 Router(config-if)#ip ospf area 2 |
|
D. |
Router(config)#interface
GigabitEthernet 0/0 Router(config-if)#ip ospf network point-to-point |
Answer: D
An engineer just installed network 10.120.10.0/24. Which configuration must be applied to the R14 router to add the new network to its OSPF routing table?
![]()
|
A. |
Router ospf 100 Network 10.120.10.0 0.0.0.255 area 0 |
|
B. |
Router ospf
120 Network 10.120.10.0 255.255.255.0 area 0 ip route 10.120.10.0 255.255.255.0 fa0/1 |
|
C. |
Router ospf 100 area 0 Network 10.120.10.0 0.0.0.255 |
|
D. |
Router ospf 100
Network 10.120.10.0 255.255.255.0 area 0 |
Answer:
A
Refer to the exhibit. Router R1 is added to the network and configured with the 10.0.0.64/26 and 10.0.20.0/26 subnets. However, traffic destined for the LAN on R3 is not accessible. Which command when executed on R1 defines a static route to reach the R3 LAN?
![]()
|
A. |
ip route 10.0.0.64 255.255.255.192 10.0.20.3 |
|
B. |
ip route 10.0.15.0 255.255.255.0 10.0.20.1 |
|
C. |
ip route 10.0.15.0 255.255.255.192 10.0.20.1 |
|
D. |
ip route 10.0.15.0 255.255.255.0 10.0.20.3 |
Answer: D
Explanation:
We need to specify the destination network (10.0.15.0/24) and the next hop IP of the router to get to that network (10.0.20.3).
Drag and Drop Question
Drag and drop the functions of SNMP fault-management from the left onto the definitions on the right.
![]()
Answer:
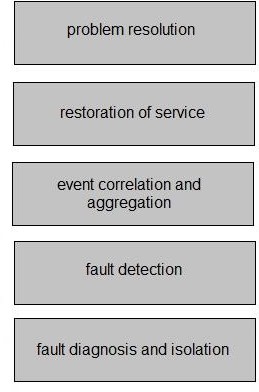
Refer to the exhibit. Which router or router group are NTP clients?

|
A. |
R1 |
|
B. |
R2 and R3 |
|
C. |
R1, R3, and R4 |
|
D. |
R1, R2, and R3 |
Answer: D
Refer to the exhibit. What is the next step to complete the implementation for the partial NAT configuration shown?
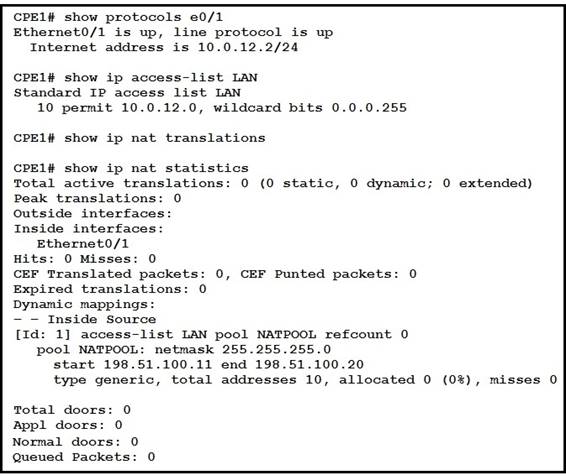
|
A. |
Modify the access
list for the
internal network on
e0/1. |
|
B. |
Reconfigure the
static NAT entries that overlap the
NAT pool. |
|
C. |
Apply the ACL to the pool
configuration. |
|
D. |
Configure the NAT outside interface. |
Answer: D
Refer to the exhibit. A newly configured PC fails to connect to the internet by using TCP port 80 to www.cisco.com. Which setting must be modified for the connection to work?

|
A. |
Subnet Mask |
|
B. |
DNS Servers |
|
C. |
Default Gateway |
|
D. |
DHCP Servers |
Answer:
B
Drag and Drop Question
Drag and drop the statements about AAA from the left onto the corresponding AAA services on the right. Not all options are used.
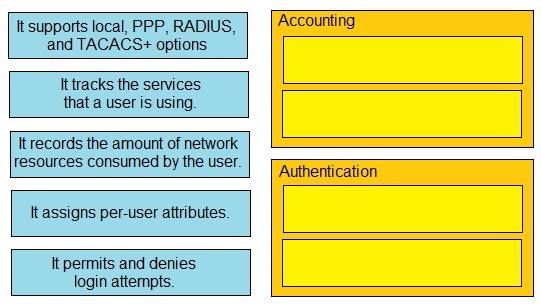
Answer:
![]()
SW1 supports connectivity for a lobby conference room and must be secured. The engineer must limit the connectivity from PC1 to the SW1 and SW2 network.
The MAC addresses allowed must be limited to two. Which configuration secures the conference room connectivity?
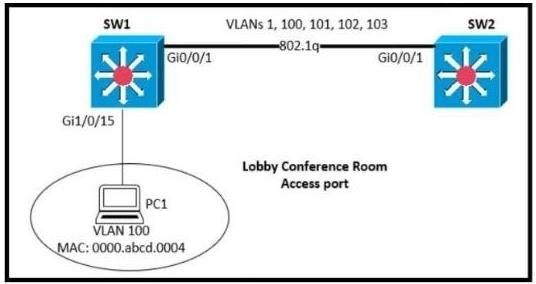
|
A. |
interface
gi1/0/15 switchport port-security switchport port-security maximum 2 |
|
B. |
interface
gi1/0/15 switchport port-security switchport port-security mac-address 0000.abcd.0004vlan 100 |
|
C. |
interface gi1/0/15 switchport port-security mac-address 0000.abcd.0004 vlan 100 |
|
D. |
interface gi1/0/15 switchport port-security mac-address 0000.abcd.0004 vlan 100 interface switchport secure-mac
limit 2 |
Answer:
A
Refer to the exhibit. An engineer is updating the management access configuration of switch SW1 to allow secured, encrypted remote configuration. Which two commands or command sequences must the engineer apply to the switch? (Choose two.)
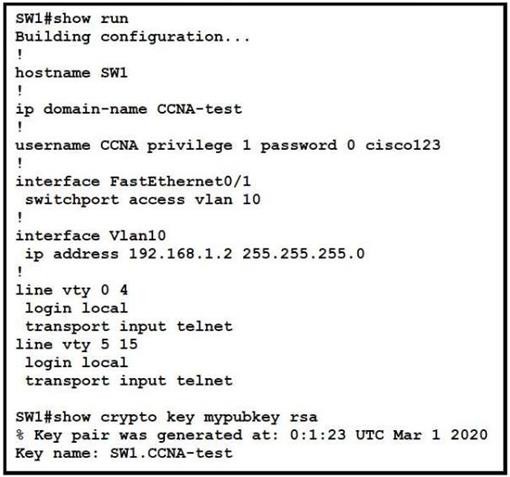
|
A. |
SW1(config)#enable secret ccnaTest123 |
|
B. |
SW1(config)#username NEW secret R3mote123 |
|
C. |
SW1(config)#line vty 0 15
SW1(config-line)#transport input ssh |
|
D. |
SW1(config)# crypto
key generate rsa |
|
E. |
SW1(config)# interface f0/1 SW1(confif-if)# switchport mode trunk |
Answer:
BC
Refer to the exhibit. What is identified by the word `switch` within line 2 of the JSON Schema?
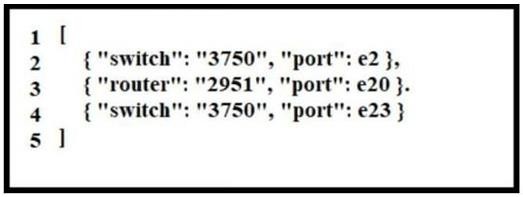
|
A. |
array |
|
B. |
value |
|
C. |
object |
|
D. |
key |
Answer: B
Explanation:
Key-value pairs have a colon between them as in "key" : "value".
Refer to the exhibit. Which type of JSON data is shown?
![]()
|
A. |
boolean |
|
B. |
array |
|
C. |
key |
|
D. |
object |
Answer: D
Drag and Drop Question
Drag and drop the characteristics from the left onto the technology types on the right.
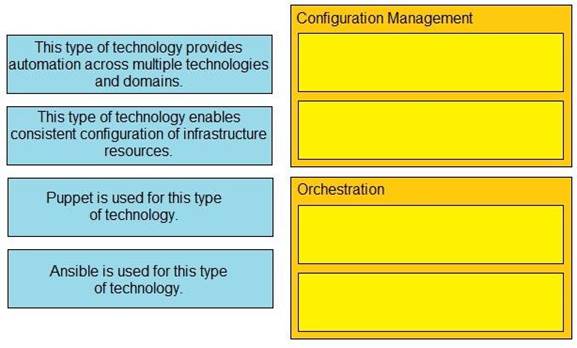
Answer:
![]()
Drag and Drop Question
Drag and drop the REST API call methods for HTTP from the left onto the actions they perform
on the right. Not all methods are used.
![]()
Answer:
![]()
Drag and Drop Question
Drag and drop the REST principles from the left onto their definitions on the right.
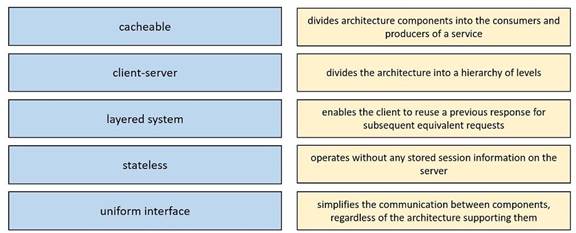
Answer:
![]()
Drag and Drop Question
Drag and drop the Ansible terms from the left onto the right.
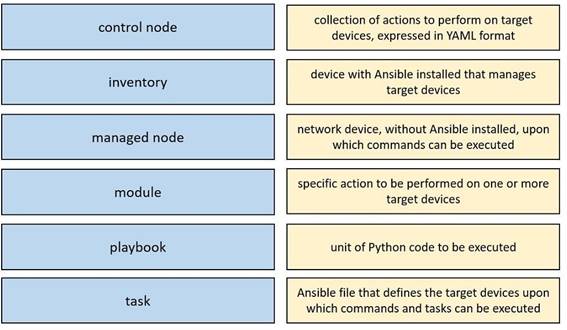
Answer:
![]()
Refer to the exhibit. How many objects keys, and JSON list values are present?
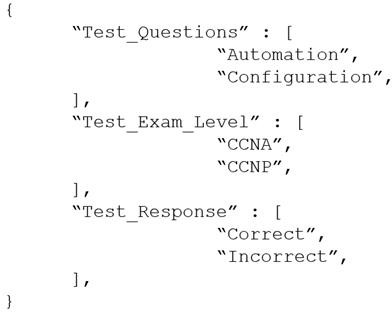
|
A. |
Three objects, two keys, and three JSON
list values |
|
B. |
Three objects, three keys, and two JSON list values |
|
C. |
One object, three keys,
and three JSON
list values |
|
D. |
One object, three
keys, and two JSON list
values |
Answer: C
Drag and Drop Question
Drag and drop the statements about networking from the left onto the corresponding networking types on the right.
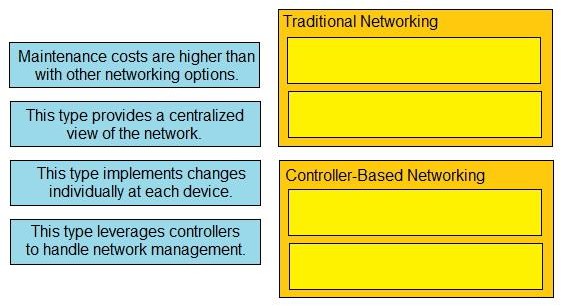
Answer:
![]()
Refer to the exhibit. A network engineer must configure NETCONF. After creating the configuration, the engineer gets output from the command show line but not from show running- config. Which command completes the configuration?
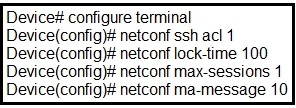
|
A. |
Device(config)#
netconf lock-time 500 |
|
B. |
Device(config)# netconf max-message 1000 |
|
C. |
Device(config)# no netconf ssh
acl 1 |
|
D. |
Device(config)#
netconf max-sessions 100 |
Answer:
B
Which functionality is provided by the console connection on a Cisco WLC?
|
A. |
out-of-band management |
|
B. |
secure in-band
connectivity for device
administration |
|
C. |
unencrypted in-band connectivity for file transfers |
|
D. |
HTTP-based GUI connectivity |
Answer:
B
What determines the sequence in which materials are planned during the material requirements planning (MRP) run?
|
A. |
The control parameters of the MRP run |
|
B. |
The creation date of the materials |
|
C. |
The low-level code of the materials |
|
D. |
The replenishment lead
time of the
materials |
Answer: C
Refer to the exhibit. After configuring a new static route on the CPE. The engineer entered this series of commands to verify that the new configuration is operating normally.
When is the static default route installed into the routing table?
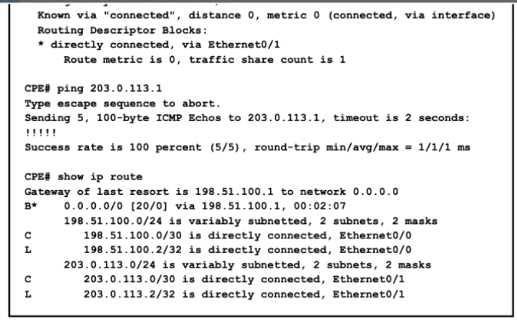
|
A. |
when 203.0.113.1 is no longer
reachable as a next hop |
|
B. |
when the default route
learned over external BGP becomes invalid |
|
C. |
when a route to 203.0.113.1 is learned via BGP |
|
D. |
when the default route over external BGP changes its
next hop |
Answer:
A
How does encryption project the wireless network?
|
A. |
via integrity checks
to identify wireless forgery attacks in the frame |
|
B. |
via specific ciphers to detect and prevent zero-day network attacks |
|
C. |
via an algorithm to change wireless data so that
only the access
point and client
understand it |
|
D. |
via a policy
to prevent unauthorized users from communicating on the wireless network |
Answer: C
Which two cable types must be used to connect an access point to the WLC when 2.5-Gbps and 5-Gbps upload speeds are required? (Choose two.)
|
A. |
10GBASE-T |
|
B. |
1000BASE-LX/LH |
|
C. |
Cat 5e |
|
D. |
Cat 5 |
|
E. |
Cat 3 |
Answer:
AC
An engineer must update the configuration on two PCs in two different subnets to communicate locally with each other. One PC is configured with IP address 192.168.25.128/25 and the other with 192.168.25.100/25.
Which network mask must the engineer configure on both PCs to enable the communication?
|
A. |
255.255.255.248 |
|
B. |
255.255.255.224 |
|
C. |
255.255.255.0 |
|
D. |
255.255.255.252 |
Answer: C
A packet from a company's branch office is destined to host 172.31.0.1 at headquarters. The sending router has three possible matches in its routing table for the packet: prefixes 172.31.0.0/16, 172.31.0.0/24, and 172.31.0.0/25. How does the router handle the packet?
|
A. |
It sends the traffic via prefix 172.31.0.0/16 |
|
B. |
It sends the traffic
via the default
gateway 0.0.0.0/0 |
|
C. |
It sends the traffic
via prefix 172.31.0.0/24 |
|
D. |
It sends the traffic via prefix 172.31.0.0/25 |
Answer: D
Which key function is provided by the data plane?
|
A. |
Originating packets |
|
B. |
Exchanging routing
table data |
|
C. |
Making routing decisions |
|
D. |
Forwarding traffic to the next
hop |
Answer: D
In a cloud-computing environment what is rapid elasticity?
|
A. |
control and monitoring of resource consumption by the tenant |
|
B. |
automatic adjustment of capacity based
on need |
|
C. |
pooling resources in a multitenant model based on need |
|
D. |
self-service of computing resources by the tenant |
Answer:
B
What is a reason to implement IPv4 private addressing?
|
A. |
Reduce the risk
of a network security breach |
|
B. |
Comply with PCI
regulations |
|
C. |
Comply with local law |
|
D. |
Reduce the size
of the forwarding table on network
routers |
Answer: D
A client experiences slow throughput from a server that is directly connected to the core switch in a data center. A network engineer finds minimal latency on connections to the server, but data transfers are unreliable, and the output of the show interfaces counters errors command shows a high FCS-Err count on the interface that is connected to the server.
What is the cause of the throughput issue?
|
A. |
a physical cable
fault |
|
B. |
a speed mismatch |
|
C. |
high bandwidth usage |
|
D. |
a cable that is too long |
Answer:
A
What is the purpose of configuring different levels of syslog for different devices on the network?
|
A. |
to rate-limit messages for different seventy
levels from each
device |
|
B. |
to set the severity of syslog messages from each device |
|
C. |
to identify the source
from which each
syslog message originated |
|
D. |
to control the number of syslog messages from different devices that are stored
locally |
Answer:
B
What are two reasons to implement IPv4 private addressing on a network? (Choose two.)
|
A. |
To enable internal applications to treat
the private IPv4 addresses as unique |
|
B. |
To facilitate renumbering when
merging networks |
|
C. |
To expand the routing table on the
router |
|
D. |
To provide protection from external denial-of-service attacks |
|
E. |
To conserve global
unique IPv4 addresses |
Answer:
AE
Explanation:
Private IPv4 addresses weren't created to be a form of protection. It's primary purpose was to enable internal networks to communicate while conserving public IPv4 addresses.
A fits this narrative as multiple businesses could share the same private IP addresses and their application would still be able to communicate without interfering with other businesses thus it's unique to their internal applications.
Which concern is addressed with the use of private IPv4 addressing?
|
A. |
Lack of routing protocol support for CIDR and VLSM |
|
B. |
Lack of security protocols at the network perimeter |
|
C. |
Lack of available TCP/UDP
ports per IPv5
address |
|
D. |
Lack of available publicly routable unique
IPv4 address |
Answer: D
What is the path for traffic sent from one user workstation to another workstation on a separate switch in a three-tier architecture model?
|
A. |
access - core
- distribution -
access |
|
B. |
access - distribution - distribution - access |
|
C. |
access - core - access |
|
D. |
access - distribution - core - distribution - access |
Answer:
B
Refer to the exhibit. When router R1 receives a packet with destination IP address 10.56.0.62 through which interface does it route the packet?
![]()
|
A. |
Null0 |
|
B. |
VIan58 |
|
C. |
Vlan60 |
|
D. |
VIan59 |
Answer:
B
What are two features of the DHCP relay agent? (Choose two.)
|
A. |
assigns DNS locally and then forwards request to DHCP
server |
|
B. |
permits one IP helper command under an individual Layer 3 interface |
|
C. |
allows only MAC-to-IP reservations to determine the local subnet
of a client |
|
D. |
minimizes the
necessary number of DHCP servers |
|
E. |
configured under the Layer 3 interface of a router
on the client
subnet |
Answer:
BE
Which is a fact related to FTP?
|
A. |
It uses block
numbers to identify and mitigate data-transfer errors |
|
B. |
It always operates without
user authentication |
|
C. |
It relies on the well-known UDP port 69. |
|
D. |
It uses two
separate connections for
control and data
traffic |
Answer: D
Which switching concept is used to create separate broadcast domains?
|
A. |
STP |
|
B. |
VTP |
|
C. |
VLAN |
|
D. |
CSMA/CD |
Answer: C
Refer to the exhibit. A packet sourced from 172.18.33.2 is destined for 172.18.32.38. Where does the router forward the packet?
![]()
|
A. |
GigabitEthernet0/0 |
|
B. |
Loopback0 |
|
C. |
10.1.1.1 |
|
D. |
10.1.1.3 |
Answer:
B
Which command configures the Cisco WLC to prevent a serial session with the WLC CLI from being automatical togged out?
|
A. |
config sessions maxsessions 0 |
|
B. |
config sessions timeout 0 |
|
C. |
config serial
timeout 0 |
|
D. |
config serial timeout 9600 |
Answer:
B
Refer to the exhibit. How many JSON objects are presented?
![]()
|
A. |
1 |
|
B. |
2 |
|
C. |
3 |
|
D. |
4 |
Answer: D
Which enhancement is implemented in WPA3?
|
A. |
applies 802.1x authentication |
|
B. |
uses TKIP |
|
C. |
employs PKI
to identify access
points |
|
D. |
protects against brute
force attacks |
Answer: D
What must be considered for a locally switched FlexConnect AP if the VLANs that are used by the AP and client access are different?
|
A. |
The APs must
be connected to the switch
with multiple links
in LAG mode |
|
B. |
The switch port mode
must be set
to trunk |
|
C. |
The native VLAN must
match the management VLAN of the
AP |
|
D. |
IEEE 802.10 trunking must be disabled on the switch
port. |
Answer: C
Which type of port is used to connect the wired network when an autonomous AP maps two VLANs to its WLANs?
|
A. |
access |
|
B. |
LAG |
|
C. |
trunk |
|
D. |
EtherChannel |
Answer: C
What is an advantage of using auto mode versus static mode for power allocation when an access point is connected to a PoE switch port?
|
A. |
All four pairs
of the cable
are used |
|
B. |
It detects the device
is a powered device |
|
C. |
The default level is used for the access
point |
|
D. |
Power policing is enabled at the same
time |
Answer: D
Which protocol must be implemented to support separate authorization and authentication solutions for wireless APs?
|
A. |
RADIUS |
|
B. |
TACACS+ |
|
C. |
802.1X |
|
D. |
Kerberos |
Answer:
B
Explanation:
Authentication and Authorization
RADIUS combines authentication and authorization. The access-accept packets sent by the RADIUS server to the client contain authorization information. This makes it difficult to decouple authentication and authorization.
TACACS+ uses the AAA architecture, which separates AAA. This allows separate authentication solutions that can still use TACACS+ for authorization and accounting. For example, with TACACS+, it is possible to use Kerberos authentication and TACACS+ authorization and accounting. After a NAS authenticates on a Kerberos server, it requests authorization information from a TACACS+ server without having to re-authenticate. The NAS informs the TACACS+ server that it has successfully authenticated on a Kerberos server, and the server then provides
authorization information.
What is a function of an endpoint?
|
A. |
It is used directly by an individual user to access
network services |
|
B. |
It passes unicast communication between hosts in a network |
|
C. |
It transmits broadcast traffic
between devices in the same
VLAN |
|
D. |
It provides security between trusted and untrusted sections of the network. |
Answer:
A
What must a network administrator consider when deciding whether to configure a new wireless network with APs in autonomous mode or APs running in cloud- based mode?
|
A. |
Autonomous mode APs are less
dependent on an underlay but more complex to maintain than APs in cloud-based mode. |
|
B. |
Cloud-based mode APs
relay on underlays and are more
complex to maintain than APs in autonomous mode. |
|
C. |
Cloud-based mode
APs are easy
to deploy but harder to automate than
APs in autonomous mode. |
|
D. |
Autonomous mode APs
are easy to deploy and automate than
APs in cloud-based mode. |
Answer:
A
Refer to the exhibit. Wireless LAN access must be set up to force all clients from the NA WLAN to authenticate against the local database. The WLAN is configured for local EAP authentication.
The time that users access the network must not be limited. Which action completes this configuration?
![]()
|
A. |
Uncheck the Guest
User check box |
|
B. |
Check the Guest
User Role check
box |
|
C. |
Set the Lifetime (seconds) value to 0 |
|
D. |
Clear the Lifetime (seconds) value |
Answer: C
Which state is bypassed in Rapid PVST+ when PortFast is enabled on a port?
|
A. |
blocking |
|
B. |
forwarding |
|
C. |
learning |
|
D. |
discarding |
Answer: C
What happens when a switch receives a frame with a destination MAC address that recently aged out?
|
A. |
The switch
floods the frame
to all ports
in all VLANs
except the port
that received the
frame. |
|
B. |
The switch floods the frame to all ports
in the VLAN
except the port
that received the
frame. |
|
C. |
The switch
references the MAC
address aging table
for historical addresses on the port that
received the frame. |
|
D. |
The switch
drops the frame
and learns the
destination MAC address again from the port that received the frame. |
Answer:
B
What is a function of store-and forward switching?
|
A. |
It reduces latency
by eliminating error
checking within the frame |
|
B. |
It produces an effective level of error-free network traffic using
CRCs. |
|
C. |
It buffers frames and forwards regardless of errors within
the frames. |
|
D. |
It forwards a frame by checking only
the destination MAC
address |
Answer:
B
Which WLC interface provides out-of-band management in the Cisco Unified Wireless Network Architecture?
|
A. |
AP-Manager |
|
B. |
service port |
|
C. |
dynamic |
|
D. |
virtual |
Answer: B
Which mode must be set for Aps to communicate to a Wireless LAN Controller using the Control and Provisioning of Wireless Access Points (CAPWAP) protocol?
|
A. |
route |
|
B. |
bridge |
|
C. |
lightweight |
|
D. |
autonomous |
Answer: C
What are two reasons a switch experiences frame flooding? (Choose two.)
|
A. |
A defective patch
cable is connected to the switch
port |
|
B. |
Topology changes are occurring within
spanning-tree |
|
C. |
An aged MAC (able
entry is causing excessive updates |
|
D. |
Port-security is configured globally |
|
E. |
The forwarding table
has overflowed |
Answer: AB
Refer to the exhibit. A network engineer must configure router R1 with a host route to the server. Which command must the engineer configure?
![]()
|
A. |
R1(conftg)#lp route 10.10.10.0 255.255.255.0 192.168.0.2 |
|
B. |
R1(Config)#lp route
10.10.10.10 265.255.255.255 192.168.0.2 |
|
C. |
R1(config)#ip route
192.168.0.2 255.255.255.255 10.10.10.10 |
|
D. |
R1(config)3|p route 0.0.0.0 0.0.0.0 192.168.0.2 |
Answer:
B
A Cisco engineer at a new branch office is configuring a wireless network with access points that connect to a controller that is based at corporate headquarters Wireless client traffic must terminate at the branch office and access-point survivability is required in the event of a WAN outage Which access point mode must be selected?
|
A. |
Lightweight with local
switching disabled |
|
B. |
Local with AP fallback enabled |
|
C. |
OfficeExtend with
high availability disabled |
|
D. |
FlexConnect with local
switching enabled |
Answer: C
Refer to Itie exhibit. A network engineer started to configure port security on a new switch. These requirements must be met:
* MAC addresses must be learned
dynamically
* Log messages must be generated without disabling the interface when unwanted traffic is seen
Which two commands must be configured to complete this task? (Choose two)
![]()
|
A. |
SW(ccnfig-if)=switchport port-security mac-address sticky |
|
B. |
SW(confKj-if)=switchport port-security violation restrict |
|
C. |
SW(config.if)sswitchport port-security mac-address 0010.7B84.45E6 |
|
D. |
SW(config-if)aswitchport port-security maximum 2 |
|
E. |
SW(ccnfig-if)=switchport port-security violation shutdown |
Answer: C
Which channel-group mode must be configured when multiple distribution interfaces connected to a WLC are bundled?
|
A. |
Channel-group mode passive. |
|
B. |
Channel-group mode on. |
|
C. |
Channel-group mode
desirable. |
|
D. |
Channel-group mode active. |
Answer:
B
Refer the exhibit. What is the cause of poor performance on router R19?
![]()
|
A. |
excessive collisions |
|
B. |
speed and duplex mismatch |
|
C. |
port oversubscription |
|
D. |
excessive CRC errors |
Answer:
A
What is a function of MAC learning on a switch?
|
A. |
MAC address learning is disabled by default on all VLANs. |
|
B. |
Frames received for
a destination MAC address not
listed in the
address table are
dropped. |
|
C. |
The MAC
address table is used to populate the ARP table. |
|
D. |
A static MAC address is manually added
to the MAC table. |
Answer: C
What is a similarity OM3 and OM4 fiber optical cable?
|
A. |
Both have a 62.5 micron
core diameter. |
|
B. |
Both have
a 50 micron core diameter. |
|
C. |
Both have
a 100 micron
core diameter. |
|
D. |
Both have a 9 micron
core diameter. |
Answer:
B
What does a switch do when it receives a frame whose destination MAC address is missing from the MAC address table?
|
A. |
It changes the checksum of the frame
to a value that indicates an invalid frame. |
|
B. |
It updates the CAM table with
the destination MAC address of the frame. |
|
C. |
It appends the table
with a static
entry for the MAC and shuts down the port. |
|
D. |
It floods the frame unchanged across all remaining ports in the incoming VLAN. |
Answer: D
Explanation:
If the address is in the table, the frame is forwarded out the port associated with the MAC address in the table. When the DESTINATION MAC address is not found in the MAC address table, the switch forwards the frame out of all ports (flooding) except for the ingress port of the frame.
Refer to the exhibit. Which configuration for RTR-1 deniess SSH access from PC-1 to any RTR-1 interface and allows all other traffic?
![]()
|
A. |
|
|
B. |
|
|
C. |
|
|
D. |
|
Answer:
B
An engineer is configuring a switch port that is connected to a VoIP handset.
Which command must the engineer configure to enable port security with a manually assigned MAC address of abod-bod on voice VLAN 4?
|
A. |
switchport port-security mac-address abcd.abcd.abcd |
|
B. |
switchport port-security mac-address abed.abed.abed vlan
4 |
|
C. |
switchport port-security mac-address sticky abcd.abcd.abcd vlan 4 |
|
D. |
switchport port-security mac-address abcd.abcd.abcd vlan voice |
Answer:
A
By default, how long will the switch continue to know a workstation MAC address after the workstation stops sending traffic?
|
A. |
200 seconds |
|
B. |
300 seconds |
|
C. |
600 seconds |
|
D. |
900 seconds |
Answer: B
Refer to the exhibit. Which entry is the longest prefix match for host IP address 192.168.10.5?
![]()
|
A. |
1 |
|
B. |
2 |
|
C. |
3 |
|
D. |
4 |
Answer:
B
What is the function of northbound API?
|
A. |
It upgrades software and restores files. |
|
B. |
It relies on global
provisioning and configuration. |
|
C. |
It supports distributed processing for configuration. |
|
D. |
It provides a path between an SDN controller and network applications. |
Answer: D
Which interface enables communication between a program on the controller and a program on the networking devices?
|
A. |
northbound interface |
|
B. |
software virtual interface |
|
C. |
southbound interface |
|
D. |
tunnel Interface |
Answer:
B
Refer to the exhibit. The loopback1 interface of the Atlanta router must reach the lookback3 interface of the Washington router.
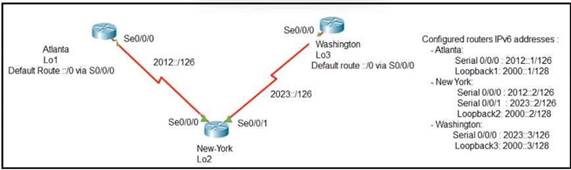
|
A. |
ipv6 route 2000::1/128 2012::2 |
|
B. |
ipv6 route
2000::1/128 2012::1 |
|
C. |
ipv6 route
2000:3/123 s0/0/0 |
|
D. |
ipv6 route
2000::3/128 2023::3 |
|
E. |
ipv6 route 2000::1/128 s0/0/1 |
Answer: BD
Refer to the exhibit. Which action by the router when a packet is sourced from 10.10.10.2 and destined 10.10.10.16?
![]()
|
A. |
It queues the packets waiting
for the route
to be learned. |
|
B. |
It floods packets to all learned next hops. |
|
C. |
It discards the packets. |
|
D. |
It uses a route that
is similar to the destination address. |
Answer: D
A project objective is to minimize the association time to the different access points as mobile devices move around the office. The ideal solution must cover numerous devices and device types, including laptops, mobile phones, tablets and wireless printers. What must be configured?
|
A. |
802.11v BSS Max Idle Service |
|
B. |
802.11v Disassociation Imminent |
|
C. |
802.11ax BSS configure |
|
D. |
802.11k neighbor List
Dual Band |
Answer:
B
Which security method is used to prevent man-in-the-middle attack?
|
A. |
authorization |
|
B. |
authentication |
|
C. |
anti-replay |
|
D. |
accounting |
Answer:
B
Which two protocols are used by an administrator for authentication and configuration on access points? (Choose two.)
|
A. |
802.1Q |
|
B. |
RADIUS |
|
C. |
Kerberos |
|
D. |
TACACS+ |
|
E. |
802.1x |
Answer: BD
Which IPsec transport mode encrypts the IP header and the payload?
|
A. |
pipe |
|
B. |
control |
|
C. |
transport |
|
D. |
tunnel |
Answer: D
Refer to the exhibit. PC1 regularly sends 1800 Mbps of traffic to the server. A network engineer needs to configure the EtherChannel to disable Port Channel 1 between SW1 and SW2 when the Ge0/0 and Ge0/1 ports on SW2 go down. Which configuration must the engineer apply to the switch?
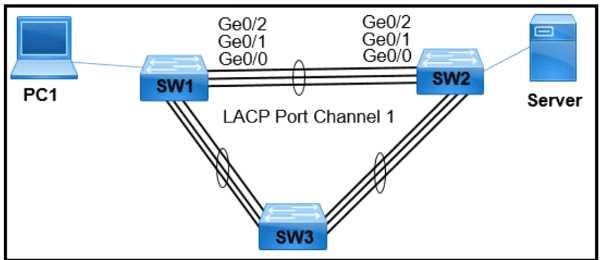
|
A. |
|
|
B. |
|
|
C. |
|
|
D. |
|
Answer: D
Refer to the exhibit. Which command must be enable a floating default route on router A?
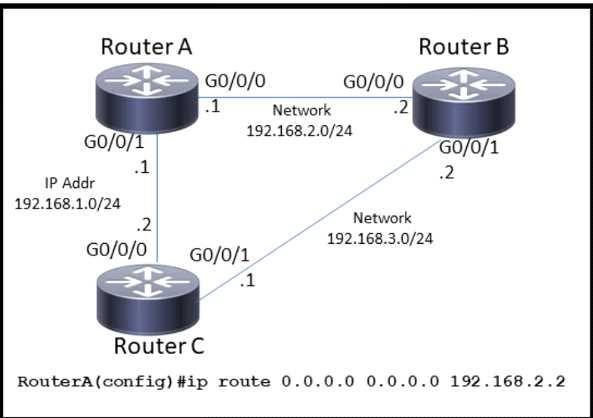
|
A. |
ip route 0.0.0.0
0.0.0.0 192.168.1.2 |
|
B. |
ip default-gateway 192.168.2.1 |
|
C. |
ip route 0.0.0.0 0.0.0.0 192.168.1.2 10 |
|
D. |
ip route 0.0.0.0
0.0.0.0 192.168.2.1 10 |
Answer: C
Refer to the exhibit. How must OSPF be configured on the GigabitEthernet0/0 interface of the neighbor device to achieve.
![]()
|
A. |
|
|
B. |
|
|
C. |
|
|
D. |
|
Answer:
A
What is the purpose of using First Hop Redundancy Protocol on a specific subnet?
|
A. |
ensures a loop-free physical topology |
|
B. |
filters traffic based on destination IP addressing |
|
C. |
sends the default route
to the hosts
on a network |
|
D. |
forwards multicast hello
messages between routers |
Answer: D
Which two features introduced in SNMPv2 provides the ability to retrieve large amounts of data in one request?
|
A. |
Get |
|
B. |
GetNext |
|
C. |
Set |
|
D. |
GetBulk |
|
E. |
Inform |
Answer: AD
Refer to the exhibit. A multivendor network exists and the company is implementing VoIP over the network for the first time.
|
A. |
|
|
B. |
|
|
C. |
|
|
D. |
|
Answer:
B
Refer to the exhibit. A network engineer must update the configuration on Switch2 so that it sends LLDP packets every minute and the information sent via LLDP is refreshed every 3 minutes.
Which configuration must the engineer apply?
![]()
|
A. |
|
|
B. |
|
|
C. |
|
|
D. |
|
Answer: C
Which IPv6 address range is suitable for anycast addresses for distributed services such DHCP or DNS?
|
A. |
FF00:1/12 |
|
B. |
2001:db8:0234:ca3e::1/128 |
|
C. |
2002:db84:3f37:ca98:be05:8/64 |
|
D. |
FE80::1/10 |
Answer:
A
A WLC sends alarms about a rogue AP, and the network administrator verifies that the alarms are caused by a legitimate autonomous AP. How must the alarms be stopped for the MAC address of the AP?
|
A. |
Remove the AP from WLC
management |
|
B. |
Place the AP into manual containment. |
|
C. |
Manually remove
the AP from
Pending state. |
|
D. |
Set the AP Class Type
to Friendly. |
Answer: D
When an access point is seeking to join wireless LAN controller, which message is sent to the AP-Manager interface?
|
A. |
Discovery response |
|
B. |
DHCP request |
|
C. |
DHCP discover |
|
D. |
Discovery request |
Answer: D
What is the primary purpose of private address space?
|
A. |
conserve globally unique
address space |
|
B. |
simplify the addressing in the network |
|
C. |
limit the number of nodes reachable via the Internet |
|
D. |
reduce network complexity |
Answer:
A
Refer to the exhibit. The P2P blocking action option is disabled on the WLC.
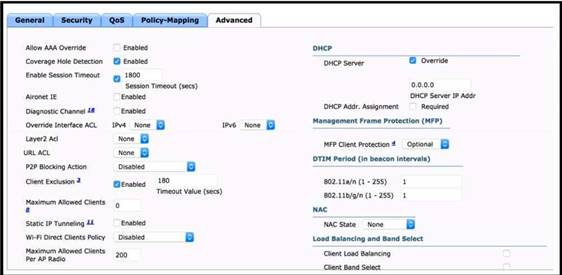
|
A. |
Enable the Static
IP Tunneling option. |
|
B. |
Disable the Coverage Hole Detection option. |
|
C. |
Check the
DHCP Addr. Assignment check box. |
|
D. |
Set the P2P Blocking Action
option to Forward-UpStream. |
Answer:
A
Which 802.11 frame type is Association Response?
|
A. |
management |
|
B. |
protected frame |
|
C. |
action |
|
D. |
control |
Answer: A
Explanation:
There are three main types of 802.11 frames: the Data Frame, the Management Frame and the Control Frame. Association Response belongs to Management Frame. Association response is sent in response to an association request.
Reference: https://en.wikipedia.org/wiki/802.11_Frame_Types
What is a reason to configure a trunk port that connects to a WLC distribution port?
|
A. |
Eliminate redundancy with
a link failure in the data
path. |
|
B. |
Allow multiple VLAN to be used in the data
path. |
|
C. |
Provide redundancy if there is a link
failure for out-of-band management. |
|
D. |
Permit multiple VLANs
to provide out-of-band management. |
Answer: D
What is a purpose of traffic shaping?
|
A. |
It enables dynamic flow identification. |
|
B. |
It enables policy-based routing. |
|
C. |
It provides best-effort service. |
|
D. |
It limits bandwidth usage. |
Answer:
A
What is a characteristics of a collapsed-core network topology?
|
A. |
It allows the
core and distribution layers to run as a single combined layer. |
|
B. |
It enables
the core and
access layers to connect to one logical distribution device over
an EtherChannel. |
|
C. |
It enables all workstations in a SOHO
environment to connect on a single
switch with internet access. |
|
D. |
It allows wireless devices to connect directly to the
core layer, which
enables faster data transmission. |
Answer:
B
To improve corporate security, an organization is planning to implement badge authentication to limit access to the data center. Which element of a security program is being deployed?
|
A. |
user training |
|
B. |
user awareness |
|
C. |
vulnerability verification |
|
D. |
physical access control |
Answer: D
Which SDN plane forwards user-generated traffic?
|
A. |
Management plane |
|
B. |
Control plane |
|
C. |
Policy plane |
|
D. |
Data plane |
Answer: D
Refer to the exhibit. An engineer executed the script and added commands that were not necessary for SSH and now must remove the commands.
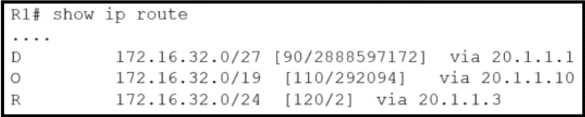
|
A. |
metric |
|
B. |
cost |
|
C. |
longest prefix |
|
D. |
administrative distance |
Answer: D
Which cipher is supported for wireless encryption only with the WPA2 standard?
|
A. |
AES256 |
|
B. |
AES |
|
C. |
RC4 |
|
D. |
SHA |
Answer:
B
What is a specification for SSIDS?
|
A. |
They are a Cisco proprietary security feature. |
|
B. |
They must
include one number
and one letter. |
|
C. |
They define
the VLAN on a switch. |
|
D. |
They are case
sensitive. |
Answer:
B
Refer to the exhibit. How does router R1 handle traffic to the 172.16.1.4/30 subnet?
|
A. |
It sends all traffic over the path via 172.16.9.5 using 172.16.4.4 as a backup. |
|
B. |
It sends all traffic
over the path via 10.0.1.100. |
|
C. |
It load-balances traffic over
172.16.9.5 and 172.16.4.4. |
|
D. |
It sends all traffic over the path via 172.16.4.4. |
Answer: C
An application in the network is being scaled up from 300 servers to 600. Each server requires 3 network connections to support production, backup, and management traffic. Each connection resides on a different subnet. The router configuration for the production network must be
configured first using a subnet in the 10.0.0.0/8 network.
Which command must be configured on the interface of the router to accommodate the requirements and limit wasted IP address space?
|
A. |
ip address 10.10.10.1 255.255.254.0 |
|
B. |
ip address 10.10.10.1 255.255.252.0 |
|
C. |
ip address 10.10.10.1 255.255.240.0 |
|
D. |
ip address 10.10.10.1 255.255.255.240 |
Answer:
B
Which device segregates a network into separate zones that have their own security policies?
|
A. |
IPS |
|
B. |
firewall |
|
C. |
access point |
|
D. |
switch |
Answer: C
Refer to the exhibit. A packet sourced from 10.10.10.32 is destined for the internet.
![]()
|
A. |
0 |
|
B. |
1 |
|
C. |
2 |
|
D. |
32 |
Answer:
B
Why implement VRRP?
|
A. |
To hand over
to end users
the autodiscovery of virtual gateways |
|
B. |
To provide end
users with a virtual gateway
in a multivendor network |
|
C. |
To leverage a weighting scheme to provide
uninterrupted service |
|
D. |
To detect link failures without
the overhead of Bidirectional Forwarding Detection |
Answer:
B
Which type of address is shared by routers in a HSRP implementation and used by hosts on the subnet as their default gateway address?
|
A. |
multicast address |
|
B. |
virtual IP
address |
|
C. |
loopback IP address |
|
D. |
broadcast address |
Answer:
B
Which type of IPv4 address type helps to conserve the globally unique address classes?
|
A. |
multicast |
|
B. |
private |
|
C. |
loopback |
|
D. |
public |
Answer:
B
Which advantage does the network assurance capability of Cisco DNA Center provide over traditional campus management?
|
A. |
Cisco DNA Center
correlates information from
different management protocols to obtain insights, and traditional campus management requires manual analysis. |
|
B. |
Cisco DNA Center
handles management tasks
at the controller to reduce the load on infrastructure
devices, and traditional campus management uses the data backbone. |
|
C. |
Cisco DNA Center leverages YANG and NETCONF
to assess the
status of fabric
and nonfabric devices, and
traditional campus management uses CLI exclusively. |
|
D. |
Cisco DNA Center automatically compares security postures among network devices, and traditional campus management needs manual comparisons. |
Answer: C
Refer to the exhibit. Router R14 is in the process of being configured. Which configuration must be used to establish a host route to PC 10?

|
A. |
ip route 10.80.65.10 255.255.255.254 10.80.65.1 |
|
B. |
ip route 10.80.65.10 255.255.255.255 10.73.65.66 |
|
C. |
ip route 1073.65.65 255.0.0.0 10.80.65.10 |
|
D. |
ip route 10.73.65.66 0.0.0.255 10.80.65.10 |
Answer:
B
What is the put method within HTTP?
|
A. |
It is a read-only operation. |
|
B. |
It is a nonldempotent operation. |
|
C. |
It replaces data at the destination. |
|
D. |
It displays
a web site. |
Answer: D
By default, which virtual MAC address does HSRP group 14 use?
|
A. |
00:05:5e:19:0c:14 |
|
B. |
00:05:0c:07:ac:14 |
|
C. |
04:15:26:73:3c:0e |
|
D. |
00:00:0c:07:ac:0e |
Answer: D
What does the implementation of a first-hop redundancy protocol protect against on a network?
|
A. |
default gateway failure |
|
B. |
BGP neighbor flapping |
|
C. |
spanning-tree loops |
|
D. |
root-bridge loss |
Answer: A
Which benefit does Cisco ONA Center provide over traditional campus management?
|
A. |
Cisco DNA Center
leverages SNMPv3 tor
encrypted management, and traditional campus management uses
SNMPv2. |
|
B. |
Cisco DNA Center automates HTTPS for secure
web access, and traditional campus
management uses HTTP. |
|
C. |
Cisco DNA Center
leverages APIs, and
traditional campus management requires manual data gathering. |
|
D. |
Cisco DNA Center
automates SSH access
for encrypted entry,
and SSH Is absent from
traditional campus management. |
Answer: B
Refer to the exhibit. An administrator received a call from a branch office regarding poor application performance hosted at the headquarters. Ethernet 1 is connected between Router1 and the LAN switch. What identifies the issue?
![]()
|
A. |
The QoS policy
is dropping traffic. |
|
B. |
There is a duplex
mismatch. |
|
C. |
The link is over
utilized. |
|
D. |
The MTU is not set to the default value. |
Answer: C
In QoS, which prioritization method is appropriate for interactive voice and video?
|
A. |
traffic policing |
|
B. |
round-robin scheduling |
|
C. |
low-latency queuing |
|
D. |
expedited forwarding |
Answer: C
Explanation:
Low Latency Queuing (LLQ) is the preferred queuing policy for VoIP audio. Given the stringent delay/jitter sensitive requirements of voice and video and the need to synchronize audio and video for CUVA, priority (LLQ) queuing is the recommended for all video traffic as well. Note that, for video, priority bandwidth is generally fudged up by 20% to account for the overhead.
The clients and OHCP server reside on different subnets.
Which command must be used to forward requests and replies between clients on the 10.10.0.1/24 subnet and the DHCP server at 192.168.10.1?
|
A. |
ip route 192.168.10.1 |
|
B. |
ip default-gateway 192.168.10.1 |
|
C. |
ip helper-address 192.168.10.1 |
|
D. |
ip dhcp address
192.168.10.1 |
Answer: C
Refer to the exhibit. Which next-hop IP address has the least desirable metric when sourced from R1?
![]()
|
A. |
10.10.10.5 |
|
B. |
10.10.10.3 |
|
C. |
10.10.10.4 |
|
D. |
10.10.10.2 |
Answer: C
Refer to the exhibit. Rapid PVST+ mode is on the same VLAN on each switch. Which switch becomes the root bridge and why?
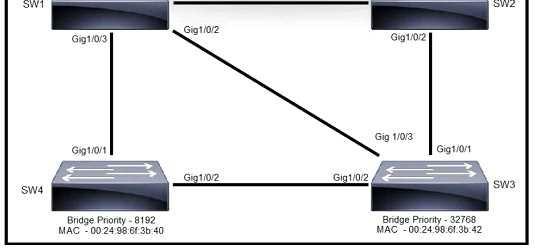
|
A. |
SW2, because its MAC address is the highest |
|
B. |
SW3, because
its priority is the highest |
|
C. |
SW4, because
its priority is highest and its MAC address is
lower |
|
D. |
SW1, because its
priority is the
lowest and its MAC address
is higher |
Answer:
B
Which two QoS tools provide congestion management? (Choose two.)
|
A. |
CBWFQ |
|
B. |
FRTS |
|
C. |
CAR |
|
D. |
PBR |
|
E. |
PQ |
Answer: AE
Explanation:
Common Cisco IOS-based congestion management tools include CBWFQ and LLQ algorithms. LLQ brings strict priority queuing (PQ) to CBWFQ.
PC1 tries to send traffic to newly installed PC2. The PC2 MAC address is not listed in the MAC address table of the switch, so the switch sends the packet to all ports in the same VLAN Which switching concept does this describe?
|
A. |
MAC address aging |
|
B. |
MAC address table |
|
C. |
frame flooding |
|
D. |
spanning-tree protocol |
Answer:
A
A network engineer is upgrading a small data center to host several new applications, including server backups that are expected to account for up to 90% of the bandwidth during peak times. The data center connects to the MPLS network provider via a primary circuit and a secondary circuit. How does the engineer inexpensively update the data center to avoid saturation of the primary circuit by traffic associated with the backups?
|
A. |
Assign traffic from
the backup servers
to a dedicated switch. |
|
B. |
Configure a dedicated circuit for the backup
traffic. |
|
C. |
Place the backup servers
in a dedicated VLAN. |
|
D. |
Advertise a more
specific route for
the backup traffic via the secondary circuit. |
Answer:
A
Refer to the exhibit. A network engineer executes the show ip route command on router D. What is the next hop to network 192.168.1.0/24 and why?
![]()
|
A. |
The next hop is 10.0.2.1 because it uses distance vector
routing |
|
B. |
The next hop is 10.0.2.1 because it is a link-state routing protocol |
|
C. |
The next hop is 10.0.0.1 because it has a better administrative distance |
|
D. |
The next hop is 10.0.0.1 because it has a higher
metric. |
Answer:
B
Refer to the exhibit. A Cisco engineer creates a new WLAN called lantest.
Which two actions must be performed so that only high-speed 2.4-Ghz clients connect? (Choose two.)
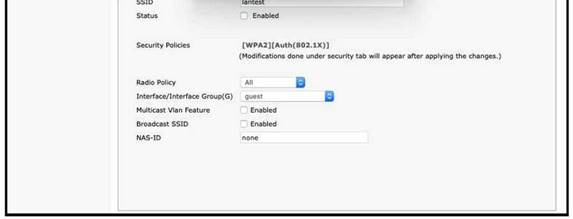
|
A. |
Enable the Broadcast SSID option |
|
B. |
Enable the
Status option. |
|
C. |
Set the Radio Policy
option to 802 11g Only. |
|
D. |
Set the Radio Policy
option to 802.11a
Only. |
|
E. |
Set the Interface/Interface Group(G) to an interface other than guest |
Answer: AB
What is the role of nonoverlapping channels in a wireless environment?
|
A. |
to reduce interference |
|
B. |
to allow for channel bonding |
|
C. |
to stabilize the RF
environment |
|
D. |
to increase bandwidth |
Answer: A
A router has two static routes to the same destination network under the same OSPF process. How does the router forward packets to the destination if the next-hop devices are different?
|
A. |
The router chooses the route with
the oldest age. |
|
B. |
The router load-balances traffic
over all routes
to the destination. |
|
C. |
The router chooses the next hop with the
lowest MAC address. |
|
D. |
The router chooses
the next hop with the
lowest IP address. |
Answer:
B
Explanation:
Load balancing is a standard functionality of Cisco IOS Software that is available across all router platforms. It is inherent to the forwarding process in the router, and it enables a router to use multiple paths to a destination when it forwards packets. The number of paths used is limited by the number of entries that the routing protocol puts in the routing table. Four entries is the default in Cisco IOS Software for IP routing protocols except for BGP. BGP has a default of one entry.
Refer to the exhibit. Which two values does router R1 use to determine the best path to reach destinations in network 1.0.0.0/8? (Choose two.)
![]()
|
A. |
longest prefix match |
|
B. |
highest administrative distance |
|
C. |
highest metric |
|
D. |
lowest metric |
|
E. |
lowest cost to reach the next hop |
Answer: AD
Refer to the exhibit. Host A switch interface is configured in VLAN 2. Host D sends a unicast packet destined for the IP address of host A.
![]()
What does the switch do when it receives the frame from host D?
|
A. |
It creates a broadcast storm. |
|
B. |
It drops the frame
from the MAC table of the switch. |
|
C. |
It shuts down the
source port and places It In err-disable mode. |
|
D. |
It floods the frame out of every
port except the
source port. |
Answer: C
A network analyst is tasked with configuring the date and time on a router using EXEC mode. The date must be set to January 1, 2020 and the time must be set to 12:00 am.
Which command should be used?
|
A. |
clock timezone |
|
B. |
clock summer-time date |
|
C. |
clock summer-time recurring |
|
D. |
clock set |
Answer: D
Refer to the exhibit. A network engineer started to configure two directly-connected routers as shown. Which command sequence must the engineer configure on R2 so that the two routers become OSPF neighbors?
![]()
|
A. |
|
|
B. |
|
|
C. |
|
|
D. |
|
Answer: D
Refer to the exhibit. A network engineer must provide configured IP addressing details to investigate a firewall rule issue.
Which subnet and mask Identify what is configured on the eth0 interface?
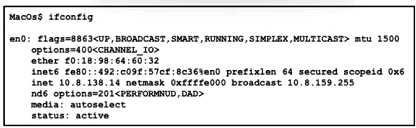
|
A. |
10.8.0.0/16 |
|
B. |
10.8.64.0/18 |
|
C. |
10.8.128.0/19 |
|
D. |
10.8.138.0/24 |
Answer: D
Refer to the exhibit. What does route 10.0.1.3/32 represent in the routing table?
![]()
|
A. |
the 10.0.0.0 network |
|
B. |
a single destination address |
|
C. |
the source 10.0.1.100 |
|
D. |
all hosts in the 10.0.1.0 subnet |
Answer:
A
Refer to the exhibit. A network administrator must permit traffic from the 10.10.0.0/24 subnet to the WAN on interlace Seria10.
What is the effect of the configuration as the administrator applies the command?
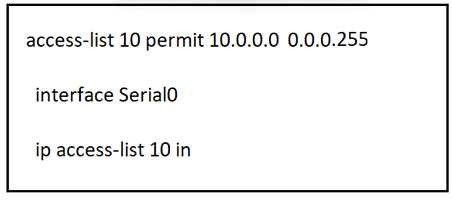
|
A. |
The permit command
fails and returns
an error code. |
|
B. |
The router accepts all incoming traffic
to Seria10 with the last
octet of the source IP set to 0. |
|
C. |
The sourced traffic from
IP range 10.0.0.0 -10.0.0.255 is allowed
on Seria10. |
|
D. |
The router fails
to apply the access list to the
interface. |
Answer: C
What is the role of community strings in SNMP operations?
|
A. |
It serves as a sequence tag on SNMP traffic messages. |
|
B. |
It serves as a password lo protect access
to MIB objects. |
|
C. |
It passes the Active
Directory username and password that
are required for device access |
|
D. |
It translates alphanumeric MIB output values
to numeric values. |
Answer:
B
Which access point mode relies on a centralized controller for management, roaming, and SSID configuration?
|
A. |
repeater mode |
|
B. |
autonomous mode |
|
C. |
bridge mode |
|
D. |
lightweight mode |
Answer: D
Explanation:
For Lightweight APs, the functions of an AP can be split between the AP and the WLC. Other functions are carried out by a WLC. The WLC is also sued to centrally configure the lightweight APs. Can be configured in modes such as Local or FlexConnect.
What are two characteristics of a small office / home office connection environment? (Choose two.)
|
A. |
It requires 10Gb
ports on all
uplinks. |
|
B. |
It supports between 50 and 100
users. |
|
C. |
It supports between 1 and 50
users. |
|
D. |
It requires a core,
distribution, and access
layer architecture. |
|
E. |
A router port
connects to a broadband connection. |
Answer: CE
Which syslog severity level is considered the most severe and results in the system being considered unusable?
|
A. |
Alert |
|
B. |
Error |
|
C. |
Emergency |
|
D. |
Critical |
Answer: C
What is the definition of backdoor malware?
|
A. |
malicious code that
is installed onto a computer to allow access
by an unauthorized user |
|
B. |
malicious code
with the main
purpose of downloading other malicious code |
|
C. |
malicious program that is used
to launch other
malicious programs |
|
D. |
malicious code that
infects a user machine and then uses
that machine to send spam |
Answer:
A
Refer to the exhibit. The primary route across Gi0/0 is configured on both routers. A secondary route must be configured to establish connectivity between the workstation networks.
Which command set must be configured to complete this task?
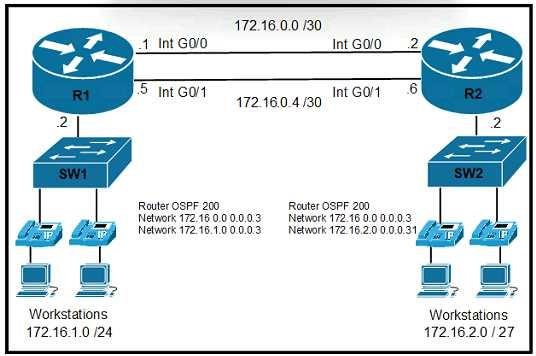
|
A. |
|
|
B. |
|
|
C. |
|
|
D. |
|
Answer: D
Which command creates a static NAT binding for a PC address of 10.1.1.1 to the public routable address 209.165.200.225 assigned to the PC?
|
A. |
R1(config)#ip nat
inside source static
10.1.1.1 209.165.200.225 |
|
B. |
R1(config)#ip nat outside
source static 209.165.200.225 10.1.1.1 |
|
C. |
R1(config)#ip nat inside
source static 209.165.200.225 10.1.1.1 |
|
D. |
R1(config)#ip nat outside source static 10.1.1.1 209.165.200.225 |
Answer:
A
What prevents a workstation from receiving a DHCP address?
|
A. |
STP |
|
B. |
VTP |
|
C. |
802.1Q |
|
D. |
DTP |
Answer: C
What is a feature of TFTP?
|
A. |
offers anonymous user
login ability |
|
B. |
uses two separate connections for control and data traffic |
|
C. |
relies on the well-known TCP port 20 to transmit data |
|
D. |
provides secure data
transfer |
Answer:
A
Which QoS forwarding per-hop behavior changes a specific value in a packet header to set the class of service for the packet?
|
A. |
shaping |
|
B. |
classification |
|
C. |
policing |
|
D. |
marking |
Answer: D
Which per-hop traffic-control feature does an ISP implement to mitigate the potential negative effects of a customer exceeding its committed bandwidth?
|
A. |
policing |
|
B. |
queuing |
|
C. |
marking |
|
D. |
shaping |
Answer:
A
Which remote access protocol provides unsecured remote CLI access?
|
A. |
console |
|
B. |
Telnet |
|
C. |
SSH |
|
D. |
Bash |
Answer:
B
What is a syslog facility?
|
A. |
host that is configured for
the system to send log
messages |
|
B. |
password that
authenticates a Network
Management System to receive log messages |
|
C. |
group of log messages associated with the configured severity level |
|
D. |
set of values
that represent the
processes that can
generate a log
message |
Answer: D
What is the function of FTP?
|
A. |
Always operated without user connection validation |
|
B. |
Uses block
number to identify and mitigate data-transfer errors |
|
C. |
Relies on the well-known UDO port 69 for data
transfer |
|
D. |
Uses two separate connections for control and data traffic |
Answer: D
How does TFTP operate in a network?
|
A. |
Provides secure data transfer |
|
B. |
Relies on the well-known TCP port 20 to transmit data |
|
C. |
Uses block
numbers to identify and mitigate data-transfer errors |
|
D. |
Requires two separate connections for control and data traffic |
Answer: C
Which device performs stateful inspection of traffic?
|
A. |
switch |
|
B. |
firewall |
|
C. |
access point |
|
D. |
wireless controller |
Answer: B
Explanation:
Stateful inspection, also known as dynamic packet filtering, is a firewall technology that monitors
the state of active connections and uses this information to determine which network packets to allow through the firewall.
How does WPA3 improve security?
|
A. |
It uses
SAE for authentication. |
|
B. |
It uses RC4 for
encryption. |
|
C. |
It uses TKIP for encryption. |
|
D. |
It uses a 4-way handshake for authentication. |
Answer:
A
Which device separates networks by security domains?
|
A. |
intrusion protection system |
|
B. |
firewall |
|
C. |
wireless controller |
|
D. |
access point |
Answer:
B
Which enhancements were implemented as part of WPA3?
|
A. |
Forward secrecy and SAE in personal mode
for secure initial
key exchange |
|
B. |
802.1x authentication and AES-128 encryption |
|
C. |
AES-64 in personal mode
and AES-128 in enterprise mode |
|
D. |
TKIP encryption improving WEP and per-packet keying |
Answer:
A
In an SDN architecture, which function of a network node is centralized on a controller?
|
A. |
Creates the IP routing table |
|
B. |
Discards a message due filtering |
|
C. |
Makes a routing decision |
|
D. |
Provides protocol access
for remote access
devices |
Answer: C
Explanation:
A controller, or SDN controller, centralizes the control of the networking devices. The degree of control, and the type of control, varies widely. For instance, the controller can perform all control plane functions (such as making routing decisions) replacing the devices' distributed control plane.
Which management security process is invoked when a user logs in to a network device using their username and password?
|
A. |
authentication |
|
B. |
auditing |
|
C. |
accounting |
|
D. |
authorization |
Answer:
A
Which port security violation mode allows from valid MAC addresses to pass but blocks traffic from invalid MAC addresses?
|
A. |
restrict |
|
B. |
shutdown |
|
C. |
protect |
|
D. |
shutdown VLAN |
Answer: C
A customer wants to provide wireless access to contractors using a guest portal on Cisco ISE. The portal is also used by employees. A solution is implemented, but contractors receive a certificate error when they attempt to access the portal. Employees can access the portal without any errors. Which change must be implemented to allow the contractors and employees to access the portal?
|
A. |
Install an Internal CA signed certificate on the Cisco
ISE. |
|
B. |
Install a trusted third-party certificate on the Cisco ISE. |
|
C. |
Install an internal CA signed certificate on the contractor devices. |
|
D. |
Install a trusted
third-party certificate on the contractor devices. |
Answer:
B
A network engineer is implementing a corporate SSID for WPA3-Personal security with a PSK. Which encryption cipher must be configured?
|
A. |
CCMP128 |
|
B. |
GCMP256 |
|
C. |
CCMP256 |
|
D. |
GCMP128 |
Answer:
A
Explanation:
WPA3 mandates the adoption of Protected Management Frames, which help guard against eavesdropping and forging. It also standardizes the 128-bit cryptographic suite and disallows obsolete security protocols. WPA3-Enterprise has optional 192-bit security encryption and a 48-
bit IV for heightened protection of sensitive corporate, financial and governmental data. WPA3- Personal uses CCMP-128 and AES-128.
Why would a network administrator choose to implement automation in a network environment?
|
A. |
To simplify the
process of maintaining a consistent configuration state across all
devices |
|
B. |
To centralize device information storage |
|
C. |
To implement centralized user account management |
|
D. |
To deploy the
management plane separately from the rest of the network |
Answer:
A
Which two REST API status-code classes represent errors? (Choose two.)
|
A. |
1XX |
|
B. |
2XX |
|
C. |
3XX |
|
D. |
4XX |
|
E. |
5XX |
Answer: DE
What is a function of a southbound API?
|
A. |
Use orchestration to provision a virtual server
configuration from a web server |
|
B. |
Automate configuration changes between a server and a switching fabric |
|
C. |
Manage flow control between
an SDN controller and a switching fabric |
|
D. |
Facilitate the information exchange between an SDN controller and application |
Answer: C
Which script paradigm does Puppet use?
|
A. |
recipes and cookbooks |
|
B. |
playbooks and roles |
|
C. |
strings and marionettes |
|
D. |
manifests and modules |
Answer: D
Which set of methods is supported with the REST API?
|
A. |
GET, PUT, ERASE,
CHANGE |
|
B. |
GET, POST, MOD, ERASE |
|
C. |
GET, PUT,
POST, DELETE |
|
D. |
GET, POST, ERASE,
CHANGE |
Answer: C
Which definition describes JWT in regard to REST API security?
|
A. |
an encrypted JSON
token that is used for
authentication |
|
B. |
an encrypted JSON token
that is used
for authorization |
|
C. |
an encoded JSON token
that is used
to securely exchange information |
|
D. |
an encoded JSON
token that is used for authentication |
Answer: C
Which communication interaction takes place when a southbound API is used?
|
A. |
between the SDN
controller and PCs on the
network |
|
B. |
between the SDN controller and switches and routers on the network |
|
C. |
between the SDN controller and services and applications on the network |
|
D. |
between network applications and switches and routers on the network |
Answer:
B
What are two characteristics of a public cloud implementation? (Choose two.)
|
A. |
It is owned
and maintained by one party,
but it is shared among
multiple organizations |
|
B. |
It enables an organization to fully customize how it deploys
network resources |
|
C. |
It provides services that are accessed over the Internet |
|
D. |
It is a data
center on the public Internet that maintains cloud
services for only one company |
|
E. |
It supports network resources from a centralized third-party provider and privately-owned virtual resources |
Answer:
AC
Drag and Drop Question
Drag and drop the steps in a standard DNS lookup operation from the left into the order on the right.
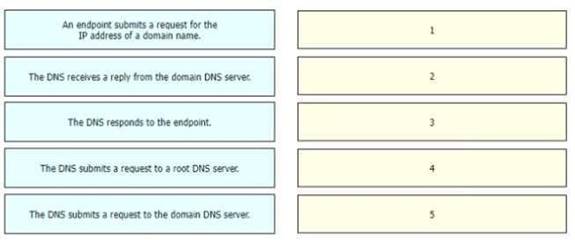
Answer:
![]()
Drag and Drop Question
Drag and drop the Ansible features from the left to the right. Not all features are used.
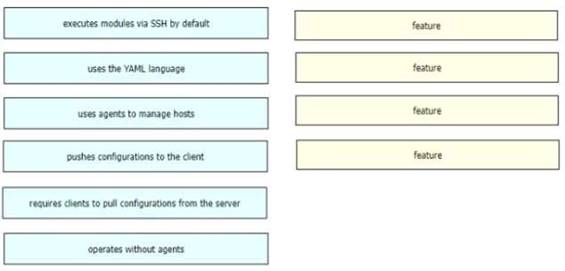
Answer:
![]()
Drag and Drop Question
Refer to the exhibit. Drag and drop the learned prefixes from the left onto the subnet masks on the right.
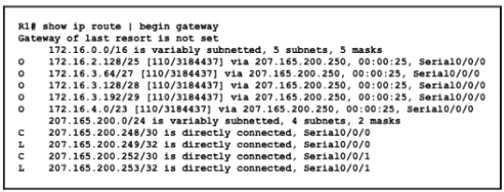
![]()
Answer:
![]()
Drag and Drop Question
Drag and drop the WLAN components from the left onto the component details on the right.
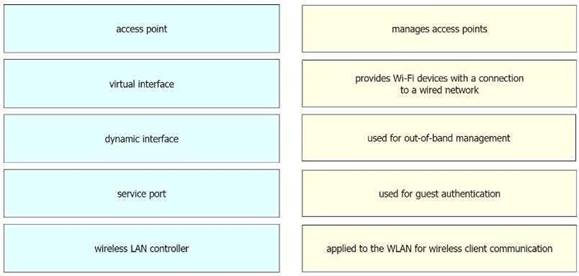
Answer:
![]()
Drag and Drop Question
Drag and drop the DNS commands from the left onto their effects on the right.
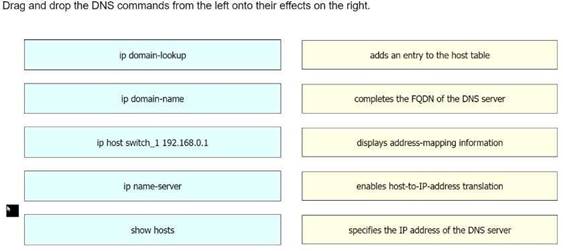
Answer:
![]()
Drag and Drop Question
Drag and drop the statement about AAA services from the left to the corresponding AAA services on the right.
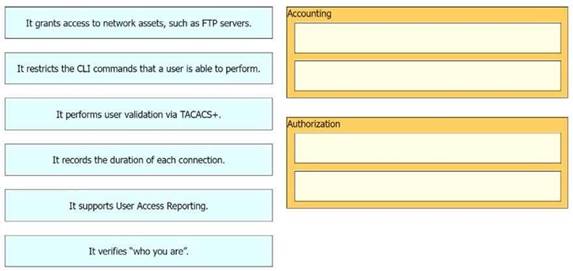
Answer:
![]()
Drag and Drop Question
An engineer must configure a core router with a floating static default route to the backup router at 10.200.0.2.
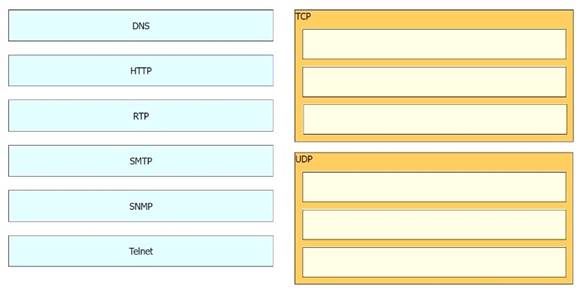
Answer:
![]()
Drag and Drop Question
Refer to the exhibit. The Router1 routing table has multiple methods to reach 10.10.10.0/24 as shown. The default Administrative Distance is used. Drag and drop the network conditions from the left onto the routing methods that Router1 uses on the right.
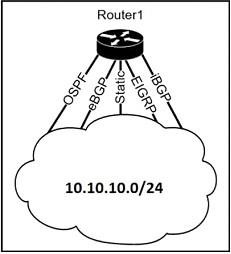
![]()
Answer:
![]()
Drag and Drop Question
Drag and drop the wireless architecture benefits from the left onto the architecture types on the right.
![]()
Answer:
![]()
Drag and Drop Question
Refer to the exhibit. Drag and drop the destination IPs from the left onto the paths to reach those destinations on the right.
![]()
Answer:
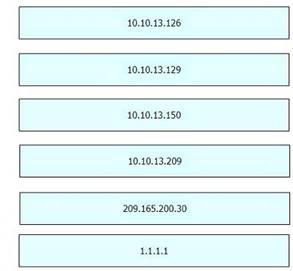
Drag and Drop Question
Drag and drop the characteristics of northbound APIs from the left onto any position on the right. Not all characteristics are used.
![]()
Answer: